WO2019165883A1 - Data processing method and apparatus - Google Patents
Data processing method and apparatus Download PDFInfo
- Publication number
- WO2019165883A1 WO2019165883A1 PCT/CN2019/074469 CN2019074469W WO2019165883A1 WO 2019165883 A1 WO2019165883 A1 WO 2019165883A1 CN 2019074469 W CN2019074469 W CN 2019074469W WO 2019165883 A1 WO2019165883 A1 WO 2019165883A1
- Authority
- WO
- WIPO (PCT)
- Prior art keywords
- data
- type
- rule
- rules
- ips
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Ceased
Links
Images
Classifications
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/40—Network security protocols
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L41/00—Arrangements for maintenance, administration or management of data switching networks, e.g. of packet switching networks
- H04L41/06—Management of faults, events, alarms or notifications
- H04L41/069—Management of faults, events, alarms or notifications using logs of notifications; Post-processing of notifications
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/14—Network architectures or network communication protocols for network security for detecting or protecting against malicious traffic
- H04L63/1408—Network architectures or network communication protocols for network security for detecting or protecting against malicious traffic by monitoring network traffic
- H04L63/1416—Event detection, e.g. attack signature detection
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/14—Network architectures or network communication protocols for network security for detecting or protecting against malicious traffic
- H04L63/1408—Network architectures or network communication protocols for network security for detecting or protecting against malicious traffic by monitoring network traffic
- H04L63/1425—Traffic logging, e.g. anomaly detection
Definitions
- the present application relates to the field of communications, and in particular, to a method and an apparatus for processing data.
- Intrusion Prevention System is a commonly used security device on the Internet. It can provide active protection services to the network, perform deep detection of network traffic, and intercept attack network traffic and intrusion activities to avoid attacks. loss.
- IPS is to embed the device directly into the network traffic, that is, to receive traffic from the external system through a network port. After checking to confirm that it does not contain abnormal activity or suspicious content, it transmits it to the internal system through another port. In this way, problematic packets, or all subsequent packets from the same data stream, can be removed from the IPS device, eliminating attacks and threats to the network and devices.
- FIG. 1 is a schematic diagram of a typical deployment manner of an IPS according to the related art.
- the network is divided into an external network and an internal network, for example, in a typical government enterprise network application scenario, the internal network.
- the internal network Refers to the internal LAN of the government or enterprise, and the external network refers to the Internet.
- a firewall is usually deployed as a demarcation point between the internal network and the external network.
- the IPS is deployed independently, it is usually deployed behind the internal network firewall, and is located on the path of internal and external network traffic. It can also be integrated into the firewall as a component.
- an alarm is sent to the alarm center to send an intrusion event log, or the data stream is blocked (such as dropping the data packet, resetting the data connection, etc.), and simultaneously sending an intrusion event log to the alarm center. .
- the rule base of IPS is the result of long-term analysis and tracking of intrusion behavior. As the network intrusion behavior continues to increase, the number of entries in the rule base continues to increase, and the number of entries in the general commercial IPS rule base is more than 10,000. Directly bring the following questions:
- the number of rule entries is large, the engine matching algorithm is required to be high, the matching/traversal time is long, the transmission delay of the data packet is increased, and the service experience is affected. At the same time, since the data packet is buffered in the memory for a long time, the maximum throughput of the device is directly limited. .
- the embodiment of the present application provides a data processing method and apparatus, so as to at least solve the problem that a large number of rules in the IPS rule base used in the related art may affect forwarding performance.
- a data processing method including: an IPS receiving data to be passed; matching the data according to a first type of rule and/or a second type of rule, wherein the first class
- the rules include rules for blocking data forwarding, and the second type of rules include rules for performing data alerts; the data is processed according to whether the results of the matching.
- a data processing apparatus including: a receiving module configured to receive data to be passed; a matching module configured to match according to a first type of rule and/or a second type of rule The data received by the receiving module, where the first type of rule includes a rule for blocking data forwarding, the second type of rule includes a rule for performing data alarm, and the processing module is configured to obtain according to the matching module. Whether the result of the match is processed by the data.
- a storage medium having stored therein a computer program, wherein the computer program is configured to execute the steps of any one of the method embodiments described above.
- an electronic device comprising a memory and a processor, wherein the memory stores a computer program, the processor being configured to run the computer program to perform any of the above The steps in the method embodiments.
- the rule base of the IPS is divided into two types according to the rule type, and at least one of the two types of rules is used to match the data received by the IPS, that is, whether to separately block the forwarding of the data, whether only
- the alarm information is sent in the above manner, which avoids the problem that the use of a large number of rules in the IPS rule base in the related art may affect the forwarding performance.
- the two types of rules can be quickly invoked. When each type of rule is used for judgment, the number of rules is avoided.
- the second rule determines the impact on forwarding performance.
- FIG. 1 is a schematic diagram of a typical deployment manner of an IPS according to the related art
- FIG. 2 is a flowchart of a method of processing data according to an embodiment of the present application.
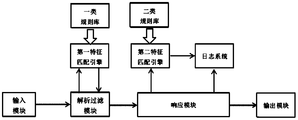
- FIG. 3 is a schematic diagram of an internal structure of an IPS according to the related art
- FIG. 4 is a schematic diagram of an internal structure of an IPS Embodiment 1 according to Embodiment 1;
- FIG. 5 is a schematic diagram of an internal structure of an IPS implementation manner 2 after a rule base separation according to a specific embodiment 2;
- FIG. 6 is a schematic diagram of a separate deployment of an IPS device after a rule base separation according to a specific embodiment 3.
- the embodiment of the present application can be applied to the scenario described in FIG. 1 , that is, the two sides of the IPS are connected to the intranet external network, and the data is forwarded in the two networks.
- FIG. 2 is a flowchart of a data processing method according to an embodiment of the present application. As shown in FIG. 2, the flow includes the following steps. step:
- Step S202 the IPS receives data to be passed
- Step S204 Matching the data according to the first type of rules and/or the second type of rules, where the first type of rules includes a rule for blocking data forwarding, and the second type of rules includes a rule for performing data alarms;
- step S206 the data is processed according to whether the result of the matching.
- the rule base of the IPS in the related art is divided into two types according to the rule type, and the two types of rules are used to respectively match the data received by the IPS, that is, whether to separately block the forwarding of the data, and/or whether The data is transmitted in the above manner.
- This avoids the problem that the large number of rules in the IPS rule base can affect the forwarding performance in the related technologies.
- the matching the data according to the first type of rules and/or the second type of rules includes: determining, according to the first type of rules, whether to block forwarding of the data; The result of the matching processes the data, including: blocking the forwarding of the data if it is determined to block forwarding of the data; and forwarding the data to the output interface of the IPS if it is determined to forward the data.
- the first type of rule matching data may be preferentially used, that is, it is first determined whether to block data forwarding, and if it is determined that the blocking data is forwarded, the data is not continuously forwarded; if the data is not blocked, Then, the data is forwarded to the output interface of the IPS to forward the data, and then the alarm rule is used for matching, thereby saving time for data to pass through the IPS.
- the method further includes: determining, according to the second type of rule, whether to alert the data, wherein, in the case of determining to alert the data , the first alarm message is sent.
- the method further includes: issuing second alarm information. That is, in the embodiment, the second alarm information may be sent at the same time as the data is forwarded, and the second alarm information is used to notify the intrusion and perform the blocking operation on the intrusion.
- the method before the matching the data according to the first type of rules and/or the second type of rules, the method further includes: obtaining the first type of rules and/or respectively from the preset location.
- a second type of rule wherein the first type of rule is set in a primary work area of the IPS; and the second type of rule is set in a secondary work area of the IPS. It should be noted that the first type of rules and the second type of rules can be stored in different locations.
- the first type of rules is more important and can be stored in the main area of the IPS work, which is convenient for quick call; the second type of rules can be In other auxiliary areas, after determining that data forwarding is not blocked, the replicated data is sent to other auxiliary areas, and the second type of rule is used for matching. At this time, the actual pressure is not formed on the IPS forwarding data.
- the first type of rule includes at least one of the following rules: a rule for discarding data; and a rule for resetting the connection. It can be understood that the first type of rule is used to detect more serious data problems, such as carrying a virus.
- FIG. 3 is a schematic diagram of an internal structure of an IPS according to the related art. As shown in FIG. 3, the internal module works and executes as follows:
- Input module configured to receive external network traffic entering the IPS and send it to the parsing filtering module.
- the parsing filtering module is configured to perform protocol parsing on the received data packet, determine whether to invoke the feature matching engine to detect according to the parsing result, send the data element to be detected to the feature matching engine, and maintain the session state of the data stream where the data packet is located. .
- Feature matching engine configured to load the intrusion behavior rule base when the system is started. When called, compare the data elements of the data with the features in the feature library, and return the comparison result, that is, whether it hits, if it hits, at the same time Returns the intrusion type, action, and other information, and outputs it to the response module.
- the response module is configured to perform a response operation according to the action information in the hit result, including release, alarm, block (such as discard, connection reset, etc.), and send the intrusion behavior information and the response result to the alarm system through the log system.
- Output module If the release operation is performed, the output module is used to send the data packet to the internal network host.
- Rule base configured to describe the intrusion behavior signature library. The typical description is as follows:
- Rule header [action, protocol type, source ip, source port, direction, destination ip, destination port], (rule option [keyword]), information),
- alert tcp any any->192.168.1.0/24 111 (content: "
- the rule base is the result of long-term analysis of intrusion behavior. As the network intrusion behavior continues to increase, the number of entries in the rule base continues to increase. Generally, the number of entries in the commercial IPS rule base is more than 10,000, which directly brings the following problems:
- the number of rule entries is large, the engine matching algorithm is required to be high, the matching/traversal time is long, the transmission delay of the data packet is increased, and the service experience is affected. At the same time, since the data packet is buffered in the memory for a long time, the maximum throughput of the device is directly limited. .
- the number of rule entries is large and the memory usage is large.
- the rules need to be tailored, which increases the false negative rate and directly affects the protection effect.
- the embodiment of the present application provides a high-performance intrusion prevention method, including the following features:
- Feature A (the rule base in the feature A can store the rules used by the matching module of the subsequent embodiment 2), and the rule base is divided into a class rule base according to the type of action in the rules of the intrusion prevention system (can be used to store the above implementation) a first type of rule in the example) and a second type of rule base (which may be used to store the second type of rule in the above embodiment), and the rule of the type includes a rule that blocks the action (including dropping, resetting, etc.).
- the second type rule base contains rules for actions as alarms;
- the IPS starts a first feature matching engine and a second feature matching engine, respectively, for loading a class rule library and a second class rule library;
- the parsing filtering module first sends the data element of the received data packet to the first feature matching engine, and the first feature matching engine performs feature matching if the hit is equivalent to using the first type of rule matching in the above embodiment. If the data is successful, the response module performs a blocking operation. If there is no hit, the parsing filtering module or the response module sends the data element to the second feature matching engine, and the response module performs the releasing operation;
- the second feature matching engine performs feature matching, and if a hit (equivalent to using the second type of rule in the above embodiment to match the data successfully), an alert operation is performed.
- the feature B of the foregoing high-performance intrusion prevention method further includes:
- Feature B1 the first feature matching engine and the second feature matching engine are located in the same operating environment, or different operating environments, and are suggested to be located in different operating environments;
- the two feature matching engines use the same matching algorithm or use different matching algorithms.
- the feature C of the foregoing high-performance intrusion prevention method further includes:
- the parsing filtering module needs to cache the data packet when sending the data element of the data packet to the first feature matching engine, and wait for the first matching engine to return the hitting result to execute the subsequent process;
- the parsing filter module directly executes the subsequent process after sending the data element of the data packet to the first feature matching engine, that is, sending the response module to perform the release operation, without waiting for the second matching engine to return the hit result;
- the response module directly performs the subsequent operation after sending the data element of the data packet to the first feature matching engine, that is, performing the release operation, without waiting for the second matching engine to return the hit result.
- the feature D of the foregoing high-performance intrusion prevention method further includes:
- the second feature matching engine ends the match and does not perform any action.
- a high performance intrusion prevention system includes a class rule base and a second class rule base, a first feature matching engine and a second feature matching engine, an input module, a parsing filter module, a response module, and an output.
- Module log system.
- the input module, the output module, and the log system are the same as those described in FIG.
- a type of rule base a rule containing actions to block operations (such as dropping, resetting, etc.) (equivalent to the first type of rules in the above embodiment);
- the second type rule base the rule containing the action as an alarm (corresponding to the second type of rule in the above embodiment);
- the parsing filter module (corresponding to some functions of the matching module in the subsequent embodiment 2): after performing protocol parsing and filtering on the received data packet, preferentially calling the first feature matching engine, and then calling the second feature matching engine according to the matching result, Or call the response module;
- the first feature matching engine (corresponding to some functions of the matching module in the subsequent embodiment 2) is configured to load a class rule base, perform matching detection on the data elements, and return a matching result;
- the second feature matching engine (which is equivalent to the partial function of the matching module in the subsequent embodiment 2) is configured to load the second type rule base and perform matching detection on the data elements. If the hit occurs, the alarm operation is performed, otherwise no operation is performed.
- a response module (corresponding to a part of the functions of the processing module in the subsequent embodiment 2): configured to perform an operation according to a matching result of the first feature engine, and if a hit, perform a blocking operation (such as discarding, resetting, etc.), otherwise executing Release the operation, optionally calling the second feature matching engine.
- a blocking operation such as discarding, resetting, etc.
- FIG. 4 is a schematic diagram of an internal structure of an IPS implementation manner according to a specific embodiment 1.
- the small reference numeral 123456789 is used to indicate the interaction order of the following modules, and may correspond to the following module descriptions.
- the internal structure of the IPS implementation mode after the rule base of the embodiment is separated, and the functions of each module are as follows:
- the input module, the output module, the log system, and the like are the same as the related art described in FIG.
- the rule base is divided into a class rule base and a second type rule base.
- One type of rule base includes rules for blocking (such as discarding, resetting, etc.), and the second class rule library includes rules for actions as alarms, and one type of rule.
- the rule base has a higher priority than the second type rule base. That is, the input data packet is preferentially matched with the rules in a type of rule base. If it is hit, the defense function is executed, including performing a blocking operation, including dropping the data packet, resetting the data flow connection, and the like, and then hitting no hit. The data packet is matched with the rules in the second-class rule base. If it is hit, an alarm operation is performed to send an alarm message to the log system.
- the first feature matching engine and the second feature matching engine are started, and a class rule library and a second class rule library are respectively loaded.
- the parsing filter module based on the original packet parsing and filtering function, preferentially invokes the first feature matching engine to perform feature matching according to the priority of the rule base, and caches the data packet, waiting for the matching result; when the first feature matching engine returns a match As a result, if the hit, the parsing filter module calls the response module, and sends the data packet and the matching result to the response module. If there is no hit, the second feature matching engine is called to send the data element to the second feature matching engine, and the data packet and The matching result is sent to the response module, and in the second feature matching engine matching process, the data packet is no longer needed to be cached.
- the second feature matching engine performs feature matching. If the hit occurs, the alarm operation is performed to send an alarm message to the log system, otherwise no operation is performed.
- the response module performs a defense operation if a rule in a type of rule base is hit, such as performing a blocking operation, and simultaneously sending an alarm message to the log system, otherwise performing a release operation. If a rule in a type of rule base is hit, the first feature matching engine may also send an alert message to the log system.
- Specific embodiment 1 may include the following workflow:
- Step 1 When the system starts or the rule base is updated, the first feature matching engine loads a class rule library into the memory, and the second feature matching engine loads the second class rule library into the memory;
- Step 2 the input module receives the data packet of the input port and sends the data packet to the parsing filtering module.
- Step 3 After parsing and filtering the received data packet, the parsing filtering module calls the first feature matching engine to perform matching, and returns a matching result;
- Step 4 If the hit, the step 7 parsing filtering module sends the matching result of the data packet and the first feature matching engine to the response module;
- Step 5 If there is no hit, the parsing filtering module calls the second feature matching engine to copy the data element and sends the data element to the second feature matching engine, and performs step 7 to send the data packet to the response module;
- Step 6 The second feature matching engine performs feature matching. If the hit occurs, the alarm operation is performed to send an alarm message to the log system, otherwise no operation is performed.
- Step 7 the parsing filter module data packet is sent to the response module, and the matching result of the first feature matching engine is included;
- Step 8 The response module performs a blocking operation according to the matching result, if a rule in a type of rule base is hit, specifically includes dropping or resetting the connection, and sending an alarm message to the log system, otherwise performing step 9 to send the data packet to Output module.
- the first feature matching engine may also send an alert message to the log system.
- step 9 the response module sends the data packet that does not perform the blocking operation to the output port and transmits the data packet to the next hop device.
- the rule base is separated, so that different types of feature matching engines can be deployed independently, for example, the first feature matching engine is deployed in a main work area (such as a core program working on a main central processing unit (CPU) core or a host), and the second feature Matching the engine to deploy the secondary workspace (such as working with other CPU cores or non-core programs of the host) will greatly reduce the memory footprint of the main workspace (about 90% reduction) and reduce the memory requirements for the main workspace.
- a main work area such as a core program working on a main central processing unit (CPU) core or a host
- the second feature Matching the engine to deploy the secondary workspace such as working with other CPU cores or non-core programs of the host
- FIG. 5 is a schematic diagram of the internal structure of the second embodiment of the IPS implementation according to the second embodiment of the rule base. As shown in FIG. 5, it is basically the same as the specific embodiment 1. Only the difference from the specific embodiment 1 is described herein.
- Input module output module
- log system same as the prior art.
- a class rule base, a second class rule base, a first feature matching engine, and a second feature matching engine are the same as in the specific embodiment 1.
- Parsing the filtering module on the basis of the original packet parsing and filtering function, calling the first feature matching engine to perform feature matching, and buffering the data packet, waiting for the matching result; when the first feature matching engine returns the matching result, the data packet and the data element are And the matching result is sent to the response module.
- the response module performs a blocking operation, such as discarding or resetting the connection, and sends an alarm message to the log system, otherwise the duplicate data element is sent to the second feature matching engine.
- a blocking operation such as discarding or resetting the connection
- sends an alarm message to the log system otherwise the duplicate data element is sent to the second feature matching engine.
- the release operation is performed, and the data packet is sent to the output module.
- the difference between the specific embodiment 1 and the specific embodiment 2 is that, in the specific embodiment 1, the second feature matching engine is invoked by the parsing filtering module. In the specific embodiment 2, the second feature matching engine is invoked by the response module.
- the rule base is separated, so that different types of feature matching engines can be deployed independently, for example, the first feature matching engine is deployed in the main work area (such as a core program working on the main CPU core or the host), and the second feature matching engine is deployed in the auxiliary work. Areas (such as working with other CPU cores or non-core programs of the host) will greatly reduce the memory footprint of the group work area (about 90% reduction) and reduce the memory requirements for the main work area.
- FIG. 6 is a schematic diagram of the separation and deployment of the IPS device after the rule base is separated according to the third embodiment. As shown in FIG. 6 , after the rule base is separated and the feature matching engine is separated, the defense function and the alarm detection function in the IPS are decoupled. The basic deployment of equipment lays the foundation.
- the white background frame in Figure 6 represents the main function module of the IPS defense function, which is composed of an input module, a detection filtering module, a first feature matching engine, a class rule library, a response module, an output module, and a log system, and is located in the same defense device. .
- the gray bottom frame in FIG. 6 represents the main function mode of the IPS alarm detection, and is composed of an input module, a detection filtering module, a second feature matching engine, a second type rule base, and a log system, and is located in the same alarm detecting device.
- the packet is preferentially routed to the IPS defense device.
- the IPS defense device matches the rules in a type of rule base. If it hits, it performs blocking (such as dropping, resetting, etc.) operations and alarm operations. If there is no hit, the packet is forwarded.
- the data packet is sent to the IPS alarm detection device, and the data packet sent to the IPS alarm detection device can further carry the data element or data element and the matching result parsed by the IPS defense device.
- the IPS alarm detection device After receiving the IPS defense device's data packet, the IPS alarm detection device matches the rules in the second-class rule base. If it hits, the alarm is triggered. Otherwise, no operation is performed. If the data element is carried in the data packet, the data element can be directly used without further parsing, thereby reducing the parsing workload.
- the matching workload on the data transmission path is reduced, the delay is reduced, the user experience and device throughput are improved, and the device is decoupled and deployed flexibly.
- the rule base is divided into a class library and a second class library, corresponding to different feature libraries, and different calls are adopted.
- the feature matching engine method overcomes the problem of the original solution and achieves the effect of improving the IPS processing performance without affecting the IPS function, and realizes an efficient intrusion prevention system with good user experience and high device performance. High reliability and flexible deployment.
- the method according to the above embodiment can be implemented by means of software plus a necessary general hardware platform, and of course, by hardware, but in many cases, the former is A better implementation.
- the technical solution of the present application which is essential or contributes to the prior art, may be embodied in the form of a software product stored in a storage medium (such as ROM/RAM, disk,
- the optical disc includes a number of instructions for causing a terminal device (which may be a mobile phone, a computer, a server, or a network device, etc.) to perform the methods described in various embodiments of the present application.
- a data processing device is also provided, which is used to implement the above-mentioned embodiments and preferred embodiments, and has not been described again.
- the term "module” may implement a combination of software and/or hardware of a predetermined function.
- the apparatus described in the following embodiments is preferably implemented in software, hardware, or a combination of software and hardware, is also possible and contemplated.
- a data processing apparatus which can be applied to an IPS, including:
- a receiving module configured to receive data to be passed
- the matching module is configured to match the data received by the receiving module according to the first type of rule and/or the second type of rule, where the first type of rule includes a rule for blocking data forwarding, and the second type of rule Including rules for performing data alerts;
- a processing module configured to process the data according to a result of whether the matching module obtains a match.
- the matching module is further configured to determine, according to the first type of rule, whether to block forwarding of the data; and the processing module is configured to determine a resistance in the matching module. In the case of forwarding the data, the forwarding of the data is blocked; in the case of determining to forward the data, the data is forwarded to the output interface of the IPS.
- the processing module is further configured to: after the matching module determines to forward the data, determine whether to alert the data according to the second type of rule, where In the case of determining to alert the data, the first alarm information is sent.
- the processing module is further configured to issue the second alarm information if the matching module determines to block forwarding of the data.
- the receiving module is further configured to: before the matching module matches the data according to the first type rule and/or the second type rule, respectively acquiring the a first type of rule and/or a second type of rule, wherein the first type of rule is set in a primary work area of the IPS; and the second type of rule is set in a secondary work area of the IPS.
- the first type of rule includes at least one of the following rules: a rule for discarding data; and a rule for resetting a connection.
- each of the above modules may be implemented by software or hardware.
- the foregoing may be implemented by, but not limited to, the foregoing modules are all located in the same processor; or, the above modules are in any combination.
- the forms are located in different processors.
- a storage medium having stored therein a computer program, the computer program being arranged to perform the method of any of the above embodiments when executed.
- an electronic device comprising a memory and a processor, wherein the memory stores a computer program, the processor being arranged to execute the computer program to perform the above embodiment One of the methods described.
- the memory can be either volatile memory or non-volatile memory, and can include both volatile and nonvolatile memory.
- the non-volatile memory may be a Read Only Memory (ROM), a Programmable Read-Only Memory (PROM), or an Erasable Programmable Read (EPROM). Only Memory), Electrically Erasable Programmable Read-Only Memory (EEPROM), Ferromagnetic Random Access Memory (FRAM), Flash Memory, Magnetic Surface Memory , CD-ROM, or Compact Disc Read-Only Memory (CD-ROM); the magnetic surface memory can be a disk storage or a tape storage.
- the volatile memory can be a random access memory (RAM) that acts as an external cache.
- RAM Random Access Memory
- SRAM Static Random Access Memory
- SSRAM Synchronous Static Random Access Memory
- SSRAM Dynamic Random Access
- DRAM Dynamic Random Access Memory
- SDRAM Synchronous Dynamic Random Access Memory
- DDRSDRAM Double Data Rate Synchronous Dynamic Random Access Memory
- ESDRAM enhancement Enhanced Synchronous Dynamic Random Access Memory
- SLDRAM Synchronous Dynamic Random Access Memory
- DRRAM Direct Memory Bus Random Access Memory
- the method disclosed in the foregoing embodiments of the present invention may be applied to a processor or implemented by a processor.
- the processor may be an integrated circuit chip with signal processing capabilities.
- each step of the above method may be completed by an integrated logic circuit of hardware in the processor or an instruction in the form of software.
- the above processor may be a general purpose processor, a digital signal processor (DSP), or other programmable logic device, discrete gate or transistor logic device, discrete hardware component, or the like.
- DSP digital signal processor
- the processor may implement or perform the methods, steps, and logic blocks disclosed in the embodiments of the present invention.
- a general purpose processor can be a microprocessor or any conventional processor or the like.
- the steps of the method disclosed in the embodiment of the present invention may be directly implemented as a hardware decoding processor, or may be performed by a combination of hardware and software modules in the decoding processor.
- the software module can be located in a storage medium, the storage medium being located in the memory, the processor reading the information in the memory, and completing the steps of the foregoing methods in combination with the hardware thereof.
- modules or steps of the present application can be implemented by a general computing device, which can be concentrated on a single computing device or distributed in a network composed of multiple computing devices. Alternatively, they may be implemented by program code executable by the computing device such that they may be stored in the storage device by the computing device and, in some cases, may be different from the order herein.
- the steps shown or described are performed, or they are separately fabricated into individual integrated circuit modules, or a plurality of modules or steps thereof are fabricated as a single integrated circuit module.
- the application is not limited to any particular combination of hardware and software.
Landscapes
- Engineering & Computer Science (AREA)
- Computer Security & Cryptography (AREA)
- Computer Networks & Wireless Communication (AREA)
- Signal Processing (AREA)
- Computer Hardware Design (AREA)
- Computing Systems (AREA)
- General Engineering & Computer Science (AREA)
- Data Exchanges In Wide-Area Networks (AREA)
Abstract
Description
相关申请的交叉引用Cross-reference to related applications
本申请基于申请号为201810172675.2、申请日为2018年3月1日的中国专利申请提出,并要求该中国专利申请的优先权,该中国专利申请的全部内容在此以引入方式并入本申请。The present application is filed on the basis of the Chinese Patent Application No. 20110117 s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s
本申请涉及通信领域,具体涉及一种数据的处理方法及装置。The present application relates to the field of communications, and in particular, to a method and an apparatus for processing data.
入侵防护系统(IPS,Intrusion Prevention System)是互联网常用的安全设备,能够提供对网络提供主动防护服务,对网络流量进行深度检测,对其中的攻击性网络流量和入侵活动拦截,从而避免攻击造成的损失。Intrusion Prevention System (IPS) is a commonly used security device on the Internet. It can provide active protection services to the network, perform deep detection of network traffic, and intercept attack network traffic and intrusion activities to avoid attacks. loss.
IPS是通过将设备直接嵌入到网络流量中,即通过一个网络端口接收来自外部系统的流量,经过检查确认其中不包含异常活动或可疑内容后,再通过另外一个端口将它传送到内部系统中。这样,有问题的数据包,或者所有来自同一数据流的后续数据包,都能在IPS设备中被清除掉,从而消除对网络和设备的攻击和威胁。IPS is to embed the device directly into the network traffic, that is, to receive traffic from the external system through a network port. After checking to confirm that it does not contain abnormal activity or suspicious content, it transmits it to the internal system through another port. In this way, problematic packets, or all subsequent packets from the same data stream, can be removed from the IPS device, eliminating attacks and threats to the network and devices.
IPS可以独立部署在网络流量路径中,也可以集成在防火墙等网络设备中,嵌入到网络流量路径中。图1是根据相关技术中的IPS的典型部署方式示意图,如图1所示,根据IPS保护的范围,将网络分为外部网络和内部网络,比如在典型的政企网应用场景中,内部网络指政府或企业的内部局域网,外部网络指互联网。在内部网络和外部网络之间,通常会部署防火墙,作为内部网络和外部网络的分界点。IPS独立部署时,一般部署在内 部网络防火墙之后,位于内部、外部之间网络流量的必经之路上,也可以作为组件集成在防火墙内。The IPS can be deployed in the network traffic path independently or integrated into a network device such as a firewall and embedded in the network traffic path. FIG. 1 is a schematic diagram of a typical deployment manner of an IPS according to the related art. As shown in FIG. 1 , according to the scope of IPS protection, the network is divided into an external network and an internal network, for example, in a typical government enterprise network application scenario, the internal network. Refers to the internal LAN of the government or enterprise, and the external network refers to the Internet. Between the internal network and the external network, a firewall is usually deployed as a demarcation point between the internal network and the external network. When the IPS is deployed independently, it is usually deployed behind the internal network firewall, and is located on the path of internal and external network traffic. It can also be integrated into the firewall as a component.
当发现恶意网络流量,根据入侵类型和策略,采用报警向告警中心发送入侵事件日志,或者阻断数据流(如丢弃数据包、复位数据连接等处理方式),并同时向告警中心发送入侵事件日志。When malicious network traffic is found, according to the type and policy of the intrusion, an alarm is sent to the alarm center to send an intrusion event log, or the data stream is blocked (such as dropping the data packet, resetting the data connection, etc.), and simultaneously sending an intrusion event log to the alarm center. .
在相关技术中,IPS的规则库是长期对入侵行为分析跟踪的结果,随着网络入侵行为的不断增加,规则库的条目数量不断增加,一般商用IPS规则库的条目数量都万条以上,这样直接带来以下问题:In the related art, the rule base of IPS is the result of long-term analysis and tracking of intrusion behavior. As the network intrusion behavior continues to increase, the number of entries in the rule base continues to increase, and the number of entries in the general commercial IPS rule base is more than 10,000. Directly bring the following questions:
规则条目数量大,对引擎匹配算法要求高,匹配/遍历时间长,增加数据包的传输延时,影响业务体验,同时由于需要数据包在内存中缓存时间长,直接限制了设备的最大吞吐量。The number of rule entries is large, the engine matching algorithm is required to be high, the matching/traversal time is long, the transmission delay of the data packet is increased, and the service experience is affected. At the same time, since the data packet is buffered in the memory for a long time, the maximum throughput of the device is directly limited. .
针对相关技术中使用IPS规则库中的大量规则判断会影响转发性能的问题,目前还没有有效的解决方案。In view of the problem that the use of a large number of rules in the IPS rule base in the related art may affect the forwarding performance, there is currently no effective solution.
发明内容Summary of the invention
本申请实施例提供了一种数据的处理方法及装置,以至少解决相关技术中使用IPS规则库中的大量规则判断会影响转发性能的问题。The embodiment of the present application provides a data processing method and apparatus, so as to at least solve the problem that a large number of rules in the IPS rule base used in the related art may affect forwarding performance.
根据本申请的一个实施例,提供了一种数据的处理方法,包括:IPS接收待通过的数据;依据第一类规则和/或第二类规则匹配所述数据,其中,所述第一类规则包括阻断数据转发的规则,所述第二类规则包括执行数据告警的规则;依据是否匹配的结果处理所述数据。According to an embodiment of the present application, a data processing method is provided, including: an IPS receiving data to be passed; matching the data according to a first type of rule and/or a second type of rule, wherein the first class The rules include rules for blocking data forwarding, and the second type of rules include rules for performing data alerts; the data is processed according to whether the results of the matching.
根据本申请的另一个实施例,还提供了一种数据的处理装置,包括:接收模块,配置为接收待通过的数据;匹配模块,配置为依据第一类规则和/或第二类规则匹配所述接收模块接收的所述数据,其中,所述第一类规则包括阻断数据转发的规则,所述第二类规则包括执行数据告警的规则;处理模块,配置为依据所述匹配模块获得的是否匹配的结果处理所述数据。According to another embodiment of the present application, there is also provided a data processing apparatus, including: a receiving module configured to receive data to be passed; a matching module configured to match according to a first type of rule and/or a second type of rule The data received by the receiving module, where the first type of rule includes a rule for blocking data forwarding, the second type of rule includes a rule for performing data alarm, and the processing module is configured to obtain according to the matching module. Whether the result of the match is processed by the data.
根据本申请的又一个实施例,还提供了一种存储介质,所述存储介质中存储有计算机程序,其中,所述计算机程序被设置为运行时执行上述任一项方法实施例中的步骤。According to still another embodiment of the present application, there is also provided a storage medium having stored therein a computer program, wherein the computer program is configured to execute the steps of any one of the method embodiments described above.
根据本申请的又一个实施例,还提供了一种电子装置,包括存储器和处理器,所述存储器中存储有计算机程序,所述处理器被设置为运行所述计算机程序以执行上述任一项方法实施例中的步骤。According to still another embodiment of the present application, there is also provided an electronic device comprising a memory and a processor, wherein the memory stores a computer program, the processor being configured to run the computer program to perform any of the above The steps in the method embodiments.
通过本申请实施例,将IPS的规则库依据规则类型至少分为两类,使用两类规则中的至少一类规则匹配IPS接收到的数据,即分开判断是否阻断该数据的转发,是否只发出告警信息,采用上述方式,避免了相关技术中使用IPS规则库中的大量规则判断会影响转发性能的问题,可以快速调用两类规则,单独使用每类规则进行判断时,避免规则数量较大的第二规则判断对转发性能的影响。According to the embodiment of the present application, the rule base of the IPS is divided into two types according to the rule type, and at least one of the two types of rules is used to match the data received by the IPS, that is, whether to separately block the forwarding of the data, whether only The alarm information is sent in the above manner, which avoids the problem that the use of a large number of rules in the IPS rule base in the related art may affect the forwarding performance. The two types of rules can be quickly invoked. When each type of rule is used for judgment, the number of rules is avoided. The second rule determines the impact on forwarding performance.
此处所说明的附图用来提供对本申请的进一步理解,构成本申请的一部分,本申请的示意性实施例及其说明用于解释本申请,并不构成对本申请的不当限定。在附图中:The drawings described herein are intended to provide a further understanding of the present application, and are intended to be a part of this application. In the drawing:
图1是根据相关技术中的IPS的典型部署方式示意图;1 is a schematic diagram of a typical deployment manner of an IPS according to the related art;
图2是根据本申请实施例的数据的处理方法的流程图;2 is a flowchart of a method of processing data according to an embodiment of the present application;
图3是根据相关技术中IPS内部结构示意图;3 is a schematic diagram of an internal structure of an IPS according to the related art;
图4是根据具体实施例1的IPS实施方式一的内部结构示意图;4 is a schematic diagram of an internal structure of an IPS Embodiment 1 according to Embodiment 1;
图5是根据具体实施例2的规则库分离后IPS实施方式二内部结构示意图;5 is a schematic diagram of an internal structure of an IPS implementation manner 2 after a rule base separation according to a specific embodiment 2;
图6是根据具体实施例3的规则库分离后IPS设备分离部署的示意图。FIG. 6 is a schematic diagram of a separate deployment of an IPS device after a rule base separation according to a specific embodiment 3.
下文中将参考附图并结合实施例来详细说明本申请。需要说明的是,在不冲突的情况下,本申请中的实施例及实施例中的特征可以相互组合。The present application will be described in detail below with reference to the drawings in conjunction with the embodiments. It should be noted that the embodiments in the present application and the features in the embodiments may be combined with each other without conflict.
需要说明的是,本申请的说明书和权利要求书及上述附图中的术语“第一”、“第二”等是用于区别类似的对象,而不必用于描述特定的顺序或先后次序。It should be noted that the terms "first", "second" and the like in the specification and claims of the present application and the above-mentioned drawings are used to distinguish similar objects, and are not necessarily used to describe a specific order or order.
本申请实施例可以应用于图1中所述的场景,即IPS两侧连接内网外网,在两个网络中转发数据。The embodiment of the present application can be applied to the scenario described in FIG. 1 , that is, the two sides of the IPS are connected to the intranet external network, and the data is forwarded in the two networks.
在本实施例中提供了一种运行于如1所示网络架构的数据的处理方法,图2是根据本申请实施例的数据的处理方法的流程图,如图2所示,该流程包括如下步骤:In this embodiment, a processing method for data running in a network architecture as shown in FIG. 1 is provided. FIG. 2 is a flowchart of a data processing method according to an embodiment of the present application. As shown in FIG. 2, the flow includes the following steps. step:
步骤S202,IPS接收待通过的数据;Step S202, the IPS receives data to be passed;
步骤S204,依据第一类规则和/或第二类规则匹配该数据,其中,该第一类规则包括阻断数据转发的规则,该第二类规则包括执行数据告警的规则;Step S204: Matching the data according to the first type of rules and/or the second type of rules, where the first type of rules includes a rule for blocking data forwarding, and the second type of rules includes a rule for performing data alarms;
步骤S206,依据是否匹配的结果处理该数据。In step S206, the data is processed according to whether the result of the matching.
通过上述步骤,将相关技术中的IPS的规则库依据规则类型至少分为两类,使用两类规则分别匹配IPS接收到的数据,即分开判断是否阻断该数据的转发,和/或,是否执行数据告警,采用上述方式,避免了相关技术中使用IPS规则库中的大量规则判断会影响转发性能的问题,可以快速调用两类规则,单独使用每类规则进行判断时,避免规则数量较大的第二规则判断对转发性能的影响。Through the above steps, the rule base of the IPS in the related art is divided into two types according to the rule type, and the two types of rules are used to respectively match the data received by the IPS, that is, whether to separately block the forwarding of the data, and/or whether The data is transmitted in the above manner. This avoids the problem that the large number of rules in the IPS rule base can affect the forwarding performance in the related technologies. You can quickly invoke two types of rules. When each type of rule is used for judgment, the number of rules is large. The second rule determines the impact on forwarding performance.
在本申请的一种可选实施例中,所述依据第一类规则和/或第二类规则匹配该数据,包括:依据该第一类规则确定是否阻断转发该数据;所述依据是否匹配的结果处理所述数据,包括:在确定阻断转发该数据的情况下, 阻断该数据的转发;在确定转发该数据的情况下,转发该数据至该IPS的输出接口。需要说明的是,本实施例可以优先使用第一类规则匹配数据,即先判断是否阻断数据的转发,如果确定阻断数据的转发,则不继续转发数据;如果不阻断数据的转发,则转发所述数据至所述IPS的输出接口以转发该数据,再使用告警规则进行匹配,从而节省了数据通过IPS的时间。In an optional embodiment of the present application, the matching the data according to the first type of rules and/or the second type of rules includes: determining, according to the first type of rules, whether to block forwarding of the data; The result of the matching processes the data, including: blocking the forwarding of the data if it is determined to block forwarding of the data; and forwarding the data to the output interface of the IPS if it is determined to forward the data. It should be noted that, in this embodiment, the first type of rule matching data may be preferentially used, that is, it is first determined whether to block data forwarding, and if it is determined that the blocking data is forwarded, the data is not continuously forwarded; if the data is not blocked, Then, the data is forwarded to the output interface of the IPS to forward the data, and then the alarm rule is used for matching, thereby saving time for data to pass through the IPS.
在本申请的一种可选实施例中,在确定转发该数据之后,该方法还包括:依据该第二类规则确定是否对该数据进行告警,其中,在确定对该数据进行告警的情况下,发出第一告警信息。In an optional embodiment of the present application, after determining to forward the data, the method further includes: determining, according to the second type of rule, whether to alert the data, wherein, in the case of determining to alert the data , the first alarm message is sent.
在本申请的一种可选实施例中,在确定阻断转发该数据的情况下,该方法还包括:发出第二告警信息。即本实施例在阻断数据的转发的同时,也可以发出第二告警信息,所述第二告警信息用于通知有入侵且进行对入侵进行阻断操作。In an optional embodiment of the present application, in the case of determining to block forwarding of the data, the method further includes: issuing second alarm information. That is, in the embodiment, the second alarm information may be sent at the same time as the data is forwarded, and the second alarm information is used to notify the intrusion and perform the blocking operation on the intrusion.
在本申请的一种可选实施例中,所述依据第一类规则和/或第二类规则匹配该数据之前,该方法还包括:分别从预设位置获取该第一类规则和/或第二类规则,其中,该第一类规则设置在该IPS的主工作区;该第二类规则设置在该IPS的辅工作区。需要说明的是,此处意在说明第一类规则和第二类规则可以存放在不同位置,第一类规则较为重要,可以存放在IPS工作的主要区域,便于快速调用;第二类规则可以放于其他辅助区域,可以在确定不阻断数据转发之后,复制数据发送至其他辅助区域,使用第二类规则进行匹配,此时已经不对IPS转发数据形成实际的压力。In an optional embodiment of the present application, before the matching the data according to the first type of rules and/or the second type of rules, the method further includes: obtaining the first type of rules and/or respectively from the preset location. A second type of rule, wherein the first type of rule is set in a primary work area of the IPS; and the second type of rule is set in a secondary work area of the IPS. It should be noted that the first type of rules and the second type of rules can be stored in different locations. The first type of rules is more important and can be stored in the main area of the IPS work, which is convenient for quick call; the second type of rules can be In other auxiliary areas, after determining that data forwarding is not blocked, the replicated data is sent to other auxiliary areas, and the second type of rule is used for matching. At this time, the actual pressure is not formed on the IPS forwarding data.
在本申请的一种可选实施例中,该第一类规则包括以下规则至少之一:丢弃数据的规则;复位连接的规则。可以理解,第一类规则是用于检测较为严重的数据问题的,例如携带病毒等情况。In an optional embodiment of the present application, the first type of rule includes at least one of the following rules: a rule for discarding data; and a rule for resetting the connection. It can be understood that the first type of rule is used to detect more serious data problems, such as carrying a virus.
下面结合具体实施例对本申请进行说明The present application will be described below in conjunction with specific embodiments.
图3是根据相关技术中IPS内部结构示意图,如图3所示,内部模块 工作和执行过程如下:FIG. 3 is a schematic diagram of an internal structure of an IPS according to the related art. As shown in FIG. 3, the internal module works and executes as follows:
输入模块:配置为接收外部进入IPS的网络流量,发送给解析过滤模块。Input module: configured to receive external network traffic entering the IPS and send it to the parsing filtering module.
解析过滤模块:配置为对接收的数据包进行协议解析,根据解析的结果决定是否调用特征匹配引擎进行检测,将需要检测的数据要素发送到特征匹配引擎,同时维护数据包所在数据流的会话状态。The parsing filtering module is configured to perform protocol parsing on the received data packet, determine whether to invoke the feature matching engine to detect according to the parsing result, send the data element to be detected to the feature matching engine, and maintain the session state of the data stream where the data packet is located. .
特征匹配引擎:配置为在系统启动时,加载入侵行为规则库,当被调用时,将数据的数据要素与特征库中的特征进行对比,并返回对比结果,即是否命中,如果命中,则同时返回入侵类型、动作等信息,输出给响应模块。Feature matching engine: configured to load the intrusion behavior rule base when the system is started. When called, compare the data elements of the data with the features in the feature library, and return the comparison result, that is, whether it hits, if it hits, at the same time Returns the intrusion type, action, and other information, and outputs it to the response module.
响应模块:配置为根据命中结果中的动作信息执行响应操作,包括放行、告警、阻断(如丢弃、连接复位等),并通过日志系统将入侵行为信息和响应结果发送给告警系统。The response module is configured to perform a response operation according to the action information in the hit result, including release, alarm, block (such as discard, connection reset, etc.), and send the intrusion behavior information and the response result to the alarm system through the log system.
输出模块:如果执行放行操作,该输出模块用于则将数据包发往内部网络主机。Output module: If the release operation is performed, the output module is used to send the data packet to the internal network host.
规则库:配置为描述入侵行为特征库,典型描述方式如下:Rule base: configured to describe the intrusion behavior signature library. The typical description is as follows:
规则头部[动作,协议类型,源ip,源端口,方向,目的ip,目的端口],(规则选项[关键字]),信息),Rule header [action, protocol type, source ip, source port, direction, destination ip, destination port], (rule option [keyword]), information),
举例如下:alert tcp any any->192.168.1.0/24 111(content:"|00 01 86 a5|";msg:"mountd access";)。For example: alert tcp any any->192.168.1.0/24 111 (content: "|00 01 86 a5|"; msg: "mountd access";).
规则库是长期对入侵行为分析跟踪的结果,随着网络入侵行为的不断增加,规则库的条目数量不断增加,一般商用IPS规则库的条目数量都万条以上,这样直接带来以下问题:The rule base is the result of long-term analysis of intrusion behavior. As the network intrusion behavior continues to increase, the number of entries in the rule base continues to increase. Generally, the number of entries in the commercial IPS rule base is more than 10,000, which directly brings the following problems:
规则条目数量大,对引擎匹配算法要求高,匹配/遍历时间长,增加数据包的传输延时,影响业务体验,同时由于需要数据包在内存中缓存时间 长,直接限制了设备的最大吞吐量。The number of rule entries is large, the engine matching algorithm is required to be high, the matching/traversal time is long, the transmission delay of the data packet is increased, and the service experience is affected. At the same time, since the data packet is buffered in the memory for a long time, the maximum throughput of the device is directly limited. .
另外规则条目数量大,占用内存多,在IPS设备内存受限的场景下,需要对规则进行裁剪,会增加漏报率,直接影响防护效果。In addition, the number of rule entries is large and the memory usage is large. In the scenario where the IPS device has limited memory, the rules need to be tailored, which increases the false negative rate and directly affects the protection effect.
为了解决上述问题,进一步分析IPS规则库的特点,发现有90%以上规则的动作是报警类型,即当命中这种类型的特征后,IPS将放行数据,只做告警,主要原因是IPS规则匹配存在一定的误报,如果采取阻断操作时,会影响正常业务,这时采取报警操作,将入侵信息报告给后台,以便后台发现更有价值的线索。In order to solve the above problems, further analysis of the characteristics of the IPS rule base, found that more than 90% of the rules of the action is the alarm type, that is, when hitting this type of feature, the IPS will release the data, only the alarm, the main reason is the IPS rule matching There is a certain false alarm. If the blocking operation is taken, it will affect the normal business. At this time, an alarm operation is taken to report the intrusion information to the background, so that more valuable clues can be found in the background.
本申请实施例提供了一种高性能入侵防御的方法,包括以下特征:The embodiment of the present application provides a high-performance intrusion prevention method, including the following features:
特征A(该特征A中的规则库可以存储后续实施例2的匹配模块使用的规则),根据入侵防御的规则中动作的类型,将规则库划分为一类规则库(可以用于存储上述实施例中的第一类规则)和二类规则库(可以用于存储上述实施例中的第二类规则),一类规则库中包含动作为阻断(包括丢弃、复位连接等)的规则,二类规则库中包含动作为告警的规则;Feature A (the rule base in the feature A can store the rules used by the matching module of the subsequent embodiment 2), and the rule base is divided into a class rule base according to the type of action in the rules of the intrusion prevention system (can be used to store the above implementation) a first type of rule in the example) and a second type of rule base (which may be used to store the second type of rule in the above embodiment), and the rule of the type includes a rule that blocks the action (including dropping, resetting, etc.). The second type rule base contains rules for actions as alarms;
特征B,对应不同的规则库,IPS启动第一特征匹配引擎和第二特征匹配引擎,分别用于加载一类规则库和二类规则库;Feature B, corresponding to different rule bases, the IPS starts a first feature matching engine and a second feature matching engine, respectively, for loading a class rule library and a second class rule library;
特征C,解析过滤模块首先将接收到的数据包的数据元素发往第一特征匹配引擎,第一特征匹配引擎执行特征匹配,如果命中(相当于上述实施例中的使用第一类规则匹配所述数据成功),响应模块执行阻断操作,如果没有命中,解析过滤模块或响应模块将数据元素发送给第二特征匹配引擎,响应模块执行放行操作;Feature C, the parsing filtering module first sends the data element of the received data packet to the first feature matching engine, and the first feature matching engine performs feature matching if the hit is equivalent to using the first type of rule matching in the above embodiment. If the data is successful, the response module performs a blocking operation. If there is no hit, the parsing filtering module or the response module sends the data element to the second feature matching engine, and the response module performs the releasing operation;
特征D,第二特征匹配引擎执行特征匹配,如果命中(相当于上述实施例中的使用第二类规则匹配所述数据成功),则执行告警操作。Feature D, the second feature matching engine performs feature matching, and if a hit (equivalent to using the second type of rule in the above embodiment to match the data successfully), an alert operation is performed.
可选地,上述高性能入侵防御的方法的特征B还包括:Optionally, the feature B of the foregoing high-performance intrusion prevention method further includes:
特征B1,第一特征匹配引擎和第二特征匹配引擎位于同一运行环境, 或不同运行环境,建议位于不同运行环境;Feature B1, the first feature matching engine and the second feature matching engine are located in the same operating environment, or different operating environments, and are suggested to be located in different operating environments;
特征B2,两个特征匹配引擎采用同样的匹配算法,或采用不同的匹配算法。Feature B2, the two feature matching engines use the same matching algorithm or use different matching algorithms.
可选地,上述高性能入侵防御的方法的特征C还包括:Optionally, the feature C of the foregoing high-performance intrusion prevention method further includes:
特征C1,解析过滤模块在将数据包的数据元素发往第一特征匹配引擎时,需要缓存数据包,等待第一匹配引擎返回命中结果才执行后续流程;Feature C1, the parsing filtering module needs to cache the data packet when sending the data element of the data packet to the first feature matching engine, and wait for the first matching engine to return the hitting result to execute the subsequent process;
特征C2,解析过滤模块在将数据包的数据元素发往第一特征匹配引擎后直接执行后续流程,即发往响应模块执行放行操作,不需要等待第二匹配引擎返回命中结果;Feature C2, the parsing filter module directly executes the subsequent process after sending the data element of the data packet to the first feature matching engine, that is, sending the response module to perform the release operation, without waiting for the second matching engine to return the hit result;
特征C3,响应模块在将数据包的数据元素发往第一特征匹配引擎后直接执行后续操作,即执行放行操作,不需要等待第二匹配引擎返回命中结果。Feature C3, the response module directly performs the subsequent operation after sending the data element of the data packet to the first feature matching engine, that is, performing the release operation, without waiting for the second matching engine to return the hit result.
可选地,上述高性能入侵防御的方法的特征D还包括:Optionally, the feature D of the foregoing high-performance intrusion prevention method further includes:
特征D1,如果没有命中,第二特征匹配引擎结束匹配,不执行任何动作。Feature D1, if there is no hit, the second feature matching engine ends the match and does not perform any action.
本申请实施例中提供的一种高性能入侵防御的系统,包括一类规则库和二类规则库、第一特征匹配引擎和第二特征匹配引擎、输入模块、解析过滤模块、响应模块、输出模块、日志系统。A high performance intrusion prevention system provided in the embodiment of the present application includes a class rule base and a second class rule base, a first feature matching engine and a second feature matching engine, an input module, a parsing filter module, a response module, and an output. Module, log system.
输入模块、输出模块、日志系统:与图3记载的相关技术相同。The input module, the output module, and the log system are the same as those described in FIG.
一类规则库:包含动作为阻断操作(如丢弃、复位连接等)的规则(相当于上述实施例中的第一类规则);A type of rule base: a rule containing actions to block operations (such as dropping, resetting, etc.) (equivalent to the first type of rules in the above embodiment);
二类规则库:包含动作为告警的规则(相当于上述实施例中的第二类规则);The second type rule base: the rule containing the action as an alarm (corresponding to the second type of rule in the above embodiment);
解析过滤模块(相当于后续实施例2中的匹配模块的部分功能):对接收的数据包进行协议解析过滤后,优先调用第一特征匹配引擎,然后根据 匹配结果,调用第二特征匹配引擎,或者调用响应模块;The parsing filter module (corresponding to some functions of the matching module in the subsequent embodiment 2): after performing protocol parsing and filtering on the received data packet, preferentially calling the first feature matching engine, and then calling the second feature matching engine according to the matching result, Or call the response module;
第一特征匹配引擎(相当于后续实施例2中的匹配模块的部分功能):配置为加载一类规则库,并对数据元素进行匹配检测,返回匹配结果;The first feature matching engine (corresponding to some functions of the matching module in the subsequent embodiment 2) is configured to load a class rule base, perform matching detection on the data elements, and return a matching result;
第二特征匹配引擎(相当于后续实施例2中的匹配模块的部分功能):配置为加载二类规则库,并对数据元素进行匹配检测,如果命中,执行告警操作,否则不执行任何操作。The second feature matching engine (which is equivalent to the partial function of the matching module in the subsequent embodiment 2) is configured to load the second type rule base and perform matching detection on the data elements. If the hit occurs, the alarm operation is performed, otherwise no operation is performed.
响应模块(相当于后续实施例2中的处理模块的部分功能):配置为根据第一特征引擎的匹配结果执行操作,如果命中,则执行阻断操作(如丢弃、复位连接等),否则执行放行操作,可选地调用第二特征匹配引擎。a response module (corresponding to a part of the functions of the processing module in the subsequent embodiment 2): configured to perform an operation according to a matching result of the first feature engine, and if a hit, perform a blocking operation (such as discarding, resetting, etc.), otherwise executing Release the operation, optionally calling the second feature matching engine.
下面是本申请实施例的具体实施例。The following is a specific embodiment of the embodiment of the present application.
具体实施例1Specific embodiment 1
图4是根据具体实施例1的IPS实施方式一的内部结构示意图,如图4所示,其中的小标号①②③④⑤⑥⑦⑧⑨用于表示以下各个模块的交互顺序,可以对应到以下的各个模块描述中。本实施例的规则库分离后IPS实施方式一内部结构,对其中各个模块功能说明如下:FIG. 4 is a schematic diagram of an internal structure of an IPS implementation manner according to a specific embodiment 1. As shown in FIG. 4, the small reference numeral 123456789 is used to indicate the interaction order of the following modules, and may correspond to the following module descriptions. The internal structure of the IPS implementation mode after the rule base of the embodiment is separated, and the functions of each module are as follows:
输入模块、输出模块、日志系统等与图3记载的相关技术相同。The input module, the output module, the log system, and the like are the same as the related art described in FIG.
将规则库分为一类规则库和二类规则库,其中一类规则库包含动作为阻断(如丢弃、复位连接等)的规则,二类规则库包含动作为告警的规则,且一类规则库的优先级高于二类规则库。即优先将输入的数据包与一类规则库中的规则进行匹配,如果命中,则执行防御功能,包括执行阻断操作,具体包括丢弃数据包、复位数据流连接等操作,然后将没有命中的数据包与二类规则库中的规则进行匹配,如果命中,则执行告警操作,向日志系统发送告警信息。The rule base is divided into a class rule base and a second type rule base. One type of rule base includes rules for blocking (such as discarding, resetting, etc.), and the second class rule library includes rules for actions as alarms, and one type of rule. The rule base has a higher priority than the second type rule base. That is, the input data packet is preferentially matched with the rules in a type of rule base. If it is hit, the defense function is executed, including performing a blocking operation, including dropping the data packet, resetting the data flow connection, and the like, and then hitting no hit. The data packet is matched with the rules in the second-class rule base. If it is hit, an alarm operation is performed to send an alarm message to the log system.
对应不同的规则库,启动第一特征匹配引擎和第二特征匹配引擎,分别加载一类规则库和二类规则库。Corresponding to different rule bases, the first feature matching engine and the second feature matching engine are started, and a class rule library and a second class rule library are respectively loaded.
解析过滤模块,在原有数据包解析、过滤功能基础上,根据规则库的优先级,优先调用第一特征匹配引擎执行特征匹配,并缓存数据包,等待匹配结果;当第一特征匹配引擎返回匹配结果,如果命中,解析过滤模块调用响应模块,将数据包和匹配结果发送给响应模块,如果没有命中,则调用第二特征匹配引擎将数据元素发送给第二特征匹配引擎,同时将数据包和匹配结果发送给响应模块,在第二特征匹配引擎匹配过程中,不再需要缓存数据包。The parsing filter module, based on the original packet parsing and filtering function, preferentially invokes the first feature matching engine to perform feature matching according to the priority of the rule base, and caches the data packet, waiting for the matching result; when the first feature matching engine returns a match As a result, if the hit, the parsing filter module calls the response module, and sends the data packet and the matching result to the response module. If there is no hit, the second feature matching engine is called to send the data element to the second feature matching engine, and the data packet and The matching result is sent to the response module, and in the second feature matching engine matching process, the data packet is no longer needed to be cached.
第二特征匹配引擎执行特征匹配,如果命中,则执行告警操作向日志系统发送告警信息,否则不执行任何操作。The second feature matching engine performs feature matching. If the hit occurs, the alarm operation is performed to send an alarm message to the log system, otherwise no operation is performed.
响应模块,根据匹配结果,如果命中一类规则库中的规则,则执行防御操作,如执行阻断操作,同时向日志系统发送告警信息,否则执行放行操作。如果命中一类规则库中的规则,也可以由第一特征匹配引擎向日志系统发送告警信息。The response module, according to the matching result, performs a defense operation if a rule in a type of rule base is hit, such as performing a blocking operation, and simultaneously sending an alarm message to the log system, otherwise performing a release operation. If a rule in a type of rule base is hit, the first feature matching engine may also send an alert message to the log system.
具体实施例1可以包括以下工作流程:Specific embodiment 1 may include the following workflow:
步骤①,在系统启动或规则库更新时,第一特征匹配引擎加载一类规则库到内存中,第二特征匹配引擎加载二类规则库到内存中;Step 1. When the system starts or the rule base is updated, the first feature matching engine loads a class rule library into the memory, and the second feature matching engine loads the second class rule library into the memory;
步骤②,输入模块接到输入端口的数据包,发送给解析过滤模块;Step 2: the input module receives the data packet of the input port and sends the data packet to the parsing filtering module.
步骤③,解析过滤模块对接收的数据包进行协议解析过滤后,调用第一特征匹配引擎进行匹配,返回匹配结果;Step 3: After parsing and filtering the received data packet, the parsing filtering module calls the first feature matching engine to perform matching, and returns a matching result;
步骤④,如果命中,将执行步骤⑦解析过滤模块将数据包和第一特征匹配引擎的匹配结果发送给响应模块;Step 4: If the hit, the step 7 parsing filtering module sends the matching result of the data packet and the first feature matching engine to the response module;
步骤⑤,如果没有命中,解析过滤模块调用第二特征匹配引擎复制数据元素并发送给第二特征匹配引擎,同时执行步骤⑦调将数据包发送给响应模块;Step 5: If there is no hit, the parsing filtering module calls the second feature matching engine to copy the data element and sends the data element to the second feature matching engine, and performs step 7 to send the data packet to the response module;
步骤⑥,第二特征匹配引擎执行特征匹配如果命中,则执行告警操作 向日志系统发送告警信息,否则不执行任何操作。
步骤⑦,解析过滤模块数据包发送给响应模块,同时含有第一特征匹配引擎的匹配结果;Step 7, the parsing filter module data packet is sent to the response module, and the matching result of the first feature matching engine is included;
步骤⑧,响应模块根据匹配结果,如果命中一类规则库中的规则,则执行阻断操作,具体包括丢弃或复位连接,同时向日志系统发送告警信息,否则执行步骤⑨,将数据包发送给输出模块。Step 8: The response module performs a blocking operation according to the matching result, if a rule in a type of rule base is hit, specifically includes dropping or resetting the connection, and sending an alarm message to the log system, otherwise performing step 9 to send the data packet to Output module.
如果命中一类规则库中的规则,也可以由第一特征匹配引擎向日志系统发送告警信息。If a rule in a type of rule base is hit, the first feature matching engine may also send an alert message to the log system.
步骤⑨,响应模块将没有执行阻断操作的数据包发送到输出端口,传输到下一跳设备。In step 9, the response module sends the data packet that does not perform the blocking operation to the output port and transmits the data packet to the next hop device.
从上面处理过程看,由于在第二特征匹配引擎匹配过程中,不需要再等待匹配结果,也不需要缓存数据包,且由于二类规则库规模比较庞大,匹配比较耗时,从而减少了传输时延,提高缓存的利用率,直接提高了设备的吞吐量。From the above processing process, since there is no need to wait for the matching result in the second feature matching engine matching process, there is no need to cache the data packet, and since the size of the second type rule base is relatively large, the matching is time consuming, thereby reducing the transmission. Delay, improve the utilization of the cache, directly improve the throughput of the device.
同时将规则库分离,使得不同类型的特征匹配引擎可以独立部署,比如第一特征匹配引擎部署在主工作区(如工作在主中央处理器(CPU)核或主机的核心程序),第二特征匹配引擎部署辅工作区(如工作其他CPU核或主机的非核心程序),将极大减小主工作区的内存占用(降低90%左右),降低对主工作区内存要求。At the same time, the rule base is separated, so that different types of feature matching engines can be deployed independently, for example, the first feature matching engine is deployed in a main work area (such as a core program working on a main central processing unit (CPU) core or a host), and the second feature Matching the engine to deploy the secondary workspace (such as working with other CPU cores or non-core programs of the host) will greatly reduce the memory footprint of the main workspace (about 90% reduction) and reduce the memory requirements for the main workspace.
具体实施例2Specific embodiment 2
图5是根据具体实施例2的规则库分离后IPS实施方式二内部结构示意图,如图5所示,和具体实施例1基本相同,这里只描述与具体实施例1的区别。FIG. 5 is a schematic diagram of the internal structure of the second embodiment of the IPS implementation according to the second embodiment of the rule base. As shown in FIG. 5, it is basically the same as the specific embodiment 1. Only the difference from the specific embodiment 1 is described herein.
输入模块、输出模块、日志系统:与现有技术相同。Input module, output module, log system: same as the prior art.
一类规则库、二类规则库、第一特征匹配引擎、第二特征匹配引擎: 与具体实施例1中相同。A class rule base, a second class rule base, a first feature matching engine, and a second feature matching engine are the same as in the specific embodiment 1.
解析过滤模块,在原有数据包解析、过滤功能基础上,调用第一特征匹配引擎执行特征匹配,并缓存数据包,等待匹配结果;当第一特征匹配引擎返回匹配结果,将数据包、数据元素和匹配结果发送给响应模块。Parsing the filtering module, on the basis of the original packet parsing and filtering function, calling the first feature matching engine to perform feature matching, and buffering the data packet, waiting for the matching result; when the first feature matching engine returns the matching result, the data packet and the data element are And the matching result is sent to the response module.
响应模块,根据匹配结果,如果命中一类规则库中的规则,则执行阻断操作,如丢弃或复位连接等,同时向日志系统发送告警信息,否则复制数据元素发送给第二特征匹配引擎,同时执行放行操作,将数据包发送给输出模块。The response module, according to the matching result, performs a blocking operation, such as discarding or resetting the connection, and sends an alarm message to the log system, otherwise the duplicate data element is sent to the second feature matching engine. At the same time, the release operation is performed, and the data packet is sent to the output module.
具体实施例1和具体实施例2的区别是,具体实施例1中,由解析过滤模块调用第二特征匹配引擎,具体实施例2中,由响应模块调用第二特征匹配引擎。The difference between the specific embodiment 1 and the specific embodiment 2 is that, in the specific embodiment 1, the second feature matching engine is invoked by the parsing filtering module. In the specific embodiment 2, the second feature matching engine is invoked by the response module.
其工作过程与具体实施例2类似,不再赘述。The working process is similar to that of the specific embodiment 2 and will not be described again.
从上面处理过程看,由于在第二特征匹配引擎匹配过程中,不需要再等待匹配结果,也不需要缓存数据包,且由于二类规则库规模比较庞大,匹配比较耗时,从而减少了传输时延,提高缓存的利用率,直接高了设备的吞吐量。From the above processing process, since there is no need to wait for the matching result in the second feature matching engine matching process, there is no need to cache the data packet, and since the size of the second type rule base is relatively large, the matching is time consuming, thereby reducing the transmission. Delay, improve cache utilization, directly increase the throughput of the device.
同时将规则库分离,使得不同类型的特征匹配引擎可以独立部署,比如第一特征匹配引擎部署在主工作区(如工作在主CPU核或主机的核心程序),第二特征匹配引擎部署辅工作区(如工作其他CPU核或主机的非核心程序),将极大减小组工作区的内存占用(降低90%左右),降低对主工作区内存要求。At the same time, the rule base is separated, so that different types of feature matching engines can be deployed independently, for example, the first feature matching engine is deployed in the main work area (such as a core program working on the main CPU core or the host), and the second feature matching engine is deployed in the auxiliary work. Areas (such as working with other CPU cores or non-core programs of the host) will greatly reduce the memory footprint of the group work area (about 90% reduction) and reduce the memory requirements for the main work area.
具体实施例3Specific embodiment 3
图6是根据具体实施例3的规则库分离后IPS设备分离部署的示意图,如图6所示,由于规则库分离、特征匹配引擎分离后,IPS中的防御功能和告警检测功能解耦,为设备独立部署打下基础。FIG. 6 is a schematic diagram of the separation and deployment of the IPS device after the rule base is separated according to the third embodiment. As shown in FIG. 6 , after the rule base is separated and the feature matching engine is separated, the defense function and the alarm detection function in the IPS are decoupled. The basic deployment of equipment lays the foundation.
图6中白底图框表示IPS防御功能主要功能模块,由输入模块、检测过滤模块、第一特征匹配引擎、一类规则库、响应模块、输出模块和日志系统共同组成,位于同一防御设备中。The white background frame in Figure 6 represents the main function module of the IPS defense function, which is composed of an input module, a detection filtering module, a first feature matching engine, a class rule library, a response module, an output module, and a log system, and is located in the same defense device. .
图6中灰底图框表示IPS告警检测主要功能模,由输入模块、检测过滤模块、第二特征匹配引擎、二类规则库和日志系统共同组成,位于同一告警检测设备中。The gray bottom frame in FIG. 6 represents the main function mode of the IPS alarm detection, and is composed of an input module, a detection filtering module, a second feature matching engine, a second type rule base, and a log system, and is located in the same alarm detecting device.
数据包优先路由到IPS防御设备,IPS防御设备与一类规则库中规则进行匹配,如果命中,则执行阻断(如丢弃、复位连接等)操作和告警操作,如果没有命中,则将数据包输出到下一跳,同时复制数据包发送给IPS告警检测设备,其中发往IPS告警检测设备的数据包,可以进一步携带IPS防御设备解析的数据元素或数据元素和匹配结果。The packet is preferentially routed to the IPS defense device. The IPS defense device matches the rules in a type of rule base. If it hits, it performs blocking (such as dropping, resetting, etc.) operations and alarm operations. If there is no hit, the packet is forwarded. The data packet is sent to the IPS alarm detection device, and the data packet sent to the IPS alarm detection device can further carry the data element or data element and the matching result parsed by the IPS defense device.
IPS告警检测设备接收到IPS防御设备的到数据包后,与二类规则库中规则进行匹配,如果命中,则告警操作,否则不做操作。如果数据包中携带有数据元素,则可不需要再解析,直接利用这些数据元素,减小解析工作量。After receiving the IPS defense device's data packet, the IPS alarm detection device matches the rules in the second-class rule base. If it hits, the alarm is triggered. Otherwise, no operation is performed. If the data element is carried in the data packet, the data element can be directly used without further parsing, thereby reducing the parsing workload.
采用IPS防御和告警检测功能独立部署方式后,降低数据传输路径上的匹配工作量,降低时延,提高用户体验和设备的吞吐量,同时设备解耦,灵活部署。After the IPS defense and alarm detection function is used in the independent deployment mode, the matching workload on the data transmission path is reduced, the delay is reduced, the user experience and device throughput are improved, and the device is decoupled and deployed flexibly.
基于上述方法,本申请中提出了一种高效入侵防御的系统和方法,通过根据规则中动作的类型,将规则库划分为一类库和二类库,对应不同的特征库,采用不同的调用特征匹配引擎的方法,从而克服原有方案的问题,在不影响IPS功能的情况下,达到了提高IPS处理性能的效果,实现了一种高效的入侵防御系统,具有用户体验好、设备性能高、可靠性高、部署灵活的特点。Based on the above method, a system and method for efficient intrusion prevention is proposed in the present application. According to the type of action in the rule, the rule base is divided into a class library and a second class library, corresponding to different feature libraries, and different calls are adopted. The feature matching engine method overcomes the problem of the original solution and achieves the effect of improving the IPS processing performance without affecting the IPS function, and realizes an efficient intrusion prevention system with good user experience and high device performance. High reliability and flexible deployment.
通过以上的实施方式的描述,本领域的技术人员可以清楚地了解到根 据上述实施例的方法可借助软件加必需的通用硬件平台的方式来实现,当然也可以通过硬件,但很多情况下前者是更佳的实施方式。基于这样的理解,本申请的技术方案本质上或者说对现有技术做出贡献的部分可以以软件产品的形式体现出来,该计算机软件产品存储在一个存储介质(如ROM/RAM、磁碟、光盘)中,包括若干指令用以使得一台终端设备(可以是手机,计算机,服务器,或者网络设备等)执行本申请各个实施例所述的方法。Through the description of the above embodiments, those skilled in the art can clearly understand that the method according to the above embodiment can be implemented by means of software plus a necessary general hardware platform, and of course, by hardware, but in many cases, the former is A better implementation. Based on such understanding, the technical solution of the present application, which is essential or contributes to the prior art, may be embodied in the form of a software product stored in a storage medium (such as ROM/RAM, disk, The optical disc includes a number of instructions for causing a terminal device (which may be a mobile phone, a computer, a server, or a network device, etc.) to perform the methods described in various embodiments of the present application.
在本实施例中还提供了一种数据的处理装置,该装置用于实现上述实施例及优选实施方式,已经进行过说明的不再赘述。如以下所使用的,术语“模块”可以实现预定功能的软件和/或硬件的组合。尽管以下实施例所描述的装置较佳地以软件来实现,但是硬件,或者软件和硬件的组合的实现也是可能并被构想的。In the embodiment, a data processing device is also provided, which is used to implement the above-mentioned embodiments and preferred embodiments, and has not been described again. As used below, the term "module" may implement a combination of software and/or hardware of a predetermined function. Although the apparatus described in the following embodiments is preferably implemented in software, hardware, or a combination of software and hardware, is also possible and contemplated.
根据本申请的另一个实施例,还提供了一种数据的处理装置,该装置可以应用于IPS,包括:According to another embodiment of the present application, there is also provided a data processing apparatus, which can be applied to an IPS, including:
接收模块,配置为接收待通过的数据;a receiving module configured to receive data to be passed;
匹配模块,配置为依据第一类规则和/或第二类规则匹配所述接收模块接收的所述数据,其中,所述第一类规则包括阻断数据转发的规则,所述第二类规则包括执行数据告警的规则;The matching module is configured to match the data received by the receiving module according to the first type of rule and/or the second type of rule, where the first type of rule includes a rule for blocking data forwarding, and the second type of rule Including rules for performing data alerts;
处理模块,配置为依据所述匹配模块获得的是否匹配的结果处理所述数据。And a processing module configured to process the data according to a result of whether the matching module obtains a match.
在本申请的一种可选实施例中,所述匹配模块,还配置为依据所述第一类规则确定是否阻断转发所述数据;所述处理模块,配置为在所述匹配模块确定阻断转发所述数据的情况下,阻断所述数据的转发;在确定转发所述数据的情况下,转发所述数据至IPS的输出接口。In an optional embodiment of the present application, the matching module is further configured to determine, according to the first type of rule, whether to block forwarding of the data; and the processing module is configured to determine a resistance in the matching module. In the case of forwarding the data, the forwarding of the data is blocked; in the case of determining to forward the data, the data is forwarded to the output interface of the IPS.
在本申请的一种可选实施例中,所述处理模块,还配置为在所述匹配 模块确定转发所述数据之后,依据所述第二类规则确定是否对所述数据进行告警,其中,在确定对所述数据进行告警的情况下,发出第一告警信息。In an optional embodiment of the present application, the processing module is further configured to: after the matching module determines to forward the data, determine whether to alert the data according to the second type of rule, where In the case of determining to alert the data, the first alarm information is sent.
在本申请的一种可选实施例中,所述处理模块,还配置为在所述匹配模块确定阻断转发所述数据的情况下,发出第二告警信息。In an optional embodiment of the present application, the processing module is further configured to issue the second alarm information if the matching module determines to block forwarding of the data.
在本申请的一种可选实施例中,所述接收模块,还配置为所述匹配模块依据第一类规则和/或第二类规则匹配所述数据之前,分别从预设位置获取所述第一类规则和/或第二类规则,其中,所述第一类规则设置在所述IPS的主工作区;所述第二类规则设置在所述IPS的辅工作区。In an optional embodiment of the present application, the receiving module is further configured to: before the matching module matches the data according to the first type rule and/or the second type rule, respectively acquiring the a first type of rule and/or a second type of rule, wherein the first type of rule is set in a primary work area of the IPS; and the second type of rule is set in a secondary work area of the IPS.
在本申请的一种可选实施例中,所述第一类规则包括以下规则至少之一:丢弃数据的规则;复位连接的规则。In an optional embodiment of the present application, the first type of rule includes at least one of the following rules: a rule for discarding data; and a rule for resetting a connection.
需要说明的是,上述各个模块是可以通过软件或硬件来实现的,对于后者,可以通过以下方式实现,但不限于此:上述模块均位于同一处理器中;或者,上述各个模块以任意组合的形式分别位于不同的处理器中。It should be noted that each of the above modules may be implemented by software or hardware. For the latter, the foregoing may be implemented by, but not limited to, the foregoing modules are all located in the same processor; or, the above modules are in any combination. The forms are located in different processors.
需要说明的是:上述实施例提供的数据的处理装置在进行数据的处理时,仅以上述各程序模块的划分进行举例说明,实际应用中,可以根据需要而将上述处理分配由不同的程序模块完成,即将装置的内部结构划分成不同的程序模块,以完成以上描述的全部或者部分处理。另外,上述实施例提供的数据的处理装置与数据的处理方法实施例属于同一构思,其具体实现过程详见方法实施例,这里不再赘述。It should be noted that, when the data processing apparatus provided in the above embodiment performs data processing, only the division of each of the above-mentioned program modules is illustrated. In actual applications, the above processing may be allocated to different program modules as needed. Upon completion, the internal structure of the device is divided into different program modules to perform all or part of the processing described above. In addition, the data processing device and the data processing method embodiment provided by the foregoing embodiments are in the same concept, and the specific implementation process is described in detail in the method embodiment, and details are not described herein again.
根据本申请的另一个实施例,还提供了一种存储介质,所述存储介质中存储有计算机程序,所述计算机程序被设置为运行时执行上述实施例任一项所述的方法。According to another embodiment of the present application, there is also provided a storage medium having stored therein a computer program, the computer program being arranged to perform the method of any of the above embodiments when executed.
根据本申请的另一个实施例,还提供了一种电子装置,包括存储器和处理器,所述存储器中存储有计算机程序,所述处理器被设置为运行所述计算机程序以执行上述实施例任一项所述的方法。According to another embodiment of the present application, there is also provided an electronic device comprising a memory and a processor, wherein the memory stores a computer program, the processor being arranged to execute the computer program to perform the above embodiment One of the methods described.
可以理解,存储器可以是易失性存储器或非易失性存储器,也可包括易失性和非易失性存储器两者。其中,非易失性存储器可以是只读存储器(ROM,Read Only Memory)、可编程只读存储器(PROM,Programmable Read-Only Memory)、可擦除可编程只读存储器(EPROM,Erasable Programmable Read-Only Memory)、电可擦除可编程只读存储器(EEPROM,Electrically Erasable Programmable Read-Only Memory)、磁性随机存取存储器(FRAM,ferromagnetic random access memory)、快闪存储器(Flash Memory)、磁表面存储器、光盘、或只读光盘(CD-ROM,Compact Disc Read-Only Memory);磁表面存储器可以是磁盘存储器或磁带存储器。易失性存储器可以是随机存取存储器(RAM,Random Access Memory),其用作外部高速缓存。通过示例性但不是限制性说明,许多形式的RAM可用,例如静态随机存取存储器(SRAM,Static Random Access Memory)、同步静态随机存取存储器(SSRAM,Synchronous Static Random Access Memory)、动态随机存取存储器(DRAM,Dynamic Random Access Memory)、同步动态随机存取存储器(SDRAM,Synchronous Dynamic Random Access Memory)、双倍数据速率同步动态随机存取存储器(DDRSDRAM,Double Data Rate Synchronous Dynamic Random Access Memory)、增强型同步动态随机存取存储器(ESDRAM,Enhanced Synchronous Dynamic Random Access Memory)、同步连接动态随机存取存储器(SLDRAM,SyncLink Dynamic Random Access Memory)、直接内存总线随机存取存储器(DRRAM,Direct Rambus Random Access Memory)。本发明实施例描述的存储器旨在包括但不限于这些和任意其它适合类型的存储器。It will be appreciated that the memory can be either volatile memory or non-volatile memory, and can include both volatile and nonvolatile memory. The non-volatile memory may be a Read Only Memory (ROM), a Programmable Read-Only Memory (PROM), or an Erasable Programmable Read (EPROM). Only Memory), Electrically Erasable Programmable Read-Only Memory (EEPROM), Ferromagnetic Random Access Memory (FRAM), Flash Memory, Magnetic Surface Memory , CD-ROM, or Compact Disc Read-Only Memory (CD-ROM); the magnetic surface memory can be a disk storage or a tape storage. The volatile memory can be a random access memory (RAM) that acts as an external cache. By way of example and not limitation, many forms of RAM are available, such as Static Random Access Memory (SRAM), Synchronous Static Random Access Memory (SSRAM), Dynamic Random Access (SSRAM). DRAM (Dynamic Random Access Memory), Synchronous Dynamic Random Access Memory (SDRAM), Double Data Rate Synchronous Dynamic Random Access Memory (DDRSDRAM), enhancement Enhanced Synchronous Dynamic Random Access Memory (ESDRAM), Synchronous Dynamic Random Access Memory (SLDRAM), Direct Memory Bus Random Access Memory (DRRAM) ). The memories described in the embodiments of the present invention are intended to include, but are not limited to, these and any other suitable types of memory.
上述本发明实施例揭示的方法可以应用于处理器中,或者由处理器实现。处理器可能是一种集成电路芯片,具有信号的处理能力。在实现过程中,上述方法的各步骤可以通过处理器中的硬件的集成逻辑电路或者软件 形式的指令完成。上述的处理器可以是通用处理器、数字信号处理器(DSP,Digital Signal Processor),或者其他可编程逻辑器件、分立门或者晶体管逻辑器件、分立硬件组件等。处理器可以实现或者执行本发明实施例中的公开的各方法、步骤及逻辑框图。通用处理器可以是微处理器或者任何常规的处理器等。结合本发明实施例所公开的方法的步骤,可以直接体现为硬件译码处理器执行完成,或者用译码处理器中的硬件及软件模块组合执行完成。软件模块可以位于存储介质中,该存储介质位于存储器,处理器读取存储器中的信息,结合其硬件完成前述方法的步骤。The method disclosed in the foregoing embodiments of the present invention may be applied to a processor or implemented by a processor. The processor may be an integrated circuit chip with signal processing capabilities. In the implementation process, each step of the above method may be completed by an integrated logic circuit of hardware in the processor or an instruction in the form of software. The above processor may be a general purpose processor, a digital signal processor (DSP), or other programmable logic device, discrete gate or transistor logic device, discrete hardware component, or the like. The processor may implement or perform the methods, steps, and logic blocks disclosed in the embodiments of the present invention. A general purpose processor can be a microprocessor or any conventional processor or the like. The steps of the method disclosed in the embodiment of the present invention may be directly implemented as a hardware decoding processor, or may be performed by a combination of hardware and software modules in the decoding processor. The software module can be located in a storage medium, the storage medium being located in the memory, the processor reading the information in the memory, and completing the steps of the foregoing methods in combination with the hardware thereof.
显然,本领域的技术人员应该明白,上述的本申请的各模块或各步骤可以用通用的计算装置来实现,它们可以集中在单个的计算装置上,或者分布在多个计算装置所组成的网络上,可选地,它们可以用计算装置可执行的程序代码来实现,从而,可以将它们存储在存储装置中由计算装置来执行,并且在某些情况下,可以以不同于此处的顺序执行所示出或描述的步骤,或者将它们分别制作成各个集成电路模块,或者将它们中的多个模块或步骤制作成单个集成电路模块来实现。这样,本申请不限制于任何特定的硬件和软件结合。Obviously, those skilled in the art should understand that the above modules or steps of the present application can be implemented by a general computing device, which can be concentrated on a single computing device or distributed in a network composed of multiple computing devices. Alternatively, they may be implemented by program code executable by the computing device such that they may be stored in the storage device by the computing device and, in some cases, may be different from the order herein. The steps shown or described are performed, or they are separately fabricated into individual integrated circuit modules, or a plurality of modules or steps thereof are fabricated as a single integrated circuit module. Thus, the application is not limited to any particular combination of hardware and software.
以上所述仅为本申请的可选实施例而已,并不用于限制本申请,对于本领域的技术人员来说,本申请可以有各种更改和变化。凡在本申请的精神和原则之内,所作的任何修改、等同替换、改进等,均应包含在本申请的保护范围之内。The above description is only an optional embodiment of the present application, and is not intended to limit the present application, and various changes and modifications may be made to the present application. Any modifications, equivalent substitutions, improvements, etc. made within the spirit and principles of this application are intended to be included within the scope of the present application.
Claims (10)
Applications Claiming Priority (2)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN201810172675.2A CN110224969A (en) | 2018-03-01 | 2018-03-01 | The processing method and processing device of data |
| CN201810172675.2 | 2018-03-01 |
Publications (1)
| Publication Number | Publication Date |
|---|---|
| WO2019165883A1 true WO2019165883A1 (en) | 2019-09-06 |
Family
ID=67805142
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| PCT/CN2019/074469 Ceased WO2019165883A1 (en) | 2018-03-01 | 2019-02-01 | Data processing method and apparatus |
Country Status (2)
| Country | Link |
|---|---|
| CN (1) | CN110224969A (en) |
| WO (1) | WO2019165883A1 (en) |
Cited By (5)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN111353018A (en) * | 2020-02-24 | 2020-06-30 | 杭州迪普信息技术有限公司 | Data processing method, device and network device based on deep packet inspection |
| CN113282620A (en) * | 2021-04-23 | 2021-08-20 | 上海中通吉网络技术有限公司 | JSON alarm message structure unified standard processing method, system, equipment and storage medium |
| CN113923002A (en) * | 2021-09-29 | 2022-01-11 | 山石网科通信技术股份有限公司 | Computer network intrusion prevention method and device, storage medium and processor |
| CN114640515A (en) * | 2022-03-09 | 2022-06-17 | 京东科技信息技术有限公司 | Data processing method and device based on flow blocking and related equipment |
| CN115174351A (en) * | 2022-07-07 | 2022-10-11 | 深圳市积加跨境网络科技有限公司 | E-commerce operation early warning data generation method |
Families Citing this family (4)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN111240938A (en) * | 2020-01-10 | 2020-06-05 | 深圳市五联云科技有限公司 | Data congestion processing method and device based on face-brushing payment |
| CN115733732A (en) * | 2022-11-18 | 2023-03-03 | 新浪技术(中国)有限公司 | Prometheus-based alarm method, device and system |
| CN115834241B (en) * | 2022-12-27 | 2025-10-17 | 北京安博通科技股份有限公司 | Method and device for deploying IPS (in-plane switching) rules of intrusion prevention system and processing equipment |
| CN118694549A (en) * | 2023-03-21 | 2024-09-24 | 华为技术有限公司 | A business processing and information generation method and device |
Citations (5)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN1435977A (en) * | 2002-02-01 | 2003-08-13 | 联想(北京)有限公司 | Method for detecting and responding of fire wall invasion |
| CN101656634A (en) * | 2008-12-31 | 2010-02-24 | 暨南大学 | Intrusion detection system and method based on IPv6 network environment |
| CN105227515A (en) * | 2014-05-28 | 2016-01-06 | 腾讯科技(深圳)有限公司 | Network intrusions blocking-up method, Apparatus and system |
| US20160127402A1 (en) * | 2014-11-04 | 2016-05-05 | Patternex, Inc. | Method and apparatus for identifying and detecting threats to an enterprise or e-commerce system |
| CN107517214A (en) * | 2017-09-05 | 2017-12-26 | 合肥丹朋科技有限公司 | System and method for providing computer network security |
Family Cites Families (5)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN101022343B (en) * | 2007-03-19 | 2010-09-08 | 杭州华三通信技术有限公司 | Network invading detecting/resisting system and method |
| CN102970306B (en) * | 2012-12-18 | 2015-07-15 | 中国科学院计算机网络信息中心 | Intrusion detection system under Internet protocol version 6 (IPv6) network environment |
| US9405900B2 (en) * | 2013-03-13 | 2016-08-02 | General Electric Company | Intelligent cyberphysical intrusion detection and prevention systems and methods for industrial control systems |
| CN103957203B (en) * | 2014-04-19 | 2015-10-21 | 盐城工学院 | A network security defense system |
| CN106713017B (en) * | 2016-12-08 | 2020-06-19 | 国网北京市电力公司 | Alarm information processing method and device |
-
2018
- 2018-03-01 CN CN201810172675.2A patent/CN110224969A/en active Pending
-
2019
- 2019-02-01 WO PCT/CN2019/074469 patent/WO2019165883A1/en not_active Ceased
Patent Citations (5)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN1435977A (en) * | 2002-02-01 | 2003-08-13 | 联想(北京)有限公司 | Method for detecting and responding of fire wall invasion |
| CN101656634A (en) * | 2008-12-31 | 2010-02-24 | 暨南大学 | Intrusion detection system and method based on IPv6 network environment |
| CN105227515A (en) * | 2014-05-28 | 2016-01-06 | 腾讯科技(深圳)有限公司 | Network intrusions blocking-up method, Apparatus and system |
| US20160127402A1 (en) * | 2014-11-04 | 2016-05-05 | Patternex, Inc. | Method and apparatus for identifying and detecting threats to an enterprise or e-commerce system |
| CN107517214A (en) * | 2017-09-05 | 2017-12-26 | 合肥丹朋科技有限公司 | System and method for providing computer network security |
Cited By (7)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN111353018A (en) * | 2020-02-24 | 2020-06-30 | 杭州迪普信息技术有限公司 | Data processing method, device and network device based on deep packet inspection |
| CN111353018B (en) * | 2020-02-24 | 2023-11-10 | 杭州迪普信息技术有限公司 | Data processing method and device based on deep packet inspection and network equipment |
| CN113282620A (en) * | 2021-04-23 | 2021-08-20 | 上海中通吉网络技术有限公司 | JSON alarm message structure unified standard processing method, system, equipment and storage medium |
| CN113923002A (en) * | 2021-09-29 | 2022-01-11 | 山石网科通信技术股份有限公司 | Computer network intrusion prevention method and device, storage medium and processor |
| CN113923002B (en) * | 2021-09-29 | 2024-04-19 | 山石网科通信技术股份有限公司 | Computer network intrusion prevention method, device, storage medium and processor |
| CN114640515A (en) * | 2022-03-09 | 2022-06-17 | 京东科技信息技术有限公司 | Data processing method and device based on flow blocking and related equipment |
| CN115174351A (en) * | 2022-07-07 | 2022-10-11 | 深圳市积加跨境网络科技有限公司 | E-commerce operation early warning data generation method |
Also Published As
| Publication number | Publication date |
|---|---|
| CN110224969A (en) | 2019-09-10 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| WO2019165883A1 (en) | Data processing method and apparatus | |
| US11831420B2 (en) | Network application firewall | |
| US8677473B2 (en) | Network intrusion protection | |
| US10432649B1 (en) | System and method for classifying an object based on an aggregated behavior results | |
| US20170093891A1 (en) | Mobile device-based intrusion prevention system | |
| JP4196989B2 (en) | Method and system for preventing virus infection | |
| US10270792B1 (en) | Methods for detecting malicious smart bots to improve network security and devices thereof | |
| US20080060074A1 (en) | Intrusion detection system, intrusion detection method, and communication apparatus using the same | |
| CN110166459B (en) | Protection method, device and equipment for deserialization loophole and readable storage medium | |
| US20180020016A1 (en) | Processing network traffic to defend against attacks | |
| US10666618B2 (en) | Enhanced security techniques for remote reverse shell prevention | |
| US8533834B1 (en) | Antivirus intelligent flow framework | |
| CN107612890B (en) | Network monitoring method and system | |
| WO2023040303A1 (en) | Network traffic control method and related system | |
| CN117411711A (en) | Threat blocking method for intrusion detection defense system | |
| JP2003099339A (en) | Intrusion detection / prevention devices and programs | |
| CN101340680B (en) | Method and apparatus for implementing virus defending and virus killing by bi-core terminal | |
| KR102905027B1 (en) | DEVICE AND METHOD FOR DDoS DETECTION IN THE PROGRAMMABLE DATA PLANE | |
| CN112532610A (en) | Intrusion prevention detection method and device based on TCP segmentation | |
| CN118316656A (en) | Data packet processing method, device, electronic device and storage medium | |
| CN112039846B (en) | Request processing method and security protection system | |
| CN117353953A (en) | An intrusion detection method, device, system and storage medium | |
| WO2023160693A1 (en) | Attack blocking method and related apparatus | |
| WO2024045542A1 (en) | Method and apparatus for preventing erroneous blocking in distributed denial of service (ddos) attack | |
| CN113518055B (en) | Data security protection processing method and device, storage medium and terminal |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| 121 | Ep: the epo has been informed by wipo that ep was designated in this application |
Ref document number: 19760865 Country of ref document: EP Kind code of ref document: A1 |
|
| NENP | Non-entry into the national phase |
Ref country code: DE |
|
| 32PN | Ep: public notification in the ep bulletin as address of the adressee cannot be established |
Free format text: NOTING OF LOSS OF RIGHTS PURSUANT TO RULE 112(1) EPC (EPO FORM 1205 DATED 20/01/2021) |
|
| 122 | Ep: pct application non-entry in european phase |
Ref document number: 19760865 Country of ref document: EP Kind code of ref document: A1 |