WO2020168755A1 - Method and device for controlling database operation, computer apparatus and storage medium - Google Patents
Method and device for controlling database operation, computer apparatus and storage medium Download PDFInfo
- Publication number
- WO2020168755A1 WO2020168755A1 PCT/CN2019/118000 CN2019118000W WO2020168755A1 WO 2020168755 A1 WO2020168755 A1 WO 2020168755A1 CN 2019118000 W CN2019118000 W CN 2019118000W WO 2020168755 A1 WO2020168755 A1 WO 2020168755A1
- Authority
- WO
- WIPO (PCT)
- Prior art keywords
- lock
- data
- record table
- lock data
- record
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Ceased
Links
Images
Classifications
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F16/00—Information retrieval; Database structures therefor; File system structures therefor
- G06F16/20—Information retrieval; Database structures therefor; File system structures therefor of structured data, e.g. relational data
- G06F16/21—Design, administration or maintenance of databases
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F16/00—Information retrieval; Database structures therefor; File system structures therefor
- G06F16/20—Information retrieval; Database structures therefor; File system structures therefor of structured data, e.g. relational data
- G06F16/22—Indexing; Data structures therefor; Storage structures
Definitions
- This application relates to a database operation control method, device, computer equipment and storage medium.
- customers do many operations on many objects (such as DB instances, users, etc.), and most of the operations are not completed immediately, which takes tens of seconds to several minutes.
- the operations of different customers on different objects may be related, and some may affect each other, and cannot be executed at the same time. For example, if customer U1 is expanding the storage capacity for library A, when customer U2 initiates the creation of a same-city disaster recovery library for library A, then the latter should not be allowed to execute, otherwise an error will be reported in the middle of the execution, and it will be difficult to continue. Or roll back.
- the inventor realizes that in order to avoid conflicts between operations, the traditional approach is to hard-code these business rules into the program. But when the volume of database products is large, hard coding simply cannot cope with such a huge business logic.
- a database operation control method, device, computer equipment, and storage medium are provided.
- a database operation control method includes:
- the operation is executed, and the lock data corresponding to the operation is added to the operation lock record table.
- a database operation control device includes:
- the operation request receiving module is configured to receive a database operation request, and the request carries an operation identifier
- a lock data search module configured to search lock data corresponding to the operation identifier, the lock data including the operation object corresponding to the operation identifier and the lock type corresponding to each operation object;
- the conflict judgment module is used for judging whether the lock data conflicts with the lock data in the operation lock record table according to the pre-defined mutual exclusion relationship of lock types.
- the lock data in the operation lock record table includes the status of being executed Operate the corresponding lock data;
- the blocking module is used to block the requested operation; the execution module is used to execute the operation and add lock data corresponding to the operation to the operation lock record table.
- a computer device including a memory and one or more processors, the memory stores computer readable instructions, when the computer readable instructions are executed by the processor, the one or more processors execute The following steps:
- the operation is executed, and the lock data corresponding to the operation is added to the operation lock record table.
- One or more non-volatile computer-readable storage media storing computer-readable instructions.
- the computer-readable instructions When executed by one or more processors, the one or more processors perform the following steps:
- the operation is executed, and the lock data corresponding to the operation is added to the operation lock record table.
- Fig. 1 is an application scenario diagram of a database operation control method according to one or more embodiments.
- Fig. 2 is a schematic flowchart of a method for controlling database operations according to one or more embodiments.
- Fig. 3 is a schematic flowchart of a step of searching lock data corresponding to an operation according to one or more embodiments.
- Fig. 4 is a block diagram of a database operation control device according to one or more embodiments.
- Figure 5 is a block diagram of a computer device according to one or more embodiments.
- the database operation control method provided in this application can be applied to the application environment as shown in FIG. 1.
- the terminal 102 communicates with the server 104 through the network through the network.
- the terminal 102 sends a database operation request to the server 104.
- the server 104 extracts the operation identifier carried in the request, searches for the lock data corresponding to the operation identifier, and determines whether the lock data conflicts with the lock data being executed in the operation lock record table.
- the conflict judgment result controls whether the currently requested operation is executed.
- the terminal 102 may be, but is not limited to, various personal computers, notebook computers, smart phones, tablet computers, and portable wearable devices.
- the server 104 may be implemented by an independent server or a server cluster composed of multiple servers.
- a database operation control method is provided. Taking the method applied to the server in FIG. 1 as an example for description, the method includes the following steps:
- Step 202 Receive a database operation request, and the request carries an operation identifier.
- the server can perform a series of database operations.
- Distributed relational database services include many operable entities, such as MyCat entities, MySQL entities, and so on.
- the terminal can request the operation of any object in the database, such as requesting to release the MyCat entity and request to restart the MySQL entity.
- the requested operation identifier can be the name of the requested operation, such as "release MyCat entity”, “restart MySQL entity”, or the operation code, such as OTD:DC (meaning “release MyCat entity”), OTY:RS (meaning “ Restart the MySQL entity”).
- Step 204 Search for lock data corresponding to the operation identifier.
- the lock data includes the operation object corresponding to the operation identifier and the lock type corresponding to each operation object.
- the lock types include exclusive locks and shared locks.
- the operation object corresponding to each operation identifier and the lock type corresponding to each operation object are defined in advance.
- the lock type corresponding to the operation object can be an exclusive lock or a shared lock.
- the lock type corresponding to the operation object is defined according to the actual business logic. If in the actual business logic, if an operation object can be used by multiple operation threads at the same time, and multiple operation threads call and execute the operation object at the same time without any failure, add a shared lock for the operation object. Correspondingly, if a certain operation object cannot be used by multiple operation threads at the same time, and multiple operation threads call and execute the operation object at the same time, it will fail, so add an exclusive lock for the operation object.
- the lock data corresponding to the operation includes the operation object and the lock type corresponding to each operation object.
- the lock data corresponding to the operation identifier may be operation object A-exclusive lock, operation object B-shared lock, operation object C exclusive lock, etc.
- Step 206 Determine whether the lock data conflicts with the lock data in the operation lock record table according to the pre-defined mutual exclusion relationship of lock types.
- the lock data in the operation lock record table includes the lock data corresponding to the operation being executed in the status. , Go to step 208, otherwise, go to step 210.
- Step 208 Block the requested operation.
- Step 210 Perform an operation, and add lock data corresponding to the operation to the operation lock record table.
- determining whether the lock data conflicts with the lock data in the operation lock record table according to the pre-defined mutual exclusion relationship of lock types includes: if the lock type of the operation object in the current request is a shared lock, and When the lock type of the same operation object in the operation lock record table is an exclusive lock, it is determined that the lock data conflicts;
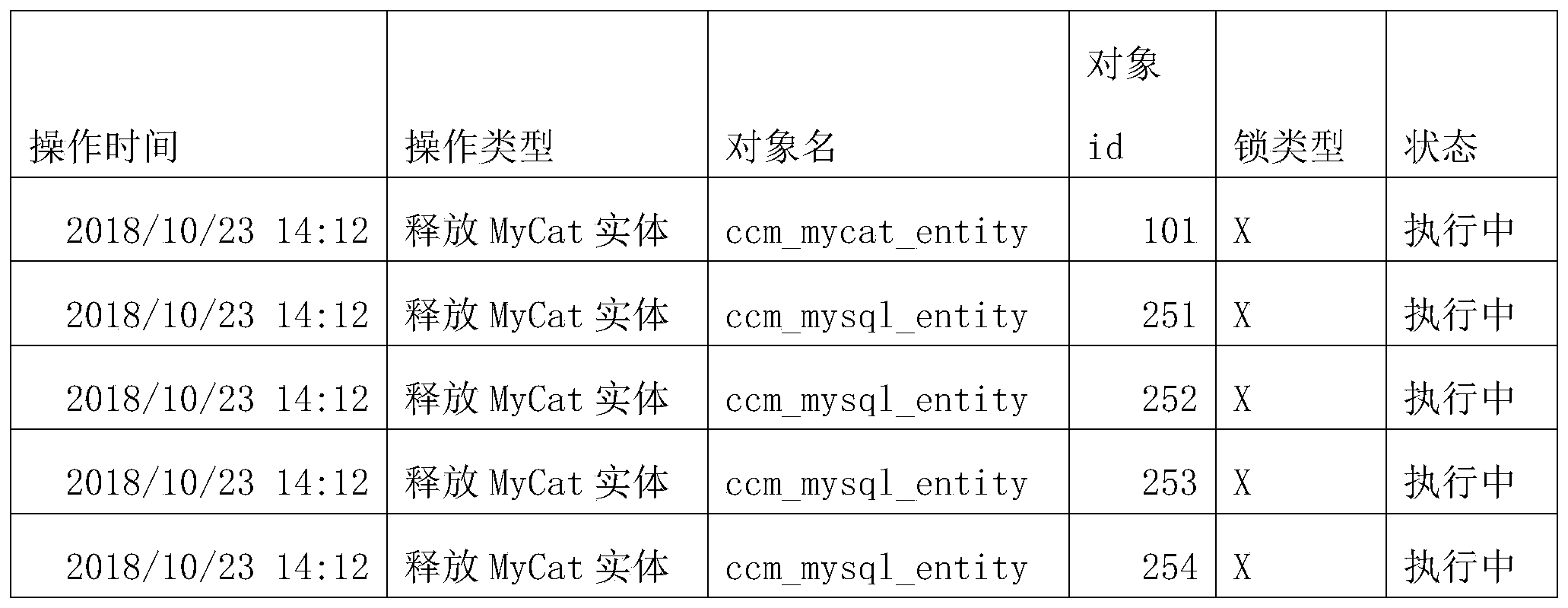
- the operation lock record table records the lock data corresponding to the operation currently being performed, as shown in Table 1 below.
- the operation being performed in Table 1 is "release MyCat entity".
- the operation lock record table records the lock information of all operation objects currently being executed.
- the server After the server receives the new operation request, it extracts the lock data corresponding to the new operation request, and judges whether the lock data corresponding to the new operation request conflicts with the lock data corresponding to the operation being performed in the operation lock data table, and if so, it blocks New operation request. Exclusive locks conflict with shared locks, exclusive locks conflict with exclusive locks, and shared locks do not conflict with shared locks.
- the operation lock record when the operation object involved in the new operation request is a shared lock and the same operation object in the operation lock record table is also a shared lock, or the operation object in the new operation request is a shared lock or an exclusive lock, the operation lock record If there is no lock record for the same operation object in the table (that is, the operation object is not locked in the operation lock record), the lock data of the operation object does not conflict.
- the operation conflicts with the operation lock record table. As long as all operation objects of the requested operation do not conflict with the operation lock record table, the operation does not conflict with the operation lock record table.
- the operation lock record table is shown in Table 1.
- the currently requested operation is "Restart MySQL”
- the lock type corresponding to the operation object is an exclusive lock.
- the server monitors the operation being performed, and when the operation is completed, it automatically deletes the corresponding operation lock record from the operation lock record table. If the execution of "Release MyCat Entity" is completed, the operation time in Table 1 is "2018/10/23 14:12" and the operation type is "Release MyCat Entity” operation lock data is automatically deleted.
- the server after the server blocks the mutually exclusive request, it adds a label to the blocked operation.
- the label includes abandonment and wait. If the waiting label is added to the blocked operation, the target lock record that is mutually exclusive with the operation in the operation lock record is monitored. When the target lock record is deleted from the operation lock record, the blocked operation is automatically executed. If the blocked operation adds a discarded label, the blocked operation will not be executed again.
- the currently requested operation is "Restart MySQL”
- the operation object corresponding to the operation is defined in advance
- the lock type is defined for the operation object
- whether the currently requested operation is executed is determined by whether there is a lock conflict between the currently requested operation and the currently executed operation.
- the mutual exclusion judgment between various operations can be realized only by pre-defining the lock data corresponding to the operation and the mutual exclusion rules between the lock data. .
- step 204 searching for lock data corresponding to the operation identifier, includes:
- Step 302 Obtain an operation definition corresponding to the operation identifier, where the operation definition includes a query statement.
- release MyCat entity includes two definition lines. The difference is that the query statements are different.
- the meaning of the query statement in the first definition line is: find id_mycat_entity, and find id_mysql_entity associated with id_mycat_entity from ccm_mycat_member. Simply put, it is to find the mysql entity associated with the MyCat entity.
- the query statement in the second definition line is: query the id_mycat_entity of the mycat entity itself.
- Step 304 Search for an operation object corresponding to the operation identifier according to the query statement.
- the operation object includes the operation itself and configuration items associated with the operation.
- the server searches for the operation definition corresponding to "Release MyCat Entity", such as the first row and the second row in Table 3. Then get the query statement in the definition, and find the operation object associated with "release MyCat entity” from the configuration management system through the first query statement.
- the configuration management database records the information of related configuration items. Let's take the DRDS distributed relational database service (Distributed Relational Database Service) as an example.
- CCM_MYCAT_ENTITY is the table corresponding to MyCat entity, MyCat entity is a configuration item, it is a distributed database middleware.
- One MyCat entity corresponds to multiple MySQL entities (that is, another configuration item), and the relationship between the MyCat entity and the MySQL entity is recorded in ccm_mycat_member. Therefore, first obtain the identity of the MyCat entity (101), and then look up the MySQL entity associated with the MyCat entity from the mycat_member association table.
- the same ccm_mycat_entity is determined based on the locked object in the definition, and 101 is found by the query statement.
- configuration items of other dimensions associated with the "release MyCat entity" operation. If there are, there are third and fourth rows of definitions when defining the release of the MyCat entity operation. Etc., each row defines configuration items corresponding to a dimension, and configuration items of the same dimension have the same lock type. For example, there are 4 associated id_mysql_entity in the first row. These four configuration items belong to the same latitude, and the corresponding lock type is also The same, as shown in Table 3, is an exclusive lock. Configuration items in other dimensions are configured as exclusive locks or shared locks according to specific business logic.
- Step 306 Obtain the lock type corresponding to each operation object from the operation definition.
- Step 308 Generate lock data corresponding to the operation identifier according to the operation object and the lock type corresponding to the operation object.
- the query statement is used to query the multi-dimensional configuration items associated with the current operation and the operation itself, and these configuration items and the operation itself are the operation objects corresponding to the operation. Obtain the lock type corresponding to each operation object from the operation definition.
- the operation object corresponding to the operation identifier and the lock type corresponding to each operation object constitute the lock data of the current operation.
- the configuration management library is constructed through the influence relationship between operations, the standard operations are defined according to the association relationship between the configurations in the configuration management library, and the associated configuration items and configuration items of the identification operations are searched through the query statements in the standard operation definitions.
- Lock type Quickly querying the configuration items that have an influence relationship with the current requested operation is the main prerequisite for judging the operation conflict.
- all the configuration items that have an influence relationship corresponding to the operation can be predefined, and these configuration items can be quickly obtained based on the query statement.
- Configuration item Comprehensive consideration of all associated configuration items (including the operation itself) can make the operation conflict judgment more accurate, and effectively reduce the probability of operation execution failure.
- the operation object corresponding to the currently requested operation includes the operation itself and the multi-dimensional configuration items associated with the operation.
- step 206 it is determined whether the lock data conflicts with the lock data in the operation lock record table, specifically:
- the meaning of the operation lock record table to lock the operation object is that there is a lock record for the operation object in the operation record table.
- the operation object corresponding to the currently requested operation includes multiple operation objects, which are the operation itself and associated multi-dimensional configuration items.
- operation objects which are the operation itself and associated multi-dimensional configuration items.
- the operation itself, the configuration item of the first dimension, and the configuration item of the second dimension are included, assuming that each dimension includes only one configuration item.
- each dimension configuration item may also include multiple configuration items.
- the server determines one by one whether the operation itself is locked in the operation lock record table, whether the first dimension configuration item is locked, whether the second dimension configuration item is locked, if the operation lock record table is for these operation objects Locking means that the lock data of the current operation does not conflict with the lock data in the operation lock record table, and the currently requested operation can be directly executed, and the lock data corresponding to the currently requested operation is added to the operation lock record table.
- the lock type is an exclusive lock, the lock data of the operation object conflicts.
- the lock data of any operation object conflicts with the lock data in the operation lock record table
- the lock data of the operation conflicts with the lock data in the operation lock record table.
- only The lock data corresponding to all operation objects does not conflict with the lock data in the operation lock record table, and the lock data of the operation does not conflict with the lock data in the operation lock record table.
- the operation lock record table is shown in Table 1.
- the currently requested operation is "Restart MySQL”
- the lock type corresponding to the operation object is an exclusive lock.
- a blocking reminder template can be defined in advance. When a blocking reminder is generated, the data in the target lock record is filled into the blocking reminder template to generate a blocking reminder.
- a database operation control device including: an operation request receiving module 402, a lock data search module 404, a conflict judgment module 406, a blocking module 408, and an execution module 410, wherein :
- the operation request receiving module 402 is configured to receive a database operation request, and the request carries an operation identifier.
- the lock data search module 404 is used to search for lock data corresponding to the operation identifier.
- the lock data includes the operation object corresponding to the operation identifier and the lock type corresponding to each operation object.
- the conflict judgment module 406 is used to judge whether the lock data conflicts with the lock data in the operation lock record table according to the pre-defined mutual exclusion relationship of lock types.
- the lock data in the operation lock record table includes the status corresponding to the operation being executed Lock data.
- the blocking module 408 If yes, enter the blocking module 408, otherwise enter the execution module 410; the blocking module 408 is used to block the requested operation; the execution module 410 is used to perform the operation and add the lock data corresponding to the operation to the operation lock record table.
- the lock types include exclusive locks and shared locks; the conflict judgment module 404 is also used to if the lock type of the operation object in the current request is a shared lock, and the lock type of the same operation object in the operation lock record table is When an exclusive lock is used, it is determined that the lock data conflicts; or the lock type of the operation object in the current request is an exclusive lock, and when the same operation object in the operation lock record table is an exclusive lock or a shared lock, it is determined that the lock data conflicts.
- the lock data search module 404 is also used to obtain the operation definition corresponding to the operation identification.
- the operation definition includes a query statement; according to the query statement, the operation object corresponding to the operation identification is found.
- the operation object includes the operation itself and the operation Associated configuration items; obtain the lock type corresponding to each operation object from the operation definition; and generate lock data corresponding to the operation identifier according to the operation object and the lock type corresponding to the operation object.
- the conflict judgment module 404 is also used to judge whether the operation object is locked in the operation lock record table; if so, it is judged whether the lock record in the operation lock record table matches the lock type of the operation object in the operation definition. Conflict; if the lock type of any operation object conflicts with the lock record, the operation is blocked; and if the lock type of all operation objects does not conflict with the lock record, the operation is executed.
- the database operation control device further includes a blocking reminder module for obtaining conflicting target lock records from the operation lock records; and generating a blocking reminder according to the target lock record, and sending the blocking reminder to the operation request terminal.
- the database operation control device further includes an operation lock record table update module for monitoring the operation being performed; and when the operation is completed, the lock data corresponding to the operation is deleted from the operation lock record table.
- the operation lock record table update module is also used to mark the blocked operation according to the tag; when the tag is a waiting tag, monitor the target lock record in the operation lock record that is mutually exclusive with the operation; and when the target lock After the record is deleted from the operation lock record, the operation of waiting for label marking is performed.
- Each module in the aforementioned database operation control device can be implemented in whole or in part by software, hardware, and a combination thereof.
- the above modules may be embedded in the form of hardware or independent of the processor in the computer equipment, or may be stored in the memory of the computer equipment in the form of software, so that the processor can call and execute the operations corresponding to the above modules.
- a computer device is provided.
- the computer device may be a server, and its internal structure diagram may be as shown in FIG. 5.
- the computer equipment includes a processor, a memory, a network interface and a database connected through a system bus. Among them, the processor of the computer device is used to provide calculation and control capabilities.
- the memory of the computer device includes a non-volatile storage medium and an internal memory.
- the non-volatile storage medium stores an operating system, computer readable instructions, and a database.
- the internal memory provides an environment for the operation of the operating system and computer-readable instructions in the non-volatile storage medium.
- the database of the computer equipment is used to store lock data.
- the network interface of the computer device is used to communicate with an external terminal through a network connection.
- the computer readable instruction is executed by the processor to realize a database operation control method.
- FIG. 5 is only a block diagram of a part of the structure related to the solution of the present application, and does not constitute a limitation on the computer device to which the solution of the present application is applied.
- the specific computer device may Including more or fewer parts than shown in the figure, or combining some parts, or having a different arrangement of parts.
- a computer device includes a memory and one or more processors.
- the memory stores computer readable instructions.
- the one or more processors execute the method in the foregoing method embodiment. step.
- One or more non-volatile computer-readable storage media storing computer-readable instructions.
- the computer-readable instructions are executed by one or more processors, one or more processors execute A step of.
- Non-volatile memory may include read only memory (ROM), programmable ROM (PROM), electrically programmable ROM (EPROM), electrically erasable programmable ROM (EEPROM), or flash memory.
- ROM read only memory
- PROM programmable ROM
- EPROM electrically programmable ROM
- EEPROM electrically erasable programmable ROM
- Volatile memory may include random access memory (RAM) or external cache memory.
- RAM is available in many forms, such as static RAM (SRAM), dynamic RAM (DRAM), synchronous DRAM (SDRAM), double data rate SDRAM (DDRSDRAM), enhanced SDRAM (ESDRAM), synchronous chain Channel (Synchlink) DRAM (SLDRAM), memory bus (Rambus) direct RAM (RDRAM), direct memory bus dynamic RAM (DRDRAM), and memory bus dynamic RAM (RDRAM), etc.
Landscapes
- Engineering & Computer Science (AREA)
- Theoretical Computer Science (AREA)
- Databases & Information Systems (AREA)
- Data Mining & Analysis (AREA)
- Physics & Mathematics (AREA)
- General Engineering & Computer Science (AREA)
- General Physics & Mathematics (AREA)
- Software Systems (AREA)
- Information Retrieval, Db Structures And Fs Structures Therefor (AREA)
Abstract
Description
本申请要求于2019年02月20日提交至中国专利局,申请号为2019101257260,申请名称为“数据库操作控制方法、装置、计算机设备和存储介质”的中国专利申请的优先权,其全部内容通过引用结合在本申请中。This application claims the priority of the Chinese patent application filed to the Chinese Patent Office on February 20, 2019, with the application number 2019101257260 and the application titled "Database Operation Control Method, Device, Computer Equipment, and Storage Medium". The reference is incorporated in this application.
本申请涉及一种数据库操作控制方法、装置、计算机设备和存储介质。This application relates to a database operation control method, device, computer equipment and storage medium.
在数据库服务中,客户会对很多对象(如DB实例,用户等)做很多操作,且大部分操作都不是立即完成,耗时几十秒到几分钟不等。不同的客户对不同对象的操作可能会有相关性,有的会有互相影响,不可以同时执行。例如有客户U1正在为A库扩容存储,还没有完成时,客户U2发起为A库创建同城灾备库,那么后者不应该允许执行,否则会造成执行到一半就报错,后续很难继续进行或回滚。发明人意识到,为了避免操作之间的冲突,传统的做法是将这些业务规则硬编码在程序里实现。但当数据库产品量较大时,硬编码根本没办法应对如此庞大的业务逻辑。In database services, customers do many operations on many objects (such as DB instances, users, etc.), and most of the operations are not completed immediately, which takes tens of seconds to several minutes. The operations of different customers on different objects may be related, and some may affect each other, and cannot be executed at the same time. For example, if customer U1 is expanding the storage capacity for library A, when customer U2 initiates the creation of a same-city disaster recovery library for library A, then the latter should not be allowed to execute, otherwise an error will be reported in the middle of the execution, and it will be difficult to continue. Or roll back. The inventor realizes that in order to avoid conflicts between operations, the traditional approach is to hard-code these business rules into the program. But when the volume of database products is large, hard coding simply cannot cope with such a huge business logic.
发明内容Summary of the invention
根据本申请公开的各种实施例,提供一种数据库操作控制方法、装置、计算机设备和存储介质。According to various embodiments disclosed in the present application, a database operation control method, device, computer equipment, and storage medium are provided.
一种数据库操作控制方法包括:A database operation control method includes:
接收数据库操作请求,所述请求中携带操作标识;Receiving a database operation request, the request carrying an operation identifier;
查找与所述操作标识对应的锁数据,所述锁数据包括所述操作标识对应的操作对象以及每个所述操作对象对应的锁类型;Searching lock data corresponding to the operation identifier, where the lock data includes the operation object corresponding to the operation identifier and the lock type corresponding to each operation object;
根据预先定义的锁类型互斥关系,判断所述锁数据是否与操作锁记录表中 的锁数据相冲突,所述操作锁记录表中的锁数据包括状态为正在执行的操作对应的锁数据;Determine whether the lock data conflicts with the lock data in the operation lock record table according to the pre-defined mutual exclusion relationship of lock types, and the lock data in the operation lock record table includes lock data corresponding to the operation being executed in the state;
若所述锁数据与操作锁记录表中的锁数据相冲突,则阻塞请求的操作;及If the lock data conflicts with the lock data in the operation lock record table, the requested operation is blocked; and
若所述锁数据与操作锁记录表中的锁数据不相冲突,则执行所述操作,将所述操作对应的锁数据添加至所述操作锁记录表。If the lock data does not conflict with the lock data in the operation lock record table, the operation is executed, and the lock data corresponding to the operation is added to the operation lock record table.
一种数据库操作控制装置包括:A database operation control device includes:
操作请求接收模块,用于接收数据库操作请求,所述请求中携带操作标识;The operation request receiving module is configured to receive a database operation request, and the request carries an operation identifier;
锁数据查找模块,用于查找与所述操作标识对应的锁数据,所述锁数据包括所述操作标识对应的操作对象以及每个所述操作对象对应的锁类型;A lock data search module, configured to search lock data corresponding to the operation identifier, the lock data including the operation object corresponding to the operation identifier and the lock type corresponding to each operation object;
冲突判断模块,用于根据预先定义的锁类型互斥关系,判断所述锁数据是否与操作锁记录表中的锁数据相冲突,所述操作锁记录表中的锁数据包括状态为正在执行的操作对应的锁数据;The conflict judgment module is used for judging whether the lock data conflicts with the lock data in the operation lock record table according to the pre-defined mutual exclusion relationship of lock types. The lock data in the operation lock record table includes the status of being executed Operate the corresponding lock data;
若是,则进入阻塞模块,否则进入执行模块;及If yes, enter the blocking module, otherwise enter the execution module; and
所述阻塞模块,用于阻塞请求的操作;所述执行模块,用于执行所述操作,将所述操作对应的锁数据添加至所述操作锁记录表。The blocking module is used to block the requested operation; the execution module is used to execute the operation and add lock data corresponding to the operation to the operation lock record table.
一种计算机设备,包括存储器和一个或多个处理器,所述存储器中储存有计算机可读指令,所述计算机可读指令被所述处理器执行时,使得所述一个或多个处理器执行以下步骤:A computer device, including a memory and one or more processors, the memory stores computer readable instructions, when the computer readable instructions are executed by the processor, the one or more processors execute The following steps:
接收数据库操作请求,所述请求中携带操作标识;Receiving a database operation request, the request carrying an operation identifier;
查找与所述操作标识对应的锁数据,所述锁数据包括所述操作标识对应的操作对象以及每个所述操作对象对应的锁类型;Searching lock data corresponding to the operation identifier, where the lock data includes the operation object corresponding to the operation identifier and the lock type corresponding to each operation object;
根据预先定义的锁类型互斥关系,判断所述锁数据是否与操作锁记录表中的锁数据相冲突,所述操作锁记录表中的锁数据包括状态为正在执行的操作对应的锁数据;Judging whether the lock data conflicts with the lock data in the operation lock record table according to the pre-defined mutual exclusion relationship of lock types, and the lock data in the operation lock record table includes the lock data corresponding to the operation being executed;
若所述锁数据与操作锁记录表中的锁数据相冲突,则阻塞请求的操作;及If the lock data conflicts with the lock data in the operation lock record table, the requested operation is blocked; and
若所述锁数据与操作锁记录表中的锁数据不相冲突,则执行所述操作,将所述操作对应的锁数据添加至所述操作锁记录表。If the lock data does not conflict with the lock data in the operation lock record table, the operation is executed, and the lock data corresponding to the operation is added to the operation lock record table.
一个或多个存储有计算机可读指令的非易失性计算机可读存储介质,计算 机可读指令被一个或多个处理器执行时,使得一个或多个处理器执行以下步骤:One or more non-volatile computer-readable storage media storing computer-readable instructions. When the computer-readable instructions are executed by one or more processors, the one or more processors perform the following steps:
接收数据库操作请求,所述请求中携带操作标识;Receiving a database operation request, the request carrying an operation identifier;
查找与所述操作标识对应的锁数据,所述锁数据包括所述操作标识对应的操作对象以及每个所述操作对象对应的锁类型;Searching lock data corresponding to the operation identifier, where the lock data includes the operation object corresponding to the operation identifier and the lock type corresponding to each operation object;
根据预先定义的锁类型互斥关系,判断所述锁数据是否与操作锁记录表中的锁数据相冲突,所述操作锁记录表中的锁数据包括状态为正在执行的操作对应的锁数据;Judging whether the lock data conflicts with the lock data in the operation lock record table according to the pre-defined mutual exclusion relationship of lock types, and the lock data in the operation lock record table includes the lock data corresponding to the operation being executed;
若所述锁数据与操作锁记录表中的锁数据相冲突,则阻塞请求的操作;及If the lock data conflicts with the lock data in the operation lock record table, the requested operation is blocked; and
若所述锁数据与操作锁记录表中的锁数据不相冲突,则执行所述操作,将所述操作对应的锁数据添加至所述操作锁记录表。If the lock data does not conflict with the lock data in the operation lock record table, the operation is executed, and the lock data corresponding to the operation is added to the operation lock record table.
本申请的一个或多个实施例的细节在下面的附图和描述中提出。本申请的其它特征和优点将从说明书、附图以及权利要求书变得明显。The details of one or more embodiments of the application are set forth in the following drawings and description. Other features and advantages of this application will become apparent from the description, drawings and claims.
为了更清楚地说明本申请实施例中的技术方案,下面将对实施例中所需要使用的附图作简单地介绍,显而易见地,下面描述中的附图仅仅是本申请的一些实施例,对于本领域普通技术人员来讲,在不付出创造性劳动的前提下,还可以根据这些附图获得其它的附图。In order to more clearly describe the technical solutions in the embodiments of the present application, the following will briefly introduce the drawings needed in the embodiments. Obviously, the drawings in the following description are only some embodiments of the present application. For those of ordinary skill in the art, other drawings can be obtained based on these drawings without creative work.
图1为根据一个或多个实施例中数据库操作控制方法的应用场景图。Fig. 1 is an application scenario diagram of a database operation control method according to one or more embodiments.
图2为根据一个或多个实施例中数据库操作控制方法的流程示意图。Fig. 2 is a schematic flowchart of a method for controlling database operations according to one or more embodiments.
图3为根据一个或多个实施例中查找与操作对应的锁数据步骤的流程示意图。Fig. 3 is a schematic flowchart of a step of searching lock data corresponding to an operation according to one or more embodiments.
图4为根据一个或多个实施例中数据库操作控制装置的框图。Fig. 4 is a block diagram of a database operation control device according to one or more embodiments.
图5为根据一个或多个实施例中计算机设备的框图。Figure 5 is a block diagram of a computer device according to one or more embodiments.
为了使本申请的技术方案及优点更加清楚明白,以下结合附图及实施例,对本申请进行进一步详细说明。应当理解,此处描述的具体实施例仅仅用以解 释本申请,并不用于限定本申请。In order to make the technical solutions and advantages of the present application clearer, the following further describes the present application in detail with reference to the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the application, but not to limit the application.
本申请提供的数据库操作控制方法,可以应用于如图1所示的应用环境中。终端102通过网络与服务器104通过网络进行通信。终端102向服务器104发送数据库操作请求,服务器104提取请求中携带的操作标识,查找与操作标识对应的锁数据,判断锁数据是否与操作锁记录表中的正在执行的锁数据相冲突,根据是否冲突的判断结果控制当前请求的操作是否执行。终端102可以但不限于是各种个人计算机、笔记本电脑、智能手机、平板电脑和便携式可穿戴设备,服务器104可以用独立的服务器或者是多个服务器组成的服务器集群来实现。The database operation control method provided in this application can be applied to the application environment as shown in FIG. 1. The
在其中一个实施例中,如图2所示,提供了一种数据库操作控制方法,以该方法应用于图1中的服务器为例进行说明,包括以下步骤:In one of the embodiments, as shown in FIG. 2, a database operation control method is provided. Taking the method applied to the server in FIG. 1 as an example for description, the method includes the following steps:
步骤202,接收数据库操作请求,请求中携带操作标识。Step 202: Receive a database operation request, and the request carries an operation identifier.
基于终端的请求,服务器可执行一系列的数据库操作。以分布式关系型数据库服务为例,分布式关系型数据库服务包括很多可操作的实体,如MyCat实体、MySQL实体等等。Based on the request of the terminal, the server can perform a series of database operations. Take distributed relational database services as an example. Distributed relational database services include many operable entities, such as MyCat entities, MySQL entities, and so on.
终端可以请求数据库中任意对象的操作,如请求释放MyCat实体,请求重启MySQL实体。The terminal can request the operation of any object in the database, such as requesting to release the MyCat entity and request to restart the MySQL entity.
请求操作标识可以是请求操作的名称,如“释放MyCat实体”、“重启MySQL实体”,还可以是操作代码,如OTD:DC(含义是“释放MyCat实体”),OTY:RS(含义是“重启MySQL实体”)。The requested operation identifier can be the name of the requested operation, such as "release MyCat entity", "restart MySQL entity", or the operation code, such as OTD:DC (meaning "release MyCat entity"), OTY:RS (meaning " Restart the MySQL entity").
步骤204,查找与操作标识对应的锁数据,锁数据包括操作标识对应的操作对象以及每个操作对象对应的锁类型。Step 204: Search for lock data corresponding to the operation identifier. The lock data includes the operation object corresponding to the operation identifier and the lock type corresponding to each operation object.
在其中一个实施例中,锁类型包括独占锁和共享锁。In one of the embodiments, the lock types include exclusive locks and shared locks.
预先定义好每个操作标识对应的操作对象以及每个操作对象对应的锁类型,操作对象对应的锁类型可以是独占锁也可以是共享锁。操作对象对应的锁类型根据实际的业务逻辑进行定义。若实际业务逻辑中,如果某一个操作对象能够同时被多个操作线程使用,多个操作线程同时调用执行该操作对象而不会出现任何故障,则为该操作对象添加共享锁。相应的,如果某一个操作对象不能够同时被多个操作线程使用,多个操作线程同时调用执行该操作对象会出现 故障,则为该操作对象添加独占锁。The operation object corresponding to each operation identifier and the lock type corresponding to each operation object are defined in advance. The lock type corresponding to the operation object can be an exclusive lock or a shared lock. The lock type corresponding to the operation object is defined according to the actual business logic. If in the actual business logic, if an operation object can be used by multiple operation threads at the same time, and multiple operation threads call and execute the operation object at the same time without any failure, add a shared lock for the operation object. Correspondingly, if a certain operation object cannot be used by multiple operation threads at the same time, and multiple operation threads call and execute the operation object at the same time, it will fail, so add an exclusive lock for the operation object.
操作对应的锁数据包括操作对象以及每个操作对象对应的锁类型。举例来说,操作标识对应的锁数据可以是,操作对象A-独占锁,操作对象B-共享锁、操作对象C独占锁等。The lock data corresponding to the operation includes the operation object and the lock type corresponding to each operation object. For example, the lock data corresponding to the operation identifier may be operation object A-exclusive lock, operation object B-shared lock, operation object C exclusive lock, etc.
步骤206,根据预先定义的锁类型互斥关系,判断锁数据是否与操作锁记录表中的锁数据相冲突,操作锁记录表中的锁数据包括状态为正在执行的操作对应的锁数据,若是,执行步骤208,否则,执行步骤210。Step 206: Determine whether the lock data conflicts with the lock data in the operation lock record table according to the pre-defined mutual exclusion relationship of lock types. The lock data in the operation lock record table includes the lock data corresponding to the operation being executed in the status. , Go to step 208, otherwise, go to step 210.
步骤208,阻塞请求的操作。Step 208: Block the requested operation.
步骤210,执行操作,将操作对应的锁数据添加至操作锁记录表。Step 210: Perform an operation, and add lock data corresponding to the operation to the operation lock record table.
在其中一个实施例中,根据预先定义的锁类型互斥关系,判断锁数据是否与操作锁记录表中的锁数据相冲突,包括:若当前请求中的操作对象的锁类型为共享锁,且操作锁记录表中同一操作对象的锁类型为独占锁时,确定锁数据相冲突;In one of the embodiments, determining whether the lock data conflicts with the lock data in the operation lock record table according to the pre-defined mutual exclusion relationship of lock types includes: if the lock type of the operation object in the current request is a shared lock, and When the lock type of the same operation object in the operation lock record table is an exclusive lock, it is determined that the lock data conflicts;
或当前请求中操作对象的锁类型为独占锁,操作锁记录表中同一操作对象为独占锁或者共享锁时,确定锁数据相冲突。Or when the lock type of the operation object in the current request is an exclusive lock, and the same operation object in the operation lock record table is an exclusive lock or a shared lock, it is determined that the lock data conflicts.
操作锁记录表记录当前正在执行的操作对应的锁数据,如下表1所示。The operation lock record table records the lock data corresponding to the operation currently being performed, as shown in Table 1 below.
表1Table 1
表1中正在执行的操作为“释放MyCat实体”,该操作对应的操作对象包括ccm_mycat_entity=101,ccm_mysql_entity=251,ccm_mysql_entity=252,ccm_mysql_entity=253,ccm_mysql_entity=254,这些操作对象对应的锁类型均为 X(独占锁)。也就是说,操作锁记录表中记录当前正在执行的所有操作对象的锁信息。The operation being performed in Table 1 is "release MyCat entity". The operation objects corresponding to this operation include ccm_mycat_entity=101, ccm_mysql_entity=251, ccm_mysql_entity=252, ccm_mysql_entity=253, ccm_mysql_entity=254, and the lock types corresponding to these operation objects are all X (exclusive lock). In other words, the operation lock record table records the lock information of all operation objects currently being executed.
服务器接收到新的操作请求后,提取新的操作请求对应的锁数据,判断新的操作请求对应的锁数据是否与操作锁数据表中正在执行的操作对应的锁数据相冲突,若是,则阻塞新的操作请求。独占锁与共享锁相冲突,独占锁与独占锁相冲突,共享锁与共享锁不相冲突。对应同一操作对象,当新的操作请求中涉及的操作对象是共享锁且操作锁记录表中同一操作对象也是共享锁,或者新的操作请求中该操作对象为共享锁或者独占锁,操作锁记录表中没有关于同一操作对象的锁记录(也即是操作锁记录中没有对该操作对象上锁)则该操作对象的锁数据不相冲突。After the server receives the new operation request, it extracts the lock data corresponding to the new operation request, and judges whether the lock data corresponding to the new operation request conflicts with the lock data corresponding to the operation being performed in the operation lock data table, and if so, it blocks New operation request. Exclusive locks conflict with shared locks, exclusive locks conflict with exclusive locks, and shared locks do not conflict with shared locks. Corresponding to the same operation object, when the operation object involved in the new operation request is a shared lock and the same operation object in the operation lock record table is also a shared lock, or the operation object in the new operation request is a shared lock or an exclusive lock, the operation lock record If there is no lock record for the same operation object in the table (that is, the operation object is not locked in the operation lock record), the lock data of the operation object does not conflict.
当前请求的操作中任一操作对象与操作锁记录表相冲突,则该操作与操作锁记录表相冲突。只要当请求的操作的所有操作对象均不与操作锁记录表相冲突,该操作才与操作锁记录表不相冲突。If any operation object in the currently requested operation conflicts with the operation lock record table, the operation conflicts with the operation lock record table. As long as all operation objects of the requested operation do not conflict with the operation lock record table, the operation does not conflict with the operation lock record table.
举例来说,操作锁记录表如表1所示,当前请求的操作为“重启MySQL”,经查找“重启MySQL”对应的操作对象为ccm_mysql_entity=251,该操作对象对应的锁类型为独占锁。For example, the operation lock record table is shown in Table 1. The currently requested operation is "Restart MySQL", the operation object corresponding to "Restart MySQL" is found to be ccm_mysql_entity=251, and the lock type corresponding to the operation object is an exclusive lock.
查询操作锁记录表,发现有正在执行的对象名=ccm_mysql_entity,对象id=251操作记录,操作记录表中该操作对象的锁类型为独占锁,因此,“重启MySQL实体”的操作对象与操作锁记录中的锁数据相冲突,故,服务器阻塞“重启MySQL实体”操作。Query the operation lock record table and find that there is an operation record that is executing object name=ccm_mysql_entity, object id=251, and the lock type of the operation object in the operation record table is an exclusive lock. Therefore, the operation object and operation lock of "restart MySQL entity" The lock data in the record conflicts, so the server blocks the "restart MySQL entity" operation.
进一步的,服务器监听正在执行的操作,当操作执行完成后,自动从操作锁记录表中删除相应的操作锁记录。如若“释放MyCat实体”执行完成后,自动将表1中操作时间为“2018/10/23 14:12”且操作类型为“释放MyCat实体”操作锁数据删除。Further, the server monitors the operation being performed, and when the operation is completed, it automatically deletes the corresponding operation lock record from the operation lock record table. If the execution of "Release MyCat Entity" is completed, the operation time in Table 1 is "2018/10/23 14:12" and the operation type is "Release MyCat Entity" operation lock data is automatically deleted.
在其中一个实施例中,服务器阻塞互斥的请求后,为阻塞的操作添加标签,标签包括放弃和等待。若阻塞的操作添加了等待的标签,则监听操作锁记录中与操作互斥的目标锁记录,当目标锁记录从操作锁记录中删除后,自动执行被阻塞的操作。如阻塞的操作添加了放弃的标签,则不再重新执行被阻塞的操作。In one of the embodiments, after the server blocks the mutually exclusive request, it adds a label to the blocked operation. The label includes abandonment and wait. If the waiting label is added to the blocked operation, the target lock record that is mutually exclusive with the operation in the operation lock record is monitored. When the target lock record is deleted from the operation lock record, the blocked operation is automatically executed. If the blocked operation adds a discarded label, the blocked operation will not be executed again.
又如,当前请求的操作为“重启MySQL”,经查找“重启MySQL”对应的操作对象为ccm_mysql_entity=257,该操作对象对应的锁类型为独占锁。而操作锁记录表中没有操作对象ccm_mysql_entity=257的操作记录,则当前请求的操作“重启MySQL”不与操作锁记录表冲突,故执行该操作,并且将该操作对应的锁数据添加至操作锁记录表。如表2所示:For another example, the currently requested operation is "Restart MySQL", the operation object corresponding to "Restart MySQL" is found to be ccm_mysql_entity=257, and the lock type corresponding to this operation object is an exclusive lock. If there is no operation record of the operation object ccm_mysql_entity=257 in the operation lock record table, the currently requested operation "restart MySQL" does not conflict with the operation lock record table, so the operation is executed and the lock data corresponding to the operation is added to the operation lock recording sheet. As shown in table 2:
表2Table 2
本实施例中,通过预先定义操作对应的操作对象,为操作对象定义锁类型,通过当前请求的操作与正在执行的操作是否存在锁冲突来判断是否执行当前请求的操作。本实施例中,无需通过编写大量的逻辑复杂的硬代码实现操作互斥,仅通过预先定义操作对应的锁数据以及锁数据之间的互斥规则即可实现各种操作之间的互斥判断。In this embodiment, the operation object corresponding to the operation is defined in advance, the lock type is defined for the operation object, and whether the currently requested operation is executed is determined by whether there is a lock conflict between the currently requested operation and the currently executed operation. In this embodiment, there is no need to write a large number of logically complex hard codes to achieve mutual exclusion of operations. The mutual exclusion judgment between various operations can be realized only by pre-defining the lock data corresponding to the operation and the mutual exclusion rules between the lock data. .
在其中一个实施例中,如图3所示,步骤204,查找与操作标识对应锁数据,包括:In one of the embodiments, as shown in FIG. 3, step 204, searching for lock data corresponding to the operation identifier, includes:
步骤302,获取与操作标识对应的操作定义,操作定义包括查询语句。Step 302: Obtain an operation definition corresponding to the operation identifier, where the operation definition includes a query statement.
预先定义标准操作,包括标准操作名称、操作代码、入参类型、查询语句以及锁类型。如表3所示:Predefine standard operations, including standard operation names, operation codes, input parameter types, query statements, and lock types. as shown in Table 3:
表3table 3
表格3中定义了两个标准操作,其中“释放MyCat实体”包括两个定义行,区别在于,查询语句不相同。第一定义行的查询语句的含义是:查找id_mycat_entity,从ccm_mycat_member中查找与id_mycat_entity关联的id_mysql_entity。简单的说,就是查找与MyCat实体关联的mysql实体。第二定义行的查询语句是:查询mycat实体自身的id_mycat_entity。Two standard operations are defined in Table 3. Among them, "release MyCat entity" includes two definition lines. The difference is that the query statements are different. The meaning of the query statement in the first definition line is: find id_mycat_entity, and find id_mysql_entity associated with id_mycat_entity from ccm_mycat_member. Simply put, it is to find the mysql entity associated with the MyCat entity. The query statement in the second definition line is: query the id_mycat_entity of the mycat entity itself.
步骤304,根据查询语句查找与操作标识对应的操作对象,操作对象包括操作本身以及操作所关联的配置项。Step 304: Search for an operation object corresponding to the operation identifier according to the query statement. The operation object includes the operation itself and configuration items associated with the operation.
若终端请求“释放MyCat实体”,则服务器查找“释放MyCat实体”对应的操作定义,如表格3中的第一行和第二行。然后获取定义中的查询语句,通过第一行查询语句从配置管理系统中查找与“释放MyCat实体”关联的操作对象。配置管理库中记录了具有相互关联的配置项信息,我们以DRDS分布式关系型数据库服务(Distributed Relational Database Service)为例进行说明。CCM_MYCAT_ENTITY是MyCat实体对应的表,MyCat实体即一个配置项,它是一种分布式数据库中间件。一个MyCat实体对应到多个MySQL实体(即另一种配置项),ccm_mycat_member中记录MyCat实体与MySQL实体之间的关联关系。因此,首先获取MyCat实体的标识(为101),然后从mycat_member关联表中查找与MyCat实体关联的MySQL实体。If the terminal requests "Release MyCat Entity", the server searches for the operation definition corresponding to "Release MyCat Entity", such as the first row and the second row in Table 3. Then get the query statement in the definition, and find the operation object associated with "release MyCat entity" from the configuration management system through the first query statement. The configuration management database records the information of related configuration items. Let's take the DRDS distributed relational database service (Distributed Relational Database Service) as an example. CCM_MYCAT_ENTITY is the table corresponding to MyCat entity, MyCat entity is a configuration item, it is a distributed database middleware. One MyCat entity corresponds to multiple MySQL entities (that is, another configuration item), and the relationship between the MyCat entity and the MySQL entity is recorded in ccm_mycat_member. Therefore, first obtain the identity of the MyCat entity (101), and then look up the MySQL entity associated with the MyCat entity from the mycat_member association table.
表4Table 4
如表4所示,在mycat_menber关联表中,查询到与id_mycat_entity(101)关联的id_mysql_entity有4个:251、252、253、254,因此,“释放MyCat实体”关联的操作对象包括ccm_mysql_entity=251,ccm_mysql_entity=252,ccm_mysql_entity=253,ccm_mysql_entity=254,其中ccm_mysql_entity是对象名,是根据定义中的上锁对象确定的。As shown in Table 4, in the mycat_menber association table, four id_mysql_entities associated with id_mycat_entity(101) are queried: 251, 252, 253, and 254. Therefore, the operation objects associated with "release MyCat entity" include ccm_mysql_entity=251, ccm_mysql_entity=252, ccm_mysql_entity=253, ccm_mysql_entity=254, where ccm_mysql_entity is the object name, which is determined according to the locked object in the definition.
通过第二行查询语句,select$1,查询到的是id_mycat_entity本身,确定的操作对象为ccm_mycat_entity=101,同样的ccm_mycat_entity是根据定义中的上锁对象确定的,101是查询语句查找出来的。Through the second line of query statement, select$1, the query is id_mycat_entity itself, and the determined operation object is ccm_mycat_entity=101. The same ccm_mycat_entity is determined based on the locked object in the definition, and 101 is found by the query statement.
进一步的,根据实际的业务逻辑,还可能存在与“释放MyCat实体”操作关联的其他维度的配置项,若存在,则在定义释放MyCat实体操作时,还存在第三行定义和第四行定义等,其中每行定义对应一个维度的配置项,同一维度的配置项具有相同的锁类型,如第一行中关联的id_mysql_entity有4个,这四个配置项属于同一纬度,对应的锁类型也是相同的,如表3所示,为独占锁。其他维度的配置项按照具体的业务逻辑,锁类型配置为独占锁或者共享锁。Further, according to the actual business logic, there may also be configuration items of other dimensions associated with the "release MyCat entity" operation. If there are, there are third and fourth rows of definitions when defining the release of the MyCat entity operation. Etc., each row defines configuration items corresponding to a dimension, and configuration items of the same dimension have the same lock type. For example, there are 4 associated id_mysql_entity in the first row. These four configuration items belong to the same latitude, and the corresponding lock type is also The same, as shown in Table 3, is an exclusive lock. Configuration items in other dimensions are configured as exclusive locks or shared locks according to specific business logic.
步骤306,从操作定义中获取每个操作对象对应的锁类型。Step 306: Obtain the lock type corresponding to each operation object from the operation definition.
步骤308,根据操作对象以及操作对象对应的锁类型,生成操作标识对应的锁数据。Step 308: Generate lock data corresponding to the operation identifier according to the operation object and the lock type corresponding to the operation object.
通过查询语句查询当前操作关联的多维度的配置项以及操作本身,这些配置项以及操作本身即为操作对应的操作对象。从操作定义中获取每个操作对象对应的锁类型。The query statement is used to query the multi-dimensional configuration items associated with the current operation and the operation itself, and these configuration items and the operation itself are the operation objects corresponding to the operation. Obtain the lock type corresponding to each operation object from the operation definition.
操作标识对应的操作对象以及每个操作对象对应的锁类型即构成了当前操作的锁数据。The operation object corresponding to the operation identifier and the lock type corresponding to each operation object constitute the lock data of the current operation.
本实施例中,通过操作之间的影响关系构建配置管理库,根据配置管理库中配置间的关联关系定义标准操作,通过标准操作定义中的查询语句查找标识 操作的关联配置项以及配置项的锁类型。快速查询到与当前请求操作具有影响关系的配置项是判断操作冲突的主要前提,本实施例中,可预先定义操作对应的所有的有影响关系的配置项,并且基于查询语句快速的获取到这些配置项。综合考虑所有的关联配置项(包括操作本身),可使操作冲突判断更加准确,有效减少了出现操作执行故障的几率。In this embodiment, the configuration management library is constructed through the influence relationship between operations, the standard operations are defined according to the association relationship between the configurations in the configuration management library, and the associated configuration items and configuration items of the identification operations are searched through the query statements in the standard operation definitions. Lock type. Quickly querying the configuration items that have an influence relationship with the current requested operation is the main prerequisite for judging the operation conflict. In this embodiment, all the configuration items that have an influence relationship corresponding to the operation can be predefined, and these configuration items can be quickly obtained based on the query statement. Configuration item. Comprehensive consideration of all associated configuration items (including the operation itself) can make the operation conflict judgment more accurate, and effectively reduce the probability of operation execution failure.
在其中一个实施例中,当前请求的操作对应的操作对象包括操作本身以及操作关联的多维度配置项,则步骤206,判断锁数据是否与操作锁记录表中的锁数据相冲突,具体为:In one of the embodiments, the operation object corresponding to the currently requested operation includes the operation itself and the multi-dimensional configuration items associated with the operation. In
逐一判断在操作锁记录表中是否对当前请求的操作对应的操作对象上锁。Judge one by one whether the operation object corresponding to the currently requested operation is locked in the operation lock record table.
操作锁记录表对操作对象上锁的含义为,操作记录表中存在对该操作对象的上锁记录,如表1所示,该操作锁记录表中对5个操作对象上了锁,分为为操作对象:ccm_mycat_entity=101,ccm_mysql_entity=251,ccm_mysql_entity=252,ccm_mysql_entity=253,ccm_mysql_entity=254。The meaning of the operation lock record table to lock the operation object is that there is a lock record for the operation object in the operation record table. As shown in Table 1, the operation lock record table locks 5 operation objects, which are divided into It is the operation object: ccm_mycat_entity=101, ccm_mysql_entity=251, ccm_mysql_entity=252, ccm_mysql_entity=253, ccm_mysql_entity=254.
本实施例中,当前请求的操作对应的操作对象包括由多个,分别为操作本身、关联的多维度配置项。例如包括操作本身、第一维度配置项和第二维度配置项,假设每个维度仅包括一个配置项。当然每个维度配置项也可以包括多个配置项。In this embodiment, the operation object corresponding to the currently requested operation includes multiple operation objects, which are the operation itself and associated multi-dimensional configuration items. For example, the operation itself, the configuration item of the first dimension, and the configuration item of the second dimension are included, assuming that each dimension includes only one configuration item. Of course, each dimension configuration item may also include multiple configuration items.
服务器逐一判断操作锁记录表中是否对操作本身上了锁,是否对第一维度配置项上了锁,是否对第二维度配置项上了锁,若操作锁记录表中均为对这些操作对象上锁,则说明当前操作的锁数据与操作锁记录表中的锁数据不相冲突,可直接执行当前请求的操作,并且将当前请求操作对应的锁数据添加至操作锁记录表中。The server determines one by one whether the operation itself is locked in the operation lock record table, whether the first dimension configuration item is locked, whether the second dimension configuration item is locked, if the operation lock record table is for these operation objects Locking means that the lock data of the current operation does not conflict with the lock data in the operation lock record table, and the currently requested operation can be directly executed, and the lock data corresponding to the currently requested operation is added to the operation lock record table.
若操作锁记录表存在对操作本身的上锁记录,则获取操作本身(其一操作对象)在操作锁记录中的锁类型,获取该操作对象在当前操作的锁数据中的锁类型,主要当两个锁类型均为共享锁时,该操作对象的锁数据才不冲突。或者仅获取操作锁记录中被上锁的操作对象的锁类型,若锁类型为独占锁,则该操作对象的锁数据相冲突。操作对应的所有操作对象中,存在任一个操作对象的锁数据与操作锁记录表中的锁数据相冲突,则该操作的锁数据与操作锁记录表 中的锁数据相冲突,相应的,只有所有的操作对象对应的锁数据与操作锁记录表中的锁数据均不相冲突,该操作的锁数据才不与操作锁记录表中的锁数据相冲突。If there is a lock record for the operation itself in the operation lock record table, obtain the lock type of the operation itself (one of the operation objects) in the operation lock record, and obtain the lock type of the operation object in the lock data of the current operation, mainly when When both lock types are shared locks, the lock data of the operation object does not conflict. Or only obtain the lock type of the locked operation object in the operation lock record. If the lock type is an exclusive lock, the lock data of the operation object conflicts. Among all operation objects corresponding to the operation, if the lock data of any operation object conflicts with the lock data in the operation lock record table, the lock data of the operation conflicts with the lock data in the operation lock record table. Correspondingly, only The lock data corresponding to all operation objects does not conflict with the lock data in the operation lock record table, and the lock data of the operation does not conflict with the lock data in the operation lock record table.
进一步的,在进行冲突判断时,若相冲突,则从操作锁记录表中获取与当前操作的操作对象的锁类型相冲突的锁记录。Further, during conflict judgment, if there is a conflict, a lock record that conflicts with the lock type of the currently operated operation object is obtained from the operation lock record table.
举例来说,操作锁记录表如表1所示,当前请求的操作为“重启MySQL”,经查找“重启MySQL”对应的操作对象为ccm_mysql_entity=251,该操作对象对应的锁类型为独占锁。For example, the operation lock record table is shown in Table 1. The currently requested operation is "Restart MySQL", the operation object corresponding to "Restart MySQL" is found to be ccm_mysql_entity=251, and the lock type corresponding to the operation object is an exclusive lock.
查询操作锁记录表,发现有正在执行的对象名=ccm_mysql_entity,对象id=251操作记录,该操作记录与当前请求操作的操作对象ccm_mysql_entity=251相冲突,故操作记录表中该操作对象的锁类型为独占锁,因此,“重启MySQL实体”的配置项与操作锁记录中的锁数据相冲突,而“2018/10/23 14:12释放MyCat实体ccm_mysql_entity 251 X执行中”要获取的相冲突的目标锁记录。Query the operation lock record table, and found that there is an operation record of the object name being executed=ccm_mysql_entity and object id=251. This operation record conflicts with the operation object ccm_mysql_entity=251 of the current requested operation, so the lock type of the operation object in the operation record table It is an exclusive lock. Therefore, the configuration item of "Restart MySQL entity" conflicts with the lock data in the operation lock record, and the conflict to be acquired by "2018/10/23 14:12 release MyCat entity ccm_mysql_entity 251 X in execution" Target lock record.
可预先定义阻塞提醒模板,生成阻塞提醒时,将目标锁记录中的数据填入至阻塞提醒模板中,生成阻塞提醒。A blocking reminder template can be defined in advance. When a blocking reminder is generated, the data in the target lock record is filled into the blocking reminder template to generate a blocking reminder.
应该理解的是,虽然图2-3的流程图中的各个步骤按照箭头的指示依次显示,但是这些步骤并不是必然按照箭头指示的顺序依次执行。除非本文中有明确的说明,这些步骤的执行并没有严格的顺序限制,这些步骤可以以其它的顺序执行。而且,图2-3中的至少一部分步骤可以包括多个子步骤或者多个阶段,这些子步骤或者阶段并不必然是在同一时刻执行完成,而是可以在不同的时刻执行,这些子步骤或者阶段的执行顺序也不必然是依次进行,而是可以与其它步骤或者其它步骤的子步骤或者阶段的至少一部分轮流或者交替地执行。It should be understood that, although the various steps in the flowchart of FIGS. 2-3 are displayed in sequence as indicated by the arrows, these steps are not necessarily executed in the order indicated by the arrows. Unless specifically stated in this article, the execution of these steps is not strictly limited in order, and these steps can be executed in other orders. Moreover, at least some of the steps in Figure 2-3 may include multiple sub-steps or multiple stages. These sub-steps or stages are not necessarily executed at the same time, but can be executed at different times. These sub-steps or stages The execution order of is not necessarily performed sequentially, but may be performed alternately or alternately with at least a part of other steps or sub-steps or stages of other steps.
在其中一个实施例中,如图4所示,提供了一种数据库操作控制装置,包括:操作请求接收模块402、锁数据查找模块404、冲突判断模块406、阻塞模块408和执行模块410,其中:In one of the embodiments, as shown in FIG. 4, a database operation control device is provided, including: an operation
操作请求接收模块402,用于接收数据库操作请求,请求中携带操作标识。The operation
锁数据查找模块404,用于查找与操作标识对应的锁数据,锁数据包括操作 标识对应的操作对象以及每个操作对象对应的锁类型。The lock
冲突判断模块406,用于根据预先定义的锁类型互斥关系,判断锁数据是否与操作锁记录表中的锁数据相冲突,操作锁记录表中的锁数据包括状态为正在执行的操作对应的锁数据。The
若是,则进入阻塞模块408,否则进入执行模块410;阻塞模块408,用于阻塞请求的操作;执行模块410,用于执行操作,将操作对应的锁数据添加至操作锁记录表。If yes, enter the
在其中一个实施例中,锁类型包括独占锁和共享锁;冲突判断模块404还用于若当前请求中的操作对象的锁类型为共享锁,且操作锁记录表中同一操作对象的锁类型为独占锁时,确定锁数据相冲突;或当前请求中操作对象的锁类型为独占锁,操作锁记录表中同一操作对象为独占锁或者共享锁时,确定锁数据相冲突。In one of the embodiments, the lock types include exclusive locks and shared locks; the
在其中一个实施例中,锁数据查找模块404还用于获取与操作标识对应的操作定义,操作定义包括查询语句;根据查询语句查找与操作标识对应的操作对象,操作对象包括操作本身以及与操作关联的配置项;从操作定义中获取每个操作对象对应的锁类型;及根据操作对象以及操作对象对应的锁类型,生成操作标识对应的锁数据。In one of the embodiments, the lock
在其中一个实施例中,冲突判断模块404还用于判断操作锁记录表中是否对操作对象上锁;若是,判断操作锁记录表中的上锁记录是否与操作定义中操作对象的锁类型相冲突;若任一操作对象的锁类型与上锁记录冲突,则阻塞操作;及若所有操作对象的锁类型与上锁记录均不相冲突,则执行操作。In one of the embodiments, the
在其中一个实施例中,数据库操作控制装置还包括阻塞提醒模块,用于从操作锁记录中获取相冲突的目标锁记录;及根据目标锁记录生成阻塞提醒,将阻塞提醒发送至操作请求终端。In one of the embodiments, the database operation control device further includes a blocking reminder module for obtaining conflicting target lock records from the operation lock records; and generating a blocking reminder according to the target lock record, and sending the blocking reminder to the operation request terminal.
在其中一个实施例中,数据库操作控制装置还包括操作锁记录表更新模块,用于监听正在执行的操作;及当操作执行完成后,从操作锁记录表中删除操作对应的锁数据。In one of the embodiments, the database operation control device further includes an operation lock record table update module for monitoring the operation being performed; and when the operation is completed, the lock data corresponding to the operation is deleted from the operation lock record table.
在其中一个实施例中,操作锁记录表更新模块还用于根据标签对阻塞的操 作进行标记;当标签为等待标签时,监听操作锁记录中与操作互斥的目标锁记录;及当目标锁记录从操作锁记录中删除后,执行等待标签标记的操作。In one of the embodiments, the operation lock record table update module is also used to mark the blocked operation according to the tag; when the tag is a waiting tag, monitor the target lock record in the operation lock record that is mutually exclusive with the operation; and when the target lock After the record is deleted from the operation lock record, the operation of waiting for label marking is performed.
关于数据库操作控制装置的具体限定可以参见上文中对于数据库操作控制方法的限定,在此不再赘述。上述数据库操作控制装置中的各个模块可全部或部分通过软件、硬件及其组合来实现。上述各模块可以硬件形式内嵌于或独立于计算机设备中的处理器中,也可以以软件形式存储于计算机设备中的存储器中,以便于处理器调用执行以上各个模块对应的操作。For the specific limitation of the database operation control device, please refer to the above limitation on the database operation control method, which will not be repeated here. Each module in the aforementioned database operation control device can be implemented in whole or in part by software, hardware, and a combination thereof. The above modules may be embedded in the form of hardware or independent of the processor in the computer equipment, or may be stored in the memory of the computer equipment in the form of software, so that the processor can call and execute the operations corresponding to the above modules.
在一个实施例中,提供了一种计算机设备,该计算机设备可以是服务器,其内部结构图可以如图5所示。该计算机设备包括通过系统总线连接的处理器、存储器、网络接口和数据库。其中,该计算机设备的处理器用于提供计算和控制能力。该计算机设备的存储器包括非易失性存储介质、内存储器。该非易失性存储介质存储有操作系统、计算机可读指令和数据库。该内存储器为非易失性存储介质中的操作系统和计算机可读指令的运行提供环境。该计算机设备的数据库用于存储锁数据。该计算机设备的网络接口用于与外部的终端通过网络连接通信。该计算机可读指令被处理器执行时以实现一种数据库操作控制方法。In one embodiment, a computer device is provided. The computer device may be a server, and its internal structure diagram may be as shown in FIG. 5. The computer equipment includes a processor, a memory, a network interface and a database connected through a system bus. Among them, the processor of the computer device is used to provide calculation and control capabilities. The memory of the computer device includes a non-volatile storage medium and an internal memory. The non-volatile storage medium stores an operating system, computer readable instructions, and a database. The internal memory provides an environment for the operation of the operating system and computer-readable instructions in the non-volatile storage medium. The database of the computer equipment is used to store lock data. The network interface of the computer device is used to communicate with an external terminal through a network connection. The computer readable instruction is executed by the processor to realize a database operation control method.
本领域技术人员可以理解,图5中示出的结构,仅仅是与本申请方案相关的部分结构的框图,并不构成对本申请方案所应用于其上的计算机设备的限定,具体的计算机设备可以包括比图中所示更多或更少的部件,或者组合某些部件,或者具有不同的部件布置。Those skilled in the art can understand that the structure shown in FIG. 5 is only a block diagram of a part of the structure related to the solution of the present application, and does not constitute a limitation on the computer device to which the solution of the present application is applied. The specific computer device may Including more or fewer parts than shown in the figure, or combining some parts, or having a different arrangement of parts.
一种计算机设备,包括存储器和一个或多个处理器,存储器中储存有计算机可读指令,计算机可读指令被处理器执行时,使得一个或多个处理器执行时实现上述方法实施例中的步骤。A computer device includes a memory and one or more processors. The memory stores computer readable instructions. When the computer readable instructions are executed by the processor, the one or more processors execute the method in the foregoing method embodiment. step.
一个或多个存储有计算机可读指令的非易失性计算机可读存储介质,计算机可读指令被一个或多个处理器执行时,使得一个或多个处理器执行时实现上述方法实施例中的步骤。One or more non-volatile computer-readable storage media storing computer-readable instructions. When the computer-readable instructions are executed by one or more processors, one or more processors execute A step of.
本领域普通技术人员可以理解实现上述实施例方法中的全部或部分流程,是可以通过计算机可读指令来指令相关的硬件来完成,所述的计算机可读指令可存储于一非易失性计算机可读取存储介质中,该计算机可读指令在执行时, 可包括如上述各方法的实施例的流程。其中,本申请所提供的各实施例中所使用的对存储器、存储、数据库或其它介质的任何引用,均可包括非易失性和/或易失性存储器。非易失性存储器可包括只读存储器(ROM)、可编程ROM(PROM)、电可编程ROM(EPROM)、电可擦除可编程ROM(EEPROM)或闪存。易失性存储器可包括随机存取存储器(RAM)或者外部高速缓冲存储器。作为说明而非局限,RAM以多种形式可得,诸如静态RAM(SRAM)、动态RAM(DRAM)、同步DRAM(SDRAM)、双数据率SDRAM(DDRSDRAM)、增强型SDRAM(ESDRAM)、同步链路(Synchlink)DRAM(SLDRAM)、存储器总线(Rambus)直接RAM(RDRAM)、直接存储器总线动态RAM(DRDRAM)、以及存储器总线动态RAM(RDRAM)等。A person of ordinary skill in the art can understand that all or part of the processes in the above-mentioned embodiment methods can be implemented by instructing relevant hardware through computer-readable instructions, which can be stored in a non-volatile computer. In a readable storage medium, when the computer-readable instructions are executed, they may include the processes of the above-mentioned method embodiments. Wherein, any reference to memory, storage, database, or other media used in the embodiments provided in this application may include non-volatile and/or volatile memory. Non-volatile memory may include read only memory (ROM), programmable ROM (PROM), electrically programmable ROM (EPROM), electrically erasable programmable ROM (EEPROM), or flash memory. Volatile memory may include random access memory (RAM) or external cache memory. As an illustration and not a limitation, RAM is available in many forms, such as static RAM (SRAM), dynamic RAM (DRAM), synchronous DRAM (SDRAM), double data rate SDRAM (DDRSDRAM), enhanced SDRAM (ESDRAM), synchronous chain Channel (Synchlink) DRAM (SLDRAM), memory bus (Rambus) direct RAM (RDRAM), direct memory bus dynamic RAM (DRDRAM), and memory bus dynamic RAM (RDRAM), etc.
以上实施例的各技术特征可以进行任意的组合,为使描述简洁,未对上述实施例中的各个技术特征所有可能的组合都进行描述,然而,只要这些技术特征的组合不存在矛盾,都应当认为是本说明书记载的范围。The technical features of the above embodiments can be combined arbitrarily. In order to make the description concise, all possible combinations of the technical features in the above embodiments are not described. However, as long as there is no contradiction between the combinations of these technical features, they should It is considered as the range described in this specification.
以上所述实施例仅表达了本申请的几种实施方式,其描述较为具体和详细,但并不能因此而理解为对发明专利范围的限制。应当指出的是,对于本领域的普通技术人员来说,在不脱离本申请构思的前提下,还可以做出若干变形和改进,这些都属于本申请的保护范围。因此,本申请专利的保护范围应以所附权利要求为准。The above-mentioned embodiments only express several implementation manners of the present application, and the description is relatively specific and detailed, but it should not be understood as a limitation on the scope of the invention patent. It should be pointed out that for those of ordinary skill in the art, without departing from the concept of this application, several modifications and improvements can be made, and these all fall within the protection scope of this application. Therefore, the scope of protection of the patent of this application shall be subject to the appended claims.
Claims (20)
Applications Claiming Priority (2)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN201910125726.0 | 2019-02-20 | ||
| CN201910125726.0A CN109857745A (en) | 2019-02-20 | 2019-02-20 | Database manipulation control method, device, computer equipment and storage medium |
Publications (1)
| Publication Number | Publication Date |
|---|---|
| WO2020168755A1 true WO2020168755A1 (en) | 2020-08-27 |
Family
ID=66898370
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| PCT/CN2019/118000 Ceased WO2020168755A1 (en) | 2019-02-20 | 2019-11-13 | Method and device for controlling database operation, computer apparatus and storage medium |
Country Status (2)
| Country | Link |
|---|---|
| CN (1) | CN109857745A (en) |
| WO (1) | WO2020168755A1 (en) |
Families Citing this family (10)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN109857745A (en) * | 2019-02-20 | 2019-06-07 | 平安科技(深圳)有限公司 | Database manipulation control method, device, computer equipment and storage medium |
| CN110708187A (en) * | 2019-09-11 | 2020-01-17 | 上海爱数信息技术股份有限公司 | Tape library management device and method supporting cluster |
| CN111026482B (en) * | 2019-11-29 | 2022-02-22 | 维沃移动通信有限公司 | Application program control method and electronic equipment |
| CN112416935A (en) * | 2020-11-20 | 2021-02-26 | 中国建设银行股份有限公司 | Data operation management method and device |
| CN112988777B (en) * | 2021-05-19 | 2021-08-10 | 腾讯科技(深圳)有限公司 | Object processing method, apparatus, computer equipment and storage medium |
| CN113342507B (en) * | 2021-07-07 | 2024-03-29 | 湖南四方天箭信息科技有限公司 | Distributed lock service realization method and device and computer equipment |
| CN115269624A (en) * | 2022-08-09 | 2022-11-01 | 携程旅游信息技术(上海)有限公司 | Control method and system for redis operation, electronic device and medium |
| CN115357252B (en) * | 2022-10-08 | 2022-12-27 | 成都数联云算科技有限公司 | Source code file generation method and device, electronic equipment and storage medium |
| CN115757452B (en) * | 2022-11-24 | 2025-12-23 | 上海达梦数据库有限公司 | Blocking method, device, equipment and storage medium |
| CN116186054A (en) * | 2022-12-27 | 2023-05-30 | 杭州趣链科技有限公司 | Database operation method and server |
Citations (5)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US20110282850A1 (en) * | 2010-05-11 | 2011-11-17 | Microsoft Corporation | Concurrently Accessing Data |
| CN103514212A (en) * | 2012-06-27 | 2014-01-15 | 腾讯科技(深圳)有限公司 | Data writing method and system |
| CN105224255A (en) * | 2015-10-14 | 2016-01-06 | 浪潮(北京)电子信息产业有限公司 | A kind of storage file management method and device |
| CN106202462A (en) * | 2016-07-15 | 2016-12-07 | 北京奇虎科技有限公司 | Method and device for data configuration data lock |
| CN109857745A (en) * | 2019-02-20 | 2019-06-07 | 平安科技(深圳)有限公司 | Database manipulation control method, device, computer equipment and storage medium |
Family Cites Families (1)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN101350022B (en) * | 2008-08-27 | 2010-04-14 | 中国工商银行股份有限公司 | Changing process method based on database logical lock |
-
2019
- 2019-02-20 CN CN201910125726.0A patent/CN109857745A/en active Pending
- 2019-11-13 WO PCT/CN2019/118000 patent/WO2020168755A1/en not_active Ceased
Patent Citations (5)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US20110282850A1 (en) * | 2010-05-11 | 2011-11-17 | Microsoft Corporation | Concurrently Accessing Data |
| CN103514212A (en) * | 2012-06-27 | 2014-01-15 | 腾讯科技(深圳)有限公司 | Data writing method and system |
| CN105224255A (en) * | 2015-10-14 | 2016-01-06 | 浪潮(北京)电子信息产业有限公司 | A kind of storage file management method and device |
| CN106202462A (en) * | 2016-07-15 | 2016-12-07 | 北京奇虎科技有限公司 | Method and device for data configuration data lock |
| CN109857745A (en) * | 2019-02-20 | 2019-06-07 | 平安科技(深圳)有限公司 | Database manipulation control method, device, computer equipment and storage medium |
Also Published As
| Publication number | Publication date |
|---|---|
| CN109857745A (en) | 2019-06-07 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| WO2020168755A1 (en) | Method and device for controlling database operation, computer apparatus and storage medium | |
| US12339822B2 (en) | Method and system for migrating content between enterprise content management systems | |
| US11550769B2 (en) | Data processing method, apparatus, and system | |
| CN112910945B (en) | Request link tracking method and service request processing method | |
| WO2020186786A1 (en) | File processing method and apparatus, computer device and storage medium | |
| US20130226872A1 (en) | On-demand file synchronization | |
| CN109885786B (en) | Data caching processing method and device, electronic equipment and readable storage medium | |
| WO2019061991A1 (en) | Multi-element universal model platform modeling method, electronic device, and computer readable storage medium | |
| WO2019019769A1 (en) | Service function implementation method, device, computer apparatus and storage medium | |
| WO2020253122A1 (en) | Data verification method and device, computer equipment and storage medium | |
| CN112785248B (en) | Human resource data cross-organization interaction method, device, equipment and storage medium | |
| CN112835886A (en) | Data table field adding method and device | |
| US11151088B2 (en) | Systems and methods for verifying performance of a modification request in a database system | |
| CN112463783B (en) | Index data monitoring method, device, computer equipment and storage medium | |
| WO2021012903A1 (en) | Data storage method and apparatus, computer device, and storage medium | |
| CN115456568A (en) | Process approval method, apparatus, computer device, storage medium, and program product | |
| CN109840250B (en) | Method, device, equipment and storage medium for managing access authority of intermediate field | |
| CN114519062B (en) | Basic data updating method, device, computer equipment and storage medium | |
| US12488390B2 (en) | Systems and methods for managing metrics in blockchain networks | |
| US12242451B2 (en) | Determining references to predefined types of records | |
| CN119311312B (en) | Code combining state detection method, apparatus, device, readable storage medium and program product | |
| CN111813842B (en) | Data processing method, device, system, equipment and storage medium | |
| US20240070132A1 (en) | Independently loading related data into data storage | |
| CN117151839A (en) | Mechanism tree changing method and device based on block chain and computer equipment | |
| CN116880927A (en) | Rule management method, device, computer equipment and storage medium |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| 121 | Ep: the epo has been informed by wipo that ep was designated in this application |
Ref document number: 19915719 Country of ref document: EP Kind code of ref document: A1 |
|
| NENP | Non-entry into the national phase |
Ref country code: DE |
|
| 122 | Ep: pct application non-entry in european phase |
Ref document number: 19915719 Country of ref document: EP Kind code of ref document: A1 |