CN109068325B - Key management and identity authentication method based on wireless sensor network - Google Patents
Key management and identity authentication method based on wireless sensor network Download PDFInfo
- Publication number
- CN109068325B CN109068325B CN201811265025.9A CN201811265025A CN109068325B CN 109068325 B CN109068325 B CN 109068325B CN 201811265025 A CN201811265025 A CN 201811265025A CN 109068325 B CN109068325 B CN 109068325B
- Authority
- CN
- China
- Prior art keywords
- node
- key
- requested
- information
- communication
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Active
Links
- 238000000034 method Methods 0.000 title claims abstract description 36
- 238000004891 communication Methods 0.000 claims abstract description 73
- 239000011159 matrix material Substances 0.000 claims description 39
- 230000008569 process Effects 0.000 claims description 11
- 238000012795 verification Methods 0.000 claims description 9
- 230000004083 survival effect Effects 0.000 claims description 3
- 230000000737 periodic effect Effects 0.000 claims description 2
- 230000007246 mechanism Effects 0.000 description 14
- 230000006870 function Effects 0.000 description 6
- 238000005516 engineering process Methods 0.000 description 3
- 230000003068 static effect Effects 0.000 description 3
- 238000010586 diagram Methods 0.000 description 2
- 238000012986 modification Methods 0.000 description 2
- 230000004048 modification Effects 0.000 description 2
- 238000012544 monitoring process Methods 0.000 description 2
- 238000011160 research Methods 0.000 description 2
- 230000002776 aggregation Effects 0.000 description 1
- 238000004220 aggregation Methods 0.000 description 1
- 230000009286 beneficial effect Effects 0.000 description 1
- 230000007547 defect Effects 0.000 description 1
- 230000007812 deficiency Effects 0.000 description 1
- 230000008447 perception Effects 0.000 description 1
- 238000012545 processing Methods 0.000 description 1
Images
Classifications
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04W—WIRELESS COMMUNICATION NETWORKS
- H04W12/00—Security arrangements; Authentication; Protecting privacy or anonymity
- H04W12/02—Protecting privacy or anonymity, e.g. protecting personally identifiable information [PII]
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/08—Key distribution or management, e.g. generation, sharing or updating, of cryptographic keys or passwords
- H04L9/0861—Generation of secret information including derivation or calculation of cryptographic keys or passwords
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/32—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials
- H04L9/3297—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials involving time stamps, e.g. generation of time stamps
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04W—WIRELESS COMMUNICATION NETWORKS
- H04W12/00—Security arrangements; Authentication; Protecting privacy or anonymity
- H04W12/04—Key management, e.g. using generic bootstrapping architecture [GBA]
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04W—WIRELESS COMMUNICATION NETWORKS
- H04W12/00—Security arrangements; Authentication; Protecting privacy or anonymity
- H04W12/06—Authentication
Landscapes
- Engineering & Computer Science (AREA)
- Computer Security & Cryptography (AREA)
- Computer Networks & Wireless Communication (AREA)
- Signal Processing (AREA)
- Mobile Radio Communication Systems (AREA)
Abstract
本发明公开一种基于无线传感器网络的密钥管理和身份认证方法,包括如下步骤:S1、建立含有多个邻近节点五元组信息的矩阵M;S2、判断请求节点是否被纳入矩阵M中内,若是则转向S3,否则转向S5;S3、判断请求节点的五元组信息是否有效,若是则转向S4,否则拒绝通信;S4、被请求节点与请求节点通过密钥分发中心进行身份验证,生成配对密钥;S5、根据请求节点和被请求节点各自的通信区域找寻中继节点,然后分别对中继节点和请求节点之间重复S3到S4,对中继节点和被请求节点之间重复S3和S4。本发明能够达到降低节点资源存储消耗,提高节点间前后向安全,抗重放攻击的目的。
The invention discloses a method for key management and identity authentication based on a wireless sensor network. , if so, turn to S3, otherwise turn to S5; S3, determine whether the quintuple information of the requesting node is valid, if so, turn to S4, otherwise refuse to communicate; S4, the requested node and the requesting node are authenticated by the key distribution center, generating pairing key; S5, find the relay node according to the respective communication areas of the requesting node and the requested node, and then repeat S3 to S4 for the relay node and the requesting node respectively, and repeat S3 for the relay node and the requested node. and S4. The invention can achieve the purpose of reducing the node resource storage consumption, improving the forward and backward security between nodes, and resisting replay attacks.
Description
技术领域technical field
本发明属于无线通信技术领域,具体涉及一种基于无线传感器网络的密钥管理和身份认证方法。The invention belongs to the technical field of wireless communication, and in particular relates to a key management and identity authentication method based on a wireless sensor network.
背景技术Background technique
无线传感器网络是由一组大量资源受限的传感器节点组成,它们以自组网的形式,彼此通过无线通信网络协同工作,已经在多个领域得到了广泛应用。无线传感器网络综合了传感器技术、无线通信技术等在内的多项技术,能够协同地实现实时感知、采集、聚合、处理分布区域内的各种监测信息,并发送到需要这些信息的用户,从而使用户可以实现对物理环境的动态智能感知。A wireless sensor network is composed of a large number of resource-constrained sensor nodes, which cooperate with each other in the form of an ad hoc network through a wireless communication network, and have been widely used in many fields. The wireless sensor network integrates a number of technologies including sensor technology and wireless communication technology, and can collaboratively realize real-time perception, collection, aggregation, and processing of various monitoring information in the distribution area, and send it to users who need this information. Enables users to achieve dynamic intellisense of the physical environment.
在无线传感器网络中,无线通信的物理特殊性要求通信的安全性,而资源约束的传感器节点则需要轻量级且高效安全的实现方案。目前外绝大多数的加密方案都依托于密钥的安全性,密钥的泄露往往会导致明文内容的泄露。因而对密钥的有效管理则是无线传感器网络安全的重要内容。In wireless sensor networks, the physical particularity of wireless communication requires communication security, while resource-constrained sensor nodes require lightweight, efficient and secure implementations. At present, the vast majority of encryption schemes rely on the security of the key, and the disclosure of the key often leads to the disclosure of the plaintext content. Therefore, the effective management of keys is an important content of wireless sensor network security.
无线传感器网络的密钥管理方案与网络性质和密钥的分配方法息息相关。根据不同的网络结构,可以分为分布式的密钥管理机制和层次结构的密钥管理机制。分布式的密钥管理机制对于网络没有特定的要求,各节点通过密钥的预分配机制实现节点间的密钥管理。层次结构的密钥管理机制是基于分簇的网络拓扑结构实现密钥的分配与管理。此外,根据不同的网络环境,可以分为静态网络密钥管理机制和动态网络结构密钥管理机制。静态网络密钥管理机制考虑的是网络或者节点保持不变的特殊情况;动态网络密钥管理机制则考虑网络和节点发生更新的情况。不同的密钥分配方案也产生了随机性密钥和确定性密钥这两种不同的分配机制。随机性密钥分配机制是指密钥概率性地由密钥池中的某些子密钥随机生成,而确定性密钥分配机制是指某些特定的节点直接产生密钥。The key management scheme of wireless sensor network is closely related to the nature of the network and the distribution method of keys. According to different network structures, it can be divided into distributed key management mechanism and hierarchical key management mechanism. The distributed key management mechanism has no specific requirements for the network, and each node implements key management between nodes through the key pre-distribution mechanism. The key management mechanism of the hierarchical structure realizes the distribution and management of keys based on the clustered network topology. In addition, according to different network environments, it can be divided into static network key management mechanism and dynamic network structure key management mechanism. The static network key management mechanism considers the special case that the network or node remains unchanged; the dynamic network key management mechanism considers the situation that the network and the node are updated. Different key distribution schemes also produce two different distribution mechanisms, random keys and deterministic keys. The random key distribution mechanism means that the key is randomly generated by some sub-keys in the key pool, while the deterministic key distribution mechanism means that some specific nodes directly generate the key.
目前国内外关于无线传感器网络密钥预分配和密钥管理的研究中,存在两种研究思路:基于随机概率密钥预分配方案和基于地理位置信息、身份信息的密钥预分配方案。基于随机概率的密钥预分配方案需要存储大量的无效密钥,资源存储消耗较大;基于位置身份信息的密钥预分配方案需要大量的计算消耗,缺少节点的认证机制。At present, there are two research ideas in the research on wireless sensor network key pre-distribution and key management at home and abroad: the key pre-distribution scheme based on random probability and the key pre-distribution scheme based on geographic location information and identity information. The key pre-distribution scheme based on random probability needs to store a large number of invalid keys, and the resource storage consumption is large; the key pre-distribution scheme based on location identity information requires a lot of computational consumption and lacks the authentication mechanism of nodes.
现有的基于无线传感器的密钥管理方案在密钥预分配阶段依然需要消耗大量的存储空间存放无用密钥,共享密钥的重叠性降低了网络的可扩展性;在生成会话密钥/配对密钥的时候,并没有及时考虑认证机制,节点间生成配对密钥的前提是节点的合法性;大部分的密钥管理方案都是基于静态网络,动态网络的效率较低。The existing wireless sensor-based key management scheme still needs to consume a lot of storage space to store useless keys in the key pre-distribution stage, and the overlapping of shared keys reduces the scalability of the network; When generating keys, the authentication mechanism is not considered in time. The premise of generating paired keys between nodes is the legitimacy of the nodes; most key management schemes are based on static networks, and dynamic networks are less efficient.
综上所述,针对现有技术的缺陷,特别需要一种基于无线传感器网络的密钥管理和身份认证方案,解决上面所提到的问题。To sum up, in view of the defects of the prior art, a key management and identity authentication scheme based on a wireless sensor network is particularly required to solve the above-mentioned problems.
发明内容SUMMARY OF THE INVENTION
本发明的目的在于克服现有技术中的不足,提供一种基于无线传感器网络的密钥管理和身份认证方法,能够达到降低节点资源存储消耗,提高节点间前后向安全,抗重放攻击的目的。The purpose of the present invention is to overcome the deficiencies in the prior art and provide a key management and identity authentication method based on a wireless sensor network, which can achieve the purpose of reducing node resource storage consumption, improving forward and backward security between nodes, and resisting replay attacks. .
为解决现有技术问题,本发明公开了一种基于无线传感器网络的密钥管理和身份认证方法,包括如下步骤:In order to solve the problems of the prior art, the present invention discloses a method for key management and identity authentication based on a wireless sensor network, comprising the following steps:
S1、建立含有多个邻近节点五元组信息的矩阵M;S1, establish a matrix M containing multiple adjacent node quintuple information;
S2、判断请求节点是否被纳入矩阵M中内,若是则转向S3,否则转向S5;S2, determine whether the request node is included in the matrix M, if so, go to S3, otherwise go to S5;
S3、判断请求节点的五元组信息是否有效,若是则转向S4,否则拒绝通信;S3, determine whether the quintuple information of the requesting node is valid, if so, turn to S4, otherwise refuse communication;
S4、被请求节点与请求节点通过密钥分发中心进行身份验证,生成配对密钥;S4, the requested node and the requesting node perform identity verification through the key distribution center to generate a pairing key;
S5、根据请求节点和被请求节点各自的通信区域找寻中继节点,然后分别对中继节点和请求节点之间重复S3到S4,对中继节点和被请求节点之间重复S3和S4。S5. Find the relay node according to the respective communication areas of the requesting node and the requested node, and then repeat S3 to S4 for the relay node and the requesting node respectively, and repeat S3 and S4 for the relay node and the requested node.
作为优选方案,As a preferred option,
S1中,矩阵M的建立方法如下:In S1, the establishment method of matrix M is as follows:
S11、动态生成被请求节点的通信阈值和邻近节点阈值;S11. Dynamically generate the communication threshold of the requested node and the adjacent node threshold;
S12、根据通信阈值和邻近节点阈值生成矩阵M;S12, generate a matrix M according to the communication threshold and the adjacent node threshold;
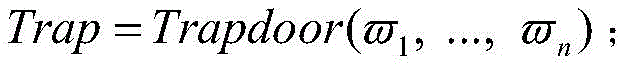
矩阵M表达式为其中q表示被请求节点的邻近节点阈值;Loc表示该节点的位置信息;AT表示该节点的存活标志,其值为0表示存活,为1表示新增,为-1表示休眠,为其它负值表示被撤销;CT表示该节点最近与被请求节点的通信认证次数;TT表示该节点有效时间的时间戳;RT表示属于通信阈值范围内,但未被纳入节点矩阵M的邻近节点的合法通信请求次数。The matrix M is expressed as Among them, q represents the adjacent node threshold of the requested node; Loc represents the location information of the node; AT represents the survival flag of the node, its value is 0 means alive, 1 means new, -1 means dormant, and other negative values means revoked; CT means the number of recent communication authentications between the node and the requested node; TT means the timestamp of the valid time of the node; RT means legal communication requests from neighboring nodes that are within the communication threshold range but not included in the node matrix M frequency.
作为优选方案,As a preferred option,
S2中,判断请求节点是否被纳入矩阵M中内的方法如下:In S2, the method for judging whether the request node is included in the matrix M is as follows:
S21、被请求节点根据矩阵M建立门限函数,根据邻近节点的请求信息生成门限值;S21, the requested node establishes a threshold function according to the matrix M, and generates a threshold value according to the request information of the adjacent nodes;
S22、判断门限值是否满足要求,若是则认定请求节点已纳入矩阵M中,否则认定未纳入矩阵M中。S22 , judging whether the threshold value meets the requirements, and if so, it is determined that the requesting node has been included in the matrix M; otherwise, it is determined that it has not been included in the matrix M.
作为优选方案,As a preferred option,
S3中,若请求节点的时间戳有效且无其它无效状态则认定该节点有效,否则认定其无效。In S3, if the timestamp of the requesting node is valid and there is no other invalid state, the node is deemed valid, otherwise it is deemed invalid.
作为优选方案,As a preferred option,
S4中,被请求节点与请求节点通过密钥分发中心进行身份验证,生成配对密钥的方法如下:In S4, the requested node and the requesting node perform identity verification through the key distribution center, and the method for generating the pairing key is as follows:
S41、请求节点向被请求节点发送认证请求的加密信息;S41, the requesting node sends the encrypted information of the authentication request to the requested node;
S42、请求节点向密钥分发中心请求分发会话密钥,并发送本轮通信的相关信息;S42, the requesting node requests the key distribution center to distribute the session key, and sends the relevant information of the current round of communication;
S43、被请求节点向密钥分发中心请求分发会话密钥,并发送本轮通信的相关信息;S43, the requested node requests the key distribution center to distribute the session key, and sends the relevant information of this round of communication;
S44、密钥分发中心分别向请求节点发送用于验证的加密信息,向被请求节点发送包含会话密钥的加密信息;S44, the key distribution center sends encrypted information for verification to the requesting node respectively, and sends encrypted information including the session key to the requested node;
S45、被请求节点解密获知会话密钥,并将会话密钥加密验证信息发送给请求节点;S45, the requested node decrypts to learn the session key, and sends the encrypted verification information of the session key to the requesting node;
S46、节点双方根据认证过程中的中间值生成配对密钥。S46. Both nodes generate a pairing key according to the intermediate value in the authentication process.
作为优选方案,As a preferred option,
S41中,请求节点将自己的位置信息加密请求信息发送给被请求节点;In S41, the requesting node sends its own location information encryption request information to the requested node;
S42中,请求节点向密钥分发中心发送两个加密信息,其一是用自己身份信息加密的随机值;其二是用请求节点和密钥分发中心共享的主密钥加密的数据信息,该数据信息包括自身的身份信息、通信的有效期限和本轮通信的临时会话随机值;请求节点的临时会话随机值由请求节点选取本轮通信的两个随机数,以及其身份信息和时间戳生成;In S42, the requesting node sends two encrypted messages to the key distribution center, one is a random value encrypted with its own identity information; the other is data information encrypted with the master key shared by the requesting node and the key distribution center, the The data information includes its own identity information, the validity period of the communication, and the temporary session random value of the current round of communication; the temporary session random value of the requesting node is generated by the requesting node selecting the two random numbers of this round of communication, as well as its identity information and timestamp. ;
S43中,被请求节点向密钥分发中心发送两个加密信息,其一是用自己身份信息加密的随机值;其二是用被请求节点和密钥分发中心共享的主密钥加密的数据信息,该数据信息包括自身的身份信息和本轮通信的临时会话随机值;被请求节点的临时会话随机值由被请求节点选取本轮通信的两个随机数,以及其身份信息生成;In S43, the requested node sends two encrypted messages to the key distribution center, one is a random value encrypted with its own identity information; the other is data information encrypted with the master key shared by the requested node and the key distribution center , the data information includes its own identity information and the temporary session random value of the current round of communication; the temporary session random value of the requested node is generated by the requested node selecting two random numbers of this round of communication and its identity information;
S44中,密钥分发中心收到被请求节点和请求节点的会话请求后,首先解密获取两个节点的身份信息,与预存的身份信息比较,再解密两个节点的随机值,用以盲化两个节点的身份信息;并将密钥分发中心和请求节点共享的主密钥加密数据发送给请求节点,用于间接告知被请求节点的身份信息;该过程中,密钥分发中心已经获知请求节点本轮的临时会话随机值和被请求节点的时间戳;In S44, after receiving the session request from the requested node and the requesting node, the key distribution center first decrypts and obtains the identity information of the two nodes, compares it with the pre-stored identity information, and then decrypts the random values of the two nodes for blinding The identity information of the two nodes; and the encrypted data of the master key shared by the key distribution center and the requesting node is sent to the requesting node to indirectly inform the identity information of the requested node; in this process, the key distribution center has been informed of the request The random value of the temporary session of the node in this round and the timestamp of the requested node;
密钥分发中心发送请求节点的临时随机值以及用密钥分发中心和请求节点共享的主密钥加密的数据信息给被请求节点,该部分作为安全凭证用于被请求节点的认证和生成两个节点通信的密钥;同时,密钥分发中心也发送密钥分发中心与被请求节点共享的主密钥加密的数据信息,该部分包括请求节点的身份信息、一个没有重放且及时的消息,也提供给被请求节点一个会话密钥及请求节点的时间戳;The key distribution center sends the temporary random value of the requesting node and the data information encrypted with the master key shared by the key distribution center and the requesting node to the requested node, which is used as a security credential for the authentication of the requested node and the generation of two At the same time, the key distribution center also sends the data information encrypted by the master key shared by the key distribution center and the requested node, this part includes the identity information of the requesting node, a message that is not replayed and timely, Also provide the requested node with a session key and the timestamp of the requesting node;
S45中,被请求节点把加密的数据信息和请求节点的临时会话随机值一起发送给请求节点,请求节点的临时会话随机值使用会话密钥加密;加密的数据信息提供给请求节点解密密钥以恢复临时随机值;请求节点的临时随机值用会话密钥加密保证该消息不是重放;In S45, the requested node sends the encrypted data information and the temporary session random value of the requesting node to the requesting node, and the temporary session random value of the requesting node is encrypted with the session key; the encrypted data information is provided to the requesting node decryption key to Restore the temporary random value; the temporary random value of the requesting node is encrypted with the session key to ensure that the message is not replayed;
S46中,由安全凭证的加密信息和被请求节点的临时会话随机值取哈希值得到两个节点本轮的配对密钥。In S46, the pairing key of the current round of the two nodes is obtained by taking the hash value of the encrypted information of the security credential and the random value of the temporary session of the requested node.
作为优选方案,As a preferred option,
S5中,根据请求节点和被请求节点各自的通信区域找寻中继节点的方法如下:In S5, the method for finding a relay node according to the respective communication areas of the requesting node and the requested node is as follows:
确定两个节点的通信区域,若有重合区域或重合候选节点则依据欧几里得距离单跳最小标准差路径原则选择中继节点;否则选择两个区域的边界处的节点继续确定通信区域,然后根据节点矩阵M寻找重合区域或重合候选节点,重复该过程知道找到中继节点。Determine the communication area of the two nodes. If there is an overlapping area or an overlapping candidate node, the relay node is selected according to the Euclidean distance single-hop minimum standard deviation path principle; otherwise, the node at the boundary of the two areas is selected to continue to determine the communication area. Then, according to the node matrix M, the coincidence area or the coincidence candidate node is searched, and the process is repeated until the relay node is found.
作为优选方案,As a preferred option,
S5中,跳表通信次数最多有三次。In S5, the number of times of skip table communication is at most three times.
作为优选方案,As a preferred option,
身份认证结束后,被请求节点会修改请求节点的门限值,并检查是否有节点无效或者时间戳过期;如果存在,就删除该节点,并选择请求次数最高的节点加入通信节点矩阵M,同时修改相应矩阵的值。After the identity authentication is completed, the requested node will modify the threshold value of the requesting node, and check whether any node is invalid or the timestamp has expired; if there is, delete the node, and select the node with the highest number of requests to join the communication node matrix M, and at the same time Modify the values of the corresponding matrix.
作为优选方案,As a preferred option,
每次系统的时间戳过期,会重新广播发送新一轮的时间戳、随机数和新的哈希函数;被请求节点只需相应修改的值;新增节点会获取本时间周期和上一个时间周期的有效信息,参与新一轮的身份认证。Every time the timestamp of the system expires, a new round of timestamp, random number and new hash function will be re-broadcasted; the requested node only needs to modify the value accordingly; the new node will obtain the current time period and the previous time Periodic valid information to participate in a new round of identity authentication.
本发明具有的有益效果:通过采用节点矩阵的形式,无需构建密钥池存储大量无用的密钥,每个节点存储可以直接单跳节点的信息,矩阵根据节点位置信息、合法性状态和活跃度进行更新,并采用哈希函数和时间戳的方法保证系统的时效性,提高了防监听、抗节点捕获攻击和抗重放攻击的能力。此外,认证过程无需知晓各个节点的具体身份信息,保障节点的隐私性。The invention has the beneficial effects: by adopting the form of a node matrix, there is no need to build a key pool to store a large number of useless keys, and each node stores the information of a single-hop node directly. It is updated, and the method of hash function and time stamp is used to ensure the timeliness of the system, which improves the ability of anti-monitoring, anti-node capture attack and anti-replay attack. In addition, the authentication process does not need to know the specific identity information of each node, ensuring the privacy of the node.
附图说明Description of drawings
图1是本发明中节点网络模型示意图;1 is a schematic diagram of a node network model in the present invention;
图2是本发明中节点间身份认证过程的示意图。FIG. 2 is a schematic diagram of an identity authentication process between nodes in the present invention.
具体实施方式Detailed ways
下面结合附图对本发明作进一步描述。以下实施例仅用于更加清楚地说明本发明的技术方案,而不能以此来限制本发明的保护范围。The present invention will be further described below in conjunction with the accompanying drawings. The following examples are only used to illustrate the technical solutions of the present invention more clearly, and cannot be used to limit the protection scope of the present invention.
如图1所示,以节点A为被请求节点、节点B为请求节点为例具体阐述两个节点之间的认证过程。As shown in FIG. 1 , the authentication process between the two nodes is specifically described by taking the node A as the requested node and the node B as the requesting node as an example.
S1、建立含有多个邻近节点五元组信息的矩阵M,具体步骤如下:S1. Establish a matrix M containing quintuple information of multiple adjacent nodes, and the specific steps are as follows:
S11、系统动态设定节点A的通信阈值,该通信阈值是基于节点A的电源能量和通信能力设置的通信范围,确保节点间的通信半径为r。设定节点A的邻近节点阈值q,其表示每个节点最多可以与q个邻近节点通信。S11. The system dynamically sets the communication threshold of node A, where the communication threshold is a communication range set based on the power energy and communication capability of node A, to ensure that the communication radius between nodes is r. Set the neighbor node threshold q of node A, which means that each node can communicate with at most q neighbor nodes.
根据阈值限制,可以确定通信阈值范围内的所有节点,并通过定位算法获取它们的位置信息。这些信息均为部署区域内的公开信息,并且这些节点可以与节点A直接单跳通信,部署区域以外的节点无法直接单跳通信。According to the threshold limit, all nodes within the communication threshold range can be determined, and their location information can be obtained through the positioning algorithm. These information are all public information in the deployment area, and these nodes can directly communicate with node A in a single hop, and nodes outside the deployment area cannot directly communicate in a single hop.
S12、根据通信阈值和邻近节点阈值生成节点A的通信节点矩阵M,其表达式为:S12, generate the communication node matrix M of node A according to the communication threshold and the adjacent node threshold, and its expression is:
其中q表示被请求节点的邻近节点阈值;Loc表示邻近节点的位置信息;AT表示该节点的存活标志,其值为0表示存活,为1表示新增,为-1表示休眠,为其它负值表示被撤销;CT表示该节点最近与被请求节点的通信认证次数;TT表示该节点有效时间的时间戳;RT表示属于通信阈值范围内,但未被纳入节点矩阵M的邻近节点的合法通信请求次数。当有节点被节点矩阵删除时,合法请求次数最高的邻近节点将优先递补进节点矩阵M,其他节点则继续按照请求次数排队,而通信节点矩阵内的节点通信次数值始终为0。系统首次部署时,通信节点矩阵M为空。 Where q represents the adjacent node threshold of the requested node; Loc represents the location information of the adjacent node; AT represents the survival flag of the node, its value is 0 means alive, 1 means new, -1 means dormant, and other negative values means revoked; CT means the number of recent communication authentications between the node and the requested node; TT means the timestamp of the valid time of the node; RT means legal communication requests from neighboring nodes that are within the communication threshold range but not included in the node matrix M frequency. When a node is deleted by the node matrix, the adjacent node with the highest number of legal requests will be preferentially replenished to the node matrix M, and other nodes will continue to queue up according to the number of requests, and the value of the communication times of the nodes in the communication node matrix is always 0. When the system is first deployed, the communication node matrix M is empty.
S2、判断请求节点是否被纳入矩阵M中,具体步骤如下:S2, determine whether the request node is included in the matrix M, the specific steps are as follows:
S21、构建节点A的门限函数并根据邻近节点的请求信息生成门限值,门限函数表达式为:S21. Construct a threshold function of node A and generate a threshold value according to the request information of adjacent nodes. The expression of the threshold function is:
其中,θ=h(λ,TBS),ζ=h(xAIDA),TBS∈BS,xA∈A,λ表示BS基站周期性地分布到每个节点的随机数,无效的节点不会接收到这个值;TBS表示BS的有效时间戳;θ表示BS系统信息的机密值;xA表示节点A选取的随机数,ζ表示节点A盲化的身份信息;表示系统BS时间戳有效期间,有效邻近节点的盲化的位置信息,ξ表示该节点是否属于矩阵M,其值为1表示属于,为0表示不属于;用来计算邻近节点是否可以和节点A直接进行单跳通信。in, θ=h(λ, T BS ), ζ=h(x A ID A ), T BS ∈ BS, x A ∈ A, λ represents the random number periodically distributed to each node by the BS base station, invalid nodes will not receive this value; T BS represents the valid timestamp of the BS; θ represents the BS system information The confidential value of ; x A represents the random number selected by node A, and ζ represents the blinded identity information of node A; Represents the blinded position information of the valid adjacent nodes during the valid period of the system BS timestamp, ξ represents whether the node belongs to the matrix M, and its value is 1 means it belongs, and 0 means it does not belong; It is used to calculate whether adjacent nodes can directly communicate with node A in a single hop.
S22、判断门限值是否满足h((h(λ,TBS),Locx),h(xAIDA))=0,若是则说明节点B在通信范围内,可以与节点A直接单跳通信,否则说明节点B不在通信范围内,其不可以与节点A直接单跳通信,必须通过其它节点间接通信。S22. Determine whether the threshold value satisfies h((h(λ, T BS ), Loc x ), h(x A ID A ))=0, if so, it means that node B is within the communication range and can directly communicate with node A Hop communication, otherwise it means that node B is not within the communication range, it cannot directly communicate with node A in a single hop, and must communicate indirectly through other nodes.
S3、判断节点B的五元组信息是否有效,具体步骤如下:S3. Determine whether the quintuple information of node B is valid, and the specific steps are as follows:
若节点B的时间戳有效,并且节点B非其它无效状态,则节点B可以直接与节点A通信进行身份认证,否则拒绝通信。If the timestamp of node B is valid, and node B is not in other invalid states, then node B can communicate with node A directly for identity authentication, otherwise, the communication is refused.
S4、节点A与节点B通过KDC(密钥分发中心)进行身份验证,生成配对密钥,具体步骤如下:S4. Node A and Node B perform identity verification through the KDC (Key Distribution Center) to generate a pairing key. The specific steps are as follows:
S41中,节点B将自己的位置信息加密请求信息发送给节点A。In S41, node B sends its own location information encryption request information to node A.
S42中,节点B向KDC发送两个加密信息,其一是用自己身份信息加密的随机值,用于KDC向节点A盲化自己的身份信息;其二是用节点B和KDC共享的主密钥KB加密的数据信息,该数据信息包括自身的身份信息、通信的有效期限和本轮通信的临时会话随机值;节点B的临时会话随机值由节点B选取本轮通信的两个随机数,以及其身份信息和时间戳生成。会话密钥和时间戳最后会以加密信息的形式返回给节点B,以确保节点B的实效性。In S42, node B sends two encrypted information to KDC, one is a random value encrypted with its own identity information, which is used by KDC to blind its own identity information to node A; the other is the master secret shared by node B and KDC. The data information encrypted by the key K B , the data information includes its own identity information, the validity period of the communication and the temporary session random value of the current round of communication; the temporary session random value of the node B is selected by the node B. The two random numbers of this round of communication , along with its identity information and timestamp generation. The session key and timestamp are finally returned to Node B in the form of encrypted information to ensure the validity of Node B.
S43中,节点A向KDC发送两个加密信息,其一是用自己身份信息加密的随机值,用于KDC向节点B盲化自己的身份信息;其二是用节点A和KDC共享的主密钥KA加密的数据信息,用于指示KDC需要发送节点A的相关信息给节点B,该数据信息包括自身的身份信息和本轮通信的临时会话随机值;节点A的临时会话随机值由节点A选取本轮通信的两个随机数,以及其身份信息生成。节点A的临时会话随机值也会和会话密钥以加密信息的形式返回给节点A,以确保节点A的实效性。In S43, node A sends two encrypted information to KDC, one is a random value encrypted with its own identity information, which is used by KDC to blind its own identity information to node B; the other is the master secret shared by node A and KDC. The data information encrypted by the key K A is used to indicate that the KDC needs to send the relevant information of the node A to the node B. The data information includes its own identity information and the temporary session random value of the current round of communication; the temporary session random value of the node A is determined by the node B. A selects two random numbers for this round of communication and generates their identity information. Node A's temporary session random value and session key are also returned to node A in the form of encrypted information to ensure node A's effectiveness.
S44中,KDC收到节点A和节点B的会话请求后,首先解密获取两个节点的身份信息,与预存的身份信息比较,再解密两个节点的随机值,用以盲化两个节点的身份信息;并将KDC和节点B共享的主密钥加密数据发送给节点B,用于间接告知节点A的身份信息;该过程中,KDC已经获知节点B本轮的临时会话随机值和节点A的时间戳。In S44, after receiving the session request from node A and node B, the KDC first decrypts and obtains the identity information of the two nodes, compares it with the pre-stored identity information, and then decrypts the random values of the two nodes to blind the two nodes. identity information; and send the encrypted data of the master key shared by KDC and node B to node B, which is used to indirectly inform node A of the identity information; in this process, KDC has already learned the temporary session random value of node B and node A of this round. timestamp.
KDC发送节点B的临时随机值的哈希值以及用KDC和节点B共享的主密钥KB加密的数据信息给节点A,该部分作为安全凭证用于节点A的认证和生成两个节点通信的密钥;同时,KDC也发送KDC与节点A共享的主密钥KA加密的数据信息,该部分包括节点B的身份信息、一个没有重放且及时的消息,也提供给节点A一个会话密钥及节点B的时间戳。The KDC sends the hash value of node B's temporary random value and the data information encrypted with the master key KB shared by KDC and node B to node A. This part is used as a security credential for node A's authentication and generation of two-node communication. At the same time, KDC also sends the data information encrypted by the master key K A shared by KDC and node A, this part includes the identity information of node B, a message that is not replayed and timely, and also provides node A with a session The key and the timestamp of Node B.
S45中,节点A把加密的数据信息和节点B的临时会话随机值一起发送给节点B,节点B的临时会话随机值使用会话密钥加密;加密的数据信息提供给节点B解密密钥以恢复临时随机值;节点B的临时随机值用会话密钥加密保证该消息不是重放。In S45, node A sends the encrypted data information and node B's temporary session random value to node B, and node B's temporary session random value is encrypted with the session key; the encrypted data information is provided to node B's decryption key to recover Temporary random value; Node B's temporary random value is encrypted with the session key to ensure that the message is not replayed.
S46中,由安全凭证的加密信息和节点A的临时会话随机值取哈希值得到两个节点本轮的配对密钥。In S46, the pairing key of the current round of the two nodes is obtained by taking the hash value of the encrypted information of the security credential and the random value of the temporary session of the node A.
S5、根据节点B和节点A各自的通信区域找寻中继节点,然后分别对中继节点和节点B之间重复S3到S4,对中继节点和节点A之间重复S3和S4,具体步骤如下:S5. Find the relay node according to the respective communication areas of node B and node A, and then repeat S3 to S4 between the relay node and node B respectively, and repeat S3 and S4 between the relay node and node A, the specific steps are as follows :
确定两个节点的通信区域,若有重合区域或重合候选节点则依据欧几里得距离单跳最小标准差路径原则选择中继节点;否则选择两个区域的边界处的节点继续确定通信区域,然后根据节点矩阵M寻找重合区域或重合候选节点,重复该过程知道找到中继节点。S5中,无线传感器网络中的跳表通信次数最多有三次。Determine the communication area of the two nodes. If there is an overlapping area or an overlapping candidate node, the relay node is selected according to the Euclidean distance single-hop minimum standard deviation path principle; otherwise, the node at the boundary of the two areas is selected to continue to determine the communication area. Then, according to the node matrix M, the coincidence area or the coincidence candidate node is searched, and the process is repeated until the relay node is found. In S5, the number of times of skip table communication in the wireless sensor network is at most three times.
身份认证结束后,节点A会修改节点B的门限值,并检查是否有节点无效或者时间戳过期;如果存在,就删除该节点,并选择请求次数最高的节点加入通信节点矩阵M,同时修改相应矩阵的值。After identity authentication, node A will modify the threshold value of node B, and check whether any node is invalid or the timestamp has expired; if it exists, it will delete the node, and select the node with the highest number of requests to join the communication node matrix M, and modify it at the same time. the value of the corresponding matrix.
每次系统的时间戳过期,会重新广播发送新一轮的时间戳、随机数和新的哈希函数;节点A只需修改相应的值;新增节点会获取本时间周期和上一个时间周期的有效信息,参与新一轮的身份认证。Every time the timestamp of the system expires, a new round of timestamp, random number and new hash function will be re-broadcasted; node A only needs to modify the corresponding value; the new node will obtain the current time period and the previous time period valid information to participate in a new round of identity authentication.
以上所述仅是本发明的优选实施方式,应当指出,对于本技术领域的普通技术人员来说,在不脱离本发明技术原理的前提下,还可以做出若干改进和变形,这些改进和变形也应视为本发明的保护范围。The above are only the preferred embodiments of the present invention. It should be pointed out that for those skilled in the art, without departing from the technical principles of the present invention, several improvements and modifications can be made. These improvements and modifications It should also be regarded as the protection scope of the present invention.
Claims (9)
Priority Applications (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN201811265025.9A CN109068325B (en) | 2018-10-29 | 2018-10-29 | Key management and identity authentication method based on wireless sensor network |
Applications Claiming Priority (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN201811265025.9A CN109068325B (en) | 2018-10-29 | 2018-10-29 | Key management and identity authentication method based on wireless sensor network |
Publications (2)
| Publication Number | Publication Date |
|---|---|
| CN109068325A CN109068325A (en) | 2018-12-21 |
| CN109068325B true CN109068325B (en) | 2021-04-16 |
Family
ID=64767556
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| CN201811265025.9A Active CN109068325B (en) | 2018-10-29 | 2018-10-29 | Key management and identity authentication method based on wireless sensor network |
Country Status (1)
| Country | Link |
|---|---|
| CN (1) | CN109068325B (en) |
Families Citing this family (4)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN110708512A (en) * | 2019-10-17 | 2020-01-17 | 烟台艾易新能源有限公司 | Intelligent household wireless network image encryption transmission optimization method |
| CN114499863B (en) * | 2022-04-15 | 2022-08-23 | 深圳市永达电子信息股份有限公司 | Multi-party authentication method based on time division and space division and computer readable storage medium |
| CN115550002B (en) * | 2022-09-20 | 2024-05-24 | 贵州电网有限责任公司 | A smart home remote control method and related device based on TEE |
| CN115348583B (en) * | 2022-10-18 | 2023-01-03 | 中国民航信息网络股份有限公司 | Communication method and system in high-speed mobile scene |
Citations (4)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN101409617A (en) * | 2008-10-08 | 2009-04-15 | 东南大学 | Method for generating inbreak-tolerated wireless sensor network topological |
| CN102395127A (en) * | 2011-11-14 | 2012-03-28 | 北京邮电大学 | Fault recovery method of wireless sensor network |
| CN103825742A (en) * | 2014-02-13 | 2014-05-28 | 南京邮电大学 | Authentication key agreement method applicable to large-scale sensor network |
| CN104093206A (en) * | 2014-07-25 | 2014-10-08 | 中国人民解放军海军航空工程学院 | A Node Self-Location Method for Underwater Sensor Networks Based on Hybrid Constraint Satisfaction |
Family Cites Families (1)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US9301246B2 (en) * | 2012-01-16 | 2016-03-29 | Electronics And Telecommunications Research Institute | Sensor network and method of link extension based on time slot relaying in the same |
-
2018
- 2018-10-29 CN CN201811265025.9A patent/CN109068325B/en active Active
Patent Citations (4)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN101409617A (en) * | 2008-10-08 | 2009-04-15 | 东南大学 | Method for generating inbreak-tolerated wireless sensor network topological |
| CN102395127A (en) * | 2011-11-14 | 2012-03-28 | 北京邮电大学 | Fault recovery method of wireless sensor network |
| CN103825742A (en) * | 2014-02-13 | 2014-05-28 | 南京邮电大学 | Authentication key agreement method applicable to large-scale sensor network |
| CN104093206A (en) * | 2014-07-25 | 2014-10-08 | 中国人民解放军海军航空工程学院 | A Node Self-Location Method for Underwater Sensor Networks Based on Hybrid Constraint Satisfaction |
Non-Patent Citations (2)
| Title |
|---|
| 一类传感器网络密钥预分配方案的设计与实现;梁迎春;《中国优秀硕士学位论文全文数据库 信息科技辑》;20110515(第5期);摘要、第29-43页 * |
| 无线传感器网络密钥管理方案的研究;张涛;《中国优秀硕士学位论文全文数据库 信息科技辑》;20100815(第8期);第14-30页 * |
Also Published As
| Publication number | Publication date |
|---|---|
| CN109068325A (en) | 2018-12-21 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| Albakri et al. | Hierarchical key management scheme with probabilistic security in a wireless sensor network (WSN) | |
| Alimoradi et al. | A hierarchical key management and authentication method for wireless sensor networks | |
| CN102244658B (en) | Partitioned dynamic secure routing method for wireless sensor network based on hash chain | |
| CN109068325B (en) | Key management and identity authentication method based on wireless sensor network | |
| CN103929744B (en) | A kind of key management method of wireless sensor network | |
| CN102131195A (en) | Key Distribution and Management Protocol for Wireless Sensor Networks Based on Multi-Hash Chain | |
| CN102123392B (en) | Secret key management method for distributed wireless sensor network | |
| Morshed et al. | CBSRP: cluster based secure routing protocol | |
| Erfani et al. | A dynamic key management scheme for dynamic wireless sensor networks | |
| Zhang et al. | An efficient and hybrid key management for heterogeneous wireless sensor networks | |
| Ibriq et al. | A secure hierarchical routing protocol for wireless sensor networks | |
| Saraswathi et al. | Dynamic and probabilistic key management for distributed wireless sensor networks | |
| Yan et al. | Secure pervasive social networking based on multi-dimensional trust levels | |
| Aziz et al. | A recent survey on key management schemes in manet | |
| Zhou et al. | An energy-efficient random verification protocol for the detection of node clone attacks in wireless sensor networks | |
| Chorzempa et al. | Key management for long-lived sensor networks in hostile environments | |
| Shi et al. | Self-healing group-wise key distribution schemes with time-limited node revocation for wireless sensor networks | |
| Fernandes et al. | A self-organized mechanism for thwarting malicious access in ad hoc networks | |
| Kavitha et al. | Hybrid cryptographic technique for heterogeneous wireless sensor networks | |
| Rehman et al. | Polynomial based dynamic key management for secure cluster communication in wireless mobile sensor network | |
| Kettaf et al. | An efficient heterogeneous key management approach for secure multicast communications in ad hoc networks | |
| Athanere et al. | A review of chronological development in group and hierarchical key management schemes in access control model: challenges and solutions | |
| Kumar et al. | To enhance security scheme for MANET using HMAC | |
| Hu et al. | Security in wireless actor & sensor networks (WASN): towards a hierarchical re-keying design | |
| Wang et al. | A CFL‐Based Key Management Scheme for Routing‐Driven Internet of Things |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| PB01 | Publication | ||
| PB01 | Publication | ||
| SE01 | Entry into force of request for substantive examination | ||
| SE01 | Entry into force of request for substantive examination | ||
| GR01 | Patent grant | ||
| GR01 | Patent grant |