CN112272088A - Auditable signature method based on multiple secure parties and related components - Google Patents
Auditable signature method based on multiple secure parties and related components Download PDFInfo
- Publication number
- CN112272088A CN112272088A CN202011155366.8A CN202011155366A CN112272088A CN 112272088 A CN112272088 A CN 112272088A CN 202011155366 A CN202011155366 A CN 202011155366A CN 112272088 A CN112272088 A CN 112272088A
- Authority
- CN
- China
- Prior art keywords
- participant
- trust
- information
- participants
- credibility
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Pending
Links
Images
Classifications
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/08—Key distribution or management, e.g. generation, sharing or updating, of cryptographic keys or passwords
- H04L9/0816—Key establishment, i.e. cryptographic processes or cryptographic protocols whereby a shared secret becomes available to two or more parties, for subsequent use
- H04L9/085—Secret sharing or secret splitting, e.g. threshold schemes
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F21/60—Protecting data
- G06F21/602—Providing cryptographic facilities or services
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F21/60—Protecting data
- G06F21/62—Protecting access to data via a platform, e.g. using keys or access control rules
- G06F21/6218—Protecting access to data via a platform, e.g. using keys or access control rules to a system of files or objects, e.g. local or distributed file system or database
- G06F21/6245—Protecting personal data, e.g. for financial or medical purposes
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F21/60—Protecting data
- G06F21/64—Protecting data integrity, e.g. using checksums, certificates or signatures
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/04—Network architectures or network communication protocols for network security for providing a confidential data exchange among entities communicating through data packet networks
- H04L63/0407—Network architectures or network communication protocols for network security for providing a confidential data exchange among entities communicating through data packet networks wherein the identity of one or more communicating identities is hidden
- H04L63/0414—Network architectures or network communication protocols for network security for providing a confidential data exchange among entities communicating through data packet networks wherein the identity of one or more communicating identities is hidden during transmission, i.e. party's identity is protected against eavesdropping, e.g. by using temporary identifiers, but is known to the other party or parties involved in the communication
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/08—Key distribution or management, e.g. generation, sharing or updating, of cryptographic keys or passwords
- H04L9/0861—Generation of secret information including derivation or calculation of cryptographic keys or passwords
- H04L9/0866—Generation of secret information including derivation or calculation of cryptographic keys or passwords involving user or device identifiers, e.g. serial number, physical or biometrical information, DNA, hand-signature or measurable physical characteristics
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/08—Key distribution or management, e.g. generation, sharing or updating, of cryptographic keys or passwords
- H04L9/0891—Revocation or update of secret information, e.g. encryption key update or rekeying
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/32—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials
- H04L9/3247—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials involving digital signatures
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/32—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials
- H04L9/3297—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials involving time stamps, e.g. generation of time stamps
Landscapes
- Engineering & Computer Science (AREA)
- Computer Security & Cryptography (AREA)
- Computer Networks & Wireless Communication (AREA)
- Theoretical Computer Science (AREA)
- Signal Processing (AREA)
- Bioethics (AREA)
- General Engineering & Computer Science (AREA)
- Health & Medical Sciences (AREA)
- General Health & Medical Sciences (AREA)
- Computer Hardware Design (AREA)
- Software Systems (AREA)
- Physics & Mathematics (AREA)
- General Physics & Mathematics (AREA)
- Computing Systems (AREA)
- Medical Informatics (AREA)
- Databases & Information Systems (AREA)
- Storage Device Security (AREA)
Abstract
The application discloses a secure multiparty-based auditable signature method, wherein secret mark information of participants is updated every other preset period before responding to the behavior that the participants sign based on the secure multiparty, the cracking difficulty of the secret mark information is increased, the security of user privacy data contained in the secret mark information is improved, a trust matrix with a time stamp is generated based on the credibility degree of each participant, credibility evaluation is carried out on each participant so as to realize identification of the identities of the participants, and if the identities of the participants are judged to be credible according to trust vectors corresponding to the participants, signature processing is allowed to be carried out according to a secret key and the secret mark information. And if the signature request is not credible, the current signature request is rejected, so that the safety and reliability of the signature process and the safety of the user privacy information can be improved. The application also provides an auditable signature device and equipment based on the security multiple parties and a readable storage medium, and the auditable signature device and equipment have the beneficial effects.
Description
Technical Field
The present application relates to the field of computer software technologies, and in particular, to a secure multiparty based auditable signature method, apparatus, device, and readable storage medium.
Background
Secure multi-party computing (SMC) is a very active academic field in cryptography, mainly used to solve the problem of personal privacy protection among a group of mutually untrusted participants, and it can solve some troublesome problems of participation of multiple people together without a trusted third party, and it can ensure that multiple mutually untrusted participants can complete computing tasks together without revealing their respective privacy information. The safe multi-party calculation plays an important role in data mining, statistical analysis, privacy protection, confidential electronic voting and the like, and has very important practical significance.
However, in actual execution, participants of the secure multi-party protocol have honest, semi-honest and malicious three types, and a non-honest participant may influence normal execution of the protocol in the execution process, induce conditions such as secret data leakage, and the like, and have an important influence on the secure operation of the system.
Therefore, how to avoid the negative influence of the non-honest participants on the protocol execution process and guarantee the security of the private data is an urgent problem to be solved by the technical personnel in the field.
Disclosure of Invention
The application aims to provide a safe multiparty-based auditable signature method, which can avoid the negative influence of non-honest participants on the protocol execution process and ensure the safety of private data; it is another object of the present application to provide a secure multiparty based auditable signature device, apparatus and a readable storage medium.
In order to solve the above technical problem, the present application provides a secure multiparty-based auditable signature method, including:
generating a key based on a secret sharing mechanism;
updating the secret mark information of the participants at intervals of a preset period, and generating a trust matrix with a time stamp based on the credibility of each participant;
determining a trust vector of the participant from the trust matrix, and judging whether the participant is trusted according to the trust vector;
if the key is judged to be credible, allowing the participant to carry out signature processing according to the key and the secret mark information; and if the secret mark information is judged to be not credible, the participant is prohibited from performing signature processing according to the secret key and the secret mark information.
Optionally, generating a time-stamped trust matrix based on the trustworthiness of each of the participants includes:
evaluating the identity credibility of the participant in the preset period to serve as a direct trust evaluation value;
evaluating the credibility of the interactive information between the participant and other participants in the preset period as an indirect trust evaluation value;
generating a credibility measurement vector of the participant in the preset period according to the direct credibility evaluation value and the indirect credibility evaluation value to serve as a credibility vector;
and forming a matrix by the trust vectors corresponding to all participants in the preset period, and taking the matrix as a trust matrix.
Optionally, the evaluating identity credibility of the participant as the direct trust evaluation value includes:
acquiring the identity to-be-verified information of the participant; the information to be verified is obtained by respectively carrying out discrete logarithm encryption processing on the information to be verified according to each secret information of the participants and then summing the information to be verified;
acquiring the sum of the secret information of the participant, and performing discrete logarithm encryption processing on the sum of the secret information to serve as identity authentication information;
matching and verifying the identity information to be verified and the identity verification information to generate an identity verification result;
and according to a preset rule, assigning the identity credibility of the participant as the direct trust evaluation value according to the identity verification result.
Optionally, the evaluating the credibility of the interaction information between the participant and each other participant as an indirect trust evaluation value includes:
matching and verifying the broadcast information between the participant and other participants to generate a broadcast verification result;
and assigning a value to the interactive information credibility of the participant according to a preset rule and the broadcast verification result to serve as the indirect trust evaluation value.
Optionally, before determining the trust vector of the participant from the trust matrix, further comprising:
encrypting and storing the trust matrix into a blockchain;
if receiving the checking application, downloading the trust matrix of the corresponding period from the block chain;
and sending the downloaded trust matrix and the group private key of the corresponding period to an applicant.
Optionally, encrypting and storing the trust matrix into a blockchain includes:
determining a trusted participant in the participants as an agent;
controlling the agent to encrypt and store the trust matrix in a blockchain;
correspondingly, if a checking application is received, downloading the trust matrix of the corresponding period from the block chain, including: and the agent receives the checking application and downloads the trust matrix of the corresponding period and the corresponding group private key from the block chain.
Optionally, determining a trusted participant among the participants as an agent includes:
the participants construct vectors from a preset set;
calling a system public key to encrypt the vector as a first competition value;
receiving a competition value sent by a neighbor participant as a second competition value;
determining the larger one of the first competition value and the second competition value as a third competition value;
sending the third competition value to another neighbor participant according to a transmission sequence to carry out vector value comparison until the maximum vector is determined, and taking the maximum vector as the maximum competitor;
and taking the participant corresponding to the maximum competitor as the agent.
The application also provides an auditable signature device based on secure multiple parties, the device including:
a key generation unit configured to generate a key based on a secret sharing mechanism;
the trust measurement unit is used for updating the secret mark information of the participants at intervals of a preset period and generating a trust matrix with a time stamp based on the credibility of each participant;
the credibility judgment unit is used for determining the credibility vector of the participant from the credibility matrix and judging whether the participant is credible according to the credibility vector; if the first unit is judged to be credible, triggering the first unit; if the judgment result is not credible, triggering a second unit;
the first unit is used for releasing the signing processing of the participant according to the secret key and the secret mark information;
the second unit is used for forbidding the participant to carry out signature processing according to the secret key and the secret mark information.
The application also provides an auditable signature device based on secure multiple parties, comprising:
a memory for storing a computer program;
a processor for implementing the steps of the secure multi-party based auditable signature method when executing the computer program.
The present application also provides a readable storage medium having stored thereon a program which, when executed by a processor, performs the steps of the secure multi-party based auditable signature method.
According to the safe multiparty-based auditable signature method, before responding to the behavior that participants sign based on the safe multiparty, the secret mark information of the participants is updated at intervals of a preset period, the cracking difficulty of the secret mark information is increased, the safety of user privacy data contained in the secret mark information is improved, a trust matrix with a time stamp is generated based on the credibility of each participant, credibility evaluation is carried out on each participant, so that the identities of the participants such as honesty, semi-honesty, maliciousness and the like are distinguished, and if the identities of the participants are judged to be credible according to the trust vectors corresponding to the participants, signature processing is allowed to be carried out according to keys and the secret mark information. And if the signature request is not credible, the current signature request is rejected, so that the safety and reliability of the signature process and the safety of the user privacy information can be improved.
The application also provides an auditable signature device and equipment based on multiple safe parties and a readable storage medium, which have the beneficial effects and are not described in detail herein.
Drawings
In order to more clearly illustrate the embodiments of the present application or the technical solutions in the prior art, the drawings needed to be used in the description of the embodiments or the prior art will be briefly introduced below, it is obvious that the drawings in the following description are only embodiments of the present application, and for those skilled in the art, other drawings can be obtained according to the provided drawings without creative efforts.
FIG. 1 is a flow chart of a secure multiparty based auditable signature method provided by an embodiment of the present application;
FIG. 2 is a schematic diagram illustrating a confidence level measurement method according to an embodiment of the present disclosure;
fig. 3 is a schematic diagram illustrating a secure multi-party audit signature implementation based on a block chain according to an embodiment of the present application;
FIG. 4 is a block diagram of a secure multiparty based auditable signature device according to an embodiment of the present application;
fig. 5 is a schematic structural diagram of a secure multiparty-based auditable signature device according to an embodiment of the present application.
Detailed Description
The core of the application is to provide a safe multiparty-based auditable signature method, which can avoid the negative influence of non-honest participants on the protocol execution process and ensure the safety of private data; at the other core of the application, the auditable signature device, equipment and a readable storage medium based on the secure multi-party are provided.
In order to make the objects, technical solutions and advantages of the embodiments of the present application clearer, the technical solutions in the embodiments of the present application will be clearly and completely described below with reference to the drawings in the embodiments of the present application, and it is obvious that the described embodiments are some embodiments of the present application, but not all embodiments. All other embodiments, which can be derived by a person skilled in the art from the embodiments given herein without making any creative effort, shall fall within the protection scope of the present application.
Under secure multi-party computing, it is assumed that in a distributed network, there is a group of participants P who are not trusted by each other1,P2,…,Pn. Suppose that each participant possesses a secret x1,x2,…,xnAnd they secretly input their respective secret data and cooperatively calculate f (x)1,x2,…,xn)→(y1,y2,…,yn). Finally, each participant can get its own output yiIn the process, each participant can not obtain any information of other participants, so that under the condition of no trusted third party, the safe multi-party calculation solves the problem that some participants share one anotherThe problem of the same participation has very important practical significance.
In actual implementation, however, there are three types of truthful, semi-truthful and malicious participants to the participants of the secure multiparty agreement. The semi-honest and malicious participants bring certain troubles to the execution of the protocol, and the semi-honest and malicious participants can participate or initiate certain behaviors which influence the running of the protocol, so that the security of private data is influenced.
In order to improve the credibility of the participants, the method for realizing trust evaluation aiming at the behaviors of the participants in the secure multi-party signature is provided, and a reliable foundation is laid for guaranteeing the safety and the reliability of the secure multi-party computing execution process.
Referring to fig. 1, fig. 1 is a flowchart of an auditable signature method based on multiple secure parties provided in this embodiment, where the method mainly includes the following steps:
step s110, generating a secret key based on a secret sharing mechanism;
the secret sharing mechanism may specifically adopt an Asmuth-Bloom secret sharing scheme, and the Asmuth-Bloom secret sharing scheme has the advantages of small calculation amount and high efficiency.
For further understanding, a specific implementation step is introduced herein, and specifically includes the following steps:
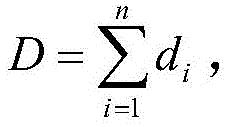
(1) initializing data;
suppose Pi(i ═ 1,2, …, n) is the set of n participants, t is the threshold value, g is the generator over the finite field gf (p), p and q are two large prime numbers, and satisfy q/(p-1), di(i-1, 2, …, n) is a set of strictly monotonically increasing positive integer sequences, q and d satisfy the Asmuth-Bloom scheme, the message to be signed is m,n, t, g, p, q, D and D are disclosed.
(2) Generating secret mark information;
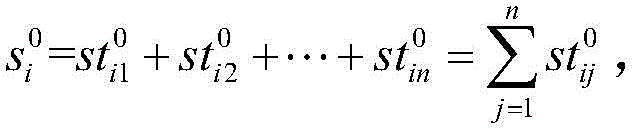
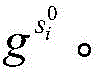
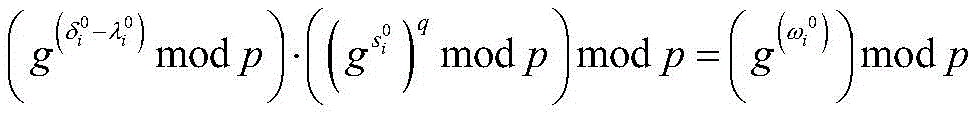
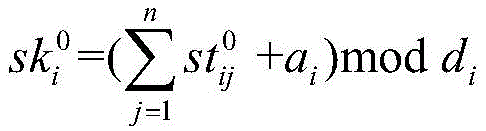
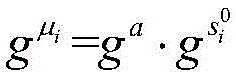
each participant PiRandomly selecting secret mark information meeting Asmuth-Bloom schemeComputing secret tagsAnd will beIs sent to Pj(j ═ 1,2, …, n), and PiRetentionBroadcastingAnd
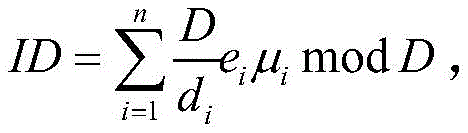
(3) generating identity label information;
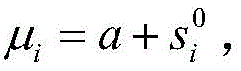
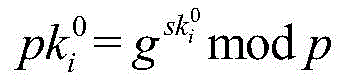
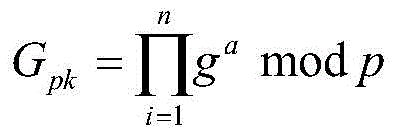
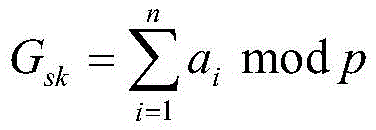
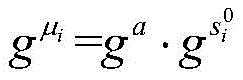
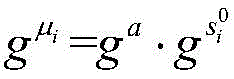
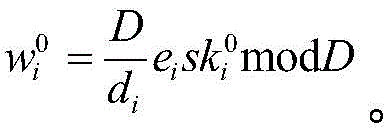
participant PiSelecting a random number aiCalculatingAnd broadcastAnd ga. Here, letIDi=μi(moddi) Then it has the only solution:wherein eiSatisfy the requirement ofThus, the authentication information of the participant is (ID, μ)i)。
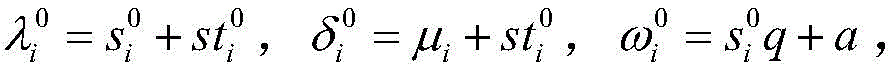
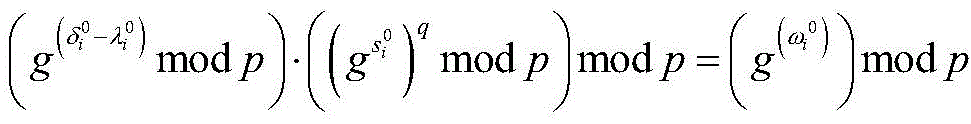
(4) Calculating verification information;
is provided withAccording to broadcast informationAnd gaIf, ifThen participant Pj(j ≠ i) Accept participant PiTransmitted information
(5) Generating a secret key;
it should be noted that, in this embodiment, only the key generation process is described as an example, and hereinafter, the abbreviation and the substitute name in the key generation process are used, and other key generation manners can refer to the description of this embodiment, and are not described herein again.
Step s120, updating the secret mark information of the participants at intervals of a preset period, and generating a trust matrix with a time stamp based on the credibility of each participant;
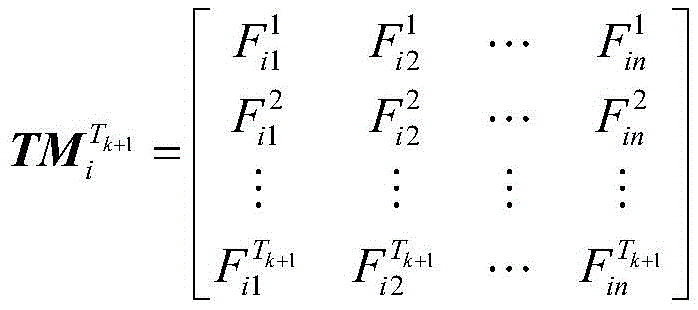
in order to ensure the credibility of participants, the method and the device establish a dynamic credibility evaluation mechanism for each participant, dynamically update secret mark information of the participants at intervals of a preset period, generate a Trust vector with a time stamp as a credibility basis of the participants, and form a Trust Matrix (TM) by the Trust vector corresponding to each participant. The trust vector corresponding to each participant in the trust matrix represents the credibility of the participant, and the credibility of the participants is quantized and formed into the trust matrix, so that the credibility of each participant is more visual.
The trust matrix is provided with a timestamp, the timestamp means the generation time (or effective time) of the trust matrix, the trust matrix is effective in the effective time of the trust matrix, and the trust matrix is updated at preset intervals, so that the trust matrix is ensured to be continuously updated along with the behavior of the participants, and the information effectiveness of the trust matrix is ensured.
The storage position of the generated trust matrix is not limited in the embodiment, and the generated trust matrix needs to be stored in a safe space as much as possible, so that the trust matrix is prevented from being tampered by illegal personnel, and the safety and reliability of the trust matrix are guaranteed.
Specifically, the specific implementation process of generating the trust matrix with the timestamp based on the trustworthiness of each participant is not limited in this embodiment, that is, the specific reference amount and the measurement mode when measuring the trustworthiness are not limited in this embodiment, and may be set according to the requirement of actual participant auditing, for example, the identity and the historical behavior of the participants may be evaluated, for example, whether the current interaction information sent by the first participant to the second participant is consistent with the received interaction information broadcast by the second participant is determined, and whether an illegal behavior exists in the historical signature record of the participants is determined.
Step s130, determining a trust vector of the participant from the trust matrix, and judging whether the participant is trusted according to the trust vector;
the trust matrix comprises trust vectors of all participants in the secure multi-party, the trust vector corresponding to the participant to be audited and signed is determined from the trust matrix, the trust vector represents a trust value obtained by credibility evaluation of the participant, the credibility of the participant can be judged according to the trust vector, the specific judgment credibility or non-credibility standard is not limited, and corresponding setting can be carried out according to the expression form of the trust vector and the actual security audit requirement, and details are not repeated herein.
If the determination is reliable, go to step s 140; if the determination is not authentic, step s150 is executed.
Step s140 allows the participant to perform a signature process based on the key and the secret tag information.
If the participant is judged to be credible, the participant is allowed to perform signature processing based on the secret key and the secret mark information by multiple parties, and the participant is allowed to perform signature processing only when the participant is credible, so that the safety and the reliability of the signature process can be guaranteed, the interference of an untrusted user on the signature process can be avoided, and the safety of user privacy data can be powerfully guaranteed.
Specifically, after determining that the participant is trusted, the specific implementation step of the participant performing signature processing according to the secret key and the secret mark information is not limited in this embodiment, and may be implemented according to an implementation manner in the related art, and is not described herein again.
And step s150, prohibiting the participant from performing signature processing according to the secret key and the secret mark information.
If the participant is determined to be not trusted, the participant is prohibited from performing signature processing according to the secret key and the secret mark information, the current signature request is rejected, and further, security early warning prompt information can be generated to prompt that the current user is not trusted, and the like.
Based on the above description, in the auditable signature method based on secure multiple parties provided in this embodiment, before responding to the behavior of a participant to perform signature based on secure multiple parties, the secret mark information of the participant is updated every preset period, the difficulty in cracking the secret mark information is increased, the security of the user privacy data included in the secret mark information is improved, a trust matrix with a time stamp is generated based on the trustworthiness degree of each participant, trust evaluation is performed on each participant, so that identification (honesty, semi-honesty and malicious) of the participant is realized, and if the identity of the participant is determined to be trustworthy according to the trust vector corresponding to the participant, the participant is allowed to perform signature processing according to the secret key and the secret mark information. And if the signature request is not credible, the current signature request is rejected, so that the safety and reliability of the signature process and the safety of the user privacy information can be improved.
The specific implementation manner of generating the trust matrix with the timestamp based on the trustworthiness degree of each participant in the foregoing embodiment is not limited, and in this embodiment, a measurement manner for the trustworthiness degree of the participant is provided mainly for the generation manner of the trust matrix, which is specifically as follows:
the process of generating a time-stamped trust matrix based on the trustworthiness of each participant may specifically include the following steps:
(1) evaluating the identity credibility of the participant in a preset period to serve as a direct trust evaluation value;
the credibility evaluation mainly comprises two aspects, namely direct credibility and indirect credibility, wherein the direct credibility refers to the credibility of the identity of the participants, and the indirect credibility refers to the credibility of the information interaction between the participants.
In this embodiment, the evaluation means for the identity credibility is not limited, and optionally, one implementation manner for evaluating the identity credibility is as follows:
(1.1) acquiring identity to-be-verified information of a participant; the information to be verified is obtained by respectively carrying out discrete logarithm encryption processing on the information to be verified according to various secret information of participants and then summing the information to be verified;
optionally, the secret information may specifically include: a secret token generated based on a secret sharing mechanism, and a random number.
(1.2) acquiring the sum of each secret information of the participant, and performing discrete logarithm encryption processing on the sum of each secret information to serve as identity authentication information;
(1.3) matching and verifying the identity information to be verified and the identity verification information to generate an identity verification result;
and (1.4) according to a preset rule, assigning a value to the identity credibility of the participant as a direct trust evaluation value according to the identity verification result.
For example, the trustworthiness of an identity may be represented by an equationAnd (6) judging. a is a random number and a is a random number,is a secret mark, a andthe information randomly selected by each member is secret information which cannot be directly obtained by an attacker or other participants and cannot be leaked, so that encryption processing is required, and gaAndrespectively shows that an encryption method is a discrete logarithm problem and is a problem which is recognized at present and cannot be cracked, namely, no one except the person can obtain a and a through the encryption processingAnd the identity of the participant can be verified, and the security of the private information is reliably guaranteed. Because a andthe information randomly selected by each member is only known by the member, an attacker is not known, and only the member knows the correct a andby passingVerification, hereCan prove a andthe member himself, not the attacker, forges. If the attacker forges the information, the equationWill not be true, it can be proven that the member is not the person himself, and the identity is not trusted.
In this embodiment, only the above equation verification form is described as an example, and other encryption manners and other verification manners based on the present application can also implement the credibility verification of the participant identity, which can be referred to the above description and are not described herein again.
(2) Evaluating the credibility of the information interaction between the participant and other participants in a preset period as an indirect trust evaluation value;
the mutual information refers to mutual information exchanged between the participants for generating the secret share. Since the information may be attacked and tampered during the transmission process, the authenticity of the mutual information needs to be verified to ensure the reliability of the signature processing process between the participants. Such as each participant PiRandomly selecting secret mark informationThat is to say PiN pieces of information are selected, and each person sends one information to other n-1 participantsIs sent to Pj(j ═ 1,2, …, n), hereNamely, the mutual information, the credibility of the mutual information needs to be verified in the embodiment for verification of the credibility of the mutual information.
However, a specific implementation manner of verifying the credibility of the mutual information in this embodiment is not limited, and optionally, a specific implementation manner of evaluating the credibility of the mutual information between the participant and each of the other participants specifically includes the following steps:
(2.1) matching and verifying the broadcast information between the participant and other participants to generate a broadcast verification result;
and (2.2) according to a preset rule, assigning a value to the credibility of the interaction information of the participant as an indirect trust evaluation value according to the broadcast verification result.
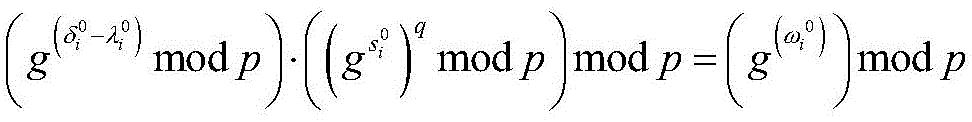
For example, the credibility of the interaction information between the participants can be determined by the equationAnd judging that if the two are the same, the verification is credible, and if the two are different, the verification is not credible. The relevant parameters in the equation can refer to the explanations in the above embodiments, and are not described in detail here.
(3) Generating a credibility measurement vector in a preset period of the participant according to the direct credibility evaluation value and the indirect credibility evaluation value, and taking the credibility measurement vector as a credibility vector;
(4) and forming a matrix by the trust vectors corresponding to all participants in a preset period to be used as a trust matrix.
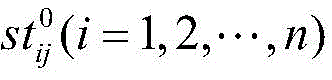
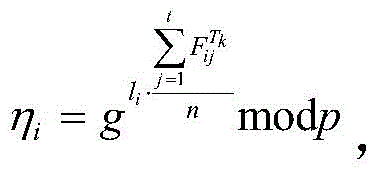
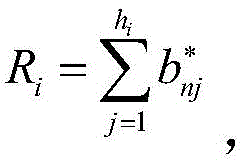
For example, as shown in fig. 2, a measure of the trustworthiness is constructed by constructing a trusted evaluation function, which mainly includes two aspects, namely direct trust and indirect trust. Direct trust refers to the credibility of the identity of the participants, and indirect trust refers to the credibility of the mutual information between the participants. WhereinIdentity trustworthiness by equalityJudging, the credibility of the mutual information is determined by the equationAnd (6) judging. The value is 1 when the equation is true, and 0 otherwise.
The trusted evaluation function is:where f (x) ═ x]For the rounding function, T is the update period. The trusted evaluation function consists of two parts, direct trust and indirect trust of the participants. f. ofDAs participant PiDirect trust evaluation at kth cycle, here IDi=μi(moddi)
Identity information IDi=μi(moddi) ID is and μiRelated, muiAre used to verify the identity of the participant. Direct trust in the evaluation is throughTo be evaluated.
Is the identity information of the participant. f. ofIAs participant PiThe indirect trust evaluation value at the k-th cycle. Direct trust fDAnd indirect trust fIThe values of (a) belong to the set a ═ {0,1},has a value range of
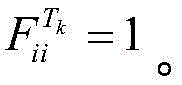
At this time, PiGenerating a trust vector TV from the evaluation result of the k period:
All participants P in the k periodiThe trust vectors of (i ═ 1,2, …, n) form the trust matrix TM, so the evaluation results for all participants at the k-th cycle are:
thus, at the k-th cycle, participant PiThe evaluation values for the other n-1 participants were:
Updating the matrix into the following matrix:
when the participant is not trusted (e.g., when the trusted evaluation function takes a value of 0, the criterion is adjustable), the participant cannot participate in the signature.
In the embodiment, credibility assessment of the participants is realized from two aspects of identity and interactive information, reliable and accurate credibility assessment of the participants is realized, the credibility measurement values form a trust matrix for auditing and tracing, and the reliability of the whole signature realization process is improved.
In order to further understand based on the above credibility evaluation method, a signature implementation method based on the above evaluation method is introduced in this embodiment.
The signature generation process is as follows:
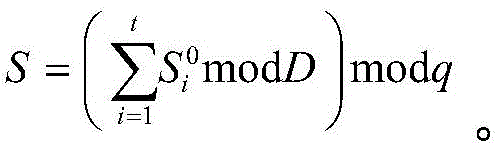
(3)Pi(i-1, 2, …, t) calculating a partial signatureSo that the participant's partial signature isHere, the
The signature verification process may specifically be: piUsing group public key GpkVerification of equation gS≡um·η·Gpkmodp. If the equality is true, the signature is valid, and if the equality is false, the signature is invalid.
Due to the existence of the mobile attack, an attacker can acquire the private key of the participant through a long-term stable attack. However, dynamically updating the keys of the participants can effectively prevent mobile attacks and improve security. The solution can keep the system public key unchanged in the whole updating process, and the function of accessing historical signature information by using the system public key is kept. Here, the update period is set to T.
After the update is completed, the participant can also generate a signature according to the above-described signature process.
In the above embodiment, the storage location of the trust matrix is not limited, and in order to improve the security of the trust matrix, a secure storage and acquisition method of the trust matrix is provided in this embodiment.
Specifically, before determining a trust vector of a participant from a trust matrix, encrypting and storing the trust matrix into a blockchain; if receiving the checking application, downloading the trust matrix of the corresponding period from the block chain; and sending the downloaded trust matrix and the group private key of the corresponding period to the applicant.
The block chain is a chain data structure formed by combining data blocks in a sequential connection mode according to a time sequence, and distributed accounts which cannot be falsified and counterfeited are guaranteed in a cryptographic mode.
In this embodiment, secure multiple parties and a block chain are combined, a trust matrix is stored in the block chain by using the characteristic that the block chain is not tampered as an audit basis, and an auditable and traceable trust mechanism is established to make the trust level more authentic and more reliable, as shown in fig. 3, a schematic diagram of secure multiple party audit signature implementation based on the block chain is shown.
In order to further improve the security of the process of storing the trust matrix into the blockchain, the process of encrypting the trust matrix and storing the trust matrix into the blockchain in the above steps can be specifically realized according to the following steps: determining trusted participants in all the participants as agents; the control agent encrypts and stores the trust matrix in the block chain; correspondingly, if a checking application is received, downloading the trust matrix of the corresponding period from the block chain, including: the agent receives the checking application and downloads the trust matrix of the corresponding period and the corresponding group private key from the blockchain.
The method comprises the steps that a participant selects an agent, the agent encrypts and stores a trust matrix into a block chain, when an applicant needs to check, the agent initiates an application to the agent and downloads the trust matrix of a corresponding period from the block chain, the agent sends a group private key of the corresponding period to the applicant, and the applicant can obtain an original trust matrix through decryption and verifies the original trust matrix. By reducing the number of contact participants of the trust matrix, the chance of tampering the trust matrix is reduced, and the security of the trust matrix is improved.
The agent is used as a key participant for storing the trust matrix, and the security and reliability of the agent need to be ensured. Optionally, one filtering rule is as follows:
the participants construct vectors from a preset set;
calling a system public key to encrypt the vector as a first competition value;
receiving a competition value sent by a neighbor participant as a second competition value;
determining the larger one of the first competition value and the second competition value as a third competition value;
sending the third competition value to another neighbor participant according to the transmission sequence to carry out vector value comparison until the maximum vector is determined, and taking the maximum vector as the maximum competitor;
and taking the participant corresponding to the largest competitor as the agent.
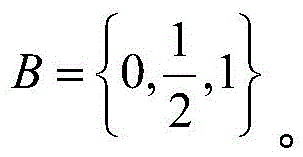
For example, each participant selects an agent through bid bidding. Each participant's secret bid yields a criterion H ═ H (H)1,h2,…,hn) N participants cooperate to calculate privacy and obtain respective bid hiAnd (4) sorting, and finally taking the highest bidder as a proxy to obtain the credible results of the participants.
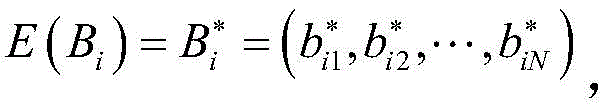
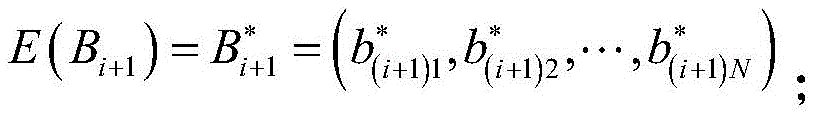
First, participant Pi(i ═ 1,2, …, N), agreeing on a corpus a ═ 1, N]Satisfy the following requirementsConstructing an N-dimensional vector B in the complete set A by each participanti=(bi1,bi2,…,bij,…,biN) Wherein for each j ∈ A, a definition is given
Second, PiEncrypting B with the System public KeyiTo obtainAnd will beTo Pi+1。Pi+1Receive PiTransmitted byAfter that, the following calculation is performed: pi+1According to Bi+1=(b(i+1)1,b(i+1)2,…,b(i+1)N) To obtainWherein for any j ∈ A there is
finally, participant Pi(i ═ 1,2, …, n), calculation formulaObtaining final bid ordering by using the highest bidder as proxy, and assuming that the highest bidder is Pr。
And then P isrAs a proxy, let Tthk(k ═ 1,2, …, n) cycle confidence evaluation matrixObtaining cipher text by system public key encryptionAnd carrying out Hash processing on the ciphertext to obtainAnd storing the finally obtained hash value into the block chain.
When required, participant PkOr other participants initiating requests to the agent, agent PrSending the group private key to applicant Pk,PkDownloading data from the blockchain and decrypting the data by using a private key to obtain a credible evaluation matrix
The agent can also update periodically to further promote the secure storage of data, which is not described herein again.
Based on the above description, the embodiment provides a block chain auditable signature scheme based on multiple secure parties, combines multiple secure parties with a block chain, establishes a credibility assessment mechanism to quantify the credibility of participants, and more objectively assesses the credibility of the participants. And by utilizing the characteristics that the block chain is not falsifiable and is public and transparent, the credible evaluation matrix is stored on the block chain to be used as a basis for verification, so that the functions of auditing and tracing are realized. A secure multi-party signature scheme is designed by adopting a secret sharing technology, the calculation amount is small, and the security is high.
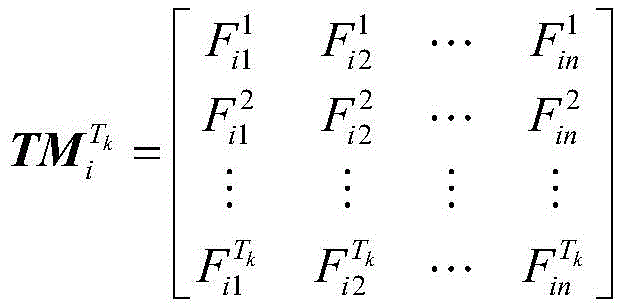
Referring to fig. 4, fig. 4 is a block diagram illustrating a structure of a secure multi-party based auditable signature device according to the present embodiment; the device mainly includes: a key generation unit 110, a trust measurement unit 120, a trust judgment unit 130, a first unit 140, and a second unit 150. The auditable signature device based on the secure multiple parties provided by the embodiment can be mutually compared with the auditable signature method based on the secure multiple parties.
The key generation unit 110 is mainly configured to generate a key based on a secret sharing mechanism;
the trust measurement unit 120 is mainly configured to update the secret tag information of the participants at intervals of a preset period, and generate a trust matrix with a timestamp based on the trustworthiness of each participant;
the credibility judgment unit 130 is mainly used for determining the credibility vector of the participant from the credibility matrix and judging whether the participant is credible according to the credibility vector; if the first unit is judged to be credible, triggering the first unit; if the judgment result is not credible, triggering a second unit;
the first unit 140 is mainly used for allowing the participant to perform signature processing according to the secret key and the secret mark information;
the second unit 150 is mainly used to prohibit the participant from performing signature processing based on the key and the secret tag information.
The embodiment provides an auditable signature device based on multiple secure parties, which mainly comprises: a memory and a processor.
Wherein, the memory is used for storing programs;
the processor is configured to execute the program to implement the steps of the secure multi-party based auditable signature method as described in the above embodiments, and in particular, reference is made to the above description of the secure multi-party based auditable signature method.
Referring to fig. 5, a schematic structural diagram of a secure multi-party based auditable signature device provided in this embodiment is shown, where the secure multi-party based auditable signature device may generate a relatively large difference due to different configurations or performances, and may include one or more processors (CPUs) 322 (e.g., one or more processors) and a memory 332, where the memory 332 stores one or more computer applications 342 or data 344. Memory 332 may be, among other things, transient or persistent storage. The program stored in memory 332 may include one or more modules (not shown), each of which may include a sequence of instructions operating on a data processing device. Still further, the central processor 322 may be configured to communicate with the memory 332 to execute a series of instruction operations in the storage medium 330 on the secure multi-party based auditable signing device 301.
The secure multi-party based auditable signing apparatus 301 may also include one or more power supplies 326, one or more wired or wireless network interfaces 350, one or more input-output interfaces 358, and/or one or more operating systems 341, such as Windows Server, Mac OS XTM, UnixTM, LinuxTM, FreeBSDTM, and the like.
The steps in the secure multi-party based auditable signing method described in figure 1 above can be implemented by the structure of the secure multi-party based auditable signing apparatus introduced in this embodiment.
The present embodiment discloses a readable storage medium, on which a program is stored, and when the program is executed by a processor, the steps of the secure multiparty based auditable signature method described in the above embodiments are implemented, and in particular, reference may be made to the description of the secure multiparty based auditable signature method in the above embodiments.
The readable storage medium may be a usb disk, a removable hard disk, a Read-Only Memory (ROM), a Random Access Memory (RAM), a magnetic disk or an optical disk, and various other readable storage media capable of storing program codes.
The embodiments are described in a progressive manner in the specification, each embodiment focuses on differences from other embodiments, and the same and similar parts among the embodiments are referred to each other. The device disclosed by the embodiment corresponds to the method disclosed by the embodiment, so that the description is simple, and the relevant points can be referred to the method part for description.
Those of skill would further appreciate that the various illustrative elements and algorithm steps described in connection with the embodiments disclosed herein may be implemented as electronic hardware, computer software, or combinations of both, and that the various illustrative components and steps have been described above generally in terms of their functionality in order to clearly illustrate this interchangeability of hardware and software. Whether such functionality is implemented as hardware or software depends upon the particular application and design constraints imposed on the implementation. Skilled artisans may implement the described functionality in varying ways for each particular application, but such implementation decisions should not be interpreted as causing a departure from the scope of the present application.
The steps of a method or algorithm described in connection with the embodiments disclosed herein may be embodied directly in hardware, in a software module executed by a processor, or in a combination of the two. A software module may reside in Random Access Memory (RAM), memory, Read Only Memory (ROM), electrically programmable ROM, electrically erasable programmable ROM, registers, hard disk, a removable disk, a CD-ROM, or any other form of storage medium known in the art.
The secure multiparty based auditable signature method, apparatus, device and readable storage medium provided by the present application are described in detail above. The principles and embodiments of the present application are explained herein using specific examples, which are provided only to help understand the method and the core idea of the present application. It should be noted that, for those skilled in the art, it is possible to make several improvements and modifications to the present application without departing from the principle of the present application, and such improvements and modifications also fall within the scope of the claims of the present application.
Claims (10)
1. A secure multiparty based auditable signature method, the method comprising:
generating a key based on a secret sharing mechanism;
updating the secret mark information of the participants at intervals of a preset period, and generating a trust matrix with a time stamp based on the credibility of each participant;
determining a trust vector of the participant from the trust matrix, and judging whether the participant is trusted according to the trust vector;
if the key is judged to be credible, allowing the participant to carry out signature processing according to the key and the secret mark information; and if the secret mark information is judged to be not credible, the participant is prohibited from performing signature processing according to the secret key and the secret mark information.
2. The secure multi-party based auditable signing method of claim 1, wherein generating a time-stamped trust matrix based on trustworthiness of each of said participants comprises:
evaluating the identity credibility of the participant in the preset period to serve as a direct trust evaluation value;
evaluating the credibility of the interactive information between the participant and other participants in the preset period as an indirect trust evaluation value;
generating a credibility measurement vector of the participant in the preset period according to the direct credibility evaluation value and the indirect credibility evaluation value to serve as a credibility vector;
and forming a matrix by the trust vectors corresponding to all participants in the preset period, and taking the matrix as a trust matrix.
3. A secure multi-party based auditable signature method as claimed in claim 2, wherein said evaluating the identity trustworthiness of the participants as a direct trust evaluation comprises:
acquiring the identity to-be-verified information of the participant; the information to be verified is obtained by respectively carrying out discrete logarithm encryption processing on the information to be verified according to each secret information of the participants and then summing the information to be verified;
acquiring the sum of the secret information of the participant, and performing discrete logarithm encryption processing on the sum of the secret information to serve as identity authentication information;
matching and verifying the identity information to be verified and the identity verification information to generate an identity verification result;
and according to a preset rule, assigning the identity credibility of the participant as the direct trust evaluation value according to the identity verification result.
4. A secure multi-party based auditable signature method as claimed in claim 2, wherein evaluating a trustworthiness of information exchanged between said participant and each other participant as an indirect trust evaluation value comprises:
matching and verifying the broadcast information between the participant and other participants to generate a broadcast verification result;
and assigning a value to the interactive information credibility of the participant according to a preset rule and the broadcast verification result to serve as the indirect trust evaluation value.
5. A secure multi-party based auditable signing method according to any of claims 1 to 4, further comprising, prior to determining the participant's trust vector from the trust matrix:
encrypting and storing the trust matrix into a blockchain;
if receiving the checking application, downloading the trust matrix of the corresponding period from the block chain;
and sending the downloaded trust matrix and the group private key of the corresponding period to an applicant.
6. The secure multi-party based auditable signing method of claim 5, wherein encrypting and storing said trust matrix into a blockchain comprises:
determining a trusted participant in the participants as an agent;
controlling the agent to encrypt and store the trust matrix in a blockchain;
correspondingly, if a checking application is received, downloading the trust matrix of the corresponding period from the block chain, including: and the agent receives the checking application and downloads the trust matrix of the corresponding period and the corresponding group private key from the block chain.
7. A secure multi-party based auditable signing method according to claim 6, wherein determining trusted ones of said parties as agents comprises:
the participants construct vectors from a preset set;
calling a system public key to encrypt the vector as a first competition value;
receiving a competition value sent by a neighbor participant as a second competition value;
determining the larger one of the first competition value and the second competition value as a third competition value;
sending the third competition value to another neighbor participant according to a transmission sequence to carry out vector value comparison until the maximum vector is determined, and taking the maximum vector as the maximum competitor;
and taking the participant corresponding to the maximum competitor as the agent.
8. A secure multiparty based auditable signature device, the device comprising:
a key generation unit configured to generate a key based on a secret sharing mechanism;
the trust measurement unit is used for updating the secret mark information of the participants at intervals of a preset period and generating a trust matrix with a time stamp based on the credibility of each participant;
the credibility judgment unit is used for determining the credibility vector of the participant from the credibility matrix and judging whether the participant is credible according to the credibility vector; if the first unit is judged to be credible, triggering the first unit; if the judgment result is not credible, triggering a second unit;
the first unit is used for releasing the signing processing of the participant according to the secret key and the secret mark information;
the second unit is used for forbidding the participant to carry out signature processing according to the secret key and the secret mark information.
9. A secure multiparty based auditable signature device, comprising:
a memory for storing a computer program;
a processor for implementing the steps of the secure multi-party based auditable signing method of any one of claims 1 to 7 when executing said computer program.
10. A readable storage medium, having stored thereon a program which, when executed by a processor, carries out the steps of the secure multiparty based auditable signature method of any of claims 1 to 7.
Priority Applications (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN202011155366.8A CN112272088A (en) | 2020-10-26 | 2020-10-26 | Auditable signature method based on multiple secure parties and related components |
Applications Claiming Priority (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN202011155366.8A CN112272088A (en) | 2020-10-26 | 2020-10-26 | Auditable signature method based on multiple secure parties and related components |
Publications (1)
| Publication Number | Publication Date |
|---|---|
| CN112272088A true CN112272088A (en) | 2021-01-26 |
Family
ID=74341400
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| CN202011155366.8A Pending CN112272088A (en) | 2020-10-26 | 2020-10-26 | Auditable signature method based on multiple secure parties and related components |
Country Status (1)
| Country | Link |
|---|---|
| CN (1) | CN112272088A (en) |
Cited By (4)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN113242123A (en) * | 2021-04-29 | 2021-08-10 | 龚健 | Common user data acquisition method and device and server |
| CN113347009A (en) * | 2021-08-05 | 2021-09-03 | 成都飞机工业(集团)有限责任公司 | Certificateless threshold signcryption method based on elliptic curve cryptosystem |
| CN113438089A (en) * | 2021-06-29 | 2021-09-24 | 山东新一代标准化研究院有限公司 | Block chain-based power Internet of things equipment communication method and network equipment thereof |
| CN119598524A (en) * | 2025-01-24 | 2025-03-11 | 北京中电普华信息技术有限公司 | Interface authentication method for large electric power model and related equipment |
-
2020
- 2020-10-26 CN CN202011155366.8A patent/CN112272088A/en active Pending
Non-Patent Citations (1)
| Title |
|---|
| 王韫烨等: "基于安全多方的区块链可审计签名方案", 《计算机应用》 * |
Cited By (5)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN113242123A (en) * | 2021-04-29 | 2021-08-10 | 龚健 | Common user data acquisition method and device and server |
| CN113438089A (en) * | 2021-06-29 | 2021-09-24 | 山东新一代标准化研究院有限公司 | Block chain-based power Internet of things equipment communication method and network equipment thereof |
| CN113347009A (en) * | 2021-08-05 | 2021-09-03 | 成都飞机工业(集团)有限责任公司 | Certificateless threshold signcryption method based on elliptic curve cryptosystem |
| CN113347009B (en) * | 2021-08-05 | 2022-01-07 | 成都飞机工业(集团)有限责任公司 | Certificateless threshold signcryption method based on elliptic curve cryptosystem |
| CN119598524A (en) * | 2025-01-24 | 2025-03-11 | 北京中电普华信息技术有限公司 | Interface authentication method for large electric power model and related equipment |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| Zhang et al. | SMAKA: Secure many-to-many authentication and key agreement scheme for vehicular networks | |
| CN109756485B (en) | Electronic contract signing method, electronic contract signing device, computer equipment and storage medium | |
| CN113301022B (en) | Internet of things equipment identity security authentication method based on block chain and fog calculation | |
| CN113691502B (en) | Communication method, device, gateway server, client and storage medium | |
| Rivera et al. | Securing digital identity in the zero trust architecture: A blockchain approach to privacy-focused multi-factor authentication | |
| CN110087237B (en) | Privacy protection method and device based on data disturbance and related components | |
| CN112272088A (en) | Auditable signature method based on multiple secure parties and related components | |
| CN113360943A (en) | Block chain private data protection method and device | |
| CN101296075A (en) | Identity authentication system based on elliptic curve | |
| CN112600675B (en) | Electronic voting method and device based on group signature, electronic equipment and storage medium | |
| CN118074919A (en) | Method, system and medium for establishing encrypted communication based on trusted hardware remote authentication | |
| CN110855667A (en) | Block chain encryption method, device and system | |
| Jan et al. | Mitigating the desynchronisation attack in multiserver environment | |
| US20260031974A1 (en) | Proof-of-work based on block cipher | |
| US11429702B2 (en) | Method of verification of a biometric authentication | |
| CN111539031B (en) | Data integrity detection method and system for privacy protection of cloud storage tag | |
| Alotaibi et al. | RAP-MEC: Robust authentication protocol for the mobile edge computing services | |
| Kaur et al. | Multi-cloud security model: establishment of inter-server communication for authentication integrity | |
| CN117749476A (en) | Trusted secure connection method and device based on encryption algorithm and electronic equipment | |
| CN111245594B (en) | Homomorphic operation-based collaborative signature method and system | |
| CN113536355A (en) | Method and device for generating session key | |
| CN111245611A (en) | Anti-quantum computing identity authentication method and system based on secret sharing and wearable equipment | |
| CN117424694A (en) | Block chain-based company certificate management method and device and electronic equipment | |
| Chaudhary et al. | Interoperable identity management protocol for multi-cloud platform | |
| Zhou et al. | An Efficient Chaotic Map‐Based Authentication Scheme with Mutual Anonymity |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| PB01 | Publication | ||
| PB01 | Publication | ||
| SE01 | Entry into force of request for substantive examination | ||
| SE01 | Entry into force of request for substantive examination | ||
| RJ01 | Rejection of invention patent application after publication |
Application publication date: 20210126 |
|
| RJ01 | Rejection of invention patent application after publication |