CN106911470B - A Privacy-enhancing Approach for Bitcoin Transactions - Google Patents
A Privacy-enhancing Approach for Bitcoin Transactions Download PDFInfo
- Publication number
- CN106911470B CN106911470B CN201710050768.3A CN201710050768A CN106911470B CN 106911470 B CN106911470 B CN 106911470B CN 201710050768 A CN201710050768 A CN 201710050768A CN 106911470 B CN106911470 B CN 106911470B
- Authority
- CN
- China
- Prior art keywords
- transaction
- verification
- amount
- receiver
- value
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Active
Links
Images
Classifications
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/08—Key distribution or management, e.g. generation, sharing or updating, of cryptographic keys or passwords
- H04L9/0816—Key establishment, i.e. cryptographic processes or cryptographic protocols whereby a shared secret becomes available to two or more parties, for subsequent use
- H04L9/0819—Key transport or distribution, i.e. key establishment techniques where one party creates or otherwise obtains a secret value, and securely transfers it to the other(s)
- H04L9/0825—Key transport or distribution, i.e. key establishment techniques where one party creates or otherwise obtains a secret value, and securely transfers it to the other(s) using asymmetric-key encryption or public key infrastructure [PKI], e.g. key signature or public key certificates
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06Q—INFORMATION AND COMMUNICATION TECHNOLOGY [ICT] SPECIALLY ADAPTED FOR ADMINISTRATIVE, COMMERCIAL, FINANCIAL, MANAGERIAL OR SUPERVISORY PURPOSES; SYSTEMS OR METHODS SPECIALLY ADAPTED FOR ADMINISTRATIVE, COMMERCIAL, FINANCIAL, MANAGERIAL OR SUPERVISORY PURPOSES, NOT OTHERWISE PROVIDED FOR
- G06Q20/00—Payment architectures, schemes or protocols
- G06Q20/02—Payment architectures, schemes or protocols involving a neutral party, e.g. certification authority, notary or trusted third party [TTP]
- G06Q20/023—Payment architectures, schemes or protocols involving a neutral party, e.g. certification authority, notary or trusted third party [TTP] the neutral party being a clearing house
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06Q—INFORMATION AND COMMUNICATION TECHNOLOGY [ICT] SPECIALLY ADAPTED FOR ADMINISTRATIVE, COMMERCIAL, FINANCIAL, MANAGERIAL OR SUPERVISORY PURPOSES; SYSTEMS OR METHODS SPECIALLY ADAPTED FOR ADMINISTRATIVE, COMMERCIAL, FINANCIAL, MANAGERIAL OR SUPERVISORY PURPOSES, NOT OTHERWISE PROVIDED FOR
- G06Q20/00—Payment architectures, schemes or protocols
- G06Q20/04—Payment circuits
- G06Q20/06—Private payment circuits, e.g. involving electronic currency used among participants of a common payment scheme
- G06Q20/065—Private payment circuits, e.g. involving electronic currency used among participants of a common payment scheme using e-cash
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06Q—INFORMATION AND COMMUNICATION TECHNOLOGY [ICT] SPECIALLY ADAPTED FOR ADMINISTRATIVE, COMMERCIAL, FINANCIAL, MANAGERIAL OR SUPERVISORY PURPOSES; SYSTEMS OR METHODS SPECIALLY ADAPTED FOR ADMINISTRATIVE, COMMERCIAL, FINANCIAL, MANAGERIAL OR SUPERVISORY PURPOSES, NOT OTHERWISE PROVIDED FOR
- G06Q20/00—Payment architectures, schemes or protocols
- G06Q20/38—Payment protocols; Details thereof
- G06Q20/382—Payment protocols; Details thereof insuring higher security of transaction
- G06Q20/3829—Payment protocols; Details thereof insuring higher security of transaction involving key management
Landscapes
- Business, Economics & Management (AREA)
- Engineering & Computer Science (AREA)
- Accounting & Taxation (AREA)
- General Business, Economics & Management (AREA)
- Strategic Management (AREA)
- Physics & Mathematics (AREA)
- Computer Security & Cryptography (AREA)
- General Physics & Mathematics (AREA)
- Theoretical Computer Science (AREA)
- Finance (AREA)
- Computer Networks & Wireless Communication (AREA)
- Signal Processing (AREA)
- Financial Or Insurance-Related Operations Such As Payment And Settlement (AREA)
Abstract
Description
(一)技术领域:(1) Technical field:
本发明设计了一种比特币交易隐私增强方法,用于保护比特币交易过程中的明文数额安全。方案通过加同态体制实现了对数额的加密解密运算,保证了传输过程中的数额隐私,同时通过承诺值证明保证了交易中隐藏数额始终为正且输入输出总额相等的要求。该方案属于信息安全中的密码学以及密码学货币领域。The invention designs a privacy enhancement method for bitcoin transactions, which is used to protect the security of plaintext amounts in the process of bitcoin transactions. The scheme realizes the encryption and decryption operation of the amount through the additive homomorphic system, which ensures the privacy of the amount in the transmission process, and at the same time, through the commitment value proof, it guarantees that the hidden amount in the transaction is always positive and the total input and output are equal. This scheme belongs to the field of cryptography and cryptographic currency in information security.
(二)技术背景:(2) Technical background:
2008年,日本程序员中本聪(Satoshi Nakamoto)设计并发布了一种点对点的去中心化数字货币——比特币。比特币系统提出了基于点对点的新型分布式模式,去除了传统电子货币的可信中心机构。比特币以及底层区块链技术展现出的去中心化、信息不可篡改、信息广泛传播、信息匿名特性逐渐被学术界与工业界关注并展开深入研究。In 2008, Japanese programmer Satoshi Nakamoto designed and released a peer-to-peer decentralized digital currency, Bitcoin. The Bitcoin system proposes a new distributed model based on peer-to-peer, which removes the trusted central organization of traditional electronic money. The decentralization, immutability of information, wide dissemination of information, and anonymity of information exhibited by Bitcoin and the underlying blockchain technology have gradually attracted the attention and in-depth research of the academic and industrial circles.
比特币的产生与发展带动了一系列基于密码学的互联网货币兴起。按照工作原理的不同,可以大致分为三类:基于PoW的、基于PoS的以及基于PoW+PoS的。POW(Proof ofWork,工作量证明)是指获得多少货币,取决于你挖矿贡献的工作量,电脑性能越好,分给你的矿就会越多,代表的货币有:比特币、莱特币、狗狗币、Zcash。POS(Proof of Stake,股权证明)根据你持有货币的量和时间进行利息分配的制度,在POS模式下,你的“挖矿”收益正比于你的币龄,而与电脑的计算性能无关,代表的有:比特股、智能坊黑币。基于PoW+PoS的代表有:以太坊、点点币。其他的还有一些货币如:瑞波币、恒星币、合约币。The emergence and development of Bitcoin has led to the rise of a series of Internet currencies based on cryptography. According to different working principles, it can be roughly divided into three categories: PoW-based, PoS-based and PoW+PoS-based. POW (Proof of Work, Proof of Work) refers to how much currency you get, depending on the amount of work you contribute to mining. The better the computer performance, the more mines will be distributed to you. The currencies represented are: Bitcoin, Litecoin , Dogecoin, Zcash. POS (Proof of Stake, Proof of Stake) is a system of interest distribution based on the amount and time of currency you hold. In the POS mode, your "mining" income is proportional to your currency age, regardless of the computer's computing performance. , representing: BitShares, Smart Square Black Coin. The representatives based on PoW+PoS are: Ethereum, Peercoin. There are other currencies such as: Ripple, Stellar, and Futures.
比特币及其他电子货币的兴起引发了对于区块链技术的广泛应用,区块链1.0时代,是以比特币等数字货币为核心形成的底层产业结构,形成了矿机、矿池、数字货币、支付钱包、交易所、数字货币网关的产业群和产业链。在区块链2.0时代,技术和应用的焦点从单纯电子货币转移到底层技术区块链技术的应用上来,形成了多元化、多样式、多场景的应用,类别和行业跨越大、独立程度高。资产验证、金融服务、慈善、媒体及社区、研究及投资、智能合约、公正防伪、资产交易、银行结算、电子商务、社交通讯、物联网、文件存储等领域。The rise of Bitcoin and other electronic currencies has led to the widespread application of blockchain technology. In the era of blockchain 1.0, the underlying industrial structure formed with Bitcoin and other digital currencies as the core has formed mining machines, mining pools, and digital currencies. , payment wallet, exchange, digital currency gateway industry group and industry chain. In the era of blockchain 2.0, the focus of technology and applications has shifted from pure electronic currency to the application of the underlying technology blockchain technology, forming diversified, multi-style, and multi-scenario applications, with large spans of categories and industries and a high degree of independence . Asset verification, financial services, charity, media and community, research and investment, smart contracts, fair anti-counterfeiting, asset trading, bank settlement, e-commerce, social communication, Internet of Things, file storage, etc.
针对大面积比特币使用的所带来的交易隐私泄露问题,方案通过运用加同态加密方案Paillier体制对明文交易数额进行加密传输。该体制是1999年由Pascal Paillier提出,加密体制的困难性基于合数阶剩余类困难问题,具有在标准模型下的抗选择明文攻击安全。该体制具有加同态特性,使得通过对加密后的密文进行乘操作来实现相应的明文加减操作,该性质运用于在不泄露隐私情况下的验证过程。除了同态特性,该体制还具备高效性,使得方案可以通过进行预计算以及运用中国剩余定理进行快速计算,满足在比特币交易时间内的加密解密步骤。Aiming at the leakage of transaction privacy caused by the use of large-scale Bitcoin, the scheme uses the Paillier scheme of the homomorphic encryption scheme to encrypt the transmission of the plaintext transaction amount. The system was proposed by Pascal Paillier in 1999. The difficulty of the encryption system is based on the composite-order residual class difficulty problem, and it has the security against chosen plaintext attack under the standard model. The system has the property of addition homomorphism, so that the corresponding plaintext addition and subtraction operations are realized by multiplying the encrypted ciphertext. This property is used in the verification process without revealing privacy. In addition to the homomorphic properties, the system is also highly efficient, allowing the scheme to perform pre-computation and fast computation using the Chinese remainder theorem to satisfy the encryption and decryption steps within the Bitcoin transaction time.
在运用加密体制进行加密后,生成的密文将存在于每个交易单中。为保证相应密文隐藏的明文的满足正值以及和相等的要求,方案运用了承诺值证明来进行验证。证明承诺值在特定区间采用2004年伍前红等人提出的方法,该方法在步骤相对简单的过程下保证了小的扩张域,使秘密数额保持为正值可证。证明两个承诺值相等运用哈希映射值相等的思想,在不泄露被承诺数的情况下验证两个承诺值包含同一个秘密。两个承诺值证明方案都具备零知识特性,保证了加密后的数额在验证过程中不被泄露。After using the encryption system for encryption, the generated ciphertext will exist in each transaction order. In order to ensure that the plaintext hidden by the corresponding ciphertext satisfies the positive and equal requirements, the scheme uses the Proof of Commitment Value for verification. The method proposed by Wu Qianhong et al. in 2004 is used to prove that the commitment value is in a specific interval. This method guarantees a small expansion field under a relatively simple process, so that the secret amount can be maintained as a positive value verifiable. Proving that two commitment values are equal uses the idea of hash map value equality to verify that two commitment values contain the same secret without revealing the number of commitments. Both proof-of-commitment schemes have zero-knowledge properties, which ensure that the encrypted amount will not be leaked during the verification process.
(三)发明内容:(3) Contents of the invention:
1、目的:本发明的目的是提出一种比特币交易隐私增强方法,以实现交易过程中将原始交易数额明文进行加密隐藏的隐私增强功能。方案一方面使加密后的密文值良好的保护了交易者隐私,另一方面还确保了隐藏的交易值始终为正值且交易数额前后总数一致,以满足与原比特系统的兼容性。1. Purpose: The purpose of the present invention is to propose a privacy enhancement method for Bitcoin transactions, so as to realize the privacy enhancement function of encrypting and hiding the plaintext of the original transaction amount during the transaction process. On the one hand, the scheme ensures that the encrypted ciphertext value protects the privacy of the trader well, and on the other hand, it also ensures that the hidden transaction value is always positive and the total number of transactions before and after is the same to meet the compatibility with the original bit system.
2、技术方案:2. Technical solutions:
本发明方法分为六个步骤,六个步骤依次分散于交易层和验证层:1)系统初始化,生成初始值。2)计算交易总输入值,即上单交易与挖矿总收入。3)系统在交易层使用接收者公钥分别加密传输数额,同时在验证层使用系统公钥加密相同数额的各个数额。4)在验证层验证隐藏后的数额是否为正,以及输入输出总额是否相等。5)验证层验证通过后,交易层将加密后的数额发送给接收者,接收者依据自己的私钥进行解密。6)接收者核查无误后进行全网广播交易单等待确认。The method of the present invention is divided into six steps, and the six steps are distributed in the transaction layer and the verification layer in turn: 1) System initialization, generating an initial value. 2) Calculate the total input value of the transaction, that is, the total revenue of the order transaction and mining. 3) The system uses the receiver's public key to encrypt the transmission amount separately at the transaction layer, and at the same time at the verification layer uses the system public key to encrypt each amount of the same amount. 4) In the verification layer, verify whether the hidden amount is positive and whether the total input and output are equal. 5) After the verification layer passes the verification, the transaction layer sends the encrypted amount to the receiver, and the receiver decrypts it according to his own private key. 6) After the receiver checks that it is correct, broadcast the transaction order on the whole network and wait for confirmation.
2.1基础知识:2.1 Basic knowledge:
2.1.1比特币系统2.1.1 Bitcoin System
比特币系统包含三个技术元素:交易、共识机制、分布式网络。该三个技术元素也形成了比特币和区块链的三层结构:交易单、区块、区块链。比特币的存在形式是一笔笔不可逆的交易单,每笔交易单记录了数个用户的交易数据,包括交易来源和发送地址、交易数额、签名等信息。每笔交易单中都会有一个由SHA-256哈希算法生成的特殊标识符来对交易单进行标识。当每笔交易单完成后必须向全网进行广播等待确认。每个旷工对过去一段时间的交易单进行验证后并找到一个首字符连续为d个零的哈希值后可生成一个数据块,每个数据块在其后生成六个数据块后最终确认且不可更改。不可更改的数据块形成一个链式结构,即区块链。区块的生成是由分布式全网节点的算力进行确认的,算力越大越容易找到新的区块,但由于计算难度的相应调整,对应的计算时间保持在10分钟左右。比特币系统相对于原有电子货币系统具体去中心化、不可伪造、公开可验证、密码学安全等优势,该系统经过近9 年发展已经证明其稳定性和拓展性。The Bitcoin system consists of three technical elements: transactions, consensus mechanisms, and distributed networks. These three technical elements also form the three-layer structure of Bitcoin and blockchain: transaction order, block, and blockchain. Bitcoin exists in the form of irreversible transaction orders. Each transaction order records the transaction data of several users, including transaction source and sending address, transaction amount, signature and other information. Each transaction ticket will have a special identifier generated by the SHA-256 hash algorithm to identify the transaction ticket. When each transaction order is completed, it must be broadcast to the whole network for confirmation. After each miner verifies the transaction order in the past period and finds a hash value whose first character is d consecutive zeros, a data block can be generated, and each data block is finally confirmed after six data blocks are generated. Cannot be changed. Immutable blocks of data form a chain structure, the blockchain. The generation of blocks is confirmed by the computing power of distributed network-wide nodes. The greater the computing power, the easier it is to find new blocks. However, due to the corresponding adjustment of the calculation difficulty, the corresponding calculation time is kept at about 10 minutes. Compared with the original electronic currency system, the Bitcoin system has the advantages of specific decentralization, unforgeability, public verifiability, and cryptographic security. After nearly 9 years of development, the system has proved its stability and scalability.
2.1.2 Paillier公钥加密体制2.1.2 Paillier public key encryption system
Paillier加密体制提供了标准模型下的抗选择明文攻击安全,具备高效的加密解密效率以及加同态的特性,该体制加解密步骤如下:The Paillier encryption system provides security against selected plaintext attacks under the standard model, with high encryption and decryption efficiency and the characteristics of adding homomorphism. The encryption and decryption steps of the system are as follows:
生成:设p和q为大素数,g为系统生成元,令n=pq,计算λ=λ(n)=lcm(p-1,q-1),其中公钥为(n,g),私钥为λ。Generation: Let p and q be large prime numbers, g is the system generator, let n=pq, calculate λ=λ(n)=lcm(p-1,q-1), where the public key is (n,g), The private key is λ.
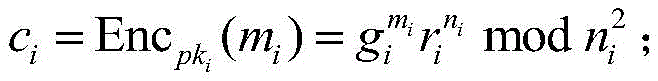
加密:c=gm·rn mod n2,其中r为任意选取。Encryption: c=g m ·rn mod n 2 , where r is arbitrarily selected.
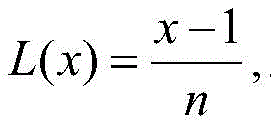
解密: Decrypt:
同态特性:Decsk(Encpk(m1)·Encpk(m2)modn2)=m1+m2 mod n。Homomorphic property: Dec sk (Enc pk (m 1 )·Enc pk (m 2 )modn 2 )=m 1 +m 2 mod n.
2.1.3承诺值证明2.1.3 Proof of Commitment Value
承诺值证明主要用于方案的验证层,一方面解决被承诺值始终为正,另一方面解决被承诺值进行操作后保证输入输出相等的特性。为了保证被加密后的隐私数额为始终为正值以防止比特币的偷窃行为,方案采用了伍前红等人于2004年提出的承诺值在特定区间的高效证明方法。该方法设计步骤相对简单,且扩张域为1,使得被承诺数可以限定在特定的区间,方案将下界设为0,即可证明被承诺数为正值。为了保证加密后的数值作为输出与交易输入值前后一致,方案采用了证明两个承诺数相等的方法。该方案设计思路简单,通过将秘密值隐藏于承诺值中,并且加入随机选取的值,利用两次哈希函数的值是否相等来进行判断是否前后一致,即可证明被承诺值前后和一致。Proof of committed value is mainly used in the verification layer of the scheme. On the one hand, it solves the problem that the committed value is always positive, and on the other hand, it solves the characteristic that the input and output are guaranteed to be equal after the committed value is operated. In order to ensure that the encrypted privacy amount is always positive to prevent bitcoin theft, the scheme adopts the efficient proof method of commitment value in a specific range proposed by Wu Qianhong and others in 2004. The design steps of this method are relatively simple, and the expansion field is 1, so that the committed number can be limited to a specific interval. The scheme sets the lower bound to 0, which can prove that the committed number is positive. In order to ensure that the encrypted value as the output is consistent with the transaction input value, the scheme adopts the method of proving that the two commitment numbers are equal. The design idea of this scheme is simple. By hiding the secret value in the commitment value, adding a randomly selected value, and using whether the values of the two hash functions are equal to determine whether the value is consistent, the committed value can be proved to be consistent.
2.2技术方案内容2.2 Contents of technical solutions
本发明设计一种比特币交易隐私增强方法,该方法依据流程分为六个步骤进行实现,方案架构分为交易层和验证层两层,六个步骤依次分布于两层之中;The present invention designs a method for enhancing the privacy of a bitcoin transaction. The method is implemented in six steps according to the process. The scheme structure is divided into two layers: a transaction layer and a verification layer, and the six steps are sequentially distributed in the two layers;
本发明一种比特币交易隐私增强方法,其运行步骤如下:The present invention is a bitcoin transaction privacy enhancement method, and its operation steps are as follows:
步骤1:系统初始化/KeyGen:生成用于加解密运算以及验证的安全参数;系统输入安全参数,输出用于加解密运算的生成的公钥和私钥对(pki,ski),同时输出用于验证的公钥pkd,注意此公钥无配对私钥;Step 1: System initialization/KeyGen: generate security parameters for encryption and decryption operations and verification; the system inputs security parameters, outputs the generated public and private key pairs (pk i ,ski ) for encryption and decryption operations, and outputs at the same time The public key pk d used for verification, note that this public key has no paired private key;
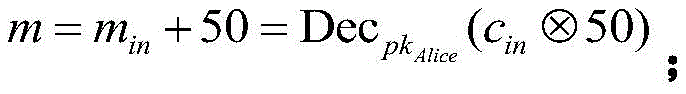
步骤2:计算输入总值/Insum:计算交易总输入值,即上单交易与挖矿总收入(非初始区块链则无此项收入);若该交易单是作为新确认的区块,则该交易单将获得额外的50比特币费用作为奖励,总收入为该部分明文与原密文相操作的总和;若该交易单不是新确认区块首单,则无额外收入,总收入即为上单交易传来的值;Step 2: Calculate the total input value/Insum: Calculate the total input value of the transaction, that is, the total revenue of the order transaction and mining (there is no such revenue for non-initial blockchains); if the transaction list is used as a newly confirmed block, Then the transaction ticket will receive an additional 50 Bitcoin fee as a reward, and the total income is the sum of the operation of the part of the plaintext and the original ciphertext; if the transaction ticket is not the first order of the newly confirmed block, there is no additional income, and the total income is It is the value sent from the top order transaction;
步骤3:加密项/Encrypt:系统在交易层使用接受者公钥分别加密传输数额,同时在验证层使用系统公钥加密相同数额的各个数额;在交易层所加密的数额将在验证层通过后发送至各个接收者账户,注意到在验证层发送的加密数额将进入“哑巴账户”,该账户无私钥,金额在验证后即丢弃;Step 3: Encrypted item/Encrypt: The system uses the receiver's public key to encrypt the transmission amount separately at the transaction layer, and uses the system public key to encrypt each amount of the same amount at the verification layer; the encrypted amount at the transaction layer will be passed in the verification layer. Send to each recipient account, notice that the encrypted amount sent at the verification layer will enter the "dumb account", which has no private key, and the amount is discarded after verification;
步骤4:验证项/Verify:在验证层验证隐藏后的数额是否为正值,以及输入输出总额是否相等;验证层分为两步,第一步通过承诺值在特定区间的证明方法证明隐藏的金额始终为正值;第二步用过两个承诺值相等的证明方法证明隐藏的金额输入输出前后总数相等;当两个步骤都为真时,进入交易层的发送环节;Step 4: Verify item/Verify: Verify whether the hidden amount is a positive value and whether the total input and output are equal in the verification layer; the verification layer is divided into two steps, the first step is to prove the hidden value through the proof method of the commitment value in a specific interval. The amount is always positive; in the second step, two proof methods of equal commitment value are used to prove that the total number of hidden amounts before and after input and output is equal; when both steps are true, enter the sending link of the transaction layer;
步骤5:解密项/Decrypt:验证层验证通过后,交易层将加密后的数额发送给接收者,接收者依据自己的私钥进行解密;在接受者核对自己的接收金额正确后,继续下一单的交易;该接受者的接收值即为下一单的输入值;Step 5: Decryption item/Decrypt: After the verification layer passes the verification, the transaction layer sends the encrypted amount to the receiver, and the receiver decrypts it according to his own private key; after the receiver checks that his received amount is correct, proceed to the next step. order transaction; the receiver's received value is the input value of the next order;
步骤6:广播确认/Broadcast:即接收者核查无误后进行全网广播交易单等待确认;经过该方案处理后的交易单上原始的明文信息将隐藏为无法识读的密文,保证了交易过程唯一可能被分析处理的隐私。Step 6: Broadcast confirmation/Broadcast: that is, the receiver will broadcast the transaction order on the whole network and wait for confirmation after verification; the original plaintext information on the transaction order processed by this solution will be hidden as unreadable ciphertext, which ensures the transaction process. The only privacy that may be processed by analysis.
其中,在步骤1中所述的“系统初始化/KeyGen”,其具体作法如下:Among them, the "system initialization/KeyGen" described in
系统的输入为安全参数,输出则为用于加解密运算以及验证的参数;在交易层,对于每个不同的接收者i,系统生成给每个接收者生成两个大素数pi和qi;接收者私钥为ski=λi,公钥为pki=(ni,gi),其中ni=piqi;The input of the system is the security parameter, and the output is the parameter used for encryption and decryption operations and verification; at the transaction layer, for each different recipient i, the system generates two large prime numbers p i and q i for each recipient. ; the receiver's private key is ski =λ i , and the public key is pk i =( ni , gi ), where ni = pi qi ;
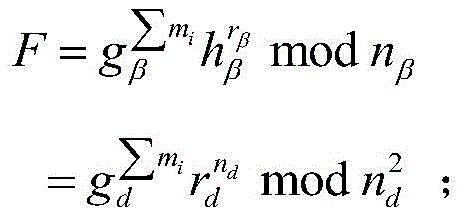
同时在验证层,系统输出用于验证的“哑巴账户”的公钥pkd=(nd,gd),注意到此公钥无配对私钥;即该系统账户不能对收到的金额进行操作;系统生成参数Vα(gα,hα)和 Vβ(gβ,hβ)用于验证。At the same time, at the verification layer, the system outputs the public key pk d = (n d , g d ) of the “dumb account” used for verification, and notices that this public key has no paired private key; that is, the system account cannot perform any verification on the amount received. Operation; the system generates parameters V α (g α , h α ) and V β (g β , h β ) for verification.
其中,在步骤2中所述的“计算输入总值/Insum”,计算输入总值分为两种情况讨论,其具体作法如下:Among them, in the "calculation of input total value/Insum" described in
若该交易单是作为新确认的区块,则该交易单将获得额外的50比特币费用作为奖励(截止至2017年1月,现在已经减半至25比特币),总收入为该部分明文与原密文相操作的总和,表示为If the transaction ticket is used as a newly confirmed block, the transaction ticket will receive an additional 50 bitcoins as a reward (as of January 2017, it has now been halved to 25 bitcoins), and the total revenue is the plaintext of this part The sum of operations with the original ciphertext, expressed as
若该交易单不是新确认区块首单,则无额外收入,总收入即为上单交易传来的值,表示为If the transaction order is not the first order of the newly confirmed block, there will be no additional income, and the total income is the value from the previous order transaction, which is expressed as
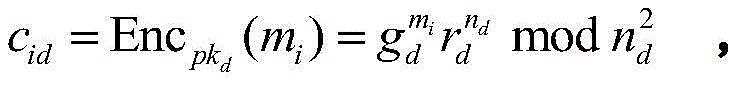
其中,在步骤3中所述的“加密项/Encrypt”,加密过程为在交易层和验证层同时加密相同的数额,其具体作法如下:Among them, in the "encryption item/Encrypt" described in step 3, the encryption process is to encrypt the same amount at the transaction layer and the verification layer at the same time, and the specific method is as follows:
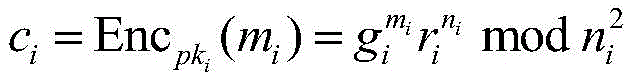
在交易层,方案使用不同接收者的公钥pk1,pk2,...,pki使用Paillier加密体制来加密发送的明文数额m1,m2,...,mi为c1,c2,...,ci,表示为:At the transaction layer, the scheme uses the public keys pk 1 , pk 2 ,...,pk i of different receivers to encrypt the sent plaintext amounts m 1 ,m 2 ,...,m i using the Paillier encryption system as c 1 , c 2 ,..., ci , expressed as:
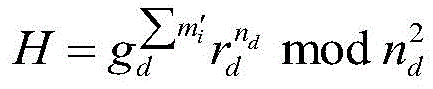
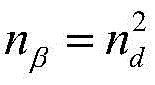
同时,在验证层,方案使用系统的同一个公钥pkd将交易层中每一个发送的数额m1,m2,...,mi进行加密,表示为:At the same time, in the verification layer, the scheme uses the same public key pk d of the system to encrypt the amount m 1 , m 2 ,..., mi sent by each transaction layer, which is expressed as:
其中方案设定随机数rd=hβ。The scheme sets random number r d =h β .
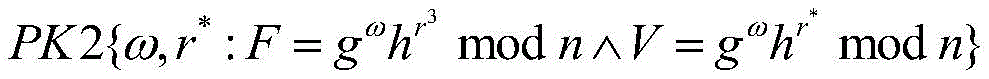
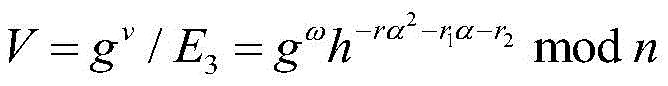
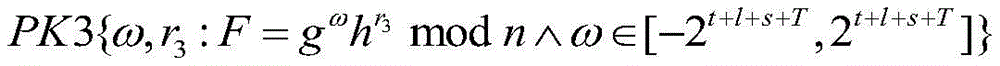
其中,在步骤4中所述的“验证项/Verify”,其验证层分为两步,第一步通过承诺值在特定区间的证明方法证明隐藏的金额始终为正值;第二步用过两个承诺值相等的证明方法证明隐藏的金额输入输出前后总数相等;其具体作法如下:Among them, the "verification item/Verify" described in step 4, its verification layer is divided into two steps, the first step proves that the hidden amount is always positive through the proof method of the commitment value in a specific interval; the second step used The proof method that the two commitment values are equal proves that the total number of hidden amounts before and after input and output is equal; the specific method is as follows:
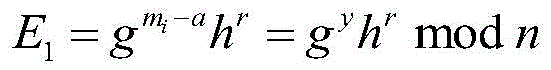
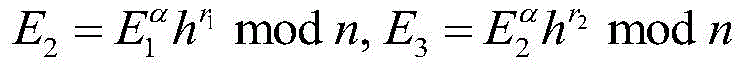
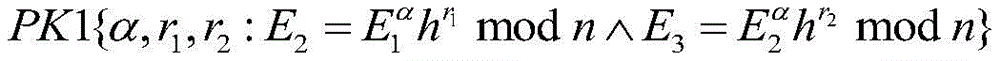
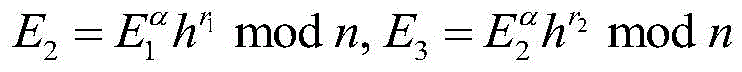
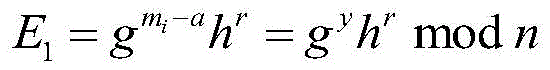
对于第一步即Verify-I,方案使用承诺值在特定区间的证明来保证被加密的数额mi为正值,发送者Alice对于不同的接收者i,分别做出承诺为了简化,使用E0,E1,E2,E3,F,V来代替Ei0,Ei1,Ei2,Ei3,Fi,Vi;For the first step, Verify-I, the scheme uses the proof that the commitment value is in a specific interval to ensure that the encrypted amount m i is a positive value, and the sender Alice makes commitments for different receivers i respectively. For simplicity, use E 0 ,E 1 ,E 2 ,E 3 ,F,V instead of E i0 ,E i1 ,E i2 ,E i3 ,Fi ,V i ;
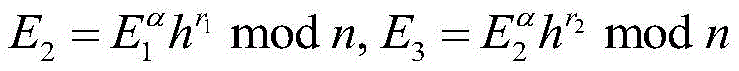
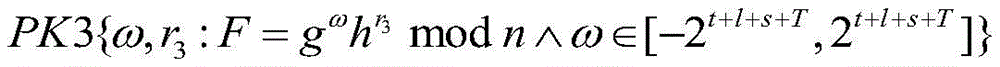
1)Alice设置v=α2y+ω>2t+l+s+T,其中任意选择α≠0,0<ω≤2s+T;设置r3-rα2+r1α+r2∈[-2sn+1,...,2sn-1],其中任意选择r1,r2,r3∈[-2sn+1,...,2sn-1];然后计算:1) Alice sets v=α 2 y+ω>2 t+l+s+T , where α≠0,0<ω≤2 s+T is arbitrarily selected; set r 3 -rα 2 +r 1 α+r 2 ∈[-2 s n+1,...,2 s n-1], where r 1 ,r 2 ,r 3 ∈[-2 s n+1,...,2 s n-1] are chosen arbitrarily ; then compute:
Alice发送(V,E2,E3,F)给接收者;Alice sends (V, E 2 , E 3 , F) to the receiver;
2)接收者计算:2) The receiver calculates:
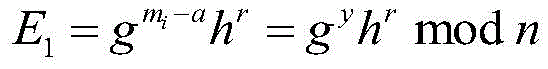
E1=E0(mi,r)/ga=gyhr mod nE 1 =E 0 (m i ,r)/g a =g y h r mod n
3)Alice和接收者各自计算:3) Alice and the receiver each calculate:
其中r*=-rα2-r1α-r2;where r * =-rα2 - r1α- r2 ;
4)接收者验证PK1,PK2,PK3的正确性,以及是否满足v>2t+l+s+T,若满足则接收者可以确信x>a;4) The receiver verifies the correctness of PK1, PK2, PK3, and whether v>2 t+l+s+T is satisfied, if satisfied, the receiver can be sure that x>a;
5)对于每个接收者mi,方案重复步骤1)-步骤4)即可证明mi>0(i={1,2,...,i});5) For each receiver mi, the scheme repeats steps 1)-4) to prove that mi > 0 ( i ={1,2,...,i});
该证明部分将对每个接收者的mi重复执行i次,如果其中有任意一次失败,交易失败;如果全部成功,系统通过,并继续下个步骤的验证;The proof part will be repeated i times for each receiver's mi, if any one of them fails, the transaction fails; if all are successful, the system passes, and continues to the next step of verification;
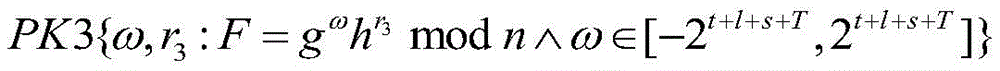
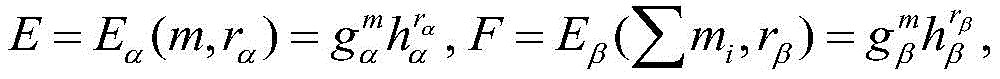
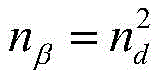
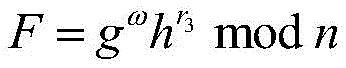
对于第二步即Verify-II,方案使用证明两个承诺值相等的证明来保证交易输出输入前后一致,即m=m1+m2+...+mi=∑mi;现在,Alice做出两个承诺如下:For the second step, Verify-II, the scheme uses the proof that the two commitment values are equal to ensure that the transaction output and input are consistent, that is, m=m 1 +m 2 +...+m i =∑m i ; now, Alice Make two promises as follows:
其中rα∈{-2sn+1,...,2sn-1},rβ=nd∈{-2sn+1,...,2sn-1};如果收到相同数额的“哑巴账户”想验证其收到的密文中所含的明文数额是否与Alice发送的值相等,那么它需要进行如下两个步骤:where r α ∈{-2 s n+1,...,2 s n-1},r β =n d ∈{-2 s n+1,...,2 s n-1}; To a "dumb account" with the same amount, it needs to perform the following two steps:
1)隐藏在承诺值E和F中的秘密值相等m=∑mi;1) The secret values hidden in the commitment values E and F are equal to m=∑m i ;
2)操作后的密文H=Πcid等于其中一个承诺F;2) The ciphertext H=Πc id after the operation is equal to one of the commitments F;
为了实现上述步骤1),我们进行如下证明:In order to realize the above step 1), we prove as follows:
1.Alice随机选择ω∈{1,...,2i+tb-1},ηα∈{1,...,2l+t+sn-1},ηβ∈{1,...,2l+t+ sn-1};然后计算:1. Alice randomly selects ω∈{1,...,2 i+t b-1},η α ∈{1,...,2 l+t+s n-1},η β ∈{1, ...,2 l+t+ s n-1}; then compute:
2.Alice计算u=H(Wα||Wβ);2. Alice calculates u=H(W α ||W β );
3.Alice计算:3. Alice calculates:
D=ω+um,Dα=ηα+urα,Dβ=ηβ+urβ D=ω+um, D α = η α +ur α , D β =η β +ur β
并且发送(u,D,Dα,Dβ)给“哑巴账户”;And send (u, D, D α , D β ) to the "dumb account";
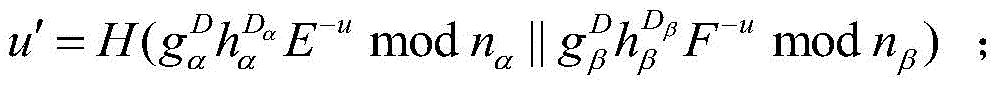
4.“哑巴账户”检验是否u=u′,其中4. The "dumb account" tests whether u=u', where
如果该部分步骤验证成功,继续进行下部分步骤证明:If this part of the step verification is successful, proceed to the next part of the step verification:
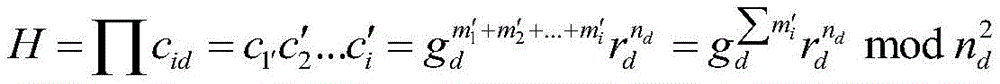
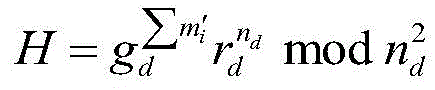
1.“哑巴账户”对收到的密文进行计算:1. The "dumb account" calculates the received ciphertext:
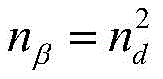
2.从上面可以看出,我们可以在加密过程中任意选取rd=hβ,在验证过程中任意选取rβ=nd;并且在系统初始化过程中,我们设置以及gd=gβ,是故:2. As can be seen from the above, we can arbitrarily select r d =h β in the encryption process, and arbitrarily select r β =n d in the verification process; and in the system initialization process, we set and g d =g β , so:
3.检查H是否等于F,如果否,交易失败,如果是则通过,并进行下一步;3. Check whether H is equal to F, if not, the transaction fails, if it is, it passes, and the next step is performed;
综上验证,当两个部分的步骤都为真时,进入交易层的发送环节。To sum up the verification, when the steps of both parts are true, enter the sending link of the transaction layer.
其中,在步骤5中所述的“解密项/Decrypt”,证层验证通过后,交易层将加密后的数额ci发送给接收者,其具体作法如下:Among them, in the "decryption item/Decrypt" described in step 5, after the certificate layer verification is passed, the transaction layer sends the encrypted amount c i to the receiver, and the specific method is as follows:
接收者依据自己的私钥ski进行解密:The receiver decrypts according to its own private key ski:
其中x∈Sn={u<n2|x=1 mod n};in x∈S n ={u<n 2 |x=1 mod n};
在接受者核对自己的接收金额正确后,继续下一单的交易;该接受者的接收值即为下一单的输入值;值得注意的是,当交易完成后,“哑巴账户”中的密文数额将被丢弃,其作用仅作为桥梁使验证层的值与发送的值产生联系。After the recipient checks that the received amount is correct, the transaction of the next order is continued; the received value of the recipient is the input value of the next order; it is worth noting that when the transaction is completed, the password in the "dumb account" The text amount will be discarded, which only acts as a bridge between the value of the verification layer and the value sent.
其中,在步骤6中所述的“广播确认/Broadcast”,即接收者核查无误后进行全网广播交易单等待确认,其具体作法如下:Among them, in the "broadcast confirmation/Broadcast" described in step 6, that is, after the receiver has verified that it is correct, the entire network broadcasts the transaction order and waits for confirmation. The specific method is as follows:
经过该方案处理后的交易单上原始的明文信息将隐藏为无法识读的密文,保证了交易过程唯一可能被分析处理的隐私;我们可以将此交易单标志为TAlice,该过程同样适用于任意其他单交易。The original plaintext information on the transaction order processed by this scheme will be hidden as unreadable ciphertext, which ensures the privacy of the transaction process that may only be analyzed and processed; we can mark this transaction order as T Alice , and this process is also applicable on any other single transaction.
通过以上步骤,本发明所提出的比特币隐私增强的方法得到了论述,该方法是从现有比特币系统存在的问题产生,继而进行完整的设计,用于解决比特币系统中数额暴露的隐私泄露问题;该方法覆盖了比特币系统、同态加密体制和承诺值证明几个密码学原语,将不同领域的方法从新应用在隐私增强的实际问题上,依据其方案设计可知,该方案具有加解密性、同态特性、零知识特性、安全性、高效性和兼容性;最终,该系统方法实现了加密后比特币的顺畅交易过程。Through the above steps, the Bitcoin privacy enhancement method proposed by the present invention has been discussed. The method is generated from the existing problems of the Bitcoin system, and then a complete design is carried out to solve the privacy of the amount exposed in the Bitcoin system. Leakage problem; this method covers several cryptographic primitives of Bitcoin system, homomorphic encryption system and commitment value proof, and applies methods from different fields to practical problems of privacy enhancement. According to its scheme design, this scheme has Encryption, homomorphic properties, zero-knowledge properties, security, efficiency, and compatibility; finally, this systematic approach realizes a smooth transaction process for encrypted bitcoins.
3、优点及功效:3. Advantages and efficacy:
本发明提供了一种比特币交易隐私增强方法,该方法在保证与原始比特币系统兼容的情况下实现了交易中数额的隐藏功能,并且保证了加密的数额始终为正且输入输出相等的要求。该方法具有1)同态特性,使得系统可以对密文进行加减操作。2)零知识特性,传输和验证不泄露任何明文值。3)安全性,可抵抗不同类型的主动攻击和被动攻击。4)高效性,相比Zerocoin等解决方案具有更少的运算复杂度,且可以通过预计算和中国剩余定理进行算法加速。5)兼容性,与传统比特币系统兼容,可以移植入原始系统。The invention provides a privacy enhancement method for bitcoin transactions, which realizes the hidden function of the amount in the transaction under the condition of ensuring compatibility with the original bitcoin system, and ensures that the encrypted amount is always positive and the input and output are equal. . This method has 1) homomorphic properties, so that the system can perform addition and subtraction operations on the ciphertext. 2) Zero-knowledge feature, transmission and verification do not reveal any plaintext value. 3) Security, can resist different types of active and passive attacks. 4) Efficiency. Compared with solutions such as Zerocoin, it has less computational complexity, and can accelerate the algorithm through pre-computation and the Chinese remainder theorem. 5) Compatibility, compatible with the traditional Bitcoin system, can be transplanted into the original system.
(四)附图说明:(4) Description of drawings:
图1为本发明所述方法的流程框图。FIG. 1 is a flow chart of the method of the present invention.
图中序号、代号、符号说明如下:The serial numbers, codes and symbols in the figure are explained as follows:
图示中,Insum/Encrypt/Verify/Decrypt/Braodcast分别代表步骤2-6,Transcation layer/Verification layer分别代表系统架构的两层,m1,m2,...,mi为发送给接收者的明文数额,c1,c2,...,ci为加密后的密文数额,(pki,ski)为加密的公私钥对,Enc/Dec为加解密过程,Dumb account为验证时设置的“哑巴账户”。In the figure, Insum/Encrypt/Verify/Decrypt/Braodcast respectively represent steps 2-6, Transcation layer/Verification layer respectively represent the two layers of the system architecture, m 1 , m 2 ,..., m i are sent to the receiver The amount of plaintext, c 1 , c 2 ,..., ci is the amount of encrypted ciphertext, (pk i , ski ) is the encrypted public-private key pair, Enc/Dec is the encryption and decryption process, and Dumb account is the verification The "dumb account" set at the time.
(五)具体实施方式(5) Specific implementation methods
本发明为一种比特币交易隐私增强方法,该方法依据流程分为六个步骤进行实现,方案架构分为交易层和验证层两层。该方法的系统流程见图1,结合流程框图,将该方法的具体实现步骤介绍如下:The present invention is a method for enhancing the privacy of a bitcoin transaction. The method is implemented in six steps according to the process, and the scheme structure is divided into two layers: a transaction layer and a verification layer. The system flow diagram of the method is shown in Figure 1. Combined with the flow chart, the specific implementation steps of the method are introduced as follows:
本发明一种比特币交易隐私增强方法,将该方法具体实施步骤如下:The present invention is a method for enhancing the privacy of bitcoin transactions, and the specific implementation steps of the method are as follows:
步骤1:系统初始化/KeyGen:输入安全参数,输出用于加解密运算以及验证的参数。在交易层,对于每个不同的接收者i,系统生成给每个接收者生成两个大素数pi和qi。接收者私钥为ski=λi,公钥为pki=(ni,gi),其中ni=piqi;Step 1: System initialization/KeyGen: Input security parameters and output parameters for encryption and decryption operations and verification. At the transaction layer, for each different receiver i, the system generates two large prime numbers p i and q i for each receiver. The receiver's private key is ski =λ i , and the public key is pk i =( ni , gi ), where ni = pi qi ;
同时在验证层,系统输出用于验证的“哑巴账户”的公钥pkd=(nd,gd),注意到此公钥无配对私钥。即该系统账户不能对收到的金额进行操作;系统生成参数Vα(gα,hα)和 Vβ(gβ,hβ)用于验证;At the same time in the verification layer, the system outputs the public key pk d = (n d , g d ) of the "dumb account" used for verification, and notices that this public key has no paired private key. That is, the system account cannot operate on the amount received; the system generates parameters V α (g α , h α ) and V β (g β , h β ) for verification;
注意到,由于“哑巴账户”和承诺值证明同处于验证层,且其参数都是由系统生成,方案设定gβ=gd以及来确保操作后的密文可以成为承诺数;Note that since the "dumb account" and the commitment value proof are both in the verification layer, and their parameters are generated by the system, the scheme sets g β =g d and To ensure that the ciphertext after the operation can become the committed number;
步骤2:计算总输入值/Insum:计算交易总输入值,即上单交易与挖矿总收入。Step 2: Calculate the total input value/Insum: Calculate the total input value of the transaction, that is, the total revenue of placing orders and mining.
若该交易单是作为新确认的区块,则该交易单将获得额外的50比特币费用作为奖励(截止至2017年1月,现在已经减半至25比特币),总收入为该部分明文与原密文相操作的总和,表示为If the transaction ticket is used as a newly confirmed block, the transaction ticket will receive an additional 50 bitcoins as a reward (as of January 2017, it has now been halved to 25 bitcoins), and the total revenue is the plaintext of this part The sum of operations with the original ciphertext, expressed as
若该交易单不是新确认区块首单,则无额外收入,总收入即为上单交易传来的值,表示为If the transaction order is not the first order of the newly confirmed block, there will be no additional income, and the total income is the value from the previous order transaction, which is expressed as
步骤3:加密项/Encrypt:在交易层,方案使用不同接收者的公钥pk1,pk2,...,pki使用Paillier加密体制来加密发送的明文数额m1,m2,...,mi为c1,c2,...,ci,表示为:Step 3: Encrypted item/Encrypt: At the transaction layer, the scheme uses the public keys pk 1 , pk 2 , ..., p i of different receivers to encrypt the sent plaintext amounts m 1 , m 2 , ..., p i using the Paillier encryption scheme .,m i is c 1 ,c 2 ,..., ci , expressed as:
同时,在验证层,方案使用系统的同一个公钥pkd将交易层中每一个发送的数额m1,m2,...,mi进行加密,表示为:At the same time, in the verification layer, the scheme uses the same public key pk d of the system to encrypt the amount m 1 , m 2 ,..., mi sent by each transaction layer, which is expressed as:
其中方案设定随机数rd=hβ;Wherein the scheme sets random number r d =h β ;
两层的共同点是加密了相同的交易数额mi,不同之处在于交易层使用来自接收者的不同的公钥pki,验证层使用了来自系统的相同公钥pkd用于实现Paillier体制的加同态特性。其内在相同的数额mi保证了接收者在验证后得到值的正确性;The common point of the two layers is that the same transaction amount mi is encrypted, the difference is that the transaction layer uses a different public key pk i from the receiver , and the verification layer uses the same public key pk d from the system for implementing the Paillier scheme. The additive homomorphism property of . The inherently same amount m i guarantees the correctness of the value obtained by the receiver after verification;
步骤4:验证项/Verify:系统在验证层验证隐藏后的数额是否为正值,以及输入输出总额是否相等。验证层分为两步,第一步通过承诺值在特定区间的证明方法证明隐藏的金额始终为正值;第二步用过两个承诺值相等的证明方法证明隐藏的金额输入输出前后总数相等;Step 4: Verify item/Verify: The system verifies whether the hidden amount is a positive value at the verification layer and whether the total input and output are equal. The verification layer is divided into two steps. The first step proves that the hidden amount is always a positive value through the proof method that the commitment value is in a specific interval; the second step uses two proof methods with equal commitment values to prove that the total number of hidden amounts before and after input and output is equal. ;
对于第一步,方案使用承诺值在特定区间的证明来保证被加密的数额mi为正值,发送者 Alice对于不同的接收者i,分别做出承诺为了简化,使用E0,E1,E2, E3,F,V来代替Ei0,Ei1,Ei2,Ei3,Fi,Vi。For the first step, the scheme uses the proof that the commitment value is in a specific interval to ensure that the encrypted amount m i is a positive value, and the sender Alice makes commitments for different receivers i respectively. For simplicity, E 0 ,E 1 ,E 2 ,E 3 ,F,V are used instead of E i0 ,E i1 ,E i2 ,E i3 ,Fi ,V i .
1)Alice设置v=α2y+ω>2t+l+s+T,其中任意选择α≠0,0<ω≤2s+T;设置r3-rα2+r1α+r2∈[-2sn+1,...,2sn-1],其中任意选择r1,r2,r3∈[-2sn+1,...,2sn-1];然后计算:1) Alice sets v=α 2 y+ω>2 t+l+s+T , where α≠0,0<ω≤2 s+T is arbitrarily selected; set r 3 -rα 2 +r 1 α+r 2 ∈[-2 s n+1,...,2 s n-1], where r 1 ,r 2 ,r 3 ∈[-2 s n+1,...,2 s n-1] are chosen arbitrarily ; then compute:
Alice发送(V,E2,E3,F)给接收者;Alice sends (V, E 2 , E 3 , F) to the receiver;
2)接收者计算:2) The receiver calculates:
E1=E0(mi,r)/ga=gyhr mod nE 1 =E 0 (m i ,r)/g a =g y h r mod n
3)Alice和接收者各自计算:3) Alice and the receiver each calculate:
其中r*=-rα2-r1α-r2;where r * =-rα2 - r1α- r2 ;
4)接收者验证PK1,PK2,PK3的正确性,以及是否满足v>2t+l+s+T,若满足则接收者可以确信x>a;4) The receiver verifies the correctness of PK1, PK2, PK3, and whether v>2 t+l+s+T is satisfied, if satisfied, the receiver can be sure that x>a;
5)对于每个接收者mi,方案重复步骤1-4即可证明mi>0(i={1,2,...,i})。5) For each receiver mi, the scheme repeats steps 1-4 to prove that mi > 0 ( i ={1,2,...,i}).
该证明部分将对每个接收者的mi重复执行i次,如果其中有任意一次失败,交易失败;如果全部成功,系统返回1,并继续下个步骤的验证。The proof part will be repeated i times for each receiver's mi, if any one of them fails, the transaction fails; if all of them are successful, the system returns 1 and continues the verification of the next step.
对于第二步,方案使用证明两个承诺值相等的证明来保证交易输出输入前后一致,即 m=m1+m2+...+mi=∑mi。现在,Alice做出两个承诺如下:For the second step, the scheme uses a proof that the two commitment values are equal to ensure that the transaction output and input are consistent, ie m=m 1 +m 2 +...+m i =∑m i . Now, Alice makes two promises as follows:
其中rα∈{-2sn+1,...,2sn-1},rβ=nd∈{-2sn+1,...,2sn-1};如果收到相同数额的“哑巴账户”想验证其收到的密文中所含的明文数额是否与Alice发送的值相等,那么它需要进行如下两个步骤:where r α ∈{-2 s n+1,...,2 s n-1},r β =n d ∈{-2 s n+1,...,2 s n-1}; To a "dumb account" with the same amount, it needs to perform the following two steps:
1)隐藏在承诺值E和F中的秘密值相等m=∑mi;1) The secret values hidden in the commitment values E and F are equal to m=∑m i ;
2)操作后的密文H=Πcid等于其中一个承诺F。2) The ciphertext H=Πc id after the operation is equal to one of the commitments F.
为了实现上述步骤1),我们进行如下证明:In order to realize the above step 1), we prove as follows:
1.Alice随机选择ω∈{1,...,2i+tb-1},ηα∈{1,...,2l+t+sn-1},ηβ∈{1,...,2l+t+ sn-1};然后计算:1. Alice randomly selects ω∈{1,...,2 i+t b-1},η α ∈{1,...,2 l+t+s n-1},η β ∈{1, ...,2 l+t+ s n-1}; then compute:
2.Alice计算u=H(Wα||Wβ);2. Alice calculates u=H(W α ||W β );
3.Alice计算:3. Alice calculates:
D=ω+um,Dα=ηα+urα,Dβ=ηβ+urβ D=ω+um, D α = η α +ur α , D β =η β +ur β
并且发送(u,D,Dα,Dβ)给“哑巴账户”;And send (u, D, D α , D β ) to the "dumb account";
4.“哑巴账户”检验是否u=u′,其中4. The "dumb account" tests whether u=u', where
如果该部分步骤验证成功,继续进行下部分步骤证明:If this part of the step verification is successful, proceed to the next part of the step verification:
1.“哑巴账户”对收到的密文进行计算:1. The "dumb account" calculates the received ciphertext:
2.从上面可以看出,我们可以在加密过程中任意选取rd=hβ,在验证过程中任意选取 rβ=nd;并且在系统初始化过程中,我们设置以及gd=gβ,是故:2. As can be seen from the above, we can arbitrarily select r d =h β in the encryption process, and arbitrarily select r β =n d in the verification process; and in the system initialization process, we set and g d =g β , so:
3.检查H是否等于F,如果否,交易失败,如果是返回1,并进行下一步。3. Check if H is equal to F, if not, the transaction fails, if it is,
综上验证,当两个部分的步骤都为真时,进入交易层的发送环节;To sum up the verification, when the steps of both parts are true, enter the sending link of the transaction layer;
步骤5:解密项/Dcrypt:证层验证通过后,交易层将加密后的数额ci发送给接收者,接收者依据自己的私钥ski进行解密:Step 5: Decryption item/ Dcrypt : After the verification of the certificate layer is passed, the transaction layer sends the encrypted amount ci to the receiver, and the receiver decrypts it according to his own private key ski :
其中x∈Sn={u<n2|x=1 mod n};in x∈S n ={u<n 2 |x=1 mod n};
在接受者核对自己的接收金额正确后,继续下一单的交易。该接受者的接收值即为下一单的输入值。值得注意的是,当交易完成后,“哑巴账户”中的密文数额将被丢弃,其作用仅作为桥梁使验证层的值与发送的值产生联系;After the recipient verifies that the received amount is correct, the transaction of the next order is continued. The receiver's received value is the input value of the next order. It is worth noting that when the transaction is completed, the amount of ciphertext in the "dumb account" will be discarded, and its role is only as a bridge to connect the value of the verification layer with the value sent;
步骤6:广播确认/Broadcast:接收者核查无误后进行全网广播交易单等待确认。经过该方案处理后的交易单上原始的明文信息将隐藏为无法识读的密文,保证了交易过程唯一可能被分析处理的隐私。我们可以将此交易单标志为TAlice,该过程同样适用于任意其他单交易。Step 6: Broadcast confirmation/Broadcast: After the receiver checks that it is correct, broadcast the transaction order on the whole network and wait for confirmation. The original plaintext information on the transaction order processed by this scheme will be hidden as unreadable ciphertext, which ensures the privacy of the only possible analysis and processing of the transaction process. We can mark this transaction as T Alice , and the same process applies to any other single transaction.
Claims (1)
Priority Applications (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN201710050768.3A CN106911470B (en) | 2017-01-23 | 2017-01-23 | A Privacy-enhancing Approach for Bitcoin Transactions |
Applications Claiming Priority (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN201710050768.3A CN106911470B (en) | 2017-01-23 | 2017-01-23 | A Privacy-enhancing Approach for Bitcoin Transactions |
Publications (2)
| Publication Number | Publication Date |
|---|---|
| CN106911470A CN106911470A (en) | 2017-06-30 |
| CN106911470B true CN106911470B (en) | 2020-07-07 |
Family
ID=59207453
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| CN201710050768.3A Active CN106911470B (en) | 2017-01-23 | 2017-01-23 | A Privacy-enhancing Approach for Bitcoin Transactions |
Country Status (1)
| Country | Link |
|---|---|
| CN (1) | CN106911470B (en) |
Families Citing this family (31)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN107330775A (en) * | 2017-07-05 | 2017-11-07 | 贵州大学 | A kind of first valency sealing method of commerce based on bit coin agreement |
| CN107506989A (en) * | 2017-08-18 | 2017-12-22 | 特兰旗(厦门)科技有限公司 | Exchange method and device |
| CN108418783B (en) * | 2017-09-01 | 2021-03-19 | 矩阵元技术(深圳)有限公司 | A method and medium for protecting the privacy of blockchain smart contracts |
| CN107886314A (en) | 2017-11-20 | 2018-04-06 | 北京比特大陆科技有限公司 | Ideal money settlement method, device and electronic equipment |
| CN108021821A (en) * | 2017-11-28 | 2018-05-11 | 北京航空航天大学 | Multicenter block chain transaction intimacy protection system and method |
| CN108418689B (en) * | 2017-11-30 | 2020-07-10 | 矩阵元技术(深圳)有限公司 | Zero-knowledge proof method and medium suitable for block chain privacy protection |
| CN108200174B (en) * | 2018-01-04 | 2019-10-25 | 成都理工大学 | Blockchain-based distributed mobile phone protection platform and its implementation method |
| WO2019180590A1 (en) * | 2018-03-23 | 2019-09-26 | nChain Holdings Limited | Computer-implemented system and method for exchange of data |
| CN111919416B (en) * | 2018-04-09 | 2021-11-19 | 华为技术有限公司 | Method and system for zero knowledge range attestation with reversible commitments |
| WO2019209168A2 (en) * | 2018-04-26 | 2019-10-31 | 华为国际有限公司 | Data processing method, related apparatus, and blockchain system |
| CN108712409B (en) * | 2018-05-09 | 2021-05-25 | 广西创轩科技有限公司 | Electronic bill transaction system based on private block chain |
| CN108764874B (en) * | 2018-05-17 | 2021-09-07 | 深圳前海微众银行股份有限公司 | Blockchain-based anonymous transfer method, system and storage medium |
| CN108805574B (en) * | 2018-05-19 | 2021-01-26 | 深圳市图灵奇点智能科技有限公司 | Transaction method and system based on privacy protection |
| CN108734017B (en) * | 2018-05-20 | 2020-11-13 | 深圳市图灵奇点智能科技有限公司 | Driving data sharing method and device, system and computer storage medium |
| CN108763955B (en) * | 2018-05-20 | 2020-11-13 | 深圳市图灵奇点智能科技有限公司 | Travel data sharing method and apparatus, travel data sharing system, and computer storage medium |
| CN109087099A (en) * | 2018-07-31 | 2018-12-25 | 杭州复杂美科技有限公司 | A kind of privacy method of commerce and system, equipment and storage medium |
| CN111783114B (en) * | 2018-08-06 | 2024-04-02 | 创新先进技术有限公司 | Block chain transaction method and device and electronic equipment |
| CN111768304A (en) | 2018-08-06 | 2020-10-13 | 阿里巴巴集团控股有限公司 | Blockchain transaction method and device, electronic device |
| CN109255720B (en) * | 2018-09-29 | 2022-01-18 | 武汉星云智慧科技有限公司 | Block chain-based community endowment card issuing and verification method and system |
| CN110419055B (en) * | 2018-11-07 | 2023-08-22 | 创新先进技术有限公司 | Blockchain data protection based on account note model using zero-knowledge proof |
| SG11201903563WA (en) * | 2018-11-07 | 2019-05-30 | Alibaba Group Holding Ltd | Blockchain system supporting public and private transactions under account models |
| MX379839B (en) | 2018-11-27 | 2025-03-11 | Advanced New Technologies Co Ltd | SYSTEM AND METHOD FOR INFORMATION PROTECTION. |
| CA3037833C (en) * | 2018-11-27 | 2022-04-19 | Alibaba Group Holding Limited | System and method for information protection |
| AU2018347197B2 (en) | 2018-11-27 | 2020-06-25 | Advanced New Technologies Co., Ltd. | System and method for information protection |
| CN110337665B (en) | 2018-11-27 | 2023-06-06 | 创新先进技术有限公司 | System and method for information protection |
| US10700850B2 (en) | 2018-11-27 | 2020-06-30 | Alibaba Group Holding Limited | System and method for information protection |
| KR102139897B1 (en) * | 2018-11-27 | 2020-07-31 | 알리바바 그룹 홀딩 리미티드 | System and method for information protection |
| DE102020104906A1 (en) * | 2020-02-25 | 2021-08-26 | Giesecke+Devrient Gesellschaft mit beschränkter Haftung | PROCEDURE FOR DIRECT TRANSFER OF ELECTRONIC COIN DATA SETS BETWEEN TERMINAL DEVICES, PAYMENT SYSTEM, CURRENCY AND MONITORING UNIT |
| US12010244B2 (en) * | 2020-11-09 | 2024-06-11 | International Business Machines Corporation | Blockchain based verifiability of user status |
| CN112235425B (en) * | 2020-12-14 | 2021-03-09 | 长沙理工大学 | A method, device, system and readable storage medium for forming a mining pool of blockchain |
| CN114329610B (en) * | 2021-12-29 | 2024-08-27 | 浙江吉利控股集团有限公司 | Blockchain privacy identity protection method, device, storage medium and system |
Family Cites Families (2)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN103259650B (en) * | 2013-04-25 | 2015-12-09 | 河海大学 | A kind of rationality many secret sharings method to honest participant's justice |
| WO2016200885A1 (en) * | 2015-06-08 | 2016-12-15 | Blockstream Corporation | Cryptographically concealing amounts transacted on a ledger while preserving a network's ability to verify the transaction |
-
2017
- 2017-01-23 CN CN201710050768.3A patent/CN106911470B/en active Active
Also Published As
| Publication number | Publication date |
|---|---|
| CN106911470A (en) | 2017-06-30 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| CN106911470B (en) | A Privacy-enhancing Approach for Bitcoin Transactions | |
| US12470369B2 (en) | Determining a common secret for the secure exchange of information and hierarchical, deterministic cryptographic keys | |
| Liu et al. | Anonymous reputation system for IIoT-enabled retail marketing atop PoS blockchain | |
| CN108418689B (en) | Zero-knowledge proof method and medium suitable for block chain privacy protection | |
| CN108021821A (en) | Multicenter block chain transaction intimacy protection system and method | |
| CN104850984B (en) | The method for safe operation that a kind of off-line cash is paid | |
| CN113159745B (en) | Block chain transaction privacy protection method based on full homomorphism | |
| CN113626852A (en) | Safe and efficient method, system and application for anonymizing chain elements of unlicensed blocks | |
| CN110599164B (en) | Supervision-capable quick payment method for any payee under chain | |
| Devidas et al. | Identity verifiable ring signature scheme for privacy protection in blockchain | |
| CN111738857A (en) | Method and device for generating and verifying hidden payment certificate applied to blockchain | |
| Islam | An auditable, privacy-preserving, transparent unspent transaction output model for blockchain-based central bank digital currency | |
| Verbücheln | How perfect offline wallets can still leak bitcoin private keys | |
| CN116094726A (en) | Partially blind signature method and system based on lattice public key cryptography | |
| CN110992010B (en) | Digital currency issue total amount control method and verification method | |
| Kang et al. | An Off-Line Payment Scheme for Digital Content via Subliminal Channel. | |
| Zhou et al. | Fast Settlement Scheme of Aviation Business Privacy Preservation Based on Consortium Blockchain | |
| CN114520728B (en) | Distributed anonymous marking method and system | |
| Saqib | Blockchain-based Data Sharing of Vehicle Passports | |
| CN120070015A (en) | Car rental transaction and trust management system based on blockchain | |
| Puzis et al. | Controllable Privacy Preserving | |
| HK1251840B (en) | Determining a common secret for the secure exchange of information and hierarchical, deterministic cryptographic keys | |
| HK40032100A (en) | Determining a common secret for the secure exchange of information and hierarchical, deterministic cryptographic keys | |
| Spognardi | Blind signatures-Untraceable Electronic Cash-Oblivious communities | |
| HK1241544B (en) | Determining a common secret for the secure exchange of information and hierarchical, deterministic cryptographic keys |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| PB01 | Publication | ||
| PB01 | Publication | ||
| SE01 | Entry into force of request for substantive examination | ||
| SE01 | Entry into force of request for substantive examination | ||
| GR01 | Patent grant | ||
| GR01 | Patent grant |