CN114254372B - Data encryption processing method and system and electronic equipment - Google Patents
Data encryption processing method and system and electronic equipment Download PDFInfo
- Publication number
- CN114254372B CN114254372B CN202210185245.0A CN202210185245A CN114254372B CN 114254372 B CN114254372 B CN 114254372B CN 202210185245 A CN202210185245 A CN 202210185245A CN 114254372 B CN114254372 B CN 114254372B
- Authority
- CN
- China
- Prior art keywords
- data
- data blocks
- round function
- determining
- function operation
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Active
Links
Images
Classifications
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F21/60—Protecting data
- G06F21/602—Providing cryptographic facilities or services
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F7/00—Methods or arrangements for processing data by operating upon the order or content of the data handled
- G06F7/58—Random or pseudo-random number generators
- G06F7/588—Random number generators, i.e. based on natural stochastic processes
Landscapes
- Engineering & Computer Science (AREA)
- Theoretical Computer Science (AREA)
- Physics & Mathematics (AREA)
- General Physics & Mathematics (AREA)
- General Engineering & Computer Science (AREA)
- Computer Hardware Design (AREA)
- Software Systems (AREA)
- Computer Security & Cryptography (AREA)
- Health & Medical Sciences (AREA)
- General Health & Medical Sciences (AREA)
- Bioethics (AREA)
- Computational Mathematics (AREA)
- Mathematical Analysis (AREA)
- Mathematical Optimization (AREA)
- Pure & Applied Mathematics (AREA)
- Storage Device Security (AREA)
Abstract
The embodiment of the application provides a data encryption processing method, a data encryption processing system and electronic equipment. The method comprises the following steps: after a data encryption request is received, selecting a plurality of first random numbers, wherein the exclusive or value among the first random numbers is a fixed value; determining a plurality of data blocks; processing the plurality of data blocks based on the plurality of first random numbers to obtain a plurality of processed data blocks; performing round function operation on the processed data blocks to obtain an output result; determining whether the number of times of round function operation is less than a set value; if the times of round function operation are less than the set value, returning to the step of determining a plurality of data blocks; if the times of round function operation are larger than or equal to a set value, determining a corresponding ciphertext based on an output result; wherein, upon returning to performing the step of determining the plurality of data blocks, the determining the plurality of data blocks is performed based on the output result. The technical scheme provided by the application can effectively resist white box attack, and has the advantages of small required storage space, high attack complexity and higher key safety degree.
Description
Technical Field
The present application relates to the field of computer technologies, and in particular, to a data encryption processing method and system, and an electronic device.
Background
With the development of science and technology, the security and credibility of the running environment of the password software are gradually reduced. For example, in a white-box attack environment, a soft-implemented cryptographic algorithm lacks security during decryption, and an attacker may use a static analysis tool, a debugger, methods and tools for directly reading data in a memory, and the like to find out an algorithm key in the memory; for another example, for a newly-appeared bypass attack, the information, such as time, power consumption, electromagnetic waves, error information and the like, leaked by the cryptographic chip in the operation process can be utilized to attack and peep the cryptographic system.
As can be seen from the above, in the existing cryptographic algorithm implemented in soft mode, since the secret key is directly present in the memory, an attacker can steal the secret key through malicious software, and thus it is difficult to cope with the white-box attack. Although the security of the key can be better ensured by utilizing the existing hardware encryption algorithm, the problems of higher use cost, poorer universality and the like exist.
Disclosure of Invention
In view of the above, the present application provides a data encryption processing method, system and electronic device that solve the above problems, or at least partially solve the above problems.
In one embodiment of the present application, a data encryption processing method is provided. The method comprises the following steps:
after a data encryption request is received, selecting a plurality of first random numbers; wherein, the exclusive or value among the plurality of first random numbers is a constant value;
determining a plurality of data blocks;
processing a plurality of data blocks based on the plurality of first random numbers to obtain the plurality of processed data blocks;
performing round function operation on the processed data blocks to obtain an output result;
determining whether the number of times of round function operation is less than a set value;
if the number of times of round function operation is less than the set value, returning to the step of determining a plurality of data blocks; if the times of round function operation are larger than or equal to the set value, determining a corresponding ciphertext based on the output result; wherein the determining the plurality of data blocks is performed based on the output result upon returning to performing the determining the plurality of data blocks.
In one embodiment of the present application, a data encryption processing system is provided. The system comprises:
the client is used for responding to a data encryption request triggered by a user and sending the data encryption request to the server;
the server is used for selecting a plurality of first random numbers after receiving the data encryption request; wherein, the exclusive or value among the plurality of first random numbers is a constant value; determining a plurality of data blocks; processing a plurality of data blocks based on the plurality of first random numbers to obtain the plurality of processed data blocks; performing round function operation on the processed data blocks to obtain an output result; determining whether the number of times of round function operation is less than a set value; if the times of round function operation are less than the set value, returning to the step of determining the plurality of data blocks; if the times of round function operation are larger than or equal to the set value, determining a corresponding ciphertext based on the output result; wherein the determining the plurality of data blocks is performed based on the output result upon returning to performing the determining the plurality of data blocks.
In one embodiment of the present application, an electronic device is provided. The electronic device includes: a memory and a processor, wherein,
the memory for storing one or more computer programs;
the processor is coupled to the memory and configured to execute the one or more computer programs stored in the memory to implement the steps in the data encryption processing method provided by the embodiment of the present application.
According to the technical scheme provided by the embodiment of the application, after a data encryption request is received, a plurality of first random numbers are selected, and the exclusive or value among the first random numbers is a fixed value; furthermore, a plurality of data blocks are determined, the data blocks are processed based on the first random numbers to hide states of the data blocks, and code extraction attack in a white-box attack environment is prevented in an external coding mode. Then, performing round function operation on the processed data blocks to obtain corresponding output results, judging whether the number of times of the current round function operation is smaller than a set value, and returning to the step of determining the data blocks if the number of times of the round function operation is smaller than the set value, wherein when the step of determining the data blocks is returned, the data blocks are determined based on the output results; otherwise, if the number of times of round function operation is determined to be larger than or equal to the set value, determining the corresponding ciphertext according to the output result. When the round function operation is realized, the required storage space is small, and an attacker can be ensured to be difficult to deduce the information related to the SM4 algorithm key according to the intermediate operation result of the round function operation, so that the key safety degree is higher.
Drawings
In order to more clearly illustrate the embodiments of the present application or the technical solutions in the prior art, the drawings required to be utilized in the embodiments or the prior art descriptions will be briefly described below, and it is obvious that the drawings in the following descriptions are some embodiments of the present application, and other drawings can be obtained by those skilled in the art without creative efforts.
Fig. 1 shows a schematic diagram of the standard SM4 algorithm;
fig. 2 is a schematic flowchart illustrating a data encryption processing method according to an embodiment of the present application;
fig. 3a shows a schematic diagram of implementing data encryption processing based on the SM4 algorithm according to an embodiment of the present application;
FIG. 3b is a schematic diagram illustrating the intermediate blocks resulting from the operation of computing round functions provided by an embodiment of the present application;
FIG. 4a is a schematic structural diagram of a data encryption processing system according to an embodiment of the present application;
FIG. 4b is a schematic diagram illustrating a specific form of a client and a server according to an embodiment of the present application;
fig. 5 is a schematic structural diagram illustrating a data encryption processing apparatus according to another embodiment of the present application;
fig. 6 shows a schematic structural diagram of an electronic device according to an embodiment of the present application.
Detailed Description
In view of the problems in the existing encryption algorithms proposed in the above background art, embodiments of the present application provide a data encryption processing scheme. The technical scheme for soft realization of SM4 algorithm security data encryption is provided in the white-box attack environment, the white-box attack can be effectively resisted, especially the code extraction attack under the white-box attack, the required storage space is small, the attack complexity is high, and the encryption key security degree is high. The white-box attack environment is a concept provided for a black-box attack environment, the traditional password security analysis environment is called as the black-box attack environment, and an attacker in the black-box attack environment can only access the input and the output of a password system; in contrast to the black box attack environment, an attacker in the white box attack environment has complete control over the algorithm execution environment and has complete knowledge of the design details of the algorithm. The ability of an attacker in the white-box attack environment includes, but is not limited to, dynamically observing the running process of the algorithm program, modifying intermediate values in the running process of the algorithm program, performing debugging analysis on the algorithm program, and the like.
In order to make the technical solutions better understood by those skilled in the art, the technical solutions in the embodiments of the present application will be clearly and completely described below with reference to the drawings in the embodiments of the present application.
In some of the flows described in the specification, claims, and above-described figures of the present application, a number of operations are included that occur in a particular order, which operations may be performed out of order or in parallel as they occur herein. The sequence numbers of the operations, e.g., 101, 102, etc., are used merely to distinguish between the various operations, and do not represent any order of execution per se. Additionally, the flows may include more or fewer operations, and the operations may be performed sequentially or in parallel. It should be noted that, the descriptions of "first", "second", etc. in this document are used for distinguishing different messages, devices, modules, etc., and do not represent a sequential order, nor limit the types of "first" and "second" to be different. In the present application, the term "or/and" is only one kind of association relationship describing the associated object, and means that three relationships may exist, for example: a or/and B, which means that A can exist independently, A and B exist simultaneously, and B exists independently; the "/" character in this application generally indicates that the objects associated with each other are in an "or" relationship. It is also noted that the terms "comprises," "comprising," or any other variation thereof, are intended to cover a non-exclusive inclusion, such that a good or system that comprises a list of elements does not include only those elements but may include other elements not expressly listed or inherent to such good or system. Without further limitation, an element defined by the phrase "comprising an … …" does not exclude the presence of other like elements in a commodity or system that includes the element. In addition, the embodiments described below are only a part of the embodiments of the present application, and not all of the embodiments. All other embodiments, which can be derived by a person skilled in the art from the embodiments given herein without making any creative effort, shall fall within the protection scope of the present application.
Before introducing the data encryption processing scheme provided by the present application, a brief description is given to an encryption algorithm on which the data encryption scheme provided by the present application is implemented.
In order to cope with the white-box attack, the application realizes data encryption based on the SM4 algorithm. The SM4 algorithm is a packet encryption algorithm that groups data information to be encrypted into packets of the same length and encrypts each packet data with the same master key, thereby converting each packet data into a packet ciphertext of the same length. The data packet length and the master key length of the standard SM4 algorithm are both 128 bits (i.e. 128 bits, 16 bytes (byte), 4 words (word)), a 32-round nonlinear iteration structure is adopted in the encryption process, encryption operation is performed in units of words (32 bits), each round of iteration operation is called a round function operation, and a round key of 32 bits is used in one round function operation. The round key is generated by a main key through a key expansion algorithm, the key expansion algorithm also adopts a 32-round nonlinear iterative structure, and the key expansion operation is carried out by taking a word as a unit. Figure 1 shows the standard SM4 algorithm bulk encryption process.
Referring to fig. 1, the whole encryption process of the standard SM4 algorithm is divided into two parts, namely a round key generation part and a data encryption operation part. Wherein,
in the round key generating part, 32-bit round keys required by the data encryption part are generated by a 128-bit master key through a key expansion algorithm, and the 32 round keys are respectively marked as: rk 0 、rk 1 、......、rk 31 . In the process of generating the round key, parameters that need to be used further include a system parameter FK and a fixed parameter CK, where the system parameter FK and the fixed parameter CK are respectively expressed as: FK = (FK) 0 ,FK 1 ,FK 2 ,FK 3 ),CK=(CK 0 ,CK 1 ,....,CK 31 ) Each entry in FK and CK is a word (i.e., 32 bits). Specifically, the process of generating the round key is as follows:
splitting an input 128-bit master key MK into 4 key blocks of 32 bits, wherein the 4 key blocks respectively use the MK 0 、MK 1 、MK 2 、MK 3 Is expressed as MK = (MK) 0 ,MK 1 ,MK 2 ,MK 3 );
The 4 key blocks are respectively subjected to XOR operation with each item of the system parameter FK to obtain a key K for circulation 0 ,K 1 ,K 2 ,K 3 I.e. K 0 =MK 0 FK 0 ,K 1 =MK 1 FK 1 ,K 2 =MK 2 FK 2 ,K 3 =MK 3 FK 3 ;
Entry round key rk i And (3) generating operation: facility fori(i=0,1, 2.., 31) characterize the number of round function operations performed wheniThe first round function F when =0 1 Operation is carried out untili=31 end, each round function F 1 The operation generates a round key. To generate a round key rk 0 For example, K 0 ,K 1 ,K 2 ,K 3 As a first round function F 1 Input of operation, to K 0 ,K 1 ,K 2 ,K 3 Execution round function F 1 In operation, K is firstly added 0 ,K 1 ,K 2 ,K 3 The last three of (i.e., K) 1 、K 2 、K 3 ) With a fixed parameter CK 0 Performing XOR operation to obtain a 32-bit first data C 0 (ii) a The first data C 0 Input to the synthetic permutation T 1 Synthesis of replacement T 1 For the first data C 0 After processing, a 32bit second data D is output 0 The second data D 0 And K 0 An intermediate value K is obtained by performing an XOR operation 4 The intermediate value K 4 I.e. the first round function F in the cryptographic operation 1 Round key rk used for operation 0 (ii) a At the same time, K is also multiplexed 1 ,K 2 ,K 3 Is a reaction of K 1 ,K 2 ,K 3 And K 4 As a second round function F 1 Input of operation to generate a second round function F in the course of a cryptographic operation 2 Round key rk used for operation 1 Repeat the above steps untili=31 executing 32 round functions F 1 And (5) operating.
In summary, set forthi+1-order round function F 1 The input of the operation is (K) i ,K i+1 ,K i+2 ,K i+3 ) Output is (K) i+1 ,K i+2 ,K i+3 ,K i+4 ) Wherein, K is i+4 =rk i ,K i+4 The calculation expression of (a) is as follows:
rk i = K i+4 =F 1 (K i ,K i+1 ,K i+2 ,K i+3 ,CK i )
wherein,is an XOR operation sign, CK i Synthesizing a permutation T for the fixed parameters used for the current iteration 1 Is a reversible transformation with 32bit data for both input and output. Note that specific values of the system parameters (FK 0, FK1, FK2, FK 3) and the fixed parameters (CK 0, CK 1.., CK 31) can be found in the related art.
Further, with continued reference to FIG. 1, in the data encryption portion, the 128-bit data to be encrypted is recorded as X due to the round function F in the data encryption portion 2 The encryption operation is carried out by taking a word (32 bit) as a unit, therefore, after 128bit data X is received, the 128bit data is required to be split into 4 32bit data blocks with equal length according to bits, and the 4 32bit data blocks are respectively marked as X 0 、X 1 、X 2 、X 3 I.e. X = (X) 0 、X 1 、X 2 、X 3 ). To X 0 、X 1 、X 2 、X 3 Performing a round function F of 32 rounds 2 After operation, X will be output 32 、X 33 、X 34 、X 35 Four data blocks, for X 32 、X 33 、X 34 、X 35 After the reverse order transformation, a ciphertext of 128 bits corresponding to the data X can be formed. In the course of the cryptographic operation, a round function F 2 Operation, round function F in round key generation section 1 The operation is similar, specifically: with a first round function F 2 Operation is for example splitting X obtained by 128bit data X 0 、X 1 、X 2 、X 3 Four data blocks are input to round function F 2 Then, X will be aligned first 0 、X 1 、X 2 、X 3 The last three of the four data blocks (i.e., X) 1 、X 2 、X 3 ) Round key rk corresponding to the round function operation 0 Performing XOR operation to obtain XOR result value A 0 (at 32-positions), i.e. A 0 =X 1 X 2 X 3 rk 0 (ii) a Thereafter, T is replaced by synthesis 2 (with the synthetic permutation T in the round key generation section 1 Like) pair xor result value a 0 Processing the data to obtain 32bit data B 0 (ii) a Data B 0 And data block X 0 The XOR operation is performed to obtain a 32-bit middle block X 4 While also multiplexing data block X 1 、X 2 、X 3 . Data block X 1 、X 2 、X 3 And intermediate block X 4 As a second round function F 2 Inputting operation, repeating the above steps until 32 round functions F are executed 2 After operation X is obtained 32 、X 33 、X 34 、X 35 These four data blocks. Then, for X again 32 、X 33 、X 34 、X 35 The four data blocks are subjected to reverse order conversion to obtain an order X 35 、X 34 、X 33 、X 32 Four data blocks of (2), for X 35 、X 34 、X 33 、X 32 These four data blocks are combined by concatenation to obtain a 128-bit cipher text corresponding to data X.
In summary, the first stepi+1-order round function F 2 The input of the operation is (X) i ,X i+1 ,X i+2 ,X i+3 ) The output is (X) i+1 ,X i+2 ,X i+3 ,X i+4 ) And the round key used is rk i (ii) a Wherein, X i+4 The calculation expression of (c) is as follows:
X i+4 = F(X i ,X i+1 ,X i+2 ,X i+3 ,rk i )
wherein, rk i Indicates the current firsti+Round key used by 1 round function operation iteration to synthesize replacement T 2 Is a reversible transformation with 32bit data for both input and output.
It should be noted that the synthesis and substitution in the round key generation section and the data encryption section is a reversible transformation, and is a composite of a nonlinear transformation and a linear transformation, the nonlinear transformation is composed of 4 parallel S-boxes, and the nonlinear transformation output is the input of the linear transformation. For a detailed description of the synthesis substitution, the S-box, etc., reference is made to the existing contents, and detailed description thereof is omitted here. In addition, the bits, bytes, words and the like are some data units commonly used in the cryptographic algorithm, a bit/bit is a binary bit, and 1 word =4 bytes =32 bits.
The following describes a data encryption processing scheme provided in the present application.
Fig. 2 is a schematic flowchart illustrating a data encryption processing method according to an embodiment of the present application. The execution main body of the method is electronic equipment with a logic operation function, and the electronic equipment can be a client or a server; the client can be any terminal device such as but not limited to a smart phone, a tablet computer, a desktop computer, a notebook computer and an intelligent wearable device, and the server can be a service cluster, a virtual server, a cloud end and the like which are composed of a plurality of servers but not limited to a single server. Hereinafter, the data encryption processing method provided by the present embodiment will be described with the server as the execution subject. As shown in fig. 2, the data encryption processing method includes the following steps:
101. after a data encryption request is received, selecting a plurality of first random numbers; wherein, the exclusive or value among the plurality of first random numbers is a constant value;
102. determining a plurality of data blocks;
103. processing the plurality of data blocks based on the plurality of first random numbers to obtain the plurality of processed data blocks;
104. performing round function operation on the processed data blocks to obtain an output result;
105. determining whether the number of times of round function operation is less than a set value;
106. if the number of times of round function operation is less than the set value, returning to the step of determining a plurality of data blocks; if the times of round function operation are larger than or equal to the set value, determining a corresponding ciphertext based on the output result; wherein the determining the plurality of data blocks is performed based on the output result upon returning to performing the determining the plurality of data blocks.
The standard SM4 algorithm shown in FIG. 1, which mixes the key in the round function for hiding, realizes the protection of the key and can avoid the password attack. However, in the environment of white-box attack in practical applications, the attacker is not necessarily the oneA cryptographic attack is performed in order to obtain the key. For example, in some applications, an attacker may extract the decrypted program directly and embed it in its own application, which is called a code extraction attack. In the code extraction attack, an attacker does not need to extract a key, a decryption program corresponds to a white-box scheme part, and the attacker can acquire data information by extracting and processing the white-box scheme decryption part. In order to prevent code extraction attack, the technical scheme provided by the embodiment keeps the whole structure of the standard SM4 algorithm as shown in FIG. 1 unchanged, and inputs (such as X) of each round function operation are input by introducing outer coding 0 ,X 1 、X 2 、X 3 ) The first random number is added for confusion to hide the input state of each round of function operation, thereby ensuring that even an attacker directly extracts the decryption program, the attacker cannot acquire the original data information.
In the foregoing 101, the selected plurality of first random numbers are used for performing obfuscation processing on a plurality of subsequently determined data blocks, so that the obfuscated plurality of data blocks are used as input of round function operation. The data length of the first random number is the same as the length of the data block, the number of the selected first random numbers is the same as the number of the plurality of data blocks determined subsequently, and the xor value between the plurality of first random numbers is a fixed value, for example, the xor value between the plurality of first random numbers may be 0 or may also be 1, which is not limited herein. As a preferred example, the following describes the technical solution provided by the present embodiment with the exclusive or value between the plurality of first random numbers being 0.
Specifically, for example, if the plurality of data blocks determined in the following are 4 32-bit data blocks, then 4 32-bit first random numbers are selected, in order to distinguish the 4 32-bit first random numbers, a self-increment mode can be adopted to add numbers to the selected 4 32-bit first random numbers in the process of selecting the first random numbers, and based on this, the selected 4 32-bit first random numbers can be respectively marked as R 0 、R 1 、R 2 And R 3 ,R 0 、R 1 、R 2 And R 3 Satisfy R 0 R 1 R 2 R 3 =0 (or R may be satisfied) 0 R 1 R 2 R 3 =1, etc.).
It should be noted that, in addition to the convenience of distinguishing the plurality of first random numbers, the number is added to the first random number, and the corresponding target random number is selected from the plurality of first random numbers for the data block to be confused by adding the first random number in order to facilitate the subsequent execution. The specific implementation regarding the selection of the target random number may be a parameter of relevance below.
In addition, the encryption request received in the foregoing 101 may be triggered by an interactive interface provided by a user through a client, and the triggering manner may be, but is not limited to, voice, a mouse, a keyboard, a hand touch, and the like. The encryption request carries data information to be encrypted, and the type of the data information to be encrypted can be determined according to an application scene, for example, the data information can be audio and video data in an audio and video transmission process. In order to deal with the white-box attack environment, for data information to be encrypted, in this embodiment, the data information to be encrypted is encrypted by soft implementation of an SM4 algorithm, and the SM4 algorithm is a packet encryption algorithm, so that after the data information to be encrypted is analyzed from an encryption request, the data information to be encrypted is first grouped according to the same length to perform packet encryption on the data information. Since the SM4 algorithm only encrypts 128-bit data (i.e., 16-byte data) at a time, in the grouping process, it is required to ensure that the data length of each packet is 128 bits (i.e., 16 bytes), and when the data information is less than 16 bytes or an integral multiple of 16 bytes, the padding algorithm is used to add corresponding padding data at the end of the data information to make the data information length an integral multiple of 16 bytes.
The padding algorithm described above may be, but is not limited to, binary bit based padding and byte based padding, wherein byte based padding includes ANSIX9.23, ISO10126, PKCS #5, PKCS #7, zero padding, and the like. For the above detailed description of binary-based padding and byte-based padding, reference is made to the prior art.
After the data information is divided into a plurality of groups of data according to the 128bit data length, the same 128bit master key is sequentially used for carrying out block encryption on the plurality of groups of data, and therefore each group of data is converted into block ciphertext data with the same length. Since the SM4 algorithm performs encryption operation in units of words (32 bits) during encryption, for this reason, before a group of data is encrypted, the group of 128-bit data needs to be split into a plurality of data blocks (the size of the data block is generally 32 bits) with equal size, and then 32 rounds of function operations are performed on the plurality of data blocks to convert the group of 128 data into a corresponding group of 128-bit ciphertext data. It should be noted that, in the process of executing 32 rounds of round function operations, the input of the first round function operation is determined by a plurality of data blocks obtained by splitting a group of 128-bit data, and the input of the other round function operations is determined based on the output result of the last round function operation.
Based on the above, one achievable technical solution of "determining a plurality of data blocks" in the above-mentioned step 102 is:
1011. determining data to be encrypted based on the encryption request;
1012. and splitting the data to obtain a plurality of data blocks with equal size.
In the above 1011, the encryption request may carry data information to be encrypted, and the data information is grouped according to a preset data length to obtain data to be encrypted. The predetermined data length is 128 bits, but in other embodiments, the predetermined length may be an integer multiple of 128 bits, such as 256 bits, which is not limited herein. As a preferred example of this embodiment, the preset length is 128 bits, and hereinafter, the technical solution provided by this embodiment will also be described with the determined data to be encrypted being 128 bits. Specific implementations for grouping data information can be found in the above related text.
In the above 1012, since the SM4 algorithm performs encryption operation in units of words (32 bits) in the data encryption process, to meet the encryption operation rule of the SM4 algorithm, further, 128-bit data to be encrypted needs to be split, and in the splitting process, the 128-bit data can be split into 4 equal-sized 32-bit data blocks by bit. Referring to fig. 3a, let the 128-bit data to be encrypted be X, then X = (X) 0 ,X 1 、X 2 、X 3 ),X 0 ,X 1 、X 2 、X 3 The 4 32-bit data blocks obtained for the splitting of the 128-bit data X are used as the plurality of data blocks determined for the first round of function F operation, that is, X 0 ,X 1 、X 2 、X 3 An input data block for operating as a first round function F; wherein, the numbers 0,1,2 and 3 are serial numbers written for different data blocks in a self-increment mode. The sequence number of a data block can represent the arrangement position of the data block in a plurality of data blocks, and can also represent the data block as the input of the operation of the round function F to a certain extent. In the respect of X 0 ,X 1 、X 2 、X 3 During the iteration of executing the set number of times (e.g. 32 times) of the round function F operation, the intermediate block generated by each round function operation is at X 0 ,X 1 、X 2 、X 3 On the basis of the sequence numbers, the sequence numbers corresponding to the intermediate blocks are programmed by sequentially increasing the sequence numbers.
Determining a plurality of data blocks (e.g., X) through the steps 1011-1012 0 ,X 1 、X 2 、X 3 ) Thereafter, the attack may be extracted for the code in the white-box attack environment based on the determinationsThe first random numbers process the data blocks to hide the real state of the input data block in each round of function operation, so as to ensure that even an attacker directly extracts the decryption program, the attacker cannot acquire the original data information.
Due to the data block multiplexing characteristic of round function operation, data blocks to which the first random number has been added for confusion may exist in the determined plurality of data blocks. The data block multiplexing refers to that a part of data blocks in a plurality of data blocks input to a round of function operation are multiplexed to be used as an output of the round of function operation, that is, an output result of the round of function operation includes the multiplexed part of data blocks input to the round of function operation, and this part of data blocks generally refers to data blocks in the plurality of data blocks participating in synthesis and replacement in the round of function operation. For example, as shown in FIG. 1, a first round function F 2 The output of the operation contains the multiplexed inputs to the round function F 2 4 data blocks X of operation 0 、X 1 、X 2 、X 3 X in (1) 1 、X 2 、X 3 X of the formula 1 、X 2 、X 3 And operating F by a first round function 2 Intermediate value X of operation generation 4 It is used as the input for the second round of function operation.
Based on this, in a specific implementation technical solution, the "processing a plurality of data blocks based on the plurality of first random numbers to obtain the processed plurality of data blocks" in the above 103 may specifically include:
1030. determining at least one data block to be processed in the plurality of data blocks;
1031. respectively acquiring the sequence number of each data block in the at least one data block;
1032. according to the sequence number, selecting a first random number from the first random numbers for each data block in the at least one data block as a target random number;
1033. and performing exclusive-or operation on each data block in the at least one data block and the corresponding target random number to obtain the at least one processed data block.
In the above 1030, at least one data block to be processed in the plurality of data blocks is related to the iteration degree to which the currently executed round function is operated. In the case where the currently performed iteration is the first round of function operation. The data blocks are obtained by splitting data to be encrypted, and the data blocks are all in a real state at the moment, namely the data blocks are all data blocks to be processed. For example, 4 data blocks X shown in FIG. 3a 0 、X 1 、X 2 、X 3 Split from the data X to be encrypted, as input to the first round of function F operation, for which the 4 blocks X are intended 0 、X 1 、X 2 、X 3 Each of which is a plurality of data blocks that need to be processed. Due to the data block multiplexing characteristic of the input round function, in the case that the currently executed iteration is other round function operations except the first round function F operation, the intermediate block generated by the last round function operation included in the plurality of data blocks is the data block to be processed. For example, with continued reference to FIG. 3a, after the first round of function F has been performed, an output is output,And X 4 In which X is 4 To aim at X 0 、X 1 、X 2 、X 3 The intermediate block resulting from the first round of the function F operation,andall the data blocks are added with the first random number; at the beginning of entering the second round function F operation iterationThen, the plurality of data determined based on the output result of the first round function F operation areAnd X 4 These four data blocks, X 4 The data block to be added with the first random number for confusion processing. The specific implementation of the round function F operation can be referred to the related contents below, and will not be described herein.
1031 to 1032 mentioned above, after acquiring the sequence numbers of the data blocks in the at least one data block, respectively, selecting one first random number as the target random number for each data block in the at least one data block from the plurality of first random numbers by a remainder method. The remainder is to take the remainder of the number of the first random numbers by using the serial number of the data block, and determine the number corresponding to the first random number for performing the obfuscation processing on the data block according to the remainder obtained by the remainder, so as to select a corresponding one of the plurality of first random numbers as the target random number according to the number. That is, in an implementation technical solution, the aforementioned 1032 "selecting one first random number as the target random number for one data block of the at least one data block from the plurality of first random numbers according to the sequence number" may specifically be implemented by adopting the following steps:
10321. utilizing the serial number of the data block to carry out the remainder on the number of the first random numbers;
10322. and selecting one first random number from the plurality of first random numbers as the target random number according to a remainder value obtained by remainder.
In a specific implementation, the remainder may be directly used as a number corresponding to the first random number used for performing the obfuscation processing on the data block, so that the first random number with the number as the remainder is selected from the plurality of first random numbers as the target random number according to the remainder.
In 1033, the xor operation is performed on each data block in the at least one data block and the corresponding target random number, so as to add the corresponding first random number to each data block in the at least one data block for confusion, thereby hiding the real state of each data block.
The following description is directed to the above steps 1030 to 1033, and a specific example is given: as can be seen from the above, in the SM4 algorithm encryption process, the input of each round function F operation is 4 data blocks of 32 bits, and based on this, 4 first random numbers of 32 bits are selected for obfuscating the data blocks input by the current round function F operation. Referring to FIG. 3a and following the above example related to step 101, the selected 4 32-bit first random numbers are set to R 0 、R 1 、R 2 、R 3 And R is 0 、R 1 、R 2 、R 3 Satisfy R 0 R 1 R 2 R 3 And = 0. Assume that the current iteration is the first round function F operation (i.e., the iteration is performedi= 0), the 4 32-bit data blocks corresponding to the input of the current round function operation are X 0 ,X 1 、X 2 、X 3 The 4 data blocks X are processed 0 ,X 1 、X 2 、X 3 Before inputting to the first round function F operation, according to X 0 ,X 1 、X 2 、X 3 The respective sequence numbers of these four data blocks, from R 0 、R 1 、R 2 、R 3 X in the four first random numbers 0 ,X 1 、X 2 、X 3 Selecting corresponding first random numbers for X pairs 0 ,X 1 、X 2 、X 3 The true state of these four blocks of data is hidden. In particular implementation, e.g. data block X 0 Is 0, the remainder obtained by taking the number (i.e., 4) of the first random number by the number 0 is 0, then R is 0 、R 1 、R 2 、R 3 The first random number (i.e., R) numbered 0 0 ) I.e. as data block X 0 The selected target random number is recorded in data block X 0 And a first random number R 0 With an XOR value of X 0 ', then X 0 '=X 0 R 0 . Similarly, the data blocks X can also be obtained separately 1 Data block X 2 And data block X 3 The result of the exclusive or with the corresponding first random number is: x 1 '=X 1 R 1 、X 2 '=X 2 R 1 、X 3 '=X 3 R 1 。X 0 '、X 1 '、X 2 '、X 3 ' are the plurality of data blocks input to the first round function F operation. After the first round function F operation is completed, the middle block X is obtained 4 While multiplexing X 1 '、X 2 ' and X 3 ', mixing X 1 '、X 2 '、X 3 ' and X 4 As an output result of the first round function F operation, subsequently, when entering the second round function F operation iteration, the plurality of data blocks determined for the second round function operation are X 1 '、X 2 '、X 3 ' and X 4 。X 1 '、X 2 '、X 3 ' and X 4 Wherein the data block to be processed is X 4 By using a slave R 0 、R 1 、R 2 、R 3 X in the four first random numbers 4 The selected target random number (i.e. R) 0 ) To X 4 Processing to hide X 4 True state of (2) can obtain X 4 ' (i.e. X) 4 '=X 4 R 0 ),X 1 '、X 2 '、X 3 ' and X 4 ' is the input for the second round function operation. By analogy, the first one can be obtainediThe input of +1 round function F operation isAnd(ii) a Wherein,i=0,1,2,... ,31。
in general, referring to the operational structure of the round function operation of the standard SM4 algorithm as shown in fig. 1, a plurality of data blocks input to the round function operation, a part of which are used to participate in the synthetic permutation T of the round function operation together with the round key 2 So that the round key can effectively influence the data which needs to be encrypted, and the hiding of the round key is realized; the other data block is used for replacing T with the synthesis 2 The output result of (a) is subjected to exclusive-or operation to obtain an intermediate block for participating in iterative operation of round function operation. It can be seen that the data blocks input to the round function operation often have two types of data blocks, one of which is used for the synthetic permutation participating in the round function operation, and the other of which is exclusive-ored with the output result of the synthetic permutation to obtain the intermediate block. Based on this, for the present embodiment, there are also two types of data blocks in the plurality of data blocks determined for the current round function operation, that is, there are a first type of data block and a second type of data block, and the second type of data block is used for participating in the synthetic permutation of the round function operation. In a specific implementation, the plurality of data blocks have at least one first type data block and at least two second type data blocks. For example, still with continued reference to FIG. 3a, let a number of data blocks be X as shown in FIG. 3a 0 ,X 1 、X 2 、X 3 The four data blocks, then X 0 ,X 1 、X 2 、X 3 The first data block (i.e., X) in (e.g., c) 0 ) Is the first type of data block, the last three data blocks (i.e. X) 1 、X 2 、X 3 ) For the second type of data block, in this case, a round function operation would result in an intermediate block. Of course, in other embodiments, X as shown in FIG. 3a may be used 0 ,X 1 、X 2 、X 3 The first two data blocks (i.e., X) in (2) 0 、X 1 ) As a first type of data block, the last two data blocks (i.e., X) 2 、X 3 ) As a second type of data block, in this case, a round function operation produces two intermediate blocks. In this embodiment, the specific number of the first type data block and the second type data block in the plurality of data blocks is not limited. However, as a preferred example, the scheme is mainly described below by taking as an example that one data block of the first type is included in the plurality of data blocks as shown in fig. 3a, and the others are all data blocks of the second type.
Further, in the implementation of round function operation, while the whole round function operation structure in the standard SM4 algorithm shown in fig. 1 is kept unchanged, the steps in each round function operation are modularized, for example, the synthesis permutation T is regarded as one module, and the step of calculating the xor operation of the middle block is regarded as one module. Moreover, linear coding is adopted to mix the input and the output of each module; wherein the aliasing introduced by the output part of the last module transform is cancelled out at the input part of the next module transform, i.e. the overall coding of the round function operation is a networked coding. The linear encoding described above may be, but is not limited to, a form of encoding employing affine transformation.
Based on the above, in a specific implementation technical solution, the above 104 "performing round function operation on the processed data blocks to obtain an output result" may specifically include:
1041. encoding the processed second type data block to obtain an encoded second type data block;
1042. synthesizing and replacing the encoded second-class data block and a round key corresponding to the current round function operation to obtain a first output value;
1043. obtaining an intermediate block based on the processed first type data block and the first output value;
1044. and taking the processed second class data block and the intermediate block as an output result of the current round function operation.
In 1041, the processed second-class data block may be encoded by using, but not limited to, an affine transformation encoding form. Specifically, the processed second class data block may be encoded by using the affine transformation P and the diagonal matrix E that are iteratively pre-generated for the current round function operation. Based on this, 1041 "encode the processed second-class data block to obtain the encoded second-class data block" may specifically adopt the following steps:
10411. acquiring a pre-generated reversible affine transformation and a diagonal matrix;
10412. and coding the processed second-class data block by using the reversible affine transformation and the diagonal matrix to obtain a coded second-class data block.
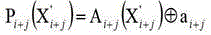
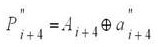
In practice, assume that it is currently at the firsti+1 iteration stages of round function operation, the pre-generated affine transformation P i And diagonal matrix E i The forms of (a) and (b) can be as follows:
E i = diag(E i0 ,E i1 ,E i2 ,E i3 );
in the above equation, in affine transformationjFor indicating input to i+1J-th data block, A, of the processed plurality of data blocks operated on by the second round function F i j+ Is a 32 x 32 invertible matrix over a finite field GF (2), a i j+ Is a 32-bit constant (i.e., a 32 x 1 column vector). Diagonal matrix E i Each of E in ij All of which are 8bit by 8bit, and may also beSeen as an 8 x 8 invertible matrix over the finite field GF (2). P is above i j+ And E i All are randomly selected and kept secret, and finally, the composite codes are codedIs stored openly, and the composite code isIs an invertible affine transformation mapping 32 bits onto 32 bits over the finite field GF (2). By composite codingTo enable encoding of the processed plurality of data blocks. I.e. for the second of the processed plurality of data blocksjThe form in which each data block is encoded can be expressed as follows:
based on the above, see FIG. 3a, let the input go toiThe processed plurality of data blocks operated on +1 round function F are、、And(ii) a Wherein,for the processed data blocks of the first type,、andfor the processed second type data block, the data blocks are respectively paired、Andand coding, wherein the obtained coded second-class data block is as follows:
obtaining the encoded second type data block、Andthen, the coded second type data block is processed、Andand is currently the firsti+1 round function F operation the corresponding round key rk i Performing a synthetic permutation T, that is to say, calculatingThe present embodiment is implemented in the form of a lookup table. Specifically, it is to、Andexclusive or value ofx i And rk i The synthetic permutation of (2) is implemented in a look-up table format, i.e. in a look-up table formatIn which is calculated, wherein,x i Is 32 bits. In order to reduce the occupied memory space and improve the calculation efficiency, the technical scheme provided by the embodiment is that a plurality of lookup tables are used for formingEach calculation ofIn the time, only a plurality of corresponding lookup tables need to be searched, and then the output values of the plurality of lookup tables are subjected to exclusive or. The plurality of look-up tables may be generated in advance based on the round key. Based on this, the aforementioned 1042 "synthesize and replace the encoded second-class data block and the round key corresponding to the current round function operation to obtain the first output value" may specifically be implemented by the following steps:
10421. generating a plurality of lookup tables according to the round key;
10422. determining a plurality of blocks based on the encoded second class data blocks;
10423. respectively taking the plurality of blocks as the input of each lookup table in the plurality of lookup tables, and executing the plurality of lookup tables to obtain a plurality of corresponding second output values;
10424. and carrying out XOR operation on the plurality of second output values to obtain the first output value.
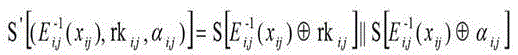
In 10421 above, considering the practical application, the synthetic permutation T of the standard SM4 algorithm includes a non-linear part and a linear part; wherein, the output of the nonlinear part is the input of the linear part, and the nonlinear part is composed of an S-box, the S-box is a fixed mapping table and is the only nonlinear operation in the SM4 algorithm process. Based on this, when the calculation of composing the synthetic permutation T by using a plurality of lookup tables is implemented in this embodiment, the generated lookup table is also composed of two major parts, namely, the nonlinear transformation and the linear transformation, and the nonlinear transformation is also an S-box operation, but the S-box operation is combined with the round key and simultaneously added with the random number for confusion; whereas the linear transformation operation of the look-up table may be completed in the form of a matrix. That is, a specific implementation scheme of 10421 "generating a plurality of lookup tables according to the round key" is as follows:
a10, determining a first transformation matrix;
a11, generating a second random number and a second transformation matrix;
a12, generating the plurality of lookup tables based on the round key, the second random number, the first transformation matrix and the second transformation matrix.
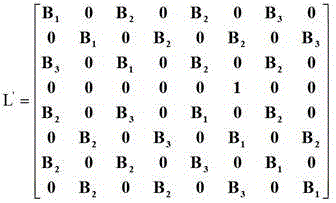
In A10, the first transformation matrix isIs a matrix of 64 bits by 64 bits and is used for determining the linear transformation of the lookup table so as to complete the linear transformation operation in the lookup table in the form of the matrix. Using the same first when generating the look-up table for the synthetic permutation T in each round function operationTransformation matrix. The first transformation matrixThe specific expression form of (A) can be as follows0 in represents a zero matrix of 8 bits × 8 bits, B 1 、B 2 And B 3 0 in represents one bit):
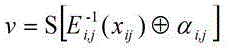
in the above a11, the generated second random number is a 32-bit random number, and is used for adding a random number for S-box operation for confusion in the process of generating the lookup table; where the S-box operates as the only non-linear transformation portion of the lookup table. And for the generated second transformation matrix I, the second transformation matrix I is an elementary transformation matrix and is used for restoring the output of the standard S box.
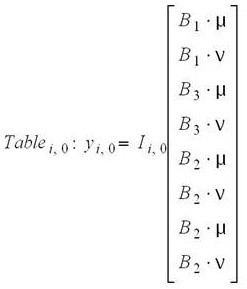
In the above-mentioned a12, according to the characteristic that the data lengths of the input and output of the S-box are both 8 bits, the round key of 32 bits and the second random data of 32 bits are equally split, and the first transformation matrix and the second transformation matrix are partitioned, so as to generate, for example, 4 lookup tables for 8-bit input-64-bit output based on the split result and the partitioning result.
Specifically, taking the example in step 104 above and continuing with FIG. 3a, assume that it is currently at the secondi+1In the iteration stage of the next round function, the split round key rk i And a second random number alpha i May be represented as follows:
rk i =(rk i,0 、rk i,1 、rk i,2 、rk i,3 ),α i =(α i,0 、α i,1 、α i,2 、α i,3 );
wherein, rk i,j And alpha i,j The data length of (j =0,1,2, 3) is 8 bits.
First transformation matrix after blockingAnd a second transformation matrix I i May be represented as follows:
wherein,(j =0,1,2, 3) is a matrix of 16 bits × 64 bits, I i,j (j =0,1,2, 3) is an elementary row transform matrix.
Then, based on rk i 、α i 、And I i The generated lookup Table tables with 4 8-bit input-64-bit output can be respectively expressed as follows:
in the above-mentioned description,representing S-box operation transformations (i.e. non-linear transformations), non-linear transformationsThe concrete structure is as follows:
order to,Then, then,u、vS-box outputs of 8 bits each atu、vOf the two onlyuIs useful information. For this purpose, Table is looked up in a look-up Table i,j In this embodiment, the matrix I is transformed by the elementary rows i,j Operate to restore the output of the S-boxu. Is recovered touThe specific construction process of (2) is as follows:
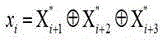
in the following, the above Table is used i,0 、Table i,1 、Table i,2 、Table i,3 The output results of the four lookup tables are subjected to XOR value obtained by XOR operationy i I.e. for the encoded second type data block and the round key rk i And performing synthesis and replacement to obtain a first output value. That is, the first output value of the permutation T is synthesizedy i The expression of (a) is as follows:
in the look-up table shown above,x ij representing inputs to a look-up Table Table i j, The block in (2), the block is determined based on the encoded second type data block. Based on the related description content in the above step 1041, at least two second-class data blocks are obtained after encoding, and the Table of the lookup Table is determined i j, Corresponding blockx ij In the process, the length of the at least two encoded second-type data blocks can be determined by performing equal-length splitting on the xor value between the at least two encoded second-type data blocks according to the number of the lookup tables. The specific determination of the block may be found in the examples described below.For eliminating coding present in block due to last transformation. Wherein j =0,1,2, 3.
With respect to 10422 to 10424, a specific example is described: as with the example in 1041 above and with reference to figure 3a,、andall the data blocks are second type data blocks after being coded; in the process of determining a plurality of blocks, the data can be divided into a plurality of blocks、Andthe XOR value between the three encoded second type data blocksx i (32 bits) are split into equal lengths according to the number of look-up tables to obtain the data shown in FIG. 3ax i0 、x i1 、x i2 、x i3 Four 8bit partitions, i.e.x i =(x i0 ,x i1 ,x i2 ,x i3 ) (ii) a Then, willx i0 、x i1 、x i2 、x i3 These four 8-bit partitions are input to respective tables as shown above i,0 、Table i,1 、Table i,2 、Table i,3 Four lookup tables are obtained by executing the four lookup tablesy i,0 、y i,1 、y i,2 、y i,3 Four second output values, pairy i,0 、y i,1 、y i,2 、y i,3 The four second output values are subjected to exclusive-OR operation, and the obtained exclusive-OR valuey i Namely, the coded second class data block and the round key rk i The resulting first output value (32 bits) is subjected to synthetic permutation.
Note that Table shown above i,0 、Table i,1 、Table i,2 、Table i,3 Four look-up tablesIn (1)、、Andi.e. for eliminatingx i Code added in E i (ii) a Wherein, as is clear from the above, E i = diag(E i0 ,E i1 ,E i2 ,E i3 ). In-execution lookup Table i j, In the process of (2), look-up Table (Table) i j, The output result of S-box in (1) is obtained by looking up the corresponding S-box input-output relationship table. The specific acquisition of the output result of the S-box can be found in the prior art.
In the embodiment, the round key is hidden by adopting the lookup table mode, and the random number is added into the S box contained in the lookup table to confuse the round key, so that half of information in the lookup table is obfuscated data, which increases the attack complexity and is beneficial to improving the security of the key. In addition, the hiding of the round function operation process can be realized by the aid of the lookup table, so that the information related to the SM4 algorithm key is difficult to derive from the intermediate operation result of the round function operation by the outside, and the key safety degree is higher. Moreover, the lookup table approach requires less memory space, which is about 277 KB.
Further, after the first output value obtained by synthesizing and replacing the encoded second-type data block and the round key corresponding to the current round function operation is obtained by executing the step 1042, the steps 1043 to 1044 are executed to obtain an intermediate block based on the processed first-type data block and the first output value, so as to determine the output result of the current round function operation.
In specific implementation, when the step 1043 is executed, the processed first type data block and the first output result are encoded, and the encoded first type data block and the encoded first output value are subjected to an exclusive or operation to obtain an intermediate block. In the encoding process, similar to the encoding of the processed second-class data block, the encoding is performed through the generated affine transformation, and in the encoding process, the encoding added by the previous transformation is eliminated first, and then new encoding is added.
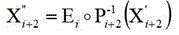
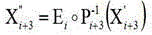
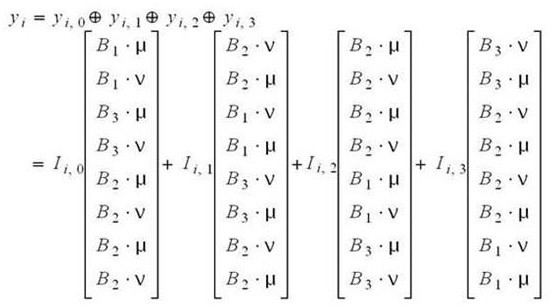
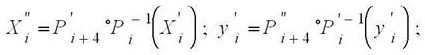
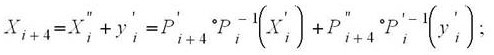
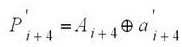
For example, taking the relevant example described in steps 1041 and 1042 above and referring to FIG. 3a, proceed with the current position being at the secondi+1 round function operation phases, as shown in FIG. 3aFor the processed data blocks of the first type,the first output value is respectively recorded as the first type data block after coding and the first output value after coding isThen pairThe encoding processes for performing affine encoding respectively are as follows:
let X i+4 To accomplish the followingiThe +1 round function operation corresponds to the available intermediate blocks, then:
wherein,for eliminating last-change interpolationAdding codes;andis the coding introduced by the current transform,,the method comprisesAre each a reversible affine transformation from 32bit to 32bit over a finite field GF (2), andand withIs the same, only the constant part (i.e. the matrix part of) Different.
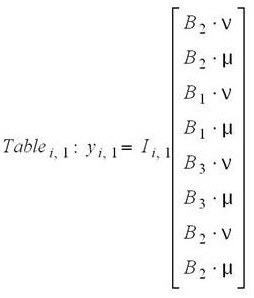
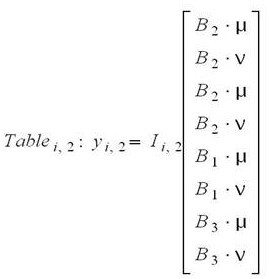
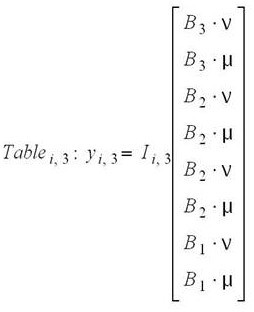
FIG. 3b shows X i+4 The specific calculation process of (2). For the specific description of fig. 3b, reference is made to the above related contents, and the detailed description is omitted here.
Further, in executing the step 1044, the processed second type data block of the plurality of processed data blocks input to the current round function operation and the intermediate block obtained in the step 1043 are used as the output result of the current round function operation based on the multiplexing characteristic of the round function operation. For example, taking the example of step 1043 above and continuing with FIG. 3a, the input is entered intoiOperated by +1 round functions、、Andthe last three of the four processed data blocks (i.e., the、And) And intermediate block X obtained via step 1043 i+4 As a result of this timeiThe output result of +1 round function operations; wherein,、andto take part iniThe second type data block of the synthetic permutation in +1 round function operations. For a description of the multiplexing properties of the operation of the round function, see the above related contents.
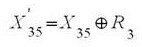
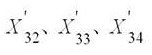
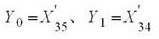
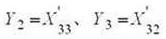
In the above 105 and 106, the set value is a preset parameter value for characterizing the iteration ending condition of the round function operation, and it can be flexibly set according to the actual situation, for example, it can be 16, 32, etc., and is not limited here. The setting value of 32 is preferably selected in this embodiment. After the current round function operation is executed to obtain a corresponding output result, the number of round function operations is correspondingly increased by one, and then whether the iteration of the round function operation is finished or not can be determined by comparing the determined number of round function operations with a set value, so thatAnd executing corresponding steps according to the determined result of whether the iteration of the round function operation is finished. Specifically, if it is determined that the number of round function operations is smaller than the set value, it is determined that the round function operation iteration does not reach the end condition, and then the step of "determining multiple data blocks" of the above step 102 is returned to enter a new round of round function operations, where the multiple data blocks are determined based on the output result of the current round function operations when the step 102 is returned to be executed. For example, referring to FIG. 3a and taking the example above at 104, let us say that the current second execution is finishedi+1(i<31) Operating the function of the second order to obtain a sequence of、、And X i+4 After the output result is obtained, a plurality of data blocks determined based on the output result are the data blocks、、And X i+4 The four data blocks of、、And X i+4 Four data blocks to be used for a new round of round function operation. Otherwise, if the number of times of the round function operation is determinedIf the number of the round function operation iterations is larger than or equal to the set value, the round function operation iterations are considered to reach the end condition, and at the moment, the corresponding ciphertext can be determined by executing operations such as reverse order transformation and the like based on the output result of the current round function operation. For example, as shown in FIG. 3a, after the current execution is finishedi+1(i= 31) round function operations, obtaining a result containingAnd X 35 After the output result is obtained, the corresponding first random number (i.e. R) is utilized first 3 ) To pairAnd X 35 X in (1) 35 Carrying out corresponding treatment to X 35 State change of (2)To hide X 35 The true state of (c); then, forAndcarrying out reverse order transformation to obtain Y 0 、Y 1 、Y 2 And Y 3 Wherein、(ii) a Will Y 0 、Y 1 、Y 2 And Y 3 And the corresponding 128-bit ciphertext Y can be obtained by sequentially splicing.
In summary, in the technical solution provided in this embodiment, after receiving the data encryption request, a plurality of first random numbers are selected first, and an exclusive or value between the plurality of first random numbers is a constant value; furthermore, a plurality of data blocks are determined, the data blocks are processed based on the first random numbers to hide states of the data blocks, and code extraction attack in a white-box attack environment is prevented in an external coding mode. Then, performing round function operation on the processed data blocks to obtain corresponding output results, judging whether the number of times of the current round function operation is smaller than a set value, and returning to the step of determining the data blocks if the number of times of the round function operation is smaller than the set value, wherein when the step of determining the data blocks is returned, the data blocks are determined based on the output results; otherwise, if the number of times of round function operation is determined to be larger than or equal to the set value, determining the corresponding ciphertext according to the output result. When the round function operation is realized, the required storage space is small, and an attacker can be ensured to be difficult to deduce the information related to the SM4 algorithm key according to the intermediate operation result of the round function operation, so that the key safety degree is higher.
Based on the above, a data encryption processing system is introduced below. Fig. 4a shows a schematic structural diagram of a data encryption processing system according to an embodiment of the present application. As shown in fig. 4a, the data encryption processing system includes: a client 100 and a server 200; wherein,
the client 100 is configured to respond to a data encryption request triggered by a user, and send the data encryption request to the server 200;
the server 200 is configured to select a plurality of first random numbers after receiving the data encryption request; wherein, the exclusive or value among the plurality of first random numbers is a constant value; determining a plurality of data blocks; processing a plurality of data blocks based on the plurality of first random numbers to obtain the plurality of processed data blocks; performing round function operation on the processed data blocks to obtain an output result; determining whether the number of times of round function operation is less than a set value; if the number of times of round function operation is less than the set value, returning to the step of determining a plurality of data blocks; if the times of round function operation are larger than or equal to the set value, determining a corresponding ciphertext based on the output result; wherein the determining the plurality of data blocks is performed based on the output result upon returning to performing the determining the plurality of data blocks.
As shown in fig. 4b, in the technical solution provided in this embodiment, the client 100 may be, but is not limited to, a desktop computer, a tablet computer, a smart phone, and a smart wearable device (e.g., a smart watch, glasses, etc.). The server 200 may be, but is not limited to, a single server, a virtual server deployed on a server or a cluster of servers, or a set of cloud computing-based computers (i.e., a cloud). Wherein the Cloud is composed of a large number of hosts or network servers based on Cloud Computing (Cloud Computing), which is a kind of distributed Computing, a super virtual computer composed of a group of loosely coupled computer sets.
The communication mode between the client 100 and the server 200 may be a wireless communication mode, and the wireless communication mode may be, but is not limited to, an ethernet, ZigBee, mobile network-based wireless communication mode, and the like; the network format of the mobile network may be, but is not limited to, any one of 2G (gsm), 2.5G (gprs), 3G (WCDMA, TD-SCDMA, UTMS), 4G (LTE), 4G + (LTE +), 5G, WiMax, and the like.
Here, it should be noted that: in the example shown in fig. 4a, the data encryption processing is performed at the server, but in other embodiments, the data encryption processing may also be performed at the client 100, that is, both the data encryption request and the data encryption processing are performed at the client, which is not limited in this embodiment. In addition, the contents of the steps in the data encryption processing system provided in the embodiment of the present application, which are not described in detail in the foregoing embodiments, may refer to the corresponding contents in the foregoing embodiments, and are not described herein again. In addition, the data encryption processing system provided in this embodiment of the present application may further include, in addition to the above steps, some or all of the other steps in the above embodiments, which may be specifically referred to corresponding contents in the above embodiments, and will not be described herein again.
Fig. 5 is a block diagram illustrating a data encryption processing apparatus according to an embodiment of the present application. The data encryption processing device can be an application software program installed in an electronic device (such as a server or a client shown in fig. 4 a), or can be tool software embedded in an operating system of the electronic device, and the like; in addition, the present invention may also be a hardware with an embedded program integrated on an electronic device, which is not limited in this embodiment of the present application. However, as a preferred example, it is preferable to select the data encryption processing apparatus provided in the embodiment of the present application as a software. As shown in fig. 5, the data encryption processing apparatus includes:
the receiving module 21 is configured to select a plurality of first random numbers after receiving the data encryption request; wherein, the exclusive or value among the plurality of first random numbers is a constant value;
a determining module 22 for determining a plurality of data blocks;
a processing module 23, configured to process a plurality of data blocks based on the plurality of first random numbers to obtain a plurality of processed data blocks;
an operation module 24, configured to perform round function operation on the processed data blocks to obtain an output result;
the determining module 22 is further configured to determine whether the number of times of the round function operation is less than a set value; and further for returning to the step of determining the plurality of data blocks if the number of round function operations is less than the set value; if the times of round function operation are larger than or equal to the set value, determining a corresponding ciphertext based on the output result; wherein the determining the plurality of data blocks is performed based on the output result upon returning to performing the determining the plurality of data blocks.
Here, it should be noted that: the data encryption processing apparatus provided in this embodiment may implement the technical solution described in the data encryption processing method embodiment shown in fig. 2, and the specific implementation principle of each module or unit may refer to the corresponding content in the data encryption processing method embodiment shown in fig. 2, which is not described herein again. In addition, the data encryption processing apparatus provided in this embodiment may further include, in addition to the above steps, other parts or all of the steps in the above embodiments, and for details, reference may be made to corresponding contents in the above embodiments, and details are not described here again.
Fig. 6 shows a schematic structural diagram of an electronic device according to an embodiment of the present application. As shown in fig. 6, the electronic apparatus includes: a memory 31 and a processor 32. Wherein the memory 31 is configured to store one or more computer instructions; the processor 32 is coupled to the memory 31 for one or more computer instructions (e.g., computer instructions implementing data storage logic) for implementing the steps in the data encryption processing method embodiment shown in fig. 2.
The memory 31 may be implemented by any type or combination of volatile or non-volatile memory devices, such as Static Random Access Memory (SRAM), electrically erasable programmable read-only memory (EEPROM), erasable programmable read-only memory (EPROM), programmable read-only memory (PROM), read-only memory (ROM), magnetic memory, flash memory, magnetic or optical disks.
Further, as shown in fig. 6, the electronic device further includes: communication components 33, power components 34, and audio components 35. Only some of the components are schematically shown in fig. 6, and the electronic device is not meant to include only the components shown in fig. 6.
Yet another embodiment of the present application provides a computer program product (not shown in any figure of the drawings). The computer program product comprises computer programs or instructions which, when executed by a processor, cause the processor to carry out the steps in the above-described data processing method embodiments.
Accordingly, the present application further provides a computer-readable storage medium storing a computer program, where the computer program can implement the steps or functions of the data processing method provided in the foregoing embodiments when executed by a computer.
Through the above description of the embodiments, those skilled in the art will clearly understand that each embodiment can be implemented by software plus a necessary general hardware platform, and certainly can also be implemented by hardware. With this understanding in mind, the above-described technical solutions may be embodied in the form of a software product, which can be stored in a computer-readable storage medium such as ROM/RAM, magnetic disk, optical disk, etc., and includes instructions for causing a computer device (which may be a personal computer, a server, or a network device, etc.) to execute the methods described in the embodiments or some parts of the embodiments.
Finally, it should be noted that: the above embodiments are only used to illustrate the technical solutions of the present application, and not to limit the same; although the present application has been described in detail with reference to the foregoing embodiments, it should be understood by those of ordinary skill in the art that: the technical solutions described in the foregoing embodiments may still be modified, or some technical features may be equivalently replaced; and such modifications or substitutions do not depart from the spirit and scope of the corresponding technical solutions in the embodiments of the present application.
Claims (10)
1. A data encryption processing method, comprising:
after a data encryption request is received, a plurality of first random numbers are selected; wherein, the exclusive or value among the plurality of first random numbers is a constant value;
determining a plurality of data blocks;
processing a plurality of data blocks based on the plurality of first random numbers to obtain the plurality of processed data blocks;
performing round function operation on the processed data blocks to obtain an output result;
determining whether the number of times of round function operation is less than a set value;
if the number of times of round function operation is less than the set value, returning to the step of determining a plurality of data blocks; if the times of round function operation are larger than or equal to the set value, determining a corresponding ciphertext based on the output result; wherein the determining the plurality of data blocks is performed based on the output result upon returning to performing the determining the plurality of data blocks.
2. The method of claim 1, wherein processing a plurality of data blocks based on the plurality of first random numbers to obtain the processed plurality of data blocks comprises:
determining at least one data block to be processed in the plurality of data blocks;
respectively acquiring the sequence number of each data block in the at least one data block;
selecting a first random number from the plurality of first random numbers for each data block in the at least one data block as a target random number according to the sequence number;
and performing exclusive-or operation on each data block in the at least one data block and the corresponding target random number to obtain the at least one processed data block.
3. The method of claim 2, wherein selecting a first random number from the plurality of first random numbers for one of the at least one data block as a target random number according to the sequence number comprises:
utilizing the serial number of the data block to carry out the remainder on the number of the first random numbers;
and selecting one first random number from the plurality of first random numbers as the target random number according to a remainder value obtained by remainder.
4. The method according to any one of claims 1 to 3, wherein the plurality of data blocks have a first type of data block and a second type of data block; wherein the second type data blocks are used for participating in synthetic permutation in round function operation; and
performing round function operation on the processed data blocks to obtain an output result, wherein the round function operation comprises the following steps:
encoding the processed second type data block to obtain an encoded second type data block;
synthesizing and replacing the encoded second-class data block and a round key corresponding to the current round function operation to obtain a first output value;
obtaining an intermediate block based on the processed first type data block and the first output value;
and taking the processed second class data block and the intermediate block as an output result of the current round function operation.
5. The method of claim 4, wherein encoding the processed second-class data block to obtain an encoded second-class data block comprises:
acquiring a pre-generated reversible affine transformation and a diagonal matrix,
and coding the processed second-class data block by using the reversible affine transformation and the diagonal matrix to obtain a coded second-class data block.
6. The method of claim 5, wherein performing a synthesis and replacement on the encoded second-class data blocks and the round key corresponding to the current round function operation to obtain a first output value comprises:
generating a plurality of lookup tables according to the round key;
determining a plurality of blocks based on the encoded second class data blocks;
respectively taking the plurality of blocks as the input of each lookup table in the plurality of lookup tables, and executing the plurality of lookup tables to obtain a plurality of corresponding second output values;
and carrying out XOR operation on the plurality of second output values to obtain the first output value.
7. The method of claim 6, wherein generating a plurality of look-up tables based on the round keys comprises:
determining a first transformation matrix;
generating a second random number and a second transformation matrix;
generating the plurality of lookup tables based on the round key, the second random number, the first transformation matrix, and the second transformation matrix.
8. The method of any of claims 1 to 3, wherein determining the plurality of data blocks after receiving the data encryption request comprises:
determining data to be encrypted based on the encryption request;
and splitting the data to obtain a plurality of data blocks with equal size.
9. A data encryption processing system, comprising:
the client is used for responding to a data encryption request triggered by a user and sending the data encryption request to the server;
the server is used for selecting a plurality of first random numbers after receiving the data encryption request; wherein, the exclusive or value among the plurality of first random numbers is a constant value; determining a plurality of data blocks; processing a plurality of data blocks based on the plurality of first random numbers to obtain the plurality of processed data blocks; performing round function operation on the processed data blocks to obtain an output result; determining whether the number of times of round function operation is less than a set value; if the number of times of round function operation is less than the set value, returning to the step of determining a plurality of data blocks; if the times of round function operation are larger than or equal to the set value, determining a corresponding ciphertext based on the output result; wherein the determining the plurality of data blocks is performed based on the output result upon returning to performing the determining the plurality of data blocks.
10. An electronic device, comprising: a memory and a processor, wherein,
the memory for storing one or more computer programs;
the processor, coupled with the memory, to execute the one or more computer programs stored in the memory to implement the steps of the method of any of claims 1-8.
Priority Applications (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN202210185245.0A CN114254372B (en) | 2022-02-28 | 2022-02-28 | Data encryption processing method and system and electronic equipment |
Applications Claiming Priority (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN202210185245.0A CN114254372B (en) | 2022-02-28 | 2022-02-28 | Data encryption processing method and system and electronic equipment |
Publications (2)
| Publication Number | Publication Date |
|---|---|
| CN114254372A CN114254372A (en) | 2022-03-29 |
| CN114254372B true CN114254372B (en) | 2022-08-05 |
Family
ID=80800053
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| CN202210185245.0A Active CN114254372B (en) | 2022-02-28 | 2022-02-28 | Data encryption processing method and system and electronic equipment |
Country Status (1)
| Country | Link |
|---|---|
| CN (1) | CN114254372B (en) |
Citations (3)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN109450632A (en) * | 2019-01-11 | 2019-03-08 | 西安电子科技大学 | Key recovery method based on whitepack block cipher CLEFIA analysis |
| CN111884794A (en) * | 2020-07-13 | 2020-11-03 | 广州安研信息科技有限公司 | SM4 white box implementation method based on interference wheel and external coding |
| CN113111317A (en) * | 2021-04-20 | 2021-07-13 | 西安电子科技大学 | Software tampering detection method based on white-box CLEFIA encryption method |
-
2022
- 2022-02-28 CN CN202210185245.0A patent/CN114254372B/en active Active
Patent Citations (3)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN109450632A (en) * | 2019-01-11 | 2019-03-08 | 西安电子科技大学 | Key recovery method based on whitepack block cipher CLEFIA analysis |
| CN111884794A (en) * | 2020-07-13 | 2020-11-03 | 广州安研信息科技有限公司 | SM4 white box implementation method based on interference wheel and external coding |
| CN113111317A (en) * | 2021-04-20 | 2021-07-13 | 西安电子科技大学 | Software tampering detection method based on white-box CLEFIA encryption method |
Non-Patent Citations (2)
| Title |
|---|
| Cryptanalysis of Two White-Box Implementations of the SM4 Block Cipher;Jingyu Li等;《International Conference on Information Security》;20210927;第54-69页 * |
| SM4 算法的一种新型白盒实现;姚思等;《密码学报》;20200615;第358-372页 * |
Also Published As
| Publication number | Publication date |
|---|---|
| CN114254372A (en) | 2022-03-29 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| US8966279B2 (en) | Securing the implementation of a cryptographic process using key expansion | |
| US8428251B2 (en) | System and method for stream/block cipher with internal random states | |
| US7783046B1 (en) | Probabilistic cryptographic key identification with deterministic result | |
| CN110235409A (en) | Use the protected RSA signature of homomorphic cryptography or the method for decryption | |
| CN113098675B (en) | Binary data encryption system and method based on polynomial complete homomorphism | |
| HK1258579A1 (en) | Fast format-preserving encryption for variable length data | |
| WO2019114122A1 (en) | Encryption method for login information, device, electronic device, and medium | |
| CN108809626A (en) | A kind of whitepack SM4 cryptographic algorithms scheme and system | |
| EP4075716B1 (en) | Method and apparatus for encrypting and decrypting and reading and writing messages, computer device, and storage medium | |
| CN103119888A (en) | Apparatus and method for block cipher processing in an insecure environment | |
| CN109450632B (en) | Key recovery method based on white-box block cipher CLEFIA analysis | |
| CN105024803A (en) | Behavioral fingerprint in a white-box implementation | |
| CN108494546A (en) | A kind of whitepack encryption method, device and storage medium | |
| CN114117490A (en) | Pytorch model encryption method, system and device based on AES algorithm | |
| CN105184115A (en) | Method For Including An Implicit Integrity Or Authenticity Check Into A White-box Implementation | |
| CN110505054A (en) | A kind of data processing method based on dynamic whitepack, device and equipment | |
| CN105721134B (en) | It is realized using the single whitepack with multiple external encodes | |
| Luo et al. | Cryptanalysis of a chaotic block cryptographic system against template attacks | |
| CN119496603B (en) | Parallel ordering method and system for secret state data based on isomorphic encryption | |
| CN114254372B (en) | Data encryption processing method and system and electronic equipment | |
| RU2188513C2 (en) | Method for cryptographic conversion of l-bit digital-data input blocks into l-bit output blocks | |
| CN115170380B (en) | A layered image scrambling encryption method based on chaotic mapping | |
| KR102780416B1 (en) | Whitebox cryptographic method and device based on block cipher mode of operation using one-way function | |
| CN115622745B (en) | Encryption method, device, terminal device and computer-readable storage medium | |
| CN109714152B (en) | White-box AES encryption method based on large affine coding |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| PB01 | Publication | ||
| PB01 | Publication | ||
| SE01 | Entry into force of request for substantive examination | ||
| SE01 | Entry into force of request for substantive examination | ||
| GR01 | Patent grant | ||
| GR01 | Patent grant |