CN109873699B - Revocable identity public key encryption method - Google Patents
Revocable identity public key encryption method Download PDFInfo
- Publication number
- CN109873699B CN109873699B CN201711265792.5A CN201711265792A CN109873699B CN 109873699 B CN109873699 B CN 109873699B CN 201711265792 A CN201711265792 A CN 201711265792A CN 109873699 B CN109873699 B CN 109873699B
- Authority
- CN
- China
- Prior art keywords
- key
- user
- ciphertext
- identity
- calculate
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Active
Links
Images
Landscapes
- Storage Device Security (AREA)
Abstract
本发明公开了一种可撤销的身份公钥加密方法,所述的方法包括以下步骤:(1)从密码学应用函数库中选取参数,并生成系统的主私钥和主公钥;(2)根据系统的参数、系统主私钥和用户的身份,生成用户的私钥;(3)根据系统参数、系统主私钥、用户身份和时间参数,生成用户的时间密钥;(4)利用消息接收者的公钥和当前时间参数计算出一个临时会话密钥,再用该临时会话密钥加密消息;(5)接收者收到密文后,先利用双线性映射、自己的私钥和时间密钥计算出会话密钥,再利用该会话密钥解密出明文消息。本发明所述的身份公钥加密系统中,被撤销的用户无法通过解密密文获得正确的明文,从而保证了身份公钥系统的安全性。
The invention discloses a revocable identity public key encryption method. The method includes the following steps: (1) selecting parameters from a cryptography application function library, and generating a master private key and a master public key of the system; (2) ) According to the parameters of the system, the master private key of the system and the identity of the user, generate the private key of the user; (3) According to the parameters of the system, the master private key of the system, the identity of the user and the time parameter, generate the time key of the user; (4) Use The public key of the message receiver and the current time parameter calculate a temporary session key, and then use the temporary session key to encrypt the message; (5) After the receiver receives the ciphertext, it first uses bilinear mapping, its own private key and time key to calculate the session key, and then use the session key to decrypt the plaintext message. In the identity public key encryption system of the present invention, the revoked user cannot obtain the correct plaintext by decrypting the ciphertext, thereby ensuring the security of the identity public key system.
Description
技术领域technical field
本发明属于信息安全技术领域,具体涉及签名技术和身份公钥加密技术,尤其涉及一种可撤销的身份公钥加密方法。The invention belongs to the technical field of information security, in particular to a signature technology and an identity public key encryption technology, in particular to a revocable identity public key encryption method.
背景技术Background technique
公钥密码是解决日益突出的信息安全问题的重要技术。在公钥密码系统里,首先需要解决的是公钥的真实性和有效性问题。传统的公钥系统通过给用户颁发公钥证书来实现认证,但与此同时,公钥证书的管理需要巨大的开销。身份公钥密码系统(IdentityBased Public Key Cryptography,IDPKC)则较好地解决了传统公钥密码系统中复杂的证书管理问题。IDPKC由著名密码学家Ad Shamir于1984年提出,在该系统中,用户的身份(比如手机号、IP地址和Email地址)就是用户的公钥。2001年,Boneh与Franklin利用双线性映射Weil对首次设计出一个实用的身份公钥加密方案,使身份公钥密码迈进了实际应用的门槛。Public key cryptography is an important technology to solve the increasingly prominent information security problems. In the public key cryptosystem, the first problem to be solved is the authenticity and validity of the public key. The traditional public key system realizes authentication by issuing public key certificates to users, but at the same time, the management of public key certificates requires huge overhead. Identity-Based Public Key Cryptography (IDPKC) better solves the complex certificate management problems in traditional public-key cryptography. IDPKC was proposed by the famous cryptographer Ad Shamir in 1984. In this system, the user's identity (such as mobile phone number, IP address and Email address) is the user's public key. In 2001, Boneh and Franklin used bilinear mapping Weil pair to design a practical identity public key encryption scheme for the first time, which made identity public key cryptography step into the threshold of practical application.
2008年,身份公钥密码算法(也称标识密码算法)正式获得国家密码管理局颁发的商密算法型号SM9(GM/T 0044-2016),为我国身份公钥密码技术的应用奠定了坚实的基础。SM9算法不需要申请数字证书,使用方便,易于部署,可采用手机号码或邮件地址作为公钥,实现数据加密、身份认证、通话加密、通道加密等,适用于保护互联网各种新兴应用的安全,如基于云计算的密码服务、电子邮件安全、智能终端保护、物联网安全、云存储安全等。In 2008, the identity public key cryptographic algorithm (also known as the identification cryptographic algorithm) officially obtained the commercial secret algorithm model SM9 (GM/T 0044-2016) issued by the State Cryptography Administration, laying a solid foundation for the application of identity public key cryptography in my country. Base. The SM9 algorithm does not need to apply for a digital certificate. It is easy to use and easy to deploy. It can use mobile phone numbers or email addresses as public keys to realize data encryption, identity authentication, call encryption, channel encryption, etc. It is suitable for protecting the security of various emerging Internet applications. Such as cloud computing-based password services, email security, intelligent terminal protection, IoT security, cloud storage security, etc.
每种公钥系统都必须解决一个重要问题——用户撤销问题,当用户的使用权限到期,用户的私钥泄露,或用户操作违规,这时系统需要撤销这类用户。在传统公钥系统中,撤销方法有撤销列表CRLs、在线证书状态协议OCSP等,都是比较成熟的技术,但这些技术并不适用于身份公钥系统。根据身份公钥系统的结构特点,目前的用户撤销技术主要是系统周期性地更新用户私钥,但是每次更新的密钥都必须通过秘密信道传输给用户,而秘密信道的建立需要系统和用户很多额外的计算资源和通信开销。因此,如何提高身份公钥系统下的用户撤销机制的运行效率是一个需要解决的重要问题。目前,Boldyreva等人设计了一个具有可扩展性的可撤销的身份公钥加密(RIBE)方案,Libert和Vergnaud对该方案作了改进,提高了安全性,Seo等人在PKC2013上提出了应对解密密钥泄露威胁的RIBE方案。但是,现有身份公钥系统的用户撤销技术在效率和实用性方面仍然有待进一步提高。Every public key system must solve an important problem - the problem of user revocation. When the user's use rights expire, the user's private key is leaked, or the user operates illegally, the system needs to revoke such users. In traditional public key systems, revocation methods include revocation list CRLs, online certificate status protocol OCSP, etc., which are relatively mature technologies, but these technologies are not suitable for identity public key systems. According to the structural characteristics of the identity public key system, the current user revocation technology is mainly that the system periodically updates the user's private key, but each updated key must be transmitted to the user through a secret channel, and the establishment of the secret channel requires the system and the user. Lots of extra computing resources and communication overhead. Therefore, how to improve the operation efficiency of the user revocation mechanism under the identity public key system is an important problem that needs to be solved. At present, Boldyreva et al. have designed a scalable and revocable identity public key encryption (RIBE) scheme. Libert and Vergnaud have improved the scheme to improve security. Seo et al. proposed a solution to decryption at PKC2013. RIBE scheme for key compromise threats. However, the user revocation technology of the existing identity public key system still needs to be further improved in terms of efficiency and practicability.
发明内容SUMMARY OF THE INVENTION
发明目的:本发明提供一种可撤销的身份公钥加密方法,该方法是基于国密标准SM9设计的,安全、高效、实用。本方法在进行数据保密传输时,能撤销用户,使得不符合要求的用户无法获得正确的明文消息,保障了系统的安全性。Purpose of the invention: The present invention provides a revocable identity public key encryption method, which is designed based on the national secret standard SM9, and is safe, efficient and practical. The method can revoke users when the data is transmitted confidentially, so that users who do not meet the requirements cannot obtain correct plaintext messages, and the security of the system is guaranteed.
为实现上述目的,本发明公开的技术方案是:私钥生成中心PKG利用用户的身份和时间参数生成用户的私钥和时间密钥,并通过定时更新时间密钥的方法来撤销不符合要求的用户。具体步骤如下:In order to achieve the above-mentioned purpose, the technical scheme disclosed by the present invention is: the private key generation center PKG utilizes the user's identity and time parameters to generate the user's private key and the time key, and revokes the non-compliance with the method of regularly updating the time key. user. Specific steps are as follows:
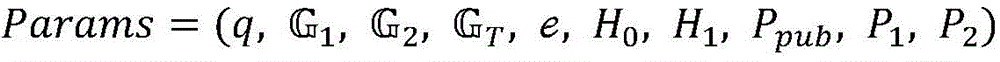
(1)系统主密钥生成:身份公钥系统从计算机编程语言库JPBC库或者PBC库中选取一套参数,所述参数包括三个阶为大素数q的循环群和选取双线性映射 的生成元P1,的生成元P2,选取两个不同的哈希函数H0和H1,选取系统主私钥ke,根据ke计算系统主公钥Ppub=[ke]P1,将参数公开,系统主私钥ke保密,并且选取一个密钥导出函数KDF和消息认证码函数MAC。(1) System master key generation: The identity public key system selects a set of parameters from the computer programming language library JPBC library or PBC library, and the parameters include three cyclic groups whose orders are large prime numbers q and Choose Bilinear Map The generator P 1 of , The generator P 2 of , selects two different hash functions H 0 and H 1 , selects the system master private key ke, calculates the system master public key P pub =[ke]P 1 according to ke, and sets the parameter Open, the system master private key ke is kept secret, and a key derivation function KDF and a message authentication code function MAC are selected.
(2)用户私钥生成:身份公钥系统将用户的身份ID作为用户的公钥,并根据ID和系统主私钥ke,生成用户的私钥SKID;(2) user private key generation: the identity public key system uses the user's identity ID as the user's public key, and generates the user's private key SK ID according to the ID and the system master private key ke;
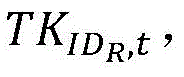
(3)时间密钥生成:根据时间参数t、用户的身份ID和系统主私钥ke,生成用户的时间密钥TKID,t;(3) time key generation: according to the time parameter t, the user's identity ID and the system master private key ke, generate the user's time key TK ID, t ;
(4)加密传输:消息发送者利用消息接收者的身份ID、时间参数t和系统公共参数Params计算出一个临时会话密钥K,再利用该临时会话密钥K加密消息M,得到密文C,将密文C发送给接收者。(4) Encrypted transmission: The message sender calculates a temporary session key K by using the identity ID of the message receiver, the time parameter t and the system public parameter Params, and then uses the temporary session key K to encrypt the message M to obtain the ciphertext C , and send the ciphertext C to the receiver.
(5)解密步骤:接收者利用双线性映射、自己的私钥SKID和时间密钥TKID,t计算出临时会话密钥K,再用该会话密钥K解密出明文消息M。(5) Decryption step: the receiver uses bilinear mapping, its own private key SK ID and time key TK ID, t to calculate the temporary session key K, and then uses the session key K to decrypt the plaintext message M.
进一步的,步骤(1)所选取的两个不同的哈希函数和其中,表示有限域Zq去掉零元素后的乘法群。Further, two different hash functions selected in step (1) and in, represents the multiplicative group of the finite field Z q with zero elements removed.
步骤(2)所述的用户私钥SKID生成,包括以下步骤:The generation of the user's private key SK ID described in step (2) comprises the following steps:
(2.1)身份公钥系统的私钥生成中心PKG计算用户身份ID的哈希函数值H0(ID);(2.1) The private key generation center PKG of the identity public key system calculates the hash function value H 0 (ID) of the user identity ID;
(2.2)PKG计算用户的私钥,其计算公式为:(2.2) PKG calculates the user's private key, and its calculation formula is:
SKID=[(H0(ID)+ke)-1ke]P2,SK ID = [(H 0 (ID)+ke) -1 ke]P 2 ,
其中,[]表示点乘运算。Among them, [] represents the dot multiplication operation.
步骤(3)所述的用户的时间密钥TKID,t生成,包括以下步骤:The time key TK ID of the described user of step (3), t generates, comprises the following steps:
(3.1)计算用户身份ID和时间参数t的哈希函数值H1(ID||t);(3.1) Calculate the hash function value H 1 (ID||t) of the user identity ID and the time parameter t;
(3.2)再计算时间密钥,计算公式如下:(3.2) Calculate the time key again, and the calculation formula is as follows:
TKID,t=[(H1(ID||t)+ke)-1ke]P2 TK ID, t = [(H 1 (ID||t)+ke) -1 ke]P 2
其中,[]表示点乘运算,||表示比特顺序级联。Among them, [] represents the dot multiplication operation, and || represents the bit order concatenation.
步骤(4)所述加密消息M包括如下步骤:The described encrypted message M of step (4) comprises the steps:
(4.1)发送者利用hash函数H0和H1分别计算QID=[H0(ID)]P1+Ppub和QID,t=[H1(ID||t)]P1+Ppub;(4.1) The sender uses the hash functions H 0 and H 1 to calculate Q ID = [H 0 (ID)]P 1 +P pub and Q ID respectively, t = [H 1 (ID||t)]P 1 +P pub ;
(4.2)从中随机选择两个数r0和r1,计算出部分密文C0=[r0]QID和C1=[r1]QID,t;(4.2) From Randomly select two numbers r 0 and r 1 in , and calculate the partial ciphertext C 0 =[r 0 ]Q ID and C 1 =[r 1 ]Q ID,t ;
(4.3)利用双线性运算计算 (4.3) Calculation using bilinear operation
(4.4)利用密钥导出函数KDF,计算用于加密的临时会话密钥K=KDF(C0,C1,W,ID,Klen)=K1||K2,其中,Klen表示密钥长度;(4.4) Using the key derivation function KDF, calculate the temporary session key used for encryption K=KDF(C 0 , C 1 , W, ID, Klen)=K 1 ||K 2 , where Klen represents the key length ;
(4.5)利用密钥K1加密消息M,计算部分密文符号表示异或;(4.5) Encrypt the message M with the key K 1 , and calculate the partial ciphertext symbol means exclusive or;
(4.6)利用密钥K2计算部分密文C3=MAC(K2,C2),该部分密文用于密文的完整性验证;(4.6) Use the key K 2 to calculate the partial ciphertext C 3 =MAC(K 2 , C 2 ), and this partial ciphertext is used for the integrity verification of the ciphertext;
(4.7)输出密文C=(C0,C1,C2,C3),并把它发送给消息接收者。(4.7) Output the ciphertext C=(C 0 , C 1 , C 2 , C 3 ), and send it to the message receiver.
步骤(5)所述的接收者利用双线性映射、自己的私钥SKID和时间密钥TKID,t解密密文,其步骤如下:The described receiver of step (5) utilizes bilinear mapping, own private key SK ID and time key TK ID, t decrypts the ciphertext, and its steps are as follows:
(5.1)利用双线性运算e、用户的私钥SKID和时间密钥TKID,t,计算W=e(C0,SKID)e(C1,TKID,t);(5.1) Calculate W=e(C 0 , SK ID ) e(C 1 , TK ID, t ) by using bilinear operation e, user’s private key SK ID and time key TK ID, t ;
(5.2)根据上一步计算得到的W,计算用于解密密文的临时会话密钥K=KDF(C0,C1,W,ID,Klen)=K1||K2;(5.2) According to the W calculated in the previous step, calculate the temporary session key K=KDF(C 0 , C 1 , W, ID, Klen)=K 1 ||K 2 for decrypting the ciphertext;
(5.3)验证密文的完整性:计算C′3=MAC(K2,C2),验证C′3是否与部分密文C3相等,如果是,则说明密文没有被修改过,可进一步解密出消息否则,输出“密文无效”。(5.3) Verify the integrity of the ciphertext: Calculate C′ 3 =MAC(K 2 , C 2 ), verify whether C′ 3 is equal to the partial ciphertext C 3 , if so, it means that the ciphertext has not been modified, and it can be Decrypt the message further Otherwise, "Ciphertext is invalid" is output.
有益效果:本发明通过更新时间密钥的方法,使得系统中不符合要求的用户无法解密出正确的明文,从而实现对用户的撤销操作。更新的时间密钥只需要通过公开信道传输,节省了通信开销,并且本发明所采用的身份公钥加密算法为国家商用密码算法SM9,具有实用性。Beneficial effects: The present invention makes the users who do not meet the requirements in the system unable to decrypt the correct plaintext through the method of updating the time key, thereby realizing the revocation operation for the user. The updated time key only needs to be transmitted through an open channel, which saves communication overhead, and the identity public key encryption algorithm adopted in the present invention is the national commercial encryption algorithm SM9, which is practical.
附图说明Description of drawings
图1是本发明身份公钥系统示意图;Fig. 1 is the identity public key system schematic diagram of the present invention;
图2是本发明的加解密过程示意图。FIG. 2 is a schematic diagram of the encryption and decryption process of the present invention.
具体实施方式Detailed ways
为了详细的说明本发明公开的技术方案,下面结合说明书附图和具体实施例做进一步的阐述。In order to describe the technical solutions disclosed in the present invention in detail, further description will be given below in conjunction with the accompanying drawings and specific embodiments of the description.
本发明所提供的一种可撤销的身份公钥加密系统如图1所示,首先由该加密系统的私钥生成中心PKG生成用户的私钥,然后将用户私钥通过秘密信道发送到各个用户端,用户均采用其身份ID作为公钥,唯一标识用户。A revocable identity public key encryption system provided by the present invention is shown in Figure 1. First, the user's private key is generated by the private key generation center PKG of the encryption system, and then the user's private key is sent to each user through a secret channel At the terminal, users use their IDs as public keys to uniquely identify users.
对于图1,本发明的有关技术术语说明如下:For Fig. 1, the relevant technical terms of the present invention are described as follows:
(1)PKG为身份公钥系统的“私钥生成中心”,负责生成用户的私钥和更新时间密钥。(1) PKG is the "private key generation center" of the identity public key system, which is responsible for generating the user's private key and updating the time key.
(2)ID为用户的身份,唯一标识用户,是用户的公钥,可采用比如手机号码或邮件地址。(2) ID is the identity of the user, which uniquely identifies the user and is the user's public key, such as a mobile phone number or an email address.
如图2所示的是一种可撤销的身份公钥加密方法具体的步骤流程图,包括如下步骤:As shown in Figure 2 is a specific step flow chart of a revocable identity public key encryption method, including the following steps:
步骤1、生成系统主密钥:Step 1. Generate the system master key:
从JAVA的JPBC库(或C语言的PBC库)中选择三个阶为素数q的循环群和(可采用256位的椭圆曲线y2=x3+b)。P1和P2分别是群和的生成元,是非对称双线性映射。选取两个不同的哈希函数和可以将任意长的比特串映射到中,这里,表示有限域Zq去掉零元素后的乘法群。Select three cyclic groups with prime order q from JAVA's JPBC library (or C language PBC library) and (256-bit elliptic curve y 2 =x 3 +b can be used). P1 and P2 are groups respectively and generator of , is an asymmetric bilinear map. Pick two different hash functions and Arbitrarily long bit strings can be mapped to in, here, represents the multiplicative group of the finite field Z q with zero elements removed.
PKG从中随机选取一个元素ke,并计算Ppub=[ke]P1。秘密保存主私钥ke,公开系统参数其中,[]表示点乘运算。PKG from Randomly select an element ke in , and calculate P pub =[ke]P 1 . The master private key ke is kept secretly, and the system parameters are disclosed Among them, [] represents the dot multiplication operation.
步骤2、私钥生成Step 2. Private key generation
以用户身份ID为输入,PKG首先计算ID的哈希函数值H0(ID),再将H0(ID)与ke模q相加得到u=H0(ID)+ke(mod q),再采用扩展欧几里得算法对u求模q逆,即u-1(mod q),然后u-1与ke相乘,得到的乘积与P2做点乘运算,用户私钥SKID=[u-1k]P2,并通过安全信道将私钥SKID传送给用户。Taking the user ID as input, PKG first calculates the hash function value H 0 (ID) of the ID, and then adds H 0 (ID) and ke mod q to obtain u=H 0 (ID)+ke (mod q), Then use the extended Euclidean algorithm to inverse u modulo q, that is, u -1 (mod q), then multiply u -1 and ke, and the obtained product is multiplied by P 2. User private key SK ID = [u -1 k]P 2 , and transmit the private key SK ID to the user through a secure channel.
步骤3、时间密钥生成Step 3. Time key generation
PKG根据用户身份ID、时间参数t和系统主密钥ke,按照公式TKID,t=[(H1(ID||t)+ke)-1ke]P2,计算出时间密钥TKID,t,具体计算过程与SKID的计算过程类似,不同的是,哈希函数H1的输入除了用户身份ID外,还有时间参数t。PKG通过公开信道将TKID,t传送给用户,并根据新的时间参数定期为用户重新计算TKID,t。PKG calculates the time key TK ID according to the user identity ID, the time parameter t and the system master key ke, according to the formula TK ID, t = [(H 1 (ID||t)+ke) -1 ke]P 2 , t , the specific calculation process is similar to the calculation process of SK ID , the difference is that the input of the hash function H 1 has a time parameter t in addition to the user identity ID. The PKG transmits the TK ID,t to the user through an open channel, and periodically recalculates the TK ID,t for the user according to the new time parameters.
时间参数t是更新密钥的时间,可根据具体的应用场景来确定,被访问频繁的系统可以将时间参数t设置的稍短一些,不经常被访问的系统可以将时间参数设置的稍长一些,比如云计算环境下的访问控制系统可将时间参数设置为一个月。The time parameter t is the time to update the key, which can be determined according to the specific application scenario. The time parameter t can be set slightly shorter for the system that is frequently accessed, and the time parameter can be set slightly longer for the system that is not frequently accessed. , for example, the access control system in the cloud computing environment can set the time parameter to one month.
步骤4、加密并传输Step 4. Encrypt and transmit
(1)消息发送者首先根据消息接收者的身份ID和时间参数t分别计算哈希值H0(ID)和H1(ID||t),并做点乘运算[H0(ID)]P1和[H1(ID||t)]P1,再计算QID=[H0(ID)]P1+Ppub和QID,t=[H1(ID||t)]P1+Ppub;(1) The message sender first calculates the hash values H 0 (ID) and H 1 (ID||t) according to the identity ID of the message receiver and the time parameter t, and performs the dot product [H 0 (ID)] P 1 and [H 1 (ID||t)]P 1 , and then calculate Q ID =[H 0 (ID)]P 1 +P pub and Q ID, t =[H 1 (ID||t)]P 1 + Ppub ;
(2)从中随机选择两个数r0和r1,计算C0=[r0]QID和C1=[r1]QID,t;(2) From Randomly select two numbers r 0 and r 1 in , and calculate C 0 =[r 0 ]Q ID and C 1 =[r 1 ]Q ID,t ;
(3)计算 (3) Calculation
(4)通过密钥导出函数KDF,计算临时会话密钥K=KDF(C0,C1,W,IDKlen)=K1||K2,其中,Klen表示密钥长度,符号“||”表示比特顺序级联;(4) Calculate the temporary session key K=KDF(C 0 , C 1 , W, IDKlen)=K 1 ||K 2 through the key derivation function KDF, where Klen represents the key length, and the symbol “||” Indicates bit order concatenation;
(5)用K1加密消息M,得到部分密文其中,符号表示比特异或;(5) Encrypt message M with K 1 to obtain partial ciphertext Among them, the symbol means bit exclusive OR;
(6)用K2计算用于完整性验证的部分密文C3=MAC(K2,C2),其中,MAC是消息认证码函数;(6) Calculate partial ciphertext C 3 =MAC(K 2 , C 2 ) for integrity verification with K 2 , where MAC is a message authentication code function;
(7)得到完整的密文C=(C0,C1,C2,C3),把密文C发送给接收者。(7) Obtain the complete ciphertext C=(C 0 , C 1 , C 2 , C 3 ), and send the ciphertext C to the receiver.
步骤6、解密Step 6. Decryption
接收者收到密文C=(C0,C1,C2,C3)后,根据自己的私钥SKID和时间密钥TKID,t,按如下过程解密出明文消息M:After receiving the ciphertext C=(C 0 , C 1 , C 2 , C 3 ), the receiver decrypts the plaintext message M according to its own private key SK ID and time key TK ID, t according to the following process:
(1)计算双线性映射e(C0,SKID)和e(C1,TKID,t)的乘积,记为W,具体计算公式为W=e(C0,SKID)e(C1,TKID,t);(1) Calculate the product of the bilinear mapping e(C 0 , SK ID ) and e(C 1 , TK ID, t ), denoted as W, and the specific calculation formula is W=e(C 0 , SK ID )e( C 1 , TK ID, t );
(2)根据W计算临时会话密钥K=KDF(C0,C1,W,ID,Klen)=K1||K2;(2) Calculate the temporary session key K=KDF(C 0 , C 1 , W, ID, Klen)=K 1 ||K 2 according to W;
(3)根据K2计算C′3=MAC(K2,C2),并验证C′3是否等于C3,如果相等,则按公式计算出消息M,否则输出“密文无效”。(3) Calculate C′ 3 =MAC(K 2 , C 2 ) according to K 2 , and verify whether C′ 3 is equal to C 3 , if it is equal, follow the formula Calculate the message M, otherwise output "invalid ciphertext".
Claims (5)
Priority Applications (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN201711265792.5A CN109873699B (en) | 2017-12-05 | 2017-12-05 | Revocable identity public key encryption method |
Applications Claiming Priority (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN201711265792.5A CN109873699B (en) | 2017-12-05 | 2017-12-05 | Revocable identity public key encryption method |
Publications (2)
| Publication Number | Publication Date |
|---|---|
| CN109873699A CN109873699A (en) | 2019-06-11 |
| CN109873699B true CN109873699B (en) | 2021-09-28 |
Family
ID=66916236
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| CN201711265792.5A Active CN109873699B (en) | 2017-12-05 | 2017-12-05 | Revocable identity public key encryption method |
Country Status (1)
| Country | Link |
|---|---|
| CN (1) | CN109873699B (en) |
Families Citing this family (13)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN110932847A (en) * | 2019-10-18 | 2020-03-27 | 中国科学院信息工程研究所 | A user revocation method for identity identification cryptosystem with ciphertext homomorphism |
| CN112818362B (en) * | 2021-01-29 | 2023-09-22 | 江苏理工学院 | Public key encryption method based on R-LWE |
| CN113098683B (en) * | 2021-03-17 | 2022-05-03 | 武汉理工大学 | Data encryption method and system based on attributes |
| CN113852466B (en) * | 2021-09-29 | 2023-05-09 | 福建师范大学 | User revocation method based on national secret SM9 |
| CN114757685A (en) * | 2022-04-12 | 2022-07-15 | 嘉应学院 | Shaddock agricultural product processing safety tracing method and system |
| CN115834058B (en) * | 2022-12-23 | 2025-08-15 | 南方电网数字电网研究院股份有限公司 | Communication encryption method, device and computer equipment |
| CN116260591B (en) * | 2023-01-12 | 2025-08-15 | 武汉大学 | SM9 group signature generation and verification method and system supporting membership revocation |
| CN116436634A (en) * | 2023-02-27 | 2023-07-14 | 陕西师范大学 | Cloud-assisted Internet of Things content subscription fine-grained access control method |
| CN117118598B (en) * | 2023-03-14 | 2024-12-31 | 荣耀终端有限公司 | Data sharing method, electronic equipment and computer cluster |
| CN116579005B (en) * | 2023-07-10 | 2023-09-19 | 西安银信博锐信息科技有限公司 | User data safety storage management method |
| CN117834312B (en) * | 2024-03-06 | 2024-06-28 | 鼎铉商用密码测评技术(深圳)有限公司 | Network access method, network access device, and computer-readable storage medium |
| CN118018310B (en) * | 2024-03-11 | 2024-09-17 | 区块链新科技(广州)有限公司 | Revocable identity-based key encryption method, storage medium and device |
| CN118432946B (en) * | 2024-07-03 | 2024-10-01 | 长春吉大正元信息技术股份有限公司 | Lightweight password application method and device and password application service system |
Citations (4)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| EP2009568A3 (en) * | 2007-06-27 | 2009-01-14 | Hitachi Ltd. | Biometric authentication |
| CN103560882A (en) * | 2013-10-29 | 2014-02-05 | 武汉理工大学 | Elliptic curve cryptosystem based on identity |
| CN105024821A (en) * | 2015-07-13 | 2015-11-04 | 西安理工大学 | Reversible Identity-Based Encryption on Lattice |
| CN106789042A (en) * | 2017-02-15 | 2017-05-31 | 西南交通大学 | User in IBC domains accesses the authentication key agreement method of the resource in PKI domains |
Family Cites Families (1)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US9160723B2 (en) * | 2013-01-14 | 2015-10-13 | Arris Technology, Inc. | Framework for provisioning devices with externally acquired component-based identity data |
-
2017
- 2017-12-05 CN CN201711265792.5A patent/CN109873699B/en active Active
Patent Citations (4)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| EP2009568A3 (en) * | 2007-06-27 | 2009-01-14 | Hitachi Ltd. | Biometric authentication |
| CN103560882A (en) * | 2013-10-29 | 2014-02-05 | 武汉理工大学 | Elliptic curve cryptosystem based on identity |
| CN105024821A (en) * | 2015-07-13 | 2015-11-04 | 西安理工大学 | Reversible Identity-Based Encryption on Lattice |
| CN106789042A (en) * | 2017-02-15 | 2017-05-31 | 西南交通大学 | User in IBC domains accesses the authentication key agreement method of the resource in PKI domains |
Non-Patent Citations (3)
| Title |
|---|
| Signing a Linear Subspace Signature Schemes for Network Coding;Dan Boneh.;《PKC 2009-Public Key Cryptography》;20091231;全文 * |
| 无双线性对的可撤销的无证书加密;孙银霞;《南京师大学报(自然科学版)》;20151231;第38卷(第4期);第1-4节 * |
| 第3部分 密钥交换协议;国家密码管理局;《SM9标识密码算法》;20160328;第3部分 * |
Also Published As
| Publication number | Publication date |
|---|---|
| CN109873699A (en) | 2019-06-11 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| CN109873699B (en) | Revocable identity public key encryption method | |
| CN108989053B (en) | Method for realizing certificateless public key cryptosystem based on elliptic curve | |
| CN108173639B (en) | A Two-Party Cooperative Signature Method Based on SM9 Signature Algorithm | |
| CN104270249B (en) | It is a kind of from the label decryption method without certificate environment to identity-based environment | |
| CN108418686B (en) | A multi-distributed SM9 decryption method and medium and key generation method and medium | |
| CN104539423B (en) | A kind of implementation method without CertPubKey cipher system of no Bilinear map computing | |
| JP4527358B2 (en) | An authenticated individual cryptographic system that does not use key escrow | |
| CN104301108B (en) | It is a kind of from identity-based environment to the label decryption method without certificate environment | |
| CN101594228B (en) | Authentication encryption method between certificate public key system and identity public key system | |
| CN110120939B (en) | Encryption method and system capable of repudiation authentication based on heterogeneous system | |
| CN103746811B (en) | Anonymous signcryption method from identity public key system to certificate public key system | |
| CN108880796B (en) | Efficient outsourcing decryption method for server based on attribute encryption algorithm | |
| CN110113155B (en) | An efficient certificateless public key encryption method | |
| CN107947913A (en) | The anonymous authentication method and system of a kind of identity-based | |
| CN104168114A (en) | Distributed type (k, n) threshold certificate-based encrypting method and system | |
| CN107086912B (en) | Ciphertext conversion method, decryption method and system in heterogeneous storage system | |
| CN102970144B (en) | The authentication method of identity-based | |
| CN104868993A (en) | Two-side authentication key negotiation method and system based on certificate | |
| CN104519071A (en) | Group encryption and decryption method and system with selection and exclusion functions | |
| CN104796260B (en) | A kind of short ciphertext identity base encryption method for meeting forward secrecy | |
| CN114598460A (en) | Multi-receiver signcryption method based on SM9 | |
| CN107682158B (en) | A Managed Authenticated Encryption Method | |
| CN103746810B (en) | Anonymous sign-cryption method from certificate public key system to identity public key system | |
| CN104283667B (en) | A kind of data transmission method, apparatus and system | |
| Zhang et al. | New application of partitioning methodology: Identity‐based dual receiver encryption |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| PB01 | Publication | ||
| PB01 | Publication | ||
| SE01 | Entry into force of request for substantive examination | ||
| SE01 | Entry into force of request for substantive examination | ||
| GR01 | Patent grant | ||
| GR01 | Patent grant |