CN114362368A - Method and system for monitoring abnormal behavior of network traffic in smart substation - Google Patents
Method and system for monitoring abnormal behavior of network traffic in smart substation Download PDFInfo
- Publication number
- CN114362368A CN114362368A CN202111670704.6A CN202111670704A CN114362368A CN 114362368 A CN114362368 A CN 114362368A CN 202111670704 A CN202111670704 A CN 202111670704A CN 114362368 A CN114362368 A CN 114362368A
- Authority
- CN
- China
- Prior art keywords
- message
- application layer
- service
- layer message
- abnormal
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Granted
Links
- 238000000034 method Methods 0.000 title claims abstract description 41
- 238000012544 monitoring process Methods 0.000 title claims abstract description 30
- 206010000117 Abnormal behaviour Diseases 0.000 title claims description 17
- 238000001514 detection method Methods 0.000 claims abstract description 143
- 230000002159 abnormal effect Effects 0.000 claims abstract description 63
- 238000012795 verification Methods 0.000 claims abstract description 54
- 230000006399 behavior Effects 0.000 claims abstract description 36
- 230000008878 coupling Effects 0.000 claims abstract description 22
- 238000010168 coupling process Methods 0.000 claims abstract description 22
- 238000005859 coupling reaction Methods 0.000 claims abstract description 22
- 230000005540 biological transmission Effects 0.000 claims description 61
- 230000005856 abnormality Effects 0.000 claims description 51
- 230000008569 process Effects 0.000 claims description 18
- 238000012360 testing method Methods 0.000 claims description 17
- 238000012790 confirmation Methods 0.000 claims description 14
- 230000006870 function Effects 0.000 claims description 12
- 230000000903 blocking effect Effects 0.000 claims description 11
- 238000004590 computer program Methods 0.000 claims description 10
- 230000004048 modification Effects 0.000 claims description 10
- 238000012986 modification Methods 0.000 claims description 10
- 238000012546 transfer Methods 0.000 claims description 6
- 238000004364 calculation method Methods 0.000 claims description 5
- 238000005259 measurement Methods 0.000 claims description 2
- 241001214347 Tehran virus Species 0.000 claims 1
- 230000001105 regulatory effect Effects 0.000 claims 1
- 230000001360 synchronised effect Effects 0.000 claims 1
- 238000004458 analytical method Methods 0.000 abstract description 7
- 230000007547 defect Effects 0.000 abstract 1
- 238000002360 preparation method Methods 0.000 description 8
- 230000006641 stabilisation Effects 0.000 description 7
- 238000011105 stabilization Methods 0.000 description 7
- 230000004913 activation Effects 0.000 description 6
- 230000008859 change Effects 0.000 description 6
- 230000006854 communication Effects 0.000 description 5
- 238000010586 diagram Methods 0.000 description 4
- 239000000284 extract Substances 0.000 description 3
- 230000004044 response Effects 0.000 description 3
- NAWXUBYGYWOOIX-SFHVURJKSA-N (2s)-2-[[4-[2-(2,4-diaminoquinazolin-6-yl)ethyl]benzoyl]amino]-4-methylidenepentanedioic acid Chemical compound C1=CC2=NC(N)=NC(N)=C2C=C1CCC1=CC=C(C(=O)N[C@@H](CC(=C)C(O)=O)C(O)=O)C=C1 NAWXUBYGYWOOIX-SFHVURJKSA-N 0.000 description 2
- 230000001186 cumulative effect Effects 0.000 description 2
- 230000007123 defense Effects 0.000 description 2
- 230000007812 deficiency Effects 0.000 description 2
- 238000005516 engineering process Methods 0.000 description 2
- 230000036244 malformation Effects 0.000 description 2
- 230000009286 beneficial effect Effects 0.000 description 1
- 238000004891 communication Methods 0.000 description 1
- 230000009133 cooperative interaction Effects 0.000 description 1
- 230000009849 deactivation Effects 0.000 description 1
- 238000002347 injection Methods 0.000 description 1
- 239000007924 injection Substances 0.000 description 1
- 238000007689 inspection Methods 0.000 description 1
- 239000000243 solution Substances 0.000 description 1
Images
Classifications
-
- Y—GENERAL TAGGING OF NEW TECHNOLOGICAL DEVELOPMENTS; GENERAL TAGGING OF CROSS-SECTIONAL TECHNOLOGIES SPANNING OVER SEVERAL SECTIONS OF THE IPC; TECHNICAL SUBJECTS COVERED BY FORMER USPC CROSS-REFERENCE ART COLLECTIONS [XRACs] AND DIGESTS
- Y02—TECHNOLOGIES OR APPLICATIONS FOR MITIGATION OR ADAPTATION AGAINST CLIMATE CHANGE
- Y02E—REDUCTION OF GREENHOUSE GAS [GHG] EMISSIONS, RELATED TO ENERGY GENERATION, TRANSMISSION OR DISTRIBUTION
- Y02E60/00—Enabling technologies; Technologies with a potential or indirect contribution to GHG emissions mitigation
-
- Y—GENERAL TAGGING OF NEW TECHNOLOGICAL DEVELOPMENTS; GENERAL TAGGING OF CROSS-SECTIONAL TECHNOLOGIES SPANNING OVER SEVERAL SECTIONS OF THE IPC; TECHNICAL SUBJECTS COVERED BY FORMER USPC CROSS-REFERENCE ART COLLECTIONS [XRACs] AND DIGESTS
- Y04—INFORMATION OR COMMUNICATION TECHNOLOGIES HAVING AN IMPACT ON OTHER TECHNOLOGY AREAS
- Y04S—SYSTEMS INTEGRATING TECHNOLOGIES RELATED TO POWER NETWORK OPERATION, COMMUNICATION OR INFORMATION TECHNOLOGIES FOR IMPROVING THE ELECTRICAL POWER GENERATION, TRANSMISSION, DISTRIBUTION, MANAGEMENT OR USAGE, i.e. SMART GRIDS
- Y04S10/00—Systems supporting electrical power generation, transmission or distribution
- Y04S10/16—Electric power substations
Landscapes
- Data Exchanges In Wide-Area Networks (AREA)
Abstract
Description
技术领域technical field
本发明涉及电力系统信息安全技术领域,尤其涉及一种智能变电站网络流量异常行为监测方法与系统。The invention relates to the technical field of power system information security, in particular to a method and system for monitoring abnormal behavior of network traffic in an intelligent substation.
背景技术Background technique
随着先进信息通信技术以及智能电子设备在变电站的广泛应用,目前的变电站已经逐步发展成为融合自动控制、智能决策、协同交互等高级功能的新一代智能变电站。智能变电站通信过程中的信息传输以网络流量为载体,流量数据的正常传输对智能变电站以及整个电力系统的安全稳定运行至关重要。网络攻击者可以通过拦截、窃取、篡改流量数据达到破坏智能变电站安全稳定运行的目的,因此网络流量的异常行为检测是智能变电站网络安全主动防御的关键手段。With the wide application of advanced information and communication technology and intelligent electronic equipment in substations, the current substations have gradually developed into a new generation of intelligent substations that integrate advanced functions such as automatic control, intelligent decision-making, and collaborative interaction. The information transmission in the communication process of the smart substation takes the network traffic as the carrier, and the normal transmission of the traffic data is very important to the safe and stable operation of the smart substation and the entire power system. Network attackers can destroy the safe and stable operation of smart substations by intercepting, stealing, and tampering with traffic data. Therefore, abnormal behavior detection of network traffic is a key means of active defense of smart substation network security.
然而,已有的智能变电站网络流量异常检测方法侧重于在网络层根据特定的流量特征指标进行检测,不能体现具体的异常情况。而流量数据的应用层报文包含重要的电力业务信息,仅根据网络层流量特征指标不能全面地反映攻击行为的特征。因此,亟需发明一种新的智能变电站网络流量异常行为监测方法,实现流量数据应用层报文的异常检测,保障智能变电站的安全、可靠运行。However, the existing intelligent substation network traffic anomaly detection methods focus on detection based on specific traffic characteristic indicators at the network layer, and cannot reflect specific abnormal situations. However, application layer packets of traffic data contain important power service information, and only based on network layer traffic characteristic indicators cannot fully reflect the characteristics of attack behaviors. Therefore, it is urgent to invent a new method for monitoring abnormal behavior of network traffic in smart substations, which can realize abnormal detection of traffic data application layer messages and ensure the safe and reliable operation of smart substations.
发明内容SUMMARY OF THE INVENTION
本发明所要解决的技术问题是,针对现有技术不足,提供一种智能变电站网络流量异常行为监测方法与系统,有效解决现有检测方法不能针对电力业务在应用层的异常行为进行检测的局限性,提升智能变电站通信过程中流量信息传输的安全性和可靠性。The technical problem to be solved by the present invention is to provide a method and system for monitoring abnormal behavior of network traffic in smart substations in view of the deficiencies of the prior art, which can effectively solve the limitation that the existing detection method cannot detect the abnormal behavior of power services at the application layer. , to improve the security and reliability of traffic information transmission in the communication process of smart substations.
为解决上述技术问题,本发明所采用的技术方案是:一种智能变电站网络流量异常行为监测方法,包括以下步骤:In order to solve the above-mentioned technical problems, the technical solution adopted by the present invention is: a method for monitoring abnormal behavior of network traffic in an intelligent substation, comprising the following steps:
S1、实时捕获智能变电站网络流量数据,并提取出应用层报文;S1. Capture the network traffic data of the smart substation in real time, and extract the application layer messages;
S2、根据步骤S1提取出的应用层报文所属协议规定的帧格式对报文进行字段级的解析;S2, perform field-level analysis on the message according to the frame format specified by the protocol to which the application layer message extracted in step S1 belongs;
S3、对解析后的应用层报文进行单字段越限检测,若出现异常,则发出告警信号;否则对解析后的应用层报文进行多字段耦合逻辑检测,若出现异常,则发出告警信号;否则对解析后的应用层报文进行整体字段异常检测,若出现异常,则发出告警信号;否则,进入步骤S4;S3. Perform single-field out-of-limit detection on the parsed application layer packet, and send an alarm signal if an abnormality occurs; otherwise, perform multi-field coupling logic detection on the parsed application layer packet, and send an alarm signal if abnormality occurs ; otherwise, perform overall field anomaly detection on the parsed application layer message, and if an anomaly occurs, send an alarm signal; otherwise, go to step S4;
S4、对解析后的应用层报文进行业务执行逻辑检测、业务校验逻辑检测、业务时标逻辑检测,若任何一个检测环节出现异常,则发出告警信号。S4. Perform service execution logic detection, service verification logic detection, and service time stamp logic detection on the parsed application layer message. If any detection link is abnormal, an alarm signal is issued.
本发明通过对智能变电站网络流量数据应用层报文的提取及解析,并依此进行异常检测,实现了应用层报文在单帧层面的单字段、多字段、整体字段异常检测,克服了现有检测方法只能针对报文格式进行简单畸形校验的不足。同时,也实现了应用层报文在多帧层面的业务执行逻辑、业务校验逻辑、业务时标逻辑的异常检测,克服了现有检测方法不能针对电力业务在应用层的异常行为进行检测的局限性,有效提升了智能变电站流量数据传输的安全性与可靠性。The invention extracts and parses the application layer message of the network flow data of the intelligent substation, and performs abnormal detection accordingly, realizes the abnormal detection of single field, multi-field and overall field of the application layer message at the single frame level, and overcomes the problem of existing problems. Some detection methods can only perform simple malformation check for the message format. At the same time, it also realizes the abnormal detection of the service execution logic, service verification logic, and service time stamping logic of the application layer message at the multi-frame layer, overcoming the problem that the existing detection methods cannot detect the abnormal behavior of the power service at the application layer. Limitations, effectively improve the security and reliability of smart substation flow data transmission.
对解析后的应用层报文进行单字段越限检测的具体实现过程包括:The specific implementation process of single-field out-of-limit detection for the parsed application layer message includes:
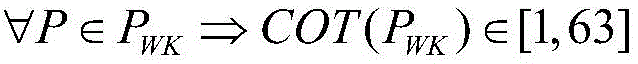
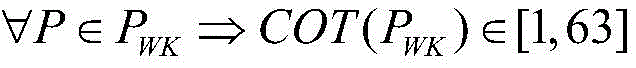
1)利用公式对解析后的应用层报文进行单字段越限检测,若该式不成立,则判定解析后的应用层报文为异常报文;否则,进入步骤2);其中,P为解析后的应用层报文,PWK表示电力稳控业务的可变帧报文,LEN(PWK)表示解析后的应用层报文实际长度,LEN(PWK)max表示电力稳控协议所规定的最大报文长度;1) Using the formula Perform single-field out-of-limit detection on the parsed application layer packet, if the formula does not hold, then determine that the parsed application layer packet is an abnormal packet; otherwise, go to step 2); where P is the parsed application layer message, P WK represents the variable frame message of the power stabilization control service, LEN(P WK ) represents the actual length of the parsed application layer message, and LEN(P WK ) max represents the maximum message specified by the power stabilization control protocol length;
2)判断公式是否成立,若否,则判定解析后的应用层报文为异常报文;否则,进入步骤3);其中,THE(PWK)表示报文理论计算长度;2) Judgment formula Whether it is established, if not, it is determined that the parsed application layer message is an abnormal message; otherwise, enter step 3); wherein, THE (P WK ) represents the theoretical calculation length of the message;
3)判断公式是否成立,若否,则判定解析后的应用层报文为异常报文;否则,进入步骤4);其中,TYP(PWK)表示报文的类型标识字段值;3) Judgment formula Whether it is established, if not, it is determined that the parsed application layer message is an abnormal message; otherwise, go to step 4); wherein, TYP (P WK ) represents the type identifier field value of the message;
4)判断公式是否成立,若否,则判定解析后的应用层报文为异常报文;否则,进入步骤5);其中,COT(PWK)表示报文的传送原因字段值;4) Judgment formula Whether it is established, if not, it is determined that the parsed application layer message is an abnormal message; otherwise, go to step 5); wherein, COT(P WK ) represents the transmission reason field value of the message;
5)判断公式是否成立,若否,则判定解析后的应用层报文为异常报文;否则,对解析后的应用层报文进行多字段耦合逻辑检测;其中,PWK_G表示电力稳控业务固定帧报文,LEN(PWK_G)表示固定帧报文长度。5) Judgment formula Whether it is true, if not, it is determined that the parsed application layer packet is an abnormal packet; otherwise, the multi-field coupling logic detection is performed on the parsed application layer packet; among them, P WK_G represents the fixed frame packet of the power stabilization control service , LEN(P WK_G ) represents the fixed frame message length.
本发明的单字段越限检测能够对报文的长度字段、类型标识字段、传送原因字段等单个字段进行基于阈值的越限检测。攻击者在构造或篡改报文时由于缺乏电力知识,存在对报文单个字段的试探性修改或赋值,会使报文单个字段的数值超出其阈值,而这种异常仅通过报文的格式检查不能检测出,但通过单字段越限检测能够精准识别。本发明所提供的单字段越限检测能够及时处理字段值越限报文,避免畸形报文影响正常的通信过程。·The single-field over-limit detection of the present invention can perform threshold-based over-limit detection for single fields such as the length field, the type identification field, and the transmission reason field of the message. Due to the lack of electrical knowledge when constructing or tampering with the message, the attacker can tentatively modify or assign a single field of the message, which will cause the value of a single field of the message to exceed its threshold, and this anomaly can only be checked by the format of the message. It cannot be detected, but it can be accurately identified by single-field out-of-limit detection. The single-field out-of-limit detection provided by the present invention can process the field value out-of-limit message in time, and avoid the abnormal message from affecting the normal communication process. ·
步骤S3中,对解析后的应用层报文进行多字段耦合逻辑检测的具体实现过程包括:In step S3, the specific implementation process of performing multi-field coupling logic detection on the parsed application layer message includes:
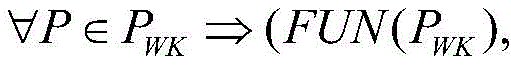
I)判断公式是否成立,若否,则判定解析后的应用层报文为异常报文;否则,进入步骤II);其中,P为解析后的应用层报文,PWK表示电力稳控业务的可变帧报文,FUN(PWK)表示报文控制域功能码数值,FCV(PWK)表示报文帧计数有效位数值;I) Judgment formula Whether it is true, if not, it is determined that the parsed application layer message is an abnormal message; otherwise, go to step II); wherein, P is the parsed application layer message, and P WK represents the variable frame of the power stabilization control service message, FUN(P WK ) represents the function code value of the message control field, and FCV(P WK ) represents the valid bit value of the message frame count;
II)判断公式是否成立,若否,则判定解析后的应用层报文为异常报文;否则,对解析后的应用层报文进行整体字段异常检测;其中,QU(PWK)表示报文的被测量品质描述词,OV表示品质描述词的溢出标志,ER表示品质描述词的有效标志。II) Judgment formula Whether it is true, if not, it is determined that the parsed application layer packet is an abnormal packet; otherwise, the overall field anomaly detection is performed on the parsed application layer packet; wherein, QU(P WK ) represents the measured quality of the packet descriptor, OV represents the overflow flag of the quality descriptor, and ER represents the valid flag of the quality descriptor.
本发明的多字段耦合逻辑检测过程能够实现报文控制域功能码耦合逻辑以及被测量品质描述词耦合逻辑的异常检测。攻击者在构造恶意报文时会同时对多个字段进行篡改,多字段的同时篡改会破坏字段与字段之间的正常耦合逻辑,这种耦和逻辑异常仅通过现有的报文格式合法性检查不能进行识别,而通过多字段耦合逻辑检测能够精准判别。本发明所提供的多字段耦合逻辑检测克服了现有检测方法只能针对报文格式进行简单畸形校验的不足,能够有效防止报文控制域信息被恶意篡改,同时保障量测数据的正常、可靠传输。The multi-field coupling logic detection process of the present invention can realize the abnormal detection of the message control field function code coupling logic and the measured quality descriptor coupling logic. An attacker will tamper with multiple fields at the same time when constructing a malicious message. Simultaneous tampering with multiple fields will destroy the normal coupling logic between fields. This kind of coupling and logic exception can only pass through the validity of the existing message format. Inspection cannot identify, but can be accurately identified through multi-field coupled logic detection. The multi-field coupling logic detection provided by the present invention overcomes the shortcoming that the existing detection method can only perform simple malformation check for the message format, can effectively prevent the message control field information from being maliciously tampered with, and at the same time guarantees the normality and integrity of the measurement data. Reliable transmission.
步骤S3中,对解析后的应用层报文进行整体字段异常检测的具体实现过程包括:判断公式是否成立,若否,则判定解析后的应用层报文为异常报文;否则,进入步骤II);其中,P为解析后的应用层报文,PWK表示电力稳控业务的可变帧报文,其中,THE_V(PWK)表示报文理论校验和,为启动字符至校验和字段前的数据单字节算术累加和的低字节,REA_V(PWK)表示报文实际校验和,为报文最后一个字节。In step S3, the specific implementation process of performing overall field anomaly detection on the parsed application layer message includes: a judgment formula Whether it is true, if not, it is determined that the parsed application layer message is an abnormal message; otherwise, go to step II); wherein, P is the parsed application layer message, and P WK represents the variable frame of the power stabilization control service message, where THE_V(P WK ) represents the theoretical checksum of the message, which is the low byte of the single-byte arithmetic cumulative sum of the data before the start character to the checksum field, and REA_V(P WK ) represents the actual checksum of the message. The checksum is the last byte of the message.
本发明的整体字段异常检测能够在不区分报文具体字段的整体层面实现异常检测,根据报文理论校验和的计算方法进行计算,如果得到的结果和报文中的校验和字段不一致则判定报文的校验和错误,并进行告警。本发明提供的整体字段异常检测方法克服了现有检测方法仅能针对报文格式校验的局限性,能够识别出畸形报文、异常报文,提升了报文传输的安全性与可用性。The overall field anomaly detection of the present invention can realize anomaly detection at the overall level without distinguishing the specific fields of the message. The calculation is performed according to the calculation method of the theoretical checksum of the message. If the obtained result is inconsistent with the checksum field in the message Determine the checksum error of the packet and generate an alarm. The overall field anomaly detection method provided by the invention overcomes the limitation that the existing detection methods can only check the message format, can identify malformed messages and abnormal messages, and improves the security and availability of message transmission.
步骤S4的具体实现过程包括:The specific implementation process of step S4 includes:
根据解析后的应用层报文的类型标识、传送原因、功能类型、信息序号字段判断解析后的应用层报文所属具体业务;Determine the specific service to which the parsed application layer packet belongs according to the type identifier, transmission reason, function type, and information sequence number fields of the parsed application layer packet;
若为文件传输、总召唤、测试模式、监视方向闭锁、遥控执行、遥调执行、扰动数据传输业务中的一种,则对解析后的应用层报文所属业务的执行逻辑进行检测,如果出现异常,则发出告警信号,否则将当前帧流量数据判定为正常流量;If it is one of the services of file transmission, general call, test mode, monitoring direction blocking, remote control execution, remote adjustment execution, and disturbance data transmission, the execution logic of the service to which the parsed application layer message belongs is detected. If abnormal, an alarm signal will be sent, otherwise, the current frame traffic data will be judged as normal traffic;
若为遥控校验、定值修改业务中的一种,则对解析后的应用层报文所属业务的校验逻辑进行检测,如果出现异常,则发出告警信号,否则将当前帧流量数据判定为正常流量;If it is one of the remote control verification and fixed value modification services, the verification logic of the service to which the parsed application layer message belongs will be detected. If there is an abnormality, an alarm signal will be sent. Otherwise, the current frame traffic data will be determined as normal flow;
若为通用历史数据查询、时间同步业务中的一种,则对解析后的应用层报文所属业务的时标逻辑进行检测,如果出现异常,则发出告警信号,否则将当前帧流量数据判定为正常流量。If it is one of the general historical data query and time synchronization services, the time stamping logic of the service to which the parsed application layer packet belongs will be detected. If an abnormality occurs, an alarm signal will be sent. Otherwise, the current frame traffic data will be determined as normal flow.
本发明的多帧报文业务逻辑异常检测能够检测各类业务的执行逻辑、校验逻辑、时标逻辑是否正确,克服了现有智能变电站网络流量异常检测方法侧重于单帧报文的简单格式校验,不能针对具体电力业务在应用层的业务逻辑进行检测的局限性。攻击者对各类业务逻辑的破坏均通过对正常报文的篡改或直接注入,这种攻击行为仅通过单帧报文无法识别,但通过本发明提供的多帧报文业务逻辑分析能够精准识别。The multi-frame message business logic abnormality detection of the present invention can detect whether the execution logic, verification logic and time stamp logic of various services are correct, and overcomes the simple format of the existing intelligent substation network traffic abnormality detection method that focuses on single-frame messages Check, the limitation of not being able to detect the business logic of the specific power business in the application layer. Attackers destroy all kinds of business logic through tampering or direct injection of normal packets. This attack behavior cannot be identified only through single-frame packets, but can be accurately identified through the business logic analysis of multi-frame packets provided by the present invention. .
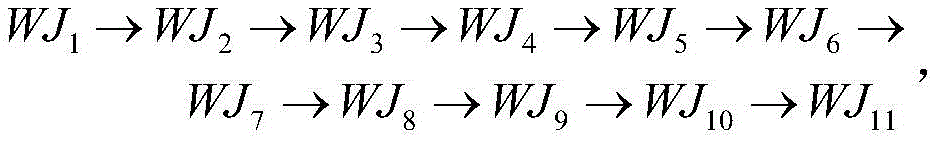
若解析后的应用层报文属于文件传输业务,则判断是否符合执行逻辑若否,发出告警信号,否则将当前帧流量数据判定为正常流量;其中,WJ1为召唤目录指令,WJ2为文件目录响应指令,WJ3为选择文件指令,WJ4为文件准备就绪指令,WJ5为召唤文件指令,WJ6为节准备就绪指令,WJ7为召唤节指令,WJ8为段数据上送指令,WJ9为最后的段发送确认指令,WJ10为节确认指令,WJ11为文件确认指令;If the parsed application layer message belongs to the file transfer service, it is judged whether it conforms to the execution logic If no, send an alarm signal, otherwise, the current frame traffic data is judged as normal traffic; wherein, WJ 1 is a call directory command, WJ 2 is a file directory response command, WJ 3 is a file selection command, and WJ 4 is a file ready command, WJ 5 is the calling file command, WJ 6 is the section ready command, WJ 7 is the calling section command, WJ 8 is the segment data upload command, WJ 9 is the last segment sending confirmation command, WJ 10 is the section confirmation command, WJ 11 Confirmation of instructions for documents;
若解析后的应用层报文属于总召唤业务,则判断是否符合执行逻辑ZZ1→ZZ2→ZZ3,若否,发出告警信号,否则将当前帧流量数据判定为正常流量;其中,ZZ1为主站启动总召唤指令,ZZ2为子站上送信息指令,ZZ3为总召唤结束指令;If the parsed application layer packet belongs to the general call service, it is judged whether it conforms to the execution logic ZZ 1 → ZZ 2 → ZZ 3 , if not, an alarm signal is sent, otherwise the current frame traffic data is judged as normal traffic; among them, ZZ 1 Start the general call command for the master station, ZZ 2 is the slave station sending information command, and ZZ 3 is the general call end command;
若解析后的应用层报文属于测试模式业务,则判断是否符合执行逻辑CS1→CS2→CS1→CS2,若否,发出告警信号,否则将当前帧流量数据判定为正常流量;其中,CS1为测试激活指令,CS2为测试结束指令;If the parsed application layer packet belongs to the test mode service, it is judged whether it conforms to the execution logic CS 1 → CS 2 → CS 1 → CS 2 , if not, an alarm signal is sent, otherwise the current frame traffic data is judged as normal traffic; , CS 1 is the test activation command, CS 2 is the test end command;
若解析后的应用层报文属于监视方向闭锁业务,则判断是否符合执行逻辑BS1→BS2→BS1→BS2,若否,发出告警信号,否则将当前帧流量数据判定为正常流量;If the parsed application layer packet belongs to the monitoring direction blocking service, it is judged whether it conforms to the execution logic BS 1 → BS 2 → BS 1 → BS 2 , if not, an alarm signal is sent, otherwise, the current frame traffic data is judged as normal traffic;
若解析后的应用层报文属于遥控执行业务,则判断是否符合执行逻辑YK1→YK2→YK3→YK4,若否,发出告警信号,否则将当前帧流量数据判定为正常流量;If the parsed application layer message belongs to the remote control execution service, it is judged whether it conforms to the execution logic YK 1 → YK 2 → YK 3 → YK 4 , if not, an alarm signal is sent, otherwise the current frame traffic data is judged as normal traffic;
若解析后的应用层报文属于遥调执行业务,则判断是否符合执行逻辑YT1→YT2→YT3→YT4,若否,发出告警信号,否则将当前帧流量数据判定为正常流量;其中,YT1为遥调设置指令,YT2为遥调设置返校指令,YT3为遥调执行指令,YT4为遥调执行返校指令;If the parsed application layer packet belongs to the remote adjustment execution service, it is judged whether it conforms to the execution logic YT 1 → YT 2 → YT 3 → YT 4 , if not, an alarm signal is sent, otherwise the current frame traffic data is judged as normal traffic; Among them, YT 1 is the remote adjustment setting instruction, YT 2 is the remote adjustment setting return-to-calibration instruction, YT 3 is the remote adjustment execution instruction, and YT 4 is the remote adjustment execution return-to-calibration instruction;
若解析后的应用层报文属于扰动数据传输业务,则判断是否符合执行逻辑RD1→RD2→RD3→RD4→RD5→RD6,若否,发出告警信号,否则将当前帧流量数据判定为正常流量;其中,RD1为扰动数据传输准备指令,RD2为传输通道准备指令,RD3为带标志的状态变位传输准备指令,RD4为带标志的状态变位传输指令,RD5为传输扰动值指令,RD6为传输结束指令。If the parsed application layer message belongs to the disturbed data transmission service, it is judged whether it conforms to the execution logic RD 1 →RD 2 →RD 3 →RD 4 →RD 5 →RD 6 , if not, send an alarm signal, otherwise the current frame traffic The data is judged to be a normal flow; wherein, RD 1 is a preparation command for disturbed data transmission, RD 2 is a preparation command for a transmission channel, RD 3 is a state change transmission preparation command with a flag, and RD 4 is a state change transmission command with a flag. RD 5 is the command to transmit the disturbance value, and RD 6 is the command to end the transmission.
本发明通过对智能变电站多种电力业务的执行逻辑进行异常检测,能够识别出业务执行过程中指令缺失、指令重复、指令错误等不符合正常业务执行逻辑的情况。针对业务执行逻辑的攻击,攻击报文的格式、字段逻辑、字段阈值等特征均正常,且报文数量不多,不会反映在网络层流量特征上,现有的网络层流量特征分析、报文格式检查等方法不能识别,但本发明的检测方法能够准确识别该攻击行为,有效防止攻击者对业务执行指令进行篡改、注入、拦截从而对电力系统造成大的破坏。By performing abnormal detection on the execution logic of various electric power services in the smart substation, the present invention can identify situations that do not conform to normal service execution logic, such as instruction missing, instruction duplication, and instruction error in the service execution process. For attacks on business execution logic, the format, field logic, field threshold and other characteristics of attack packets are normal, and the number of packets is small, which will not be reflected in the network layer traffic characteristics. The existing network layer traffic characteristics analysis and reporting However, the detection method of the present invention can accurately identify the attack behavior, effectively preventing attackers from tampering, injecting and intercepting service execution instructions, thereby causing great damage to the power system.
若为遥控校验、定值修改业务中的一种,则对解析后的应用层报文所属业务的校验逻辑进行检测的具体实现过程包括:If it is one of remote control verification and fixed value modification services, the specific implementation process for detecting the verification logic of the service to which the parsed application layer message belongs includes:
若解析后的应用层报文属于遥控校验业务,则判断公式是否成立,若否,发出告警信号,否则将当前帧流量数据判定为正常流量;其中,OTP1为遥控校验命令的操作类型,OTP2为遥控校验结果的操作类型,COT2表示遥控校验结果的传送原因,H表示数值为16进制;If the parsed application layer packet belongs to the remote control verification service, the judgment formula Whether it is established, if not, send an alarm signal, otherwise, the current frame traffic data will be judged as normal traffic; among them, OTP 1 is the operation type of the remote control verification command, OTP 2 is the operation type of the remote control verification result, and COT 2 represents the remote control verification. The reason for the transmission of the test result, H indicates that the value is in hexadecimal;
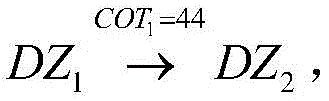
若解析后的应用层报文属于定值修改业务,则判断是否符合执行逻辑若否,发出告警信号,否则将当前帧流量数据判定为正常流量;其中,DZ1表示定值校验指令,COT1表示定值校验指令的传送原因,DZ2表示定值改写指令。该公式表示定值校验指令的传送原因为44时,即定值校验正确,则执行定值改写指令。If the parsed application layer message belongs to the fixed value modification service, it is judged whether it conforms to the execution logic If not, send an alarm signal, otherwise, the current frame traffic data will be judged as normal traffic; among them, DZ 1 represents the fixed value verification command, COT 1 represents the transmission reason of the fixed value verification command, and DZ 2 represents the fixed value rewriting command. This formula indicates that when the transmission reason of the fixed value verification command is 44, that is, the fixed value verification is correct, then the fixed value rewrite command is executed.
本发明通过对电力业务中的校验逻辑进行异常检测,能够识别出针对业务校验过程的攻击行为,例如业务校验正确但未执行或业务校验错误依旧执行。业务校验逻辑异常检测克服了现有检测方法缺乏考虑业务校验过程的异常以及业务校验与执行逻辑关联性的不足,能够准确识别出业务非法执行或未合法执行的情况。The present invention can identify the attack behavior against the service verification process by performing abnormal detection on the verification logic in the power service, for example, the service verification is correct but not executed or the service verification error is still executed. The business verification logic anomaly detection overcomes the deficiencies of the existing detection methods that lack consideration of the business verification process anomalies and the logical correlation between business verification and execution logic, and can accurately identify the illegal execution or non-legal execution of the business.
若为通用历史数据查询、时间同步业务中的一种,则对解析后的应用层报文所属业务的时标逻辑进行检测的具体实现过程包括:If it is one of general historical data query and time synchronization services, the specific implementation process for detecting the time stamp logic of the service to which the parsed application layer message belongs includes:
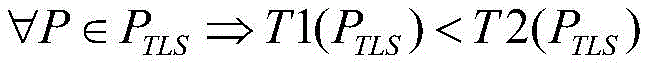
若解析后的应用层报文属于通用历史数据查询业务,则判断公式是否成立,若否,发出告警信号,否则将当前帧流量数据判定为正常流量;其中,PTLS表示通用历史数据查询业务报文,T1(PTLS)表示通用历史数据查询的开始时间,T2(PTLS)表示通用历史数据查询的结束时间;If the parsed application layer packet belongs to the general historical data query service, the judgment formula Whether it is true, if not, send an alarm signal, otherwise, the current frame traffic data is determined as normal traffic; among them, P TLS represents the general historical data query service message, T1 (P TLS ) represents the start time of general historical data query, T2 ( P TLS ) indicates the end time of general historical data query;
若解析后的应用层报文属于时间同步业务,则判断公式是否成立,若否,发出告警信号,否则将当前帧流量数据判定为正常流量;其中,PSJTB表示时间同步业务报文,TB1(PSJTB)表示时间同步业务发送报文的时间,TB2(PSJTB)表示时间同步业务确认报文的时间,Δt表示时间同步命令发送报文与确认报文的最大时间差。If the parsed application layer packet belongs to the time synchronization service, the judgment formula Whether it is true, if not, send an alarm signal, otherwise the current frame traffic data is judged as normal traffic; among them, P SJTB represents the time synchronization service message, TB1 (P SJTB ) represents the time when the time synchronization service sends the message, TB2 (P SJTB ) SJTB ) represents the time of the confirmation message of the time synchronization service, and Δt represents the maximum time difference between the message sent by the time synchronization command and the confirmation message.
本发明通过对智能变电站电力业务中的时标逻辑进行异常检测,能够判别通用历史数据查询业务的查询时间是否正常以及时间同步业务的同步过程是否正常。针对时标逻辑的异常检测技术克服了现有方法仅能根据装置时钟判别异常的局限性,实现了在流量数据应用层报文层面对时标类型攻击的主动监测与防御,提升了智能变电站网络流量数据中数据查询指令与对时指令传输的准确性与可靠性。The invention can judge whether the query time of the general historical data query service is normal and whether the synchronization process of the time synchronization service is normal by performing abnormal detection on the time stamp logic in the power service of the intelligent substation. The anomaly detection technology for time stamping logic overcomes the limitation of existing methods that can only identify anomalies based on the device clock, realizes active monitoring and defense against time stamping attacks at the packet level of the traffic data application layer, and improves the network of smart substations. Accuracy and reliability of data query commands and time-synchronization command transmission in traffic data.
作为一个发明构思,本发明还提供了一种计算机装置,包括存储器、处理器及存储在存储器上的计算机程序;所述处理器执行所述计算机程序,以实现本发明所述方法的步骤。As an inventive concept, the present invention also provides a computer device including a memory, a processor and a computer program stored in the memory; the processor executes the computer program to implement the steps of the method of the present invention.
作为一个发明构思,本发明还提供了一种计算机程序产品,包括计算机程序/指令;其特征在于,该计算机程序/指令被处理器执行时实现本发明所述方法的步骤。As an inventive concept, the present invention also provides a computer program product, comprising a computer program/instruction; characterized in that, when the computer program/instruction is executed by a processor, the steps of the method of the present invention are implemented.
与现有技术相比,本发明所具有的有益效果为:Compared with the prior art, the present invention has the following beneficial effects:
(1)本发明充分考虑了智能变电站网络流量数据在应用层的异常行为,针对应用层报文的字段特征以及业务特征进行异常检测,克服了现有异常检测方法依赖于网络层流量特征指标的局限性。(1) The present invention fully considers the abnormal behavior of the network traffic data of the smart substation in the application layer, and performs abnormal detection according to the field characteristics and service characteristics of the application layer message, which overcomes the problem that the existing abnormal detection method depends on the network layer traffic characteristic index. limitation.
(2)本发明针对智能变电站网络流量数据的应用层报文进行单字段越限检测、多字段耦合逻辑检测、整体字段异常检测,克服了现有异常检测方法仅停留在报文格式校验的不足。(2) The present invention performs single-field out-of-limit detection, multi-field coupling logic detection, and overall field abnormality detection for the application layer message of the network traffic data of the smart substation, and overcomes the problem that the existing abnormality detection method only stays in the message format check. insufficient.
(3)本发明建立了电力稳定控制业务的正常行为模型,依据所建立的业务模型进行业务执行逻辑、业务校验逻辑、业务时标逻辑的检测,实现了智能变电站网络流量业务异常的判别,提升了智能变电站网络流量异常行为检测的准确性。(3) The present invention establishes a normal behavior model of the power stability control business, and detects business execution logic, business verification logic, and business time-scale logic according to the established business model, and realizes the abnormal discrimination of the network traffic business of the intelligent substation, Improves the accuracy of abnormal behavior detection of network traffic in smart substations.
附图说明Description of drawings
图1是本发明实施例中的智能变电站网络流量异常行为检测流程图。FIG. 1 is a flow chart for detecting abnormal behavior of network traffic in a smart substation according to an embodiment of the present invention.
图2是本发明实施例中智能变电站网络流量异常行为监测系统的结构示意图。FIG. 2 is a schematic structural diagram of a system for monitoring abnormal behavior of network traffic in a smart substation according to an embodiment of the present invention.
图3是本发明实施例中单帧报文字段特征的异常检测模块系统单元图。FIG. 3 is a system unit diagram of an anomaly detection module for field characteristics of a single frame message in an embodiment of the present invention.
图4是本发明实施例中多帧报文业务逻辑的异常检测模块系统单元图。FIG. 4 is a system unit diagram of an abnormality detection module of a multi-frame message service logic in an embodiment of the present invention.
具体实施方式Detailed ways
图1为本发明实施例提供的智能变电站网络流量异常行为检测方法的流程图,具体实施步骤如下:1 is a flowchart of a method for detecting abnormal behavior of network traffic in a smart substation provided by an embodiment of the present invention, and the specific implementation steps are as follows:
步骤S1:利用智能变电站交换机镜像端口对网络流量数据进行实时捕获,并提取出应用层报文;Step S1: use the mirror port of the smart substation switch to capture the network traffic data in real time, and extract the application layer message;
步骤S2:根据步骤S1提取出的应用层报文所属协议规定的帧格式对报文进行字段级的解析,获取报文的类型标识、传送原因、功能类型、信息序号字段值;Step S2: perform field-level analysis on the message according to the frame format specified by the protocol to which the application layer message extracted in step S1 belongs, and obtain the type identifier, transmission reason, function type, and information sequence number field value of the message;
步骤S3:针对步骤S2解析后的应用层报文,建立基于字段特征的异常行为检测模型,依据异常检测模型对报文进行单字段越限检测、多字段耦合逻辑检测、整体字段异常检测,如果出现异常,则发出告警信号,否则进入步骤S4;Step S3: For the application layer message parsed in step S2, establish an abnormal behavior detection model based on field features, and perform single-field out-of-limit detection, multi-field coupling logic detection, and overall field abnormality detection on the message according to the abnormality detection model. If an abnormality occurs, an alarm signal is sent, otherwise, go to step S4;
步骤S4:针对步骤S2解析后的应用层报文,建立基于业务特征的正常行为模型,依据正常行为模型对报文进行业务执行逻辑检测、业务校验逻辑检测、业务时标逻辑检测,如果出现异常,则发出告警信号。Step S4: For the application layer message parsed in step S2, establish a normal behavior model based on business characteristics, and perform business execution logic detection, business verification logic detection, and business time stamp logic detection on the message according to the normal behavior model. If abnormal, an alarm signal will be issued.
进一步的,步骤S3包括:Further, step S3 includes:
S3-1:建立报文单字段越限异常检测模型,依据模型对步骤S2解析后的应用层报文进行检测,如果出现异常,则发出告警信号,否则进入步骤S3-2。S3-1: Establish a message single field out-of-limit exception detection model, and detect the application layer message parsed in step S2 according to the model. If an abnormality occurs, an alarm signal is sent, otherwise, step S3-2 is entered.
S3-2:建立报文多字段耦合逻辑异常检测模型,依据模型对步骤S2解析后的应用层报文进行检测,如果出现异常,则发出告警信号,否则进入步骤S3-3。S3-2: Establish a message multi-field coupling logic abnormality detection model, and detect the application layer message parsed in step S2 according to the model. If abnormality occurs, send an alarm signal, otherwise, go to step S3-3.
S3-3:建立报文整体字段异常检测模型,依据模型对步骤S2解析后的应用层报文进行检测,如果出现异常,则发出告警信号,否则进入步骤S4。S3-3: Establish an abnormality detection model for the overall field of the message, and detect the application layer message parsed in step S2 according to the model. If an abnormality occurs, send an alarm signal, otherwise, go to step S4.
进一步的,步骤S3-1包括:Further, step S3-1 includes:
S3-1-1:针对实时捕获的电力稳定控制系统业务流量,建立可变帧报文长度越限异常检测模型,如公式(1)所示,依据模型检测应用层报文长度是否超出协议所规定的最大长度,若是,即违反公式(1),则判定为异常报文,否则进入步骤S3-1-2。S3-1-1: According to the real-time captured business traffic of the power stability control system, establish a variable frame packet length violation detection model, as shown in formula (1), according to the model to detect whether the application layer packet length exceeds the limit of the protocol. If it is the specified maximum length, that is, it violates the formula (1), it is judged as an abnormal message, otherwise, it goes to step S3-1-2.
其中,P为步骤S2解析后的网络流量数据应用层报文,PWK表示电力稳控业务可变帧报文,LEN(PWK)表示报文实际长度,LEN(PWK)max表示电力稳控协议所规定的最大报文长度。Among them, P is the network traffic data application layer message parsed in step S2, P WK represents the variable frame message of the power stability control service, LEN(P WK ) represents the actual length of the message, and LEN(P WK ) max represents the power stability control The maximum packet length specified by the control protocol.
S3-1-2:建立可变帧报文长度一致性异常检测模型,如公式(2)所示,依据模型检测报文理论计算长度与实际长度是否相等,若否,即违反公式(2),则判定为异常报文,否则进入步骤S3-1-3。S3-1-2: Establish a variable frame packet length consistency anomaly detection model, as shown in formula (2), according to the model to detect whether the theoretically calculated length of the packet is equal to the actual length, if not, it violates formula (2) , it is determined as an abnormal message, otherwise, go to step S3-1-3.
其中,THE(PWK)表示报文理论计算长度。Among them, THE(P WK ) represents the theoretical calculation length of the message.
S3-1-3:建立报文类型标识字段值越限异常检测模型,如公式(3)所示,依据模型检测报文类型标识字段值是否越限,若是,即违反公式(3),则判定为异常报文,否则进入步骤S3-1-4。S3-1-3: Establish an abnormality detection model for the out-of-limit value of the message type identifier field. As shown in formula (3), check whether the value of the message type identifier field exceeds the limit according to the model. If yes, it violates formula (3), then It is determined that it is an abnormal message, otherwise it goes to step S3-1-4.
其中,TYP(PWK)表示报文的类型标识字段值。Among them, TYP(P WK ) represents the value of the type identification field of the message.
S3-1-4:建立报文传送原因字段值越限异常检测模型,如公式(4)所示,依据模型检测报文传送原因字段值是否越限,若是,即违反公式(4),则判定为异常报文,否则进入步骤S3-1-4。S3-1-4: Establish an abnormality detection model for the over-limit value of the message transmission reason field, as shown in formula (4), according to the model to detect whether the value of the message transmission reason field exceeds the limit, if yes, it violates the formula (4), then It is determined that it is an abnormal message, otherwise it goes to step S3-1-4.
其中,COT(PWK)表示报文的传送原因字段值。Wherein, COT(P WK ) represents the transmission reason field value of the packet.
S3-1-5:建立固定帧报文长度越限异常检测模型,如公式(5)所示,依据模型检测固定帧报文长度是否为5个字节,若否,即违反公式(5),则判定为异常报文,否则进入步骤S3-2。S3-1-5: Establish a fixed frame message length violation detection model, as shown in formula (5), according to the model to detect whether the fixed frame message length is 5 bytes, if not, it violates formula (5) , it is determined as an abnormal message, otherwise, it goes to step S3-2.
其中,PWK_G表示电力稳控业务固定帧报文,LEN(PWK_G)表示固定帧报文长度。Wherein, P WK_G represents the fixed frame message of the power stabilization control service, and LEN(P WK_G ) represents the length of the fixed frame message.
进一步的,步骤S3-2包括:Further, step S3-2 includes:
S3-2-1:针对实时捕获的电力稳定控制系统业务流量,建立报文控制域功能码与帧计数有效位耦合逻辑异常检测模型,如公式(6)所示,依据模型检测应用层报文控制域功能码与帧计数有效位逻辑是否正常,若否,即违反公式(6),则判定为异常报文,否则进入步骤S3-2-2。S3-2-1: For the real-time captured business traffic of the power stability control system, establish a logical anomaly detection model for the coupling of the function code of the message control domain and the effective bit of the frame count, as shown in formula (6), and detect the application layer message according to the model. Check whether the logic of the function code of the control domain and the valid bit of the frame count is normal, if not, that is, violating the formula (6), it is judged as an abnormal message, otherwise, go to step S3-2-2.
其中,FUN(PWK)表示报文控制域功能码数值,FCV(PWK)表示报文帧计数有效位数值。Among them, FUN(P WK ) represents the function code value of the message control field, and FCV(P WK ) represents the valid bit value of the message frame count.
S3-2-2:建立报文被测量品质描述词标志位耦合逻辑异常检测模型,如公式(7)所示,依据模型检测应用层报文被测量品质描述词标志位耦合逻辑是否正常,若否,即违反公式(7),则判定为异常报文,否则进入步骤S3-3。S3-2-2: Establish a detection model for the abnormality detection of the flag bit coupling logic of the measured quality descriptor of the packet. As shown in formula (7), check whether the coupling logic of the measured quality descriptor flag bit of the application layer packet is normal according to the model. If no, that is, it violates the formula (7), it is determined as an abnormal message, otherwise, it goes to step S3-3.
其中,QU(PWK)表示报文的被测量品质描述词,OV表示品质描述词的溢出标志,ER表示品质描述词的有效标志。Among them, QU(P WK ) represents the measured quality descriptor of the packet, OV represents the overflow flag of the quality descriptor, and ER represents the effective flag of the quality descriptor.
进一步的,步骤S3-3包括:Further, step S3-3 includes:
S3-3:针对实时捕获的电力稳定控制系统业务流量,建立报文校验和异常检测模型,如公式(8)所示,依据模型检测应用层报文的整体校验和是否正确,若否,即违反公式(8),则发出告警信号,否则进入步骤S4。S3-3: According to the real-time captured business traffic of the power stability control system, establish a packet checksum abnormality detection model, as shown in formula (8), according to the model to detect whether the overall checksum of the application layer packet is correct, if not , that is, if formula (8) is violated, an alarm signal is issued, otherwise, it goes to step S4.
其中,THE_V(PWK)表示报文理论校验和,为启动字符至校验和字段前的数据单字节算术累加和的低字节,REA_V(PWK)表示报文实际校验和,为报文最后一个字节。Among them, THE_V(P WK ) represents the theoretical checksum of the message, which is the low byte of the single-byte arithmetic cumulative sum of the data before the start character to the checksum field, REA_V(P WK ) represents the actual checksum of the message, is the last byte of the message.
进一步的,步骤S4包括:Further, step S4 includes:
S4-1:根据步骤S2解析后的应用层报文的类型标识、传送原因、功能类型、信息序号字段判断报文所属具体业务,如果为文件传输、总召唤、测试模式、监视方向闭锁、遥控执行、遥调执行、扰动数据传输业务中的一种,则进入步骤S4-2;如果为遥控校验、定值修改业务则进入步骤S4-3;如果为通用历史数据查询、时间同步业务则进入步骤S4-4。S4-1: Determine the specific service to which the message belongs according to the type identifier, transmission reason, function type, and information sequence number fields of the application layer message parsed in step S2, if it is file transmission, general call, test mode, monitoring direction blocking, remote control One of execution, remote adjustment execution, and disturbance data transmission services, then enter step S4-2; if it is remote control verification, fixed value modification services, then enter step S4-3; if it is general historical data query, time synchronization services, then Go to step S4-4.
S4-2:建立业务执行逻辑正常行为模型,依据模型对应用层报文所属业务的执行逻辑进行检测,如果出现异常,则发出告警信号,否则将该帧流量数据判定为正常流量。S4-2: Establish a normal behavior model of service execution logic, and detect the execution logic of the service to which the application layer message belongs according to the model. If an abnormality occurs, an alarm signal is sent, otherwise the frame traffic data is determined as normal traffic.
S4-3:建立业务校验逻辑正常行为模型,依据模型对应用层报文所属业务的校验逻辑进行检测,如果出现异常,则发出告警信号,否则将该帧流量数据判定为正常流量。S4-3: Establish a normal behavior model of service verification logic, and detect the verification logic of the service to which the application layer packet belongs according to the model. If an abnormality occurs, an alarm signal is sent, otherwise the frame traffic data is determined as normal traffic.
S4-4:建立业务时标逻辑正常行为模型,依据模型对应用层报文所属业务的时标逻辑进行检测,如果出现异常,则发出告警信号,否则将该帧流量数据判定为正常流量。S4-4: Establish a normal behavior model of the service time stamping logic, and detect the time stamping logic of the service to which the application layer message belongs according to the model. If an abnormality occurs, an alarm signal is sent, otherwise the frame traffic data is determined as normal traffic.
进一步的,步骤S4-2包括:Further, step S4-2 includes:
S4-2-1:如果报文属于文件传输业务,则进入步骤S4-2-2;如果报文属于总召唤业务,则进入步骤S4-2-3;如果报文属于测试模式业务,则进入步骤S4-2-4;如果报文属于监视方向闭锁业务,则进入步骤S4-2-5;如果报文属于遥控执行业务,则进入步骤S4-2-6;如果报文属于遥调执行业务,则进入步骤S4-2-7;如果报文属于扰动数据传输业务,则进入步骤S4-2-8。S4-2-1: if the message belongs to the file transfer service, go to step S4-2-2; if the message belongs to the general call service, go to step S4-2-3; if the message belongs to the test mode service, go to step S4-2-3 Step S4-2-4; if the message belongs to the monitoring direction blocking service, proceed to step S4-2-5; if the message belongs to the remote control execution service, then proceed to step S4-2-6; if the message belongs to the remote adjustment execution service , then go to step S4-2-7; if the message belongs to the disturbed data transmission service, go to step S4-2-8.
S4-2-2:建立文件传输业务执行逻辑的正常行为模型,如公式(9)所示。文件传输业务的正常执行逻辑为召唤目录、文件目录响应、选择文件、文件准备就绪、召唤文件、节准备就绪、召唤节、段数据上送、最后的段发送确认、节确认、文件确认,如果出现逻辑异常,即违反公式(9),则发出告警信号,否则将该帧流量数据判定为正常流量。S4-2-2: Establish a normal behavior model of the file transfer service execution logic, as shown in formula (9). The normal execution logic of the file transfer service is calling directory, file directory response, file selection, file ready, calling file, section ready, calling section, segment data upload, final segment sending confirmation, section confirmation, file confirmation, if If a logic abnormality occurs, that is, a violation of formula (9), an alarm signal is sent, otherwise, the frame traffic data is determined as normal traffic.
其中,WJ1为召唤目录指令,WJ2为文件目录响应指令,WJ3为选择文件指令,WJ4为文件准备就绪指令,WJ5为召唤文件指令,WJ6为节准备就绪指令,WJ7为召唤节指令,WJ8为段数据上送指令,WJ9为最后的段发送确认指令,WJ10为节确认指令,WJ11为文件确认指令。Among them, WJ 1 is a call directory command, WJ 2 is a file directory response command, WJ 3 is a file selection command, WJ 4 is a file ready command, WJ 5 is a call file command, WJ 6 is a section ready command, and WJ 7 is a command Calling a section command, WJ 8 is the segment data upload command, WJ 9 is the last segment sending confirmation command, WJ 10 is the section confirmation command, and WJ 11 is the file confirmation command.
S4-2-3:建立总召唤业务执行逻辑的正常行为模型,如公式(10)所示。总召唤业务的正常执行逻辑为主站启动总召唤、子站上送信息、总召唤结束,如果出现逻辑异常,即违反公式(10),则发出告警信号,否则将该帧流量数据判定为正常流量。S4-2-3: Establish a normal behavior model of the general call service execution logic, as shown in formula (10). The normal execution logic of the general call service starts the general call for the main station, sends information to the sub station, and ends the general call. If there is a logic abnormality, that is, violating the formula (10), an alarm signal is sent, otherwise the frame of traffic data is judged as normal. flow.
ZZ1→ZZ2→ZZ3 (10)ZZ 1 → ZZ 2 → ZZ 3 (10)
其中,ZZ1为主站启动总召唤指令,ZZ2为子站上送信息指令,ZZ3为总召唤结束指令。Among them, ZZ 1 starts the general call command for the master station, ZZ 2 is the slave station sending information command, and ZZ 3 is the general call end command.
S4-2-4:建立测试模式业务执行逻辑的正常行为模型,如公式(11)所示。测试模式业务的正常执行逻辑为测试激活、测试结束,如果出现逻辑异常,即违反公式(11),则发出告警信号,否则将该帧流量数据判定为正常流量。S4-2-4: Establish a normal behavior model of the business execution logic in the test mode, as shown in formula (11). The normal execution logic of the test mode service is test activation and test end. If there is a logic abnormality, that is, formula (11) is violated, an alarm signal is sent, otherwise the frame traffic data is determined as normal traffic.
CS1→CS2→CS1→CS2 (11)CS 1 → CS 2 → CS 1 → CS 2 (11)
其中,CS1为测试激活指令,CS2为测试结束指令。Among them, CS 1 is a test activation command, and CS 2 is a test end command.
S4-2-5:建立监视方向闭锁业务执行逻辑的正常行为模型,如公式(12)所示。监视方向闭锁业务的正常执行逻辑为监视方向闭锁激活、监视方向闭锁停止激活,如果出现逻辑异常,即违反公式(12),则发出告警信号,否则将该帧流量数据判定为正常流量。S4-2-5: Establish a normal behavior model of the monitoring direction blocking business execution logic, as shown in formula (12). The normal execution logic of monitoring direction blocking service is monitoring direction blocking activation and monitoring direction blocking deactivation. If a logic abnormality occurs, that is, formula (12) is violated, an alarm signal is sent, otherwise the frame traffic data is determined as normal traffic.
BS1→BS2→BS1→BS2 (12)BS1 → BS2→ BS1 → BS2 ( 12 )
其中,BS1为监视方向闭锁激活指令,BS2为监视方向闭锁停止激活指令。Among them, BS 1 is the monitoring direction blocking activation command, and BS 2 is the monitoring direction blocking stop activation command.
S4-2-6:建立遥控业务执行逻辑的正常行为模型,如公式(13)所示。遥控业务的正常执行逻辑为遥控设置、遥控设置返校、遥控执行、遥控执行返校,如果出现逻辑异常,即违反公式(13),则发出告警信号,否则将该帧流量数据判定为正常流量。S4-2-6: Establish a normal behavior model of the remote control service execution logic, as shown in formula (13). The normal execution logic of the remote control service is remote control setting, remote control setting return to school, remote control execution, and remote control execution return to school. If there is a logic abnormality, that is, violating formula (13), an alarm signal will be sent, otherwise the frame of traffic data will be judged as normal traffic. .
YK1→YK2→YK3→YK4 (13)YK 1 → YK 2 → YK 3 → YK 4 (13)
其中,YK1为遥控设置指令,YK2为遥控设置返校指令,YK3为遥控执行指令,YK4为遥控执行返校指令。Among them, YK 1 is the remote control setting instruction, YK 2 is the remote control setting return-to-school instruction, YK 3 is the remote control execution instruction, and YK 4 is the remote control execution return-to-school instruction.
S4-2-7:建立遥调业务执行逻辑的正常行为模型,如公式(14)所示。遥调业务的正常执行逻辑为遥调设置、遥调设置返校、遥调执行、遥调执行返校,如果出现逻辑异常,即违反公式(14),则发出告警信号,否则将该帧流量数据判定为正常流量。S4-2-7: Establish a normal behavior model of the remote adjustment service execution logic, as shown in formula (14). The normal execution logic of the remote adjustment service is remote adjustment setting, remote adjustment setting return to calibration, remote adjustment execution, and remote adjustment execution return to calibration. The data is judged to be normal flow.
YT1→YT2→YT3→YT4 (14)YT 1 →YT 2 →YT 3 →YT 4 (14)
其中,YT1为遥调设置指令,YT2为遥调设置返校指令,YT3为遥调执行指令,YT4为遥调执行返校指令。Among them, YT 1 is the remote adjustment setting instruction, YT 2 is the remote adjustment setting return-to-calibration instruction, YT 3 is the remote adjustment execution instruction, and YT 4 is the remote adjustment execution return-to-calibration instruction.
S4-2-8:建立扰动数据传输业务执行逻辑的正常行为模型,如公式(15)所示。扰动数据传输业务的正常执行逻辑为扰动数据传输准备、传输通道准备、带标志的状态变位传输准备、带标志的状态变位传输、传输扰动值、传输结束,如果出现逻辑异常,即违反公式(15),则发出告警信号,否则将该帧流量数据判定为正常流量。S4-2-8: Establish a normal behavior model for disturbing the execution logic of the data transmission service, as shown in formula (15). The normal execution logic of the perturbed data transmission service is preparation for perturbed data transmission, transmission channel preparation, preparation for state change transmission with flags, state change transmission with flags, transmission of disturbance value, and end of transmission. If a logic abnormality occurs, the formula is violated. (15), send an alarm signal, otherwise the frame traffic data is judged as normal traffic.
RD1→RD2→RD3→RD4→RD5→RD6 (15)RD 1 →RD 2 →RD 3 →RD 4 →RD 5 →RD 6 (15)
其中,RD1为扰动数据传输准备指令,RD2为传输通道准备指令,RD3为带标志的状态变位传输准备指令,RD4为带标志的状态变位传输指令,RD5为传输扰动值指令,RD6为传输结束指令。Among them, RD 1 is the preparation command for disturbed data transmission, RD 2 is the preparation command for the transmission channel, RD 3 is the command for preparing state change transmission with flag, RD 4 is the command for state change transmission with flag, RD 5 is the transmission disturbance value command, RD 6 is the transfer end command.
进一步的,步骤S4-3包括:Further, step S4-3 includes:
S4-3-1:如果报文属于遥控校验业务,则进入步骤S4-3-2;如果报文属于定值修改业务,则进入步骤S4-3-3。S4-3-1: If the message belongs to the remote control verification service, go to step S4-3-2; if the message belongs to the fixed value modification service, go to step S4-3-3.
S4-3-2:建立遥控业务校验逻辑的正常行为模型,如公式(16)所示。遥控校验业务由遥控校验命令和遥控校验结果两帧报文组成,遥控校验结果的操作类型(01:分/02:合)由遥控校验命令以及遥控校验结果的传送原因字段决定,如果出现逻辑异常,即违反式(16),则发出告警信号,否则将该帧流量数据判定为正常流量。S4-3-2: Establish a normal behavior model of the remote control service verification logic, as shown in formula (16). The remote control verification service consists of two frames of remote control verification command and remote control verification result. The operation type (01:min/02:combined) of the remote control verification result is composed of the remote control verification command and the transmission reason field of the remote control verification result. It is decided that if there is a logical abnormality, that is, the formula (16) is violated, an alarm signal is sent, otherwise the frame traffic data is judged as normal traffic.
其中,OTP1为遥控校验命令的操作类型,OTP2为遥控校验结果的操作类型,COT2表示遥控校验结果的传送原因,H表示数值为16进制。Among them, OTP 1 is the operation type of the remote control verification command, OTP 2 is the operation type of the remote control verification result, COT 2 represents the transmission reason of the remote control verification result, and H represents the value in hexadecimal.
S4-3-3:建立定值修改业务校验逻辑的正常行为模型,如公式(17)所示。定值修改业务中定值校验指令正确才能执行定值改写指令,如果定值校验指令错误依然执行定值改写指令,即违反式(17),则判定为异常报文,发出告警信号,否则将该帧流量数据判定为正常流量。S4-3-3: Establish a normal behavior model of the fixed value modification business verification logic, as shown in formula (17). In the fixed value modification business, the fixed value rewriting command can only be executed if the fixed value verification command is correct. If the fixed value verification command is wrong and the fixed value rewriting command is still executed, that is, it violates the formula (17), it will be judged as an abnormal message, and an alarm signal will be issued. Otherwise, the frame traffic data is determined as normal traffic.
其中,DZ1表示定值校验指令,COT1表示定值校验指令的传送原因,DZ2表示定值改写指令。该公式表示定值校验指令的传送原因为44时,即定值校验正确,则执行定值改写指令。Among them, DZ 1 represents the fixed value verification command, COT 1 represents the transmission reason of the fixed value verification command, and DZ 2 represents the fixed value rewriting command. This formula indicates that when the transmission reason of the fixed value verification command is 44, that is, the fixed value verification is correct, then the fixed value rewrite command is executed.
进一步的,步骤S4-4包括:Further, step S4-4 includes:
S4-4-1:如果报文属于通用历史数据查询业务,则进入步骤S4-4-2;如果报文属于时间同步业务,则进入步骤S4-4-3。S4-4-1: If the message belongs to the general historical data query service, proceed to step S4-4-2; if the message belongs to the time synchronization service, proceed to step S4-4-3.
S4-4-2:建立通用历史数据查询业务时标逻辑的正常行为模型,如公式(18)所示。通用历史数据查询的开始时间一定小于结束时间,如果违反式(18),则判定为异常报文,发出告警信号,否则将该帧流量数据判定为正常流量。S4-4-2: Establish a normal behavior model of the general historical data query business time stamp logic, as shown in formula (18). The start time of the general historical data query must be less than the end time. If it violates the formula (18), it will be judged as an abnormal packet and an alarm signal will be sent, otherwise the frame traffic data will be judged as normal traffic.
其中,PTLS表示通用历史数据查询业务报文,T1(PTLS)表示通用历史数据查询的开始时间,T2(PTLS)表示通用历史数据查询的结束时间。Among them, P TLS represents the general historical data query service message, T1 (P TLS ) represents the start time of the general historical data query, and T2 (P TLS ) represents the end time of the general historical data query.
S4-4-3:建立时间同步业务时标逻辑的正常行为模型,如公式(19)所示,对时间同步命令的确认帧时间进行检测,如果违反公式(19),则判定为异常报文,发出告警信号,否则将该帧流量数据判定为正常流量。S4-4-3: Establish a normal behavior model of the time-stamping logic of the time synchronization service, as shown in formula (19), detect the confirmation frame time of the time synchronization command, and if it violates formula (19), it is determined as an abnormal message , send an alarm signal, otherwise the frame traffic data is judged as normal traffic.
其中,PSJTB表示时间同步业务报文,TB1(PSJTB)表示时间同步业务发送报文的时间,TB2(PSJTB)表示时间同步业务确认报文的时间,Δt表示时间同步命令发送报文与确认报文的最大时间差。Among them, P SJTB represents the time synchronization service message, TB1 (P SJTB ) represents the time when the time synchronization service sends the message, TB2 (P SJTB ) represents the time of the time synchronization service acknowledgment message, Δt represents the time synchronization command to send the message and the The maximum time difference for acknowledging packets.
本发明依托海量智能变电站网络流量数据,通过对流量数据的应用层报文进行字段级解析,获取报文所表示的具体业务。其次根据报文的字段特征对报文进行进行单字段越限检测、多字段耦合逻辑检测、整体字段异常检测。最后根据报文所属业务特征建立正常行为模型,并基于正常行为模型进行异常检测,实现了智能变电站网络流量异常行为的准确监测,确保智能变电站通信过程中信息的安全、可靠传输。The invention relies on the massive intelligent substation network flow data, and obtains the specific business represented by the message by performing field-level analysis on the application layer message of the flow data. Secondly, according to the field characteristics of the message, single-field out-of-limit detection, multi-field coupling logic detection, and overall field anomaly detection are performed on the message. Finally, a normal behavior model is established according to the service characteristics of the packet, and anomaly detection is carried out based on the normal behavior model, which realizes the accurate monitoring of abnormal behavior of network traffic in smart substations, and ensures the safe and reliable transmission of information in the communication process of smart substations.
图2为本发明实施例提供的智能变电站网络流量异常行为监测系统的结构示意图,该系统适用于执行本发明任意实施例提供的方法,包括:流量数据获取模块100,应用层报文解析模块200,单帧报文字段特征异常检测模块300,多帧报文业务逻辑异常检测模块400。本发明的所有模块均设置于处理器内。2 is a schematic structural diagram of a system for monitoring abnormal behavior of network traffic in a smart substation provided by an embodiment of the present invention. The system is suitable for executing the method provided by any embodiment of the present invention, and includes: a traffic
所述的流量数据获取模块100,用于镜像采集流量数据,并提取出每帧流量数据的应用层报文。The traffic
所述的应用层报文解析模块200,用于对提取出的应用层报文按照协议规定的帧格式进行逐个字段解析,获取报文表示的具体业务。The application layer
所述的单帧报文字段特征异常检测模块300,用于对单帧报文在字段特征层面进行异常检测。The field feature
所述的多帧报文业务逻辑异常检测模块400,用于对同一业务的报文进行帧与帧之间的逻辑异常检测。The multi-frame message service logic
所述流量数据获取模块100输出端与所述应用层报文解析模块200输入端相连,用于输入所提取的应用层报文。The output end of the traffic
所述应用层报文解析模块200的输出端与单帧报文字段特征异常检测模块300输入端相连,用于输入该帧流量数据的应用层报文解析结果。The output end of the application layer
所述单帧报文字段特征的异常检测模块300的输出端与所述的多帧报文业务逻辑异常检测模块400的输入端相连,用于输入该帧流量数据的应用层报文解析结果。The output end of the
如图3,进一步的,所述单帧报文字段特征异常检测模块300包括:数据获取单元301,第一检测单元302,第二检测单元303,第三检测单元304。As shown in FIG. 3 , further, the single-frame message field feature
所述数据获取单元301的输出端与所述第一检测单元302输入端相连,用于输入应用层报文及其解析结果。The output end of the
所述第一检测单元302的输出端与第二检测单元303的输入端相连,所述第二检测单元303的输出端与第三检测单元304的输入端相连。The output terminal of the
在一个实施例中,数据获取单元301,读取电力稳控业务流量数据的应用层报文及其解析结果,该单元将所读取信息传递给第一检测单元302、第二检测单元303、第三检测单元304。In one embodiment, the
所述第一检测单元302,用于建立报文单字段越限异常检测模型,依据模型对应用层报文进行检测,如果出现异常,则发出告警信号。The
在一个实施例中,检测应用层报文长度是否超出协议所规定的最大长度、检测报文理论计算长度与实际长度是否相等、检测报文类型标识字段值是否越限、检测报文传送原因字段值是否越限、检测应用层报文固定帧长度是否为5个字节,如果出现异常,则发出告警信号,该单元将异常结果作为单帧报文字段特征异常检测模块300的输出端。In one embodiment, it is detected whether the length of the application layer message exceeds the maximum length specified by the protocol, whether the theoretically calculated length of the message is equal to the actual length, whether the value of the message type identifier field exceeds the limit, and the field of the message transmission reason is detected. Check whether the value exceeds the limit, and check whether the fixed frame length of the application layer message is 5 bytes. If there is an abnormality, an alarm signal is sent.
所述第二检测单元303,用于建立报文多字段耦合逻辑异常检测模型,依据模型对应用层报文进行检测,如果出现异常,则发出告警信号。The
在一个实施例中,检测应用层报文控制域功能码与帧计数有效位逻辑是否正常、检测应用层报文被测量品质描述词标志位耦合逻辑是否正常,如果出现异常,则发出告警信号,该单元将异常结果作为单帧报文字段特征的异常检测模块300的输出端。In one embodiment, it is detected whether the logic of the function code of the control field of the application layer message and the valid bit of the frame count are normal, and whether the coupling logic of the flag bit of the measured quality descriptor of the application layer message is normal, and if there is an abnormality, an alarm signal is sent out, This unit takes the abnormal result as the output end of the
所述第三检测单元304,用于建立报文整体字段异常检测模型,依据模型对应用层报文进行检测,如果出现异常,则发出告警信号。The
在一个实施例中,检测应用层报文的整体校验和是否正确,如果出现异常,则发出告警信号,该单元将异常结果作为单帧报文字段特征的异常检测模块300的输出端。In one embodiment, it detects whether the overall checksum of the application layer message is correct, and if an abnormality occurs, an alarm signal is sent.
如图4,进一步的,所述多帧报文业务逻辑异常检测模块400包括:数据获取单元401,第一检测单元402,第二检测单元403,第三检测单元404。As shown in FIG. 4 , further, the multi-frame message service logic
所述数据获取单元401的输出端与所述第一检测单元402输入端相连,用于输入应用层报文及其所属具体业务。The output end of the
所述第一检测单元402的输出端与第二检测单元403的输入端相连,所述第二检测单元403的输出端与第三检测单元404的输入端相连。The output terminal of the
在一个实施例中,数据获取单元401,获取应用层报文及其所属具体业务,该单元将读取信息传递给第一检测单元402、第二检测单元403、第三检测单元404。In one embodiment, the
所述第一检测单元402,用于检测业务执行逻辑异常。The
在一个实施例中,建立业务执行逻辑正常行为模型,依据模型对应用层报文所属业务的执行逻辑进行检测,如果出现异常,则发出告警信号,该单元将异常结果作为多帧报文业务逻辑异常检测模块400的输出端。In one embodiment, a normal behavior model of service execution logic is established, and the execution logic of the service to which the application layer message belongs is detected according to the model, if an abnormality occurs, an alarm signal is sent, and the unit takes the abnormal result as the multi-frame message service logic The output of the
所述第二检测单元403,用于检测业务校验逻辑异常。The
在一个实施例中,建立业务校验逻辑正常行为模型,依据模型对应用层报文所属业务的校验逻辑进行检测,如果出现异常,则发出告警信号,该单元将异常结果作为多帧报文业务逻辑异常检测模块400的输出端。In one embodiment, a normal behavior model of the service verification logic is established, and the verification logic of the service to which the application layer message belongs is detected according to the model. If an abnormality occurs, an alarm signal is sent, and the unit takes the abnormal result as a multi-frame message The output end of the business logic
所述第三检测单元404,用于检测业务时标逻辑异常。The
在一个实施例中,建立业务时标逻辑正常行为模型,依据模型对应用层报文所属业务的时标逻辑进行检测,如果出现异常,则发出告警信号,该单元将异常结果作为多帧报文业务逻辑异常检测模块400的输出端。In one embodiment, a normal behavior model of service time stamping logic is established, and according to the model, the time stamping logic of the service to which the application layer message belongs is detected, if an abnormality occurs, an alarm signal is sent, and the unit treats the abnormal result as a multi-frame message The output end of the business logic
Claims (10)
Priority Applications (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN202111670704.6A CN114362368B (en) | 2021-12-31 | 2021-12-31 | Intelligent substation network flow abnormal behavior monitoring method and system |
Applications Claiming Priority (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN202111670704.6A CN114362368B (en) | 2021-12-31 | 2021-12-31 | Intelligent substation network flow abnormal behavior monitoring method and system |
Publications (2)
| Publication Number | Publication Date |
|---|---|
| CN114362368A true CN114362368A (en) | 2022-04-15 |
| CN114362368B CN114362368B (en) | 2024-04-16 |
Family
ID=81106010
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| CN202111670704.6A Active CN114362368B (en) | 2021-12-31 | 2021-12-31 | Intelligent substation network flow abnormal behavior monitoring method and system |
Country Status (1)
| Country | Link |
|---|---|
| CN (1) | CN114362368B (en) |
Cited By (6)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN115278684A (en) * | 2022-07-26 | 2022-11-01 | 上海欣诺通信技术股份有限公司 | 5G signaling attack monitoring method and device based on DPI technology |
| CN115694931A (en) * | 2022-12-27 | 2023-02-03 | 中国南方电网有限责任公司 | Intrusion prevention and detection method and system for remote operation and maintenance of relay protection |
| CN117118709A (en) * | 2023-08-25 | 2023-11-24 | 国网山东省电力公司泰安供电公司 | An abnormal flow early warning method, system, equipment and medium for power systems |
| CN117978551A (en) * | 2024-03-29 | 2024-05-03 | 南京鼎研电力科技有限公司 | Interactive abnormal behavior analysis method for substation monitoring network |
| CN119071234A (en) * | 2024-11-05 | 2024-12-03 | 成都流体动力创新中心 | A method for processing entity activity data, computer equipment and storage medium |
| CN119558817A (en) * | 2024-10-25 | 2025-03-04 | 中国长江电力股份有限公司 | A method and system for analyzing abnormalities in automatic startup process of a hydropower station |
Citations (7)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US5097469A (en) * | 1989-05-19 | 1992-03-17 | Concord Communications, Inc. | Passive monitor for broadcast communication network |
| CN103124105A (en) * | 2012-03-27 | 2013-05-29 | 湖南大学 | Wireless intelligent sensor network system for monitoring states of intelligent substation devices |
| KR101375813B1 (en) * | 2012-09-13 | 2014-03-20 | 한국전력공사 | Active security sensing device and method for intrusion detection and audit of digital substation |
| WO2014090025A1 (en) * | 2012-12-11 | 2014-06-19 | 国网上海市电力公司 | On-line and off-line integrated analysis and testing method for smart substation |
| CN110401624A (en) * | 2018-04-25 | 2019-11-01 | 全球能源互联网研究院有限公司 | The detection method and system of source net G system mutual message exception |
| WO2021063068A1 (en) * | 2019-09-30 | 2021-04-08 | 全球能源互联网研究院有限公司 | Operation and maintenance control and operation and maintenance analysis method and apparatus, system, and storage medium |
| CN113420099A (en) * | 2021-07-06 | 2021-09-21 | 广州方硅信息技术有限公司 | Buried point data access control method and device, computer equipment and storage medium |
-
2021
- 2021-12-31 CN CN202111670704.6A patent/CN114362368B/en active Active
Patent Citations (7)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US5097469A (en) * | 1989-05-19 | 1992-03-17 | Concord Communications, Inc. | Passive monitor for broadcast communication network |
| CN103124105A (en) * | 2012-03-27 | 2013-05-29 | 湖南大学 | Wireless intelligent sensor network system for monitoring states of intelligent substation devices |
| KR101375813B1 (en) * | 2012-09-13 | 2014-03-20 | 한국전력공사 | Active security sensing device and method for intrusion detection and audit of digital substation |
| WO2014090025A1 (en) * | 2012-12-11 | 2014-06-19 | 国网上海市电力公司 | On-line and off-line integrated analysis and testing method for smart substation |
| CN110401624A (en) * | 2018-04-25 | 2019-11-01 | 全球能源互联网研究院有限公司 | The detection method and system of source net G system mutual message exception |
| WO2021063068A1 (en) * | 2019-09-30 | 2021-04-08 | 全球能源互联网研究院有限公司 | Operation and maintenance control and operation and maintenance analysis method and apparatus, system, and storage medium |
| CN113420099A (en) * | 2021-07-06 | 2021-09-21 | 广州方硅信息技术有限公司 | Buried point data access control method and device, computer equipment and storage medium |
Cited By (10)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN115278684A (en) * | 2022-07-26 | 2022-11-01 | 上海欣诺通信技术股份有限公司 | 5G signaling attack monitoring method and device based on DPI technology |
| CN115278684B (en) * | 2022-07-26 | 2024-02-13 | 上海欣诺通信技术股份有限公司 | 5G signaling attack monitoring method and device based on DPI technology |
| CN115694931A (en) * | 2022-12-27 | 2023-02-03 | 中国南方电网有限责任公司 | Intrusion prevention and detection method and system for remote operation and maintenance of relay protection |
| CN117118709A (en) * | 2023-08-25 | 2023-11-24 | 国网山东省电力公司泰安供电公司 | An abnormal flow early warning method, system, equipment and medium for power systems |
| CN117978551A (en) * | 2024-03-29 | 2024-05-03 | 南京鼎研电力科技有限公司 | Interactive abnormal behavior analysis method for substation monitoring network |
| CN117978551B (en) * | 2024-03-29 | 2024-06-04 | 南京鼎研电力科技有限公司 | Interaction abnormal behavior analysis method for transformer substation monitoring network |
| CN119558817A (en) * | 2024-10-25 | 2025-03-04 | 中国长江电力股份有限公司 | A method and system for analyzing abnormalities in automatic startup process of a hydropower station |
| CN119558817B (en) * | 2024-10-25 | 2025-10-17 | 中国长江电力股份有限公司 | Analysis method and system for abnormal automatic startup flow of hydropower station |
| CN119071234A (en) * | 2024-11-05 | 2024-12-03 | 成都流体动力创新中心 | A method for processing entity activity data, computer equipment and storage medium |
| CN119071234B (en) * | 2024-11-05 | 2025-01-24 | 成都流体动力创新中心 | Entity activity data processing method, computer equipment and storage medium |
Also Published As
| Publication number | Publication date |
|---|---|
| CN114362368B (en) | 2024-04-16 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| CN114362368A (en) | Method and system for monitoring abnormal behavior of network traffic in smart substation | |
| CN114124478B (en) | Method and system for abnormal detection of industrial control flow in electric power system | |
| CN114825607B (en) | Attack behavior monitoring method and device for relay protection information processing system | |
| CN106817363B (en) | Intelligent ammeter abnormity detection method based on neural network | |
| CN102593733B (en) | Debugging method for transformer substation equipment | |
| CN109462590B (en) | Unknown protocol reverse analysis method based on fuzzy test | |
| CN105429977A (en) | Method for monitoring abnormal flows of deep packet detection equipment based on information entropy measurement | |
| CN101119241A (en) | Condition detection based protocol abnormity detecting method and system | |
| CN114938287B (en) | Power network abnormal behavior detection method and device integrating service characteristics | |
| CN111209339B (en) | Block synchronization method, device, computer and storage medium | |
| CN112149120A (en) | Transparent transmission type double-channel electric power Internet of things safety detection system | |
| CN110336698A (en) | A kind of failure data analyzing method, server and storage medium | |
| CN111478893B (en) | Detection method for slow HTTP attack | |
| CN104882964B (en) | A Method of Checking and Correcting Substation Information Based on Information Redundancy | |
| CN102904721A (en) | Signature and authentication method for information safety control of intelligent substations and device thereof | |
| CN120729910A (en) | Abnormality monitoring method, device and system for edge devices | |
| CN106789967B (en) | A kind of acquisition of multi-source network security incident and synchronous method | |
| CN120180419A (en) | An X86 industrial control motherboard identity authentication system based on multimodal fusion | |
| Hoeve | Detecting intrusions in encrypted control traffic | |
| CN113329064A (en) | Communication method of Internet of things interaction protocol based on water conservancy data acquisition and control | |
| CN105099810A (en) | Communication test method and system for sampling value interface | |
| CN117560196A (en) | A smart substation secondary system testing system and method | |
| CN113645241B (en) | Intrusion detection method, device and equipment for industrial control proprietary protocol | |
| CN115712922A (en) | Internet of things electronic information processing system and method | |
| CN120825531B (en) | Carbon data transmission method, device, computer equipment and readable storage medium |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| PB01 | Publication | ||
| PB01 | Publication | ||
| SE01 | Entry into force of request for substantive examination | ||
| SE01 | Entry into force of request for substantive examination | ||
| GR01 | Patent grant | ||
| GR01 | Patent grant |