CN111611609A - Risk data sharing method and system based on safe multi-party calculation and block chain - Google Patents
Risk data sharing method and system based on safe multi-party calculation and block chain Download PDFInfo
- Publication number
- CN111611609A CN111611609A CN202010266336.8A CN202010266336A CN111611609A CN 111611609 A CN111611609 A CN 111611609A CN 202010266336 A CN202010266336 A CN 202010266336A CN 111611609 A CN111611609 A CN 111611609A
- Authority
- CN
- China
- Prior art keywords
- node
- loan
- overdue
- user node
- amount
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Granted
Links
Images
Classifications
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F21/60—Protecting data
- G06F21/62—Protecting access to data via a platform, e.g. using keys or access control rules
- G06F21/6218—Protecting access to data via a platform, e.g. using keys or access control rules to a system of files or objects, e.g. local or distributed file system or database
- G06F21/6245—Protecting personal data, e.g. for financial or medical purposes
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F16/00—Information retrieval; Database structures therefor; File system structures therefor
- G06F16/10—File systems; File servers
- G06F16/17—Details of further file system functions
- G06F16/176—Support for shared access to files; File sharing support
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F16/00—Information retrieval; Database structures therefor; File system structures therefor
- G06F16/20—Information retrieval; Database structures therefor; File system structures therefor of structured data, e.g. relational data
- G06F16/27—Replication, distribution or synchronisation of data between databases or within a distributed database system; Distributed database system architectures therefor
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F21/60—Protecting data
- G06F21/64—Protecting data integrity, e.g. using checksums, certificates or signatures
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06Q—INFORMATION AND COMMUNICATION TECHNOLOGY [ICT] SPECIALLY ADAPTED FOR ADMINISTRATIVE, COMMERCIAL, FINANCIAL, MANAGERIAL OR SUPERVISORY PURPOSES; SYSTEMS OR METHODS SPECIALLY ADAPTED FOR ADMINISTRATIVE, COMMERCIAL, FINANCIAL, MANAGERIAL OR SUPERVISORY PURPOSES, NOT OTHERWISE PROVIDED FOR
- G06Q40/00—Finance; Insurance; Tax strategies; Processing of corporate or income taxes
- G06Q40/03—Credit; Loans; Processing thereof
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/008—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols involving homomorphic encryption
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/06—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols the encryption apparatus using shift registers or memories for block-wise or stream coding, e.g. DES systems or RC4; Hash functions; Pseudorandom sequence generators
- H04L9/0643—Hash functions, e.g. MD5, SHA, HMAC or f9 MAC
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/32—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials
- H04L9/3247—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials involving digital signatures
Landscapes
- Engineering & Computer Science (AREA)
- Theoretical Computer Science (AREA)
- Computer Security & Cryptography (AREA)
- Physics & Mathematics (AREA)
- General Physics & Mathematics (AREA)
- Databases & Information Systems (AREA)
- General Engineering & Computer Science (AREA)
- Signal Processing (AREA)
- Health & Medical Sciences (AREA)
- Bioethics (AREA)
- General Health & Medical Sciences (AREA)
- Computer Networks & Wireless Communication (AREA)
- Business, Economics & Management (AREA)
- Software Systems (AREA)
- Finance (AREA)
- Computer Hardware Design (AREA)
- Accounting & Taxation (AREA)
- Data Mining & Analysis (AREA)
- Computing Systems (AREA)
- Medical Informatics (AREA)
- Power Engineering (AREA)
- Development Economics (AREA)
- Economics (AREA)
- Marketing (AREA)
- Strategic Management (AREA)
- Technology Law (AREA)
- General Business, Economics & Management (AREA)
- Financial Or Insurance-Related Operations Such As Payment And Settlement (AREA)
Abstract
The invention discloses a risk data sharing method and system based on safe multi-party calculation and a block chain, wherein the method comprises the following steps: acquiring a user node ID, calculating a hash value of the user node ID, and inquiring historical loan information of the user node according to the hash value; acquiring a historical loan amount private certificate of a user node, and calculating an overdue amount private certificate and an overdue duration private certificate by using a private key of the user node and the historical loan information acquired by inquiry; constructing a multi-party safety certificate of the overdue amount and a multi-party safety certificate of the overdue duration of the user node loan; sharing the processed loan information obtained by the query to a request node; the method realizes the co-construction of the wind control data alliance by a plurality of Internet financial institutions through safe multi-party calculation, and under the condition that original data is not exported, the distributed real-time safe calculation is carried out, so that the freshness, effectiveness and accuracy of the data are ensured, the safety of services and data is ensured to the maximum extent, and the supervision requirements are met.
Description
Technical Field
The invention relates to the technical field of information, in particular to a risk data sharing method and system based on safe multi-party calculation and a block chain.
Background
The data is a foundation for supporting the whole internet financial wind control, and the mutual-fund companies identify the fraud risk of the client through the large data technologies of user portrait, data mining, deep learning and the like by collecting, sorting and cleaning the client information. In order to reduce the overdue bad account rate of the pneumatic control, the financial company obviously provides great help for complete user data, and has guiding significance for the user to adapt to different risk interest rate products in a differentiated mode.
The block chain technology is taken as a distributed account book technology, brings deep influence on the financial field, and drives a new technical revolution and application revolution. In the financial industry, various financial products are developed and generated under the background of technologies such as block chains, cloud computing, big data and the like, on one hand, the services and the applications provide accurate and personalized services for users, on the other hand, relevant information of the users is collected, although great convenience is brought to life of people, the collected information often contains a large amount of sensitive information including medical history, income, identity, interest, position and the like, the privacy of the users can be directly or indirectly revealed by operations such as sharing, collection, release, analysis and utilization of the information, and great threat and puzzlement are brought to the users.
Disclosure of Invention
In order to solve the problem that the privacy of a user is directly or indirectly revealed by sensitive information sharing in a block chain environment in the background art, the invention provides a risk data sharing method and system based on secure multiparty computing and a block chain, wherein the risk data sharing method based on the secure multiparty computing and the block chain comprises the following steps:
acquiring a user node ID, calculating a hash value of the user node ID, and inquiring historical loan information of the user node according to the hash value;
acquiring a historical loan amount private certificate of a user node, and calculating an overdue amount private certificate and an overdue duration private certificate by using a private key of the user node and the historical loan information acquired by inquiry;
constructing a multi-party safety certificate of the overdue amount and a multi-party safety certificate of the overdue duration of the user node loan;
sharing the overdue amount multi-party safety certificate, the overdue duration multi-party safety certificate, the historical loan amount private certificate, the overdue duration private certificate and the signature of the user node loan submission material to a request node; the request node is a data sharing initiator.
Further, the querying historical loan information of the user node according to the hash value includes:
the pointer simultaneously clockwise and anticlockwise bidirectionally and circularly traverses the linked list to inquire the hash value at the current position of the bidirectional circular linked list in the cache;
if the hash value is found, extracting historical loan information of the user node corresponding to the hash value, and adding 1 to the access frequency of the position where the hash value is located;
if the hash value is not found after the bidirectional circulation traversal for one week, accessing a database and extracting the historical loan information of the user node in the database; and the pointer of the bidirectional circular linked list continuously moves in two directions, the cache position with the lowest first access position is found out, the hash value is filled and replaced to the position, and the access times of the replacement position are added by 1.
Further, the historical loan amount privacy voucher calculation formula comprises:
cloan=ruG+vloanH
the overdue amount private voucher calculation formula comprises the following steps:
coverdue=rBG+voverdueH
the expiration duration private voucher calculation formula comprises:
coverdue=rBG+voverdueH
wherein, r isuIs a user node private key, rBTo share a node private key, vloanV for inquiring the loan amount in the acquired historical loan information, theoverdueD, the overdue amount of the user node in the acquired historical loan information is inquiredoverdueFor inquiring the overdue time of the user node in the acquired historical loan information, G and H are base points of an elliptic curve, and cloanPrivacy of the voucher for the historical loan amount, said coverdueFor overdue amount private vouchers, said cdA private voucher for overdue duration;
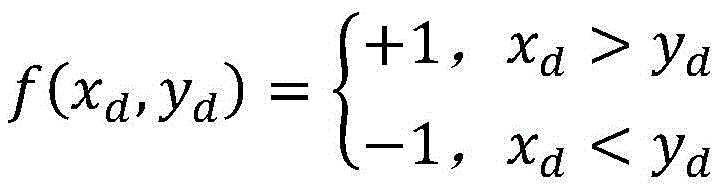
the overdue duration multiparty security certification calculation formula comprises the following steps:
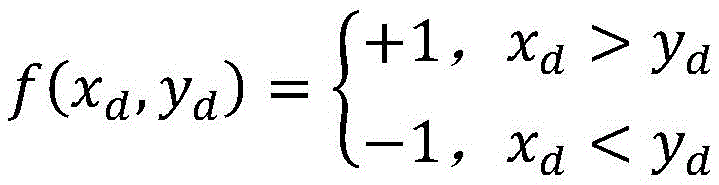
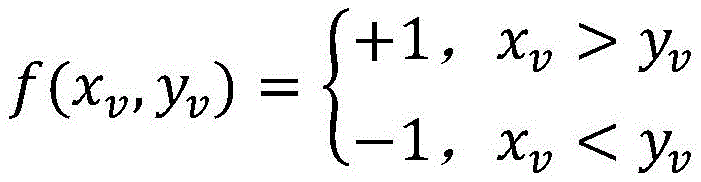
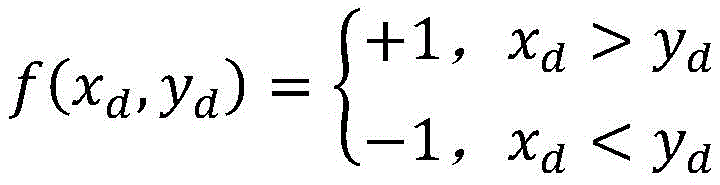
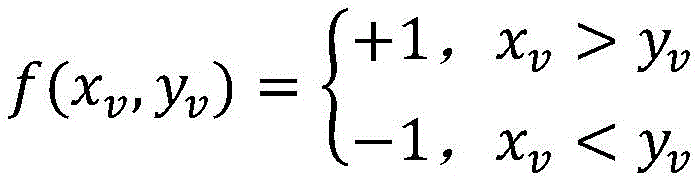
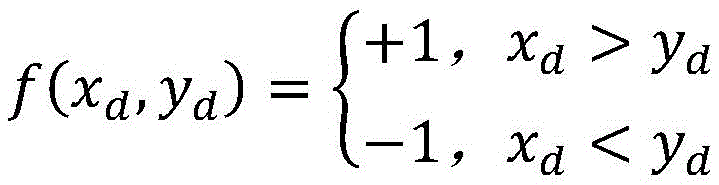
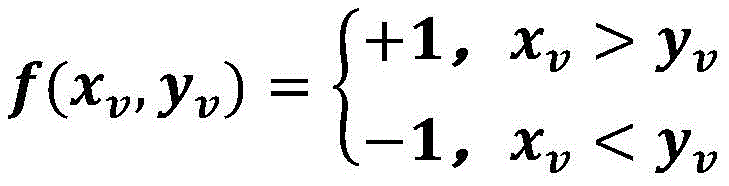
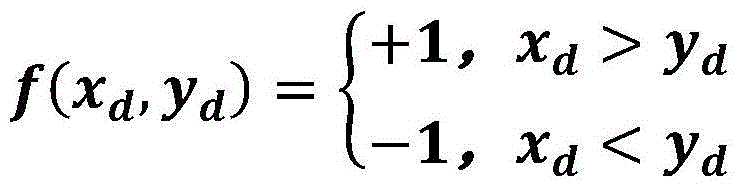
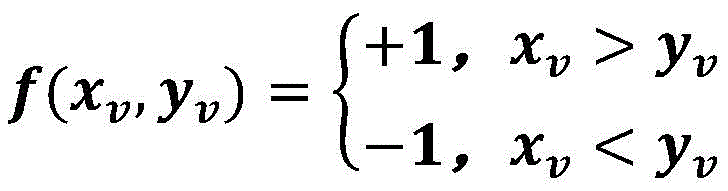
wherein, the f (x)d,yd) For long timeout multiparty security certification, the xdIs the expiration duration of the user node, ydIs the timeout duration threshold of the requesting node;
the overdue amount multiparty security certification calculation formula comprises the following steps:
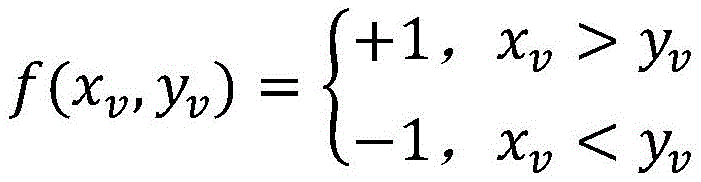
wherein, the f (x)v,yv) For overdue amount multiparty security certificationX is saidvFor the overdue amount of the user node, yvIs the overdue amount threshold of the requesting node.
Further, the method for constructing the multi-party security certificate comprises the following steps:
generating a system public and private key pair through a homomorphic encryption key generation algorithm, and sending the system public key to a request node;
encrypting each element in the shared node parameter set by using a system public key according to a homomorphic encryption algorithm to generate a ciphertext set; the shared node parameter set comprises a parameter true value and n-1 confusion values, wherein n is a positive integer greater than 1;
sending the ciphertext set to a request node;
the request node generates a request node parameter set, wherein the request node parameter set comprises a threshold true value corresponding to a parameter true value in a sharing node parameter set and n-1 confusion values;
the request node integrates and calculates elements in the request node parameter set and elements in the ciphertext set to obtain a set to be replaced;
receiving a replaced set which is sent by the request node and obtained by randomly replacing the set to be replaced;
decrypting the set after replacement to obtain a decryption result; the decryption result comprises a constructed multi-party security certificate;
the parameter true value in the sharing node parameter set comprises an overdue amount and an overdue duration, and the parameter true value in the requesting node parameter set comprises an overdue amount threshold and an overdue duration threshold; the multi-party security certificate comprises a multi-party security certificate of overdue amount and a multi-party security certificate of overdue duration.
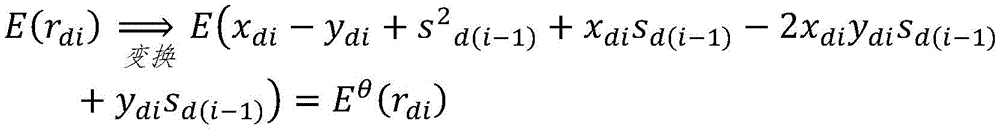
Further, the integrated calculation formula includes:
E(zdi)=E(xdi-ydi)
E(fdi)=E(xdi-2xdiydi+ydi)
E(sdi)=E(sd(i-1)+fdi) Wherein s isd0=0
E(rdi)=E(zdi+sdisd(i-1))
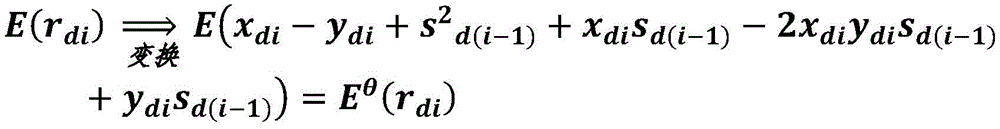
Wherein E (m) is the homomorphic encryption algorithm, and the system public key is used for encrypting a plaintext m; the E (x)di) For the ith element in the ciphertext set, ydiFor the ith element in the requesting node parameter set, the zdiIs a first intermediate variable, said fdiIs a second intermediate variable, said sdiIs a third intermediate variable, said E (r)di) Is the ith element in the set to be replaced;
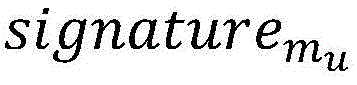
the random permutation calculation formula includes:
wherein E (m) is the homomorphic encryption algorithm, xdiFor sharing the ith element in the node parameter set, the ydiFor the ith element in the parameter set of the requesting node, sdiIs a third intermediate variable, said E (r)di) For the ith element in the set to be permuted, Eθ(rdi) Is the ith element in the permuted set.
The method for loan auditing by using the risk data sharing method comprises the following steps:
receiving loan material information submitted by a user node according to a preset format;
encrypting the loan material information and the loan material information signature by using a user node public key according to an asymmetric encryption algorithm to obtain a ciphertext, storing the ciphertext into a distributed file system, and storing a hash value of the ciphertext into a block chain network; the loan material information signature is obtained by encrypting a private key of the user node;
sending a user node ID to a sharing node, and receiving processed loan information obtained by the sharing node according to the risk data sharing method; the processed loan information comprises overdue amount multi-party safety certification, overdue duration multi-party safety certification, a historical loan amount private certificate, an overdue duration private certificate and a signature of loan materials submitted by a user node at a sharing node;
and auditing the user node according to the received processed loan information, and judging whether to pay the user node according to a preset rule.
Further, before receiving the loan material information submitted by the user node according to the preset format, the method further includes:
the user node registers to an identity authentication node by providing identity information, the identity authentication node verifies the identity information of the user node, and a user ID and a public and private key pair of the user node are generated and distributed to the user node if the verification is passed;
the sharing node, the request node and the auditing node register to the identity authentication node by providing enterprise qualification information, the identity authentication node verifies the enterprise qualification information, and respective node IDs and public and private key pairs are generated for the sharing node, the request node and the auditing node after verification is passed and distributed to corresponding nodes;
the identity authentication node registers a user ID, a sharing node ID, a requesting node ID and an auditing node ID in a blockchain network.
Further, the auditing the user node according to the received processed loan information, and determining whether to pay the user node according to a preset rule, including:
verifying the effectiveness of the historical loan amount private voucher, the overdue amount private voucher and the overdue duration private voucher through a private voucher verification function;
determining the overdue condition of the user node at the sharing node according to the overdue amount multi-party safety certificate and the overdue duration multi-party safety certificate;
verifying the validity of the loan material signature submitted by the user node at the sharing node through a signature verification function;
and comprehensively evaluating and determining whether to pay according to the loan information of the user node.
Further, the user node generates a loan amount private voucher by using a private key of the user node and submitting the loan amount in the loan material information;
the user node synthesizes a self private key and an audit node public key into a re-encryption key, and encrypts the ciphertext through the re-encryption key to obtain a re-encrypted ciphertext;
and issuing the loan amount private certificate and the re-encrypted ciphertext to a block chain, and verifying the validity of loan information through the audit node.
Further, the verifying the validity of the loan information by the auditing node includes:
the audit node decrypts the re-encrypted ciphertext by using a private key of the audit node to obtain loan material information of the user node, a loan material information signature of the user node and a loan amount private voucher;
the audit node verifies the validity of the signature of the user node through a signature verification function;
if the signature verification is valid, obtaining the loan amount of the user node through the loan material information of the user node, and constructing a certificate according to the user public key and the loan amount of the user node;
if the construction certificate is equal to the loan amount private certificate, judging that the loan is valid;
the construction certificate cθThe calculation formula comprises:
cθ=RA+vH
wherein, cθTo construct a certificate, RAThe method is characterized in that the method is a user node public key, v is the user node loan amount, and H is an elliptic curve base point.
The risk data sharing system based on the secure multi-party computing and the block chain comprises:
the system comprises user nodes, sharing nodes and request nodes;
the user node initiates a loan application to the request node;
the request node sends a loan history information query request to the sharing node and receives a query result;
the sharing node acquires a user node ID, calculates a hash value of the user node ID, and queries historical loan information of the user node according to the hash value;
the sharing node acquires a private voucher of the historical loan amount of the user node;
the sharing node calculates an overdue amount private certificate and an overdue duration private certificate by using a private key of the sharing node and the historical loan information obtained by inquiry;
the sharing node constructs a multi-party safety certificate of the overdue amount and a multi-party safety certificate of the overdue duration of the loan of the user node;
the sharing node shares the overdue amount multi-party safety certificate, the overdue duration multi-party safety certificate, the historical loan amount private certificate, the overdue duration private certificate and the signature of the user node loan submission material to the request node.
Further, the sharing node comprises a loan information query unit;
the loan information inquiry unit inquires the hash value through a bidirectional cache linked list in the cache, and the linked list pointer traverses the linked list in a clockwise and anticlockwise bidirectional cycle mode at the current position of the bidirectional cycle linked list;
if the hash value is found, extracting historical loan information of the user node corresponding to the hash value, and adding 1 to the access frequency of the position where the hash value is located;
if the hash value is not found after the bidirectional circulation traversal for one week, accessing a database and extracting the historical loan information of the user node in the database; and the pointer of the bidirectional circular linked list continuously moves in two directions, the cache position with the lowest first access position is found out, the hash value is filled and replaced to the position, and the access times of the replacement position are added by 1.
Further, the historical loan amount privacy voucher calculation formula comprises:
cloan=ruG+vloanH
the overdue amount private voucher calculation formula comprises the following steps:
coverdue=rBG+voverdueH
the expiration duration private voucher calculation formula comprises:
cd=rBG+doverdueH
wherein, r isuIs a user node private key, rBTo share a node private key, vloanV for inquiring the loan amount in the acquired historical loan information, theoverdueD, the overdue amount of the user node in the acquired historical loan information is inquiredoverdueFor inquiring the overdue time of the user node in the acquired historical loan information, G and H are base points of an elliptic curve, and cloanPrivacy of the voucher for the historical loan amount, said coverdueFor overdue amount private vouchers, said cdA private voucher for overdue duration;
the overdue duration multiparty security certification calculation formula comprises the following steps:
wherein, the f (x)d,yd) For long timeout multiparty security certification, the xdIs the expiration duration of the user node, ydIs the timeout duration threshold of the requesting node;
the overdue amount multiparty security certification calculation formula comprises the following steps:
wherein, the f (x)v,yv) For overdue amount multiparty security certification, the xvFor the overdue amount of the user node, yvIs the overdue amount threshold of the requesting node.
Further, the sharing node comprises a multi-party security certification construction unit;
the multi-party security certification constructing unit generates a system public and private key pair through a homomorphic encryption key generating algorithm and sends the system public key to a request node;
the multi-party security certification construction unit encrypts each element in the shared node parameter set by using a system public key according to a homomorphic encryption algorithm to generate a ciphertext set; the shared node parameter set comprises a parameter true value and n-1 confusion values, wherein n is a positive integer greater than 1;
the multi-party security certification construction unit sends the ciphertext set to a request node;
the request node generates a request node parameter set, wherein the request node parameter set comprises a threshold true value corresponding to a parameter true value in a sharing node parameter set and n-1 confusion values;
the request node integrates and calculates elements in the request node parameter set and elements in the ciphertext set to obtain a set to be replaced;
the multi-party security certification construction unit receives a replaced set which is sent by the request node and obtained by randomly replacing a set to be replaced;
the multi-party security certification construction unit decrypts the replaced set to obtain a decryption result; the decryption result comprises a constructed multi-party security certificate;
the parameter true value in the sharing node parameter set comprises an overdue amount and an overdue duration, and the parameter true value in the requesting node parameter set comprises an overdue amount threshold and an overdue duration threshold; the multi-party security certificate comprises a multi-party security certificate of overdue amount and a multi-party security certificate of overdue duration.
Further, the integrated calculation formula includes:
E(zdi)=E(xdi-ydi)
E(fdi)=E(xdi-2xdiydi+ydi)
E(sdi)=E(sd(i-1)+fdi) Wherein s isd0=0
E(rdi)=E(zdi+sdisd(i-1))
Wherein E (m) is the homomorphic encryption algorithm, and the system public key is used for encrypting a plaintext m; the E (x)di) For the ith element in the ciphertext set, ydiFor the ith element in the requesting node parameter set, the zdiIs a first intermediate variable, said fdiIs a second intermediate variable, said sdiIs a third intermediate variable, said E (r)di) Is the ith element in the set to be replaced;
the random permutation calculation formula includes:
wherein E (m) is the homomorphic encryption algorithm, xdiFor sharing the ith element in the node parameter set, the ydiFor the ith element in the parameter set of the requesting node, sdiIs a third intermediate variable, said E (r)di) For the ith element in the set to be permuted, Eθ(rdi) Is the ith element in the permuted set.
The system for loan auditing by using the risk data sharing system comprises:
the request node receives loan material information submitted by the user node according to a preset format;
the request node encrypts the loan material information and the loan material information signature according to an asymmetric encryption algorithm by using a user node public key to obtain a ciphertext, stores the ciphertext into a distributed file system, and stores a hash value of the ciphertext into a block chain network; the loan material information signature is obtained by encrypting a private key of the user node;
the request node sends a user node ID to a sharing node and receives processed loan information obtained by the sharing node according to the risk data sharing method; the processed loan information comprises overdue amount multi-party safety certification, overdue duration multi-party safety certification, a historical loan amount private certificate, an overdue duration private certificate and a signature of loan materials submitted by a user node at a sharing node;
and the request node checks the user node according to the received processed loan information and judges whether to pay the user node according to a preset rule.
Further, the system also comprises an identity authentication node, wherein the identity authentication node is used for receiving identity information of the user node, the sharing node, the request node and the auditing node and distributing corresponding public and private key pairs and node IDs;
the identity authentication node registers the identity information provided by the user node and verifies the identity information of the user node; if the verification is passed, generating a user ID and a public and private key pair of the user node, and distributing the user ID and the public and private key pair to the user node;
the identity authentication node registers enterprise qualification information provided by the sharing node, the request node and the auditing node and verifies the enterprise qualification information; after the verification is passed, respective node IDs and public and private key pairs are generated for the sharing node, the request node and the auditing node and are distributed to corresponding nodes;
the identity authentication node registers a user ID, a sharing node ID, a requesting node ID and an auditing node ID in a blockchain network.
Further, the requesting node verifies the validity of the historical loan amount private certificate, the overdue amount private certificate and the overdue duration private certificate through a private certificate verification function;
the request node judges the overdue condition of the user node at the sharing node according to the overdue amount multi-party safety certificate and the overdue duration multi-party safety certificate;
the requesting node verifies the validity of the loan material signature submitted by the user node at the sharing node through a signature verification function;
and the requesting node comprehensively evaluates and determines whether to put money on the user node according to the loan information of the user node.
Further, the user node generates a loan amount private voucher by using a private key of the user node and the loan amount submitted in the loan material information;
the user node synthesizes a re-encryption key by using a self private key and an audit node public key, and encrypts the ciphertext through the re-encryption key to obtain a re-encrypted ciphertext;
and the request node issues the loan amount private certificate and the re-encrypted ciphertext to a block chain, and the validity of loan information is verified through the audit node.
Further, the audit node decrypts the re-encrypted ciphertext by using a private key of the audit node to obtain loan material information of the user node, a loan material information signature of the user node and a loan amount private certificate;
the audit node verifies the validity of the signature of the user node through a signature verification function;
if the signature verification is valid, obtaining the loan amount of the user node through the loan material information of the user node, and constructing a certificate according to the user public key and the loan amount of the user node; if the construction certificate is equal to the loan amount private certificate, judging that the loan is valid;
the construction certificate cθThe calculation formula comprises:
cθ=RA+vH
wherein, cθTo construct a certificate, RAThe method is characterized in that the method is a user node public key, v is the user node loan amount, and H is an elliptic curve base point.
The invention has the beneficial effects that: the invention provides a risk data sharing method and system based on safe multi-party calculation and a block chain, wherein the method realizes that a plurality of Internet financial institutions build a wind control data alliance together through the safe multi-party calculation, and under the condition that original data are not taken out of a warehouse, the distributed real-time safe calculation ensures the freshness, effectiveness and accuracy of the data, thereby ensuring the safety of business and data to the maximum extent and meeting the supervision requirement; the financial institution can also authorize the auditing institution to view the loan information and verify the validity of the private data through an agent re-encryption mode.
Drawings
A more complete understanding of exemplary embodiments of the present invention may be had by reference to the following drawings in which:
fig. 1 is a flowchart of a risk data sharing method based on secure multiparty computation and block chaining according to an embodiment of the present invention;
fig. 2 is a flow chart of a method for loan review using the risk data sharing method described above according to an embodiment of the invention;
FIG. 3 is a block diagram of a risk data sharing system based on secure multi-party computation and block chaining according to an embodiment of the present invention;
fig. 4 is a block diagram of a system for loan review using the risk data sharing system described above according to an embodiment of the invention.
Detailed Description
The exemplary embodiments of the present invention will now be described with reference to the accompanying drawings, however, the present invention may be embodied in many different forms and is not limited to the embodiments described herein, which are provided for complete and complete disclosure of the present invention and to fully convey the scope of the present invention to those skilled in the art. The terminology used in the exemplary embodiments illustrated in the accompanying drawings is not intended to be limiting of the invention. In the drawings, the same units/elements are denoted by the same reference numerals.
Unless otherwise defined, terms (including technical and scientific terms) used herein have the same meaning as commonly understood by one of ordinary skill in the art to which this invention belongs. Further, it will be understood that terms, such as those defined in commonly used dictionaries, should be interpreted as having a meaning that is consistent with their meaning in the context of the relevant art and will not be interpreted in an idealized or overly formal sense.
Fig. 1 is a flowchart of a risk data sharing method based on secure multiparty computation and block chaining according to an embodiment of the present invention; as shown in fig. 1, the method includes:
the data sharing process is initiated by a data request node, the data request node sends a historical loan information query request of a loan user to the data sharing node, and the sharing node completes the operation of querying the loan information of the user according to the user node ID of the loan user.
And during query, the cache is queried first, and if the cache does not exist, the database is queried.
The cache adopts a bidirectional circular linked list structure, the double-pointer design mode can improve half of the searching efficiency, and the cache position indicated by each pointer in the linked list marks the historical access times. The method for inquiring the cache position of the hash value by calculating the hash value of the user node ID comprises the following steps:
the pointer simultaneously and circularly traverses the linked list clockwise and anticlockwise from the current position of the bidirectional circular linked list to inquire the hash value;
if the hash value is found, extracting historical loan information of the user node corresponding to the hash value, and adding 1 to the access frequency of the position where the hash value is located;
if the hash value is not found after the bidirectional loop traversal for one week, accessing a database and extracting historical loan information of the user node in the database; and simultaneously, the pointer of the bidirectional circular linked list continuously moves in two directions, the cache position with the lowest first access position is found out, the hash value is filled and replaced to the position, and the access times of the replacement position are added by 1.
the historical loan amount privacy voucher calculation formula comprises the following steps:
cloan=ruG+vloanH
the overdue amount private voucher calculation formula comprises the following steps:
coverdue=rBG+voverdueH
the expiration duration private voucher calculation formula comprises:
coverdue=rBG+voverdueH
wherein, r isuIs a user node private key, rBSharing the node private key; v isloanV for inquiring the loan amount in the acquired historical loan information, theoverdueD, the overdue amount of the user node in the acquired historical loan information is inquiredoverdueThe overdue time of the user node in the historical loan information obtained by query is determined; c is mentionedloanPrivacy of the voucher for the historical loan amount, said coverdueFor overdue amount private vouchers, said cdA private voucher for overdue duration;
the base points G and H are elliptic curve base points, for example, the base point G is given an array constant of 64 bytes in length, such as G ═ {0x86,0xbe,0x66,0x7e, …,0xb8}, where H ═ hash (G,62) + {0x04, 0x45} ═ 0x50,0x92,0x9b, …,0xa3,0x89,0x04,0x45}, that is, the base point H is the first 62 bytes of the hash value of the base point G, and the 63 rd bit and 64 th bit of the base point H are filled with {0x04, 0x45 }.
in order to realize distributed real-time safety calculation under the condition that original data is not delivered out of a warehouse, safe multi-party calculation is adopted to construct multi-party safety certificates of overdue amount and overdue duration, and the overdue condition of the user loan is obtained under the encryption condition; in the whole process, the request node does not know whether the loan record of the financial machine user node at the sharing node is overdue or not, the sharing node does not tell the overdue finance and the overdue duration of the request node in a plain text, the request node compares the overdue amount threshold of the request node with the overdue amount threshold of the sharing node and calculates the overdue duration and the overdue duration threshold by multiple parties through setting the overdue amount threshold and the overdue duration threshold.
The overdue duration multiparty safety certification calculation formula is as follows:
wherein, the f (x)d,yd) For long timeout multiparty security certification, the xdIs the expiration duration of the user node, ydIs the timeout duration threshold of the requesting node;
the overdue amount multi-party security certificate calculation formula is as follows:
wherein, the f (x)v,yv) For overdue amount multiparty security certification, the xvFor the overdue amount of the user node, yvIs the overdue amount threshold of the requesting node.
Taking the expiration time as an example, the construction process of the multi-party security certification is concretely explained as follows:
the input data comprises a sharing node parameter set and a request node parameter set, wherein the sharing node parameter set comprises n elements, and the n elements comprise an expiration time length true value and n-1 confusion values; the parameter set of the requesting node also comprises n elements, and the n elements comprise a true value of the overdue duration threshold and n-1 confusion values; and n is a positive integer greater than 1.
The output data is f (x)d,yd) And f (x)d,yd) Satisfies the following conditions:
firstly, generating a system public and private key pair by utilizing a Paillier homomorphic encryption key generation algorithm, and sending the system public key to a request node;
the key generation algorithm is as follows:
1. selecting two large prime numbers p and q, wherein p is approximately equal to q;
2. calculating N ═ p × q, λ ═ Φ (N), where Φ (N) is an euler function;
3. selecting a random number g;
5. The system public key is (n, g) and the system private key SK is (λ, μ).
Then, encrypting each element in the shared node parameter set by using a shared node public key according to a Paillier homomorphic encryption algorithm to generate a ciphertext set, wherein the Paillier homomorphic encryption algorithm meets the conditions of addition and multiplication homomorphy, and the specific calculation process is as follows:
1. and (3) encryption process:
selecting a random number r, wherein the gcd (r, n) is 1;
encrypting a plaintext m to obtain a ciphertext c, wherein c is E (m, r) is gm·rnmod n2。
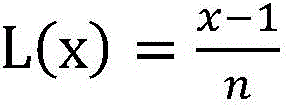
2. And (3) decryption process:
m=D(c)=L(cλmodn2)·μmod n
wherein m is plaintext and c is ciphertext.
Then, the ciphertext set is sent to a request node, and the request node integrates and calculates elements in the request node parameter set and elements in the ciphertext set to obtain a set to be replaced; the integrated calculation formula is as follows:
E(zdi)=E(xdi-ydi)
E(fdi)=E(xdi-2xdiydi+ydi)
E(sdi)=E(sd(i-1)+fdi) Wherein s isd0=0
E(rdi)=E(zdi+sdisd(i-1))
Wherein E (m) is the homomorphic encryption algorithm, and the system public key is used for encrypting a plaintext m; the E (x)di) For the ith element in the ciphertext set, ydiFor the ith element in the requesting node parameter set, the zdiIs a first intermediate variable, said fdiIs a second intermediate variable, said sdiIs as followsThree intermediate variables, said E (r)di) Is the ith element in the set to be replaced;
the set to be permuted is denoted as { E (r)d1),E(rd2),...,E(rdn) Requesting the node to randomly replace the set to be replaced to obtain a replaced set { E }θ(rd1),Eθ(rd2),...,Eθ(rdn) Sending the replaced set to a sharing node; the principle of random permutation is as follows:
wherein E (m) is the homomorphic encryption algorithm, xdiFor sharing the ith element in the node parameter set, the ydiFor the ith element in the parameter set of the requesting node, sdiIs a third intermediate variable, said E (r)di) For the ith element in the set to be permuted, Eθ(rdi) Is the ith element in the permuted set.
Finally, decrypting the set after replacement to obtain a decryption result; the decryption result comprises built overdue duration multiparty security certification, namely v must exist in the decryption resultdSatisfy vd∈{+1,-1},f(xd,yd)=vdSaid f (x)d,yd) Namely, the multi-party safety certification of the overdue time.
Similarly, the overdue amount multi-party security certification can be constructed by the same method, that is, the parameter true value in the shared node parameter set comprises an overdue amount and an overdue duration, and the parameter true value in the request node parameter set comprises an overdue amount threshold and an overdue duration threshold; the multi-party security certificate comprises a multi-party security certificate of overdue amount and a multi-party security certificate of overdue duration.
and the sharing node processes the query information and then sends the query information to the request node, and the request node performs subsequent processing.
Fig. 2 is a flow chart of a method for loan review using the risk data sharing method described above according to an embodiment of the invention; as shown in fig. 2, the method includes:
step 210, receiving loan material information submitted by a user node according to a preset format;
before receiving the loan material information submitted by the user node according to the preset format, the method further comprises the following steps:
the user node registers to an identity authentication node by providing identity information, the identity authentication node verifies the identity information of the user node, and a user ID and a public and private key pair of the user node are generated and distributed to the user node if the verification is passed;
the sharing node, the request node and the auditing node register to the identity authentication node by providing enterprise qualification information, the identity authentication node verifies the enterprise qualification information, and respective node IDs and public and private key pairs are generated for the sharing node, the request node and the auditing node after verification is passed and distributed to corresponding nodes; the enterprise qualification information comprises a unified social credit code, a business license plate, legal information, an organization name and the like;
the identity authentication node registers a user ID, a sharing node ID, a requesting node ID and an auditing node ID in a blockchain network.
The loan material information comprises identity information, bank running water, social insurance information and loan amount;
the user node signs the loan material information through a private key distributed by the identity authentication node, and the signature of the loan material information is sent to the request node.
220, encrypting the loan material information and the loan material information signature by using a user node public key according to an asymmetric encryption algorithm to obtain a ciphertext, storing the ciphertext into a distributed file system, and storing the hash value of the ciphertext into a block chain network; the loan material information signature is obtained by encrypting a private key of the user node;
the asymmetric encryption algorithm adopts an elliptic curve encryption algorithm, and the calculation formula is as follows:
wherein m issuFor encrypted ciphertext, EccEncrypt is an elliptic Curve encryption Algorithm, muIn order to be the loan material information,signing loan material information, RuIs the user public key.
Step 230, sending a user node ID to a sharing node, and receiving processed loan information obtained by the sharing node according to the risk data sharing method; the processed loan information comprises overdue amount multi-party safety certification, overdue duration multi-party safety certification, a historical loan amount private certificate, an overdue duration private certificate and a signature of loan materials submitted by a user node at a sharing node;
according to the risk data sharing method based on the secure multi-party calculation and the block chain, the processed loan information obtained by inquiring the sharing node is obtained and comprises the overdue money multi-party security certificate, the overdue time multi-party security certificate, the historical loan money private certificate, the overdue time private certificate and the signature of loan materials submitted by the user node at the sharing node.
Step 240, auditing the user node according to the received processed loan information, and judging whether to pay the user node according to a preset rule;
according to the historical loan information of the user node obtained by inquiry, the request node can check and evaluate the risk of the user node and determine whether to pay the user node; the method comprises the following steps:
firstly, verifying the validity of a historical loan amount private certificate, an overdue amount private certificate and an overdue duration private certificate of a user node at a sharing node through a private certificate verification function;
then, determining the overdue condition of the user node at the sharing node according to the overdue money multi-party safety certificate and the overdue duration multi-party safety certificate;
then, verifying the validity of the loan material signature submitted by the user node at the sharing node through a signature verification function;
and finally, comprehensively evaluating and determining whether to pay according to the loan information of the user node.
In addition, the invention can also finish auditing and monitoring of financial activities, and the specific method comprises the following steps:
the user node generates a loan amount private voucher by using a private key of the user node and the loan amount submitted in the loan material information;
the user node synthesizes the self private key and the audit node public key into a re-encryption key, and the encrypted ciphertext m in the step 220 is subjected to the re-encryption keysuRe-encrypting to obtain re-encrypted ciphertext msu→Audit;
Issuing the loan amount private certificate and the re-encrypted ciphertext to a block chain, and verifying the validity of loan information through the audit node;
the audit node decrypts the received re-encrypted ciphertext m by using a private key thereofsu→AuditObtaining loan material information m of user nodeuLoan material information signature of user nodeAnd a loan amount privacy voucher;
the audit node verifies the signature of the user node through a signature verification functionThe effectiveness of (a);
if the signature verification is valid, the loan material information m of the user node is passeduObtaining the loan amount of the user node and according to the userConstructing a certificate by the public key and the user node loan amount;
if the construction certificate is equal to the loan amount private certificate, judging that the loan is valid;
the construction certificate cθThe calculation formula comprises:
cθ=RA+vH
wherein, cθTo construct a certificate, RAThe method is characterized in that the method is a user node public key, v is the user node loan amount, and H is an elliptic curve base point.
FIG. 3 is a block diagram of a risk data sharing system based on secure multi-party computation and block chaining according to an embodiment of the present invention; as shown in fig. 3, the system is deployed in a blockchain, and the system includes:
a user node 310, a sharing node 320, and a requesting node 330;
the user node 310 initiates a loan application to the requesting node 330;
the requesting node 330 sends a loan history information query request to the sharing node 320 and receives a query result;
the sharing node 320 acquires the user node ID, calculates the hash value of the user node ID, and queries the historical loan information of the user node according to the hash value;
the sharing node 320 includes a loan information query unit 3201;
the loan information query unit 3201 queries the hash value through a bidirectional cache linked list in cache, and the linked list pointer traverses the linked list in a clockwise and counterclockwise bidirectional cycle at the current position of the bidirectional cycle linked list;
if the hash value is found, extracting historical loan information of the user node corresponding to the hash value, and adding 1 to the access frequency of the position where the hash value is located;
if the hash value is not found after the bidirectional circulation traversal for one week, accessing a database and extracting the historical loan information of the user node in the database; the pointer of the bidirectional circular linked list continuously moves in two directions, a cache position with the lowest first access position is found out, the hash value is filled and replaced to the position, and the access times of the replacement position are added by 1;
the sharing node 320 acquires a private voucher of the historical loan amount of the user node; the sharing node 320 calculates an overdue amount private certificate and an overdue duration private certificate by using a private key of the sharing node and the historical loan information obtained by inquiry;
the historical loan amount privacy voucher calculation formula comprises the following steps:
cloan=ruG+vloanH
the overdue amount private voucher calculation formula comprises the following steps:
coverdue=rBG+voverdueH
the expiration duration private voucher calculation formula comprises:
cd=rBG+doverdueH
wherein, r isuIs a user node private key, rBTo share a node private key, vloanV for inquiring the loan amount in the acquired historical loan information, theoverdueD, the overdue amount of the user node in the acquired historical loan information is inquiredoverdueFor inquiring the overdue time of the user node in the acquired historical loan information, G and H are base points of an elliptic curve, and cloanPrivacy of the voucher for the historical loan amount, said coverdueFor overdue amount private vouchers, said cdA private voucher for overdue duration;
the sharing node 320 constructs a multi-party safety certificate of the overdue amount and a multi-party safety certificate of the overdue duration of the loan of the user node;
the overdue duration multiparty security certification calculation formula comprises the following steps:
wherein, the f (x)d,yd) For long timeout multiparty security certification, the xdIs the expiration duration of the user node, ydTo request forA timeout duration threshold of the node;
the overdue amount multiparty security certification calculation formula comprises the following steps:
wherein, the f (x)v,yv) For overdue amount multiparty security certification, the xvFor the overdue amount of the user node, yvA threshold for the amount of overdue for the requesting node;
the sharing node 320 includes a multi-party security attestation building unit 3202;
the multi-party security certification constructing unit 3202 generates a system public and private key pair through a homomorphic encryption key generating algorithm, and sends the system public key to a request node;
the multiparty security certification constructing unit 3202 encrypts each element in the shared node parameter set by using a system public key according to a homomorphic encryption algorithm to generate a ciphertext set; the shared node parameter set comprises a parameter true value and n-1 confusion values, wherein n is a positive integer greater than 1;
the multi-party security certification constructing unit 3202 sends the ciphertext set to the requesting node 330;
the request node 330 generates a request node parameter set, where the request node parameter set includes a threshold true value corresponding to a parameter true value in a shared node parameter set and n-1 confusion values;
the request node 330 integrates and calculates the elements in the request node parameter set and the elements in the ciphertext set to obtain a set to be replaced;
the integrated calculation formula includes:
E(zdi)=E(xdi-ydi)
E(fdi)=E(xdi-2xdiydi+ydi)
E(sdi)=E(sd(i-1)+fdi) Wherein s isd0=0
E(rdi)=E(zdi+sdiSd(i-1))
Wherein E (m) is the homomorphic encryption algorithm, and the system public key is used for encrypting a plaintext m; the E (x)di) For the ith element in the ciphertext set, ydiFor the ith element in the requesting node parameter set, the zdiIs a first intermediate variable, said fdiIs a second intermediate variable, said sdiIs a third intermediate variable, said E (r)di) Is the ith element in the set to be replaced;
the multiparty security certification constructing unit 3202 receives a replaced set obtained by randomly replacing a set to be replaced and sent by the requesting node 330;
the random permutation calculation formula includes:
wherein E (m) is the homomorphic encryption algorithm, xdiFor sharing the ith element in the node parameter set, the ydiFor the ith element in the parameter set of the requesting node, sdiIs a third intermediate variable, said E (r)di) For the ith element in the set to be permuted, Eθ(rdi) Is the ith element in the permuted set.
The multiparty security certification constructing unit 3202 decrypts the replaced set to obtain a decryption result; the decryption result comprises a constructed multi-party security certificate;
the parameter true value in the sharing node parameter set comprises an overdue amount and an overdue duration, and the parameter true value in the requesting node parameter set comprises an overdue amount threshold and an overdue duration threshold; the multi-party security certification comprises a multi-party security certification of overdue amount and a multi-party security certification of overdue duration;
the sharing node 320 shares the overdue amount multi-party security certificate, the overdue duration multi-party security certificate, the historical loan amount private certificate, the overdue duration private certificate, and the signature of the user node loan submission material to the requesting node 330.
FIG. 4 is a block diagram of a system for loan review using the risk data sharing system described above in accordance with an embodiment of the invention; as shown in fig. 4:
the system comprises an identity authentication node 410, wherein the identity authentication node 410 is used for receiving identity information of a user node 310, a sharing node 320, a requesting node 330 and an auditing node 420 and distributing corresponding public and private key pairs and node IDs;
the identity authentication node 410 registers the identity information provided by the user node 310 and verifies the identity information of the user node 310; if the verification is passed, generating a user ID and a user node public and private key pair, and distributing the user ID and the user node public and private key pair to the user node 310;
the identity authentication node 410 registers the enterprise qualification information provided by the sharing node 320, the request node 330 and the auditing node 420, and verifies the enterprise qualification information; after the verification is passed, respective node IDs and public and private key pairs are generated for the sharing node 320, the request node 330 and the auditing node 420, and are distributed to corresponding nodes;
the identity authentication node 410 registers the user ID, the sharing node ID, the requesting node ID, and the auditing node ID into the blockchain network.
The request node 330 receives the loan material information submitted by the user node 310 according to a preset format;
the request node 330 encrypts the loan material information and the loan material information signature according to an asymmetric encryption algorithm by using a user node public key to obtain a ciphertext, stores the ciphertext into a distributed file system, and stores a hash value of the ciphertext into a block chain network; the loan material information signature is obtained by encrypting a private key of the user node;
the request node 330 sends a user node ID to the sharing node 320, and receives processed loan information obtained by the sharing node 320 according to the risk data sharing method; the processed loan information comprises overdue amount multi-party safety certification, overdue duration multi-party safety certification, historical loan amount private certificate, overdue duration private certificate and signature of loan materials submitted by the user node 310 at the sharing node 320;
the request node 330 checks the user node 310 according to the received processed loan information, and determines whether to pay for the user node 310 according to preset rules;
the requesting node 330 verifies the validity of the historical loan amount private voucher, the overdue amount private voucher and the overdue duration private voucher through a private voucher verification function;
the requesting node 330 determines the overdue condition of the user node 310 at the sharing node 320 according to the overdue amount multi-party security certificate and the overdue duration multi-party security certificate;
the requesting node 330 verifies the validity of the loan material signature submitted by the user node 310 at the sharing node 320 through a signature verification function;
the requesting node 330 determines whether to pay for the loan information of the user node 310 based on the comprehensive evaluation of the loan information.
In addition, the method can also be used for finishing auditing supervision of financial activities;
the user node 310 generates a loan amount private voucher by using a private key of the user node and the loan amount submitted in the loan material information;
the user node 310 synthesizes a self private key and an audit node public key into a re-encryption key, and encrypts the ciphertext through the re-encryption key to obtain a re-encrypted ciphertext;
the request node 330 issues the loan amount private certificate and the re-encrypted ciphertext to a block chain, and the auditing node 420 verifies the validity of loan information;
the auditing node 420 decrypts the re-encrypted ciphertext by using a private key thereof to obtain loan material information of the user node 310, a loan material information signature of the user node 310 and a loan amount private certificate;
the auditing node 420 verifies the validity of the signature of the user node through a signature verification function;
if the signature verification is valid, obtaining the user node loan amount through the loan material information of the user node 310, and constructing a certificate according to the user public key and the user node loan amount; if the construction certificate is equal to the loan amount private certificate, judging that the loan is valid;
the construction certificate cθThe calculation formula comprises:
cθ=RA+vH
wherein, cθTo construct a certificate, RAThe method is characterized in that the method is a user node public key, v is the user node loan amount, and H is an elliptic curve base point.
In the description provided herein, numerous specific details are set forth. However, it is understood that embodiments of the disclosure may be practiced without these specific details. In some instances, well-known methods, structures and techniques have not been shown in detail in order not to obscure an understanding of this description.
Those skilled in the art will appreciate that the modules in the device in an embodiment may be adaptively changed and disposed in one or more devices different from the embodiment. The modules or units or components of the embodiments may be combined into one module or unit or component, and furthermore they may be divided into a plurality of sub-modules or sub-units or sub-components. All of the features disclosed in this specification (including any accompanying claims, abstract and drawings), and all of the processes or elements of any method or apparatus so disclosed, may be combined in any combination, except combinations where at least some of such features and/or processes or elements are mutually exclusive. Each feature disclosed in this specification (including any accompanying claims, abstract and drawings) may be replaced by alternative features serving the same, equivalent or similar purpose, unless expressly stated otherwise. Reference to step numbers in this specification is only for distinguishing between steps and is not intended to limit the temporal or logical relationship between steps, which includes all possible scenarios unless the context clearly dictates otherwise.
Moreover, those skilled in the art will appreciate that while some embodiments described herein include some features included in other embodiments, rather than other features, combinations of features of different embodiments are meant to be within the scope of the disclosure and form different embodiments. For example, any of the embodiments claimed in the claims can be used in any combination.
Various component embodiments of the disclosure may be implemented in hardware, or in software modules running on one or more processors, or in a combination thereof. The present disclosure may also be embodied as device or system programs (e.g., computer programs and computer program products) for performing a portion or all of the methods described herein. Such programs implementing the present disclosure may be stored on a computer-readable medium or may be in the form of one or more signals. Such a signal may be downloaded from an internet website or provided on a carrier signal or in any other form.
It should be noted that the above-mentioned embodiments illustrate rather than limit the disclosure, and that those skilled in the art will be able to design alternative embodiments without departing from the scope of the appended claims. The word "comprising" does not exclude the presence of elements or steps not listed in a claim. The word "a" or "an" preceding an element does not exclude the presence of a plurality of such elements. The disclosure may be implemented by means of hardware comprising several distinct elements, and by means of a suitably programmed computer. In the unit claims enumerating several systems, several of these systems may be embodied by one and the same item of hardware.
The foregoing is directed to embodiments of the present disclosure, and it is noted that numerous improvements, modifications, and variations may be made by those skilled in the art without departing from the spirit of the disclosure, and that such improvements, modifications, and variations are considered to be within the scope of the present disclosure.
Claims (20)
1. A method for risk data sharing based on secure multiparty computing and blockchains, the method comprising:
acquiring a user node ID, calculating a hash value of the user node ID, and inquiring historical loan information of the user node according to the hash value;
acquiring a historical loan amount private certificate of a user node, and calculating an overdue amount private certificate and an overdue duration private certificate by using a private key of the user node and the historical loan information acquired by inquiry;
constructing a multi-party safety certificate of the overdue amount and a multi-party safety certificate of the overdue duration of the user node loan;
sharing the overdue amount multi-party safety certificate, the overdue duration multi-party safety certificate, the historical loan amount private certificate, the overdue duration private certificate and the signature of the user node loan submission material to a request node; the request node is a data sharing initiator.
2. The method according to claim 1, wherein the querying historical loan information of the user node according to the hash value comprises:
the pointer simultaneously clockwise and anticlockwise bidirectionally and circularly traverses the linked list to inquire the hash value at the current position of the bidirectional circular linked list in the cache;
if the hash value is found, extracting historical loan information of the user node corresponding to the hash value, and adding 1 to the access frequency of the position where the hash value is located;
if the hash value is not found after the bidirectional circulation traversal for one week, accessing a database and extracting the historical loan information of the user node in the database; and the pointer of the bidirectional circular linked list continuously moves in two directions, the cache position with the lowest first access position is found out, the hash value is filled and replaced to the position, and the access times of the replacement position are added by 1.
3. The method of claim 1, wherein:
the historical loan amount privacy voucher calculation formula comprises the following steps:
cloan=ruG+vloanH
the overdue amount private voucher calculation formula comprises the following steps:
coverdue=rBG+voverdueH
the expiration duration private voucher calculation formula comprises:
coverdue=rBG+voverdueH
wherein, r isuIs a user node private key, rBTo share a node private key, vloanV for inquiring the loan amount in the acquired historical loan information, theoverdueD, the overdue amount of the user node in the acquired historical loan information is inquiredoverdueFor inquiring the overdue time of the user node in the acquired historical loan information, G and H are base points of an elliptic curve, and cloanPrivacy of the voucher for the historical loan amount, said coverdueFor overdue amount private vouchers, said cdA private voucher for overdue duration;
the overdue duration multiparty security certification calculation formula comprises the following steps:
wherein, the f (x)d,yd) For long timeout multiparty security certification, the xdIs the expiration duration of the user node, ydIs the timeout duration threshold of the requesting node;
the overdue amount multiparty security certification calculation formula comprises the following steps:
wherein, the f (x)v,yv) For overdue amount multiparty security certification, the xvFor the overdue amount of the user node, yvIs the overdue amount threshold of the requesting node.
4. The method of claim 3, wherein the method of building a multi-party security attestation comprises:
generating a system public and private key pair through a homomorphic encryption key generation algorithm, and sending the system public key to a request node;
encrypting each element in the shared node parameter set by using a system public key according to a homomorphic encryption algorithm to generate a ciphertext set; the shared node parameter set comprises a parameter true value and n-1 confusion values, wherein n is a positive integer greater than 1;
sending the ciphertext set to a request node;
the request node generates a request node parameter set, wherein the request node parameter set comprises a threshold true value corresponding to a parameter true value in a sharing node parameter set and n-1 confusion values;
the request node integrates and calculates elements in the request node parameter set and elements in the ciphertext set to obtain a set to be replaced;
receiving a replaced set which is sent by the request node and obtained by randomly replacing the set to be replaced;
decrypting the set after replacement to obtain a decryption result; the decryption result comprises a constructed multi-party security certificate;
the parameter true value in the sharing node parameter set comprises an overdue amount and an overdue duration, and the parameter true value in the requesting node parameter set comprises an overdue amount threshold and an overdue duration threshold; the multi-party security certificate comprises a multi-party security certificate of overdue amount and a multi-party security certificate of overdue duration.
5. The method of claim 4, wherein:
the integrated calculation formula includes:
E(zdi)=E(xdi-ydi)
E(fdi)=E(xdi-2xdiydi+ydi)
E(sdi)=E(sd(i-1)+fdi) Wherein s isd0=0
E(rdi)=E(zdi+sdisd(i-1))
Wherein E (m) is the homomorphic encryption algorithm, and the system public key is used for encrypting a plaintext m; the E (x)di) For the ith element in the ciphertext set, ydiFor the ith element in the requesting node parameter set, the zdiIs a first intermediate variable, said fdiIs a second intermediate variable, said sdiIs a third intermediate variable, said E (r)di) Is the ith element in the set to be replaced;
the random permutation calculation formula includes:
wherein E (m) is the homomorphic encryption algorithm, xdiFor sharing the ith element in the node parameter set, the ydiFor the ith element in the parameter set of the requesting node, sdiIs a third intermediate variable, said E (r)di) For the ith element in the set to be permuted, Eθ(rdi) Is the ith element in the permuted set.
6. A method of loan auditing using the risk data sharing method of claim 1, the method comprising:
receiving loan material information submitted by a user node according to a preset format;
encrypting the loan material information and the loan material information signature by using a user node public key according to an asymmetric encryption algorithm to obtain a ciphertext, storing the ciphertext into a distributed file system, and storing a hash value of the ciphertext into a block chain network; the loan material information signature is obtained by encrypting a private key of the user node;
sending a user node ID to a sharing node, and receiving processed loan information obtained by the sharing node according to the risk data sharing method; the processed loan information comprises overdue amount multi-party safety certification, overdue duration multi-party safety certification, a historical loan amount private certificate, an overdue duration private certificate and a signature of loan materials submitted by a user node at a sharing node;
and auditing the user node according to the received processed loan information, and judging whether to pay the user node according to a preset rule.
7. The method of claim 6, wherein the receiving user node is further configured to, prior to the loan material information submitted in the predetermined format:
the user node registers to an identity authentication node by providing identity information, the identity authentication node verifies the identity information of the user node, and a user ID and a public and private key pair of the user node are generated and distributed to the user node if the verification is passed;
the sharing node, the request node and the auditing node register to the identity authentication node by providing enterprise qualification information, the identity authentication node verifies the enterprise qualification information, and respective node IDs and public and private key pairs are generated for the sharing node, the request node and the auditing node after verification is passed and distributed to corresponding nodes;
the identity authentication node registers a user ID, a sharing node ID, a requesting node ID and an auditing node ID in a blockchain network.
8. The method according to claim 6, wherein the auditing the user node according to the received processed loan information, and determining whether to pay the user node according to preset rules, comprises:
verifying the effectiveness of the historical loan amount private voucher, the overdue amount private voucher and the overdue duration private voucher through a private voucher verification function;
determining the overdue condition of the user node at the sharing node according to the overdue amount multi-party safety certificate and the overdue duration multi-party safety certificate;
verifying the validity of the loan material signature submitted by the user node at the sharing node through a signature verification function;
and comprehensively evaluating and determining whether to pay according to the loan information of the user node.
9. The method of claim 6, wherein:
the user node generates a loan amount private voucher by using a private key of the user node and the loan amount submitted in the loan material information;
the user node synthesizes a self private key and an audit node public key into a re-encryption key, and encrypts the ciphertext through the re-encryption key to obtain a re-encrypted ciphertext;
and issuing the loan amount private certificate and the re-encrypted ciphertext to a block chain, and verifying the validity of loan information through the audit node.
10. The method of claim 9, wherein verifying the validity of loan information by the audit node comprises:
the audit node decrypts the re-encrypted ciphertext by using a private key of the audit node to obtain loan material information of the user node, a loan material information signature of the user node and a loan amount private voucher;
the audit node verifies the validity of the signature of the user node through a signature verification function;
if the signature verification is valid, obtaining the loan amount of the user node through the loan material information of the user node, and constructing a certificate according to the user public key and the loan amount of the user node;
if the construction certificate is equal to the loan amount private certificate, judging that the loan is valid;
the construction certificate cθThe calculation formula comprises:
cθ=RA+υH
wherein, cθTo construct a certificate, RAFor user node public key, v for user node creditThe sum of money is H which is the base point of the elliptic curve.
11. A secure multi-party computation and blockchain based risk data sharing system, the system comprising:
the system comprises user nodes, sharing nodes and request nodes;
the user node initiates a loan application to the request node;
the request node sends a loan history information query request to the sharing node and receives a query result;
the sharing node acquires a user node ID, calculates a hash value of the user node ID, and queries historical loan information of the user node according to the hash value;
the sharing node acquires a private voucher of the historical loan amount of the user node;
the sharing node calculates an overdue amount private certificate and an overdue duration private certificate by using a private key of the sharing node and the historical loan information obtained by inquiry;
the sharing node constructs a multi-party safety certificate of the overdue amount and a multi-party safety certificate of the overdue duration of the loan of the user node;
the sharing node shares the overdue amount multi-party safety certificate, the overdue duration multi-party safety certificate, the historical loan amount private certificate, the overdue duration private certificate and the signature of the user node loan submission material to the request node.
12. The system of claim 11, wherein:
the sharing node comprises a loan information query unit;
the loan information inquiry unit inquires the hash value through a bidirectional cache linked list in the cache, and the linked list pointer traverses the linked list in a clockwise and anticlockwise bidirectional cycle mode at the current position of the bidirectional cycle linked list;
if the hash value is found, extracting historical loan information of the user node corresponding to the hash value, and adding 1 to the access frequency of the position where the hash value is located;
if the hash value is not found after the bidirectional circulation traversal for one week, accessing a database and extracting the historical loan information of the user node in the database; and the pointer of the bidirectional circular linked list continuously moves in two directions, the cache position with the lowest first access position is found out, the hash value is filled and replaced to the position, and the access times of the replacement position are added by 1.
13. The system of claim 11, wherein:
the historical loan amount privacy voucher calculation formula comprises the following steps:
cloan=ruG+vloanH
the overdue amount private voucher calculation formula comprises the following steps:
coverdue=rBG+voverdueH
the expiration duration private voucher calculation formula comprises:
cd=rBG+doverdueH
wherein, r isuIs a user node private key, rBTo share a node private key, vloanV for inquiring the loan amount in the acquired historical loan information, theoverdueD, the overdue amount of the user node in the acquired historical loan information is inquiredoverdueFor inquiring the overdue time of the user node in the acquired historical loan information, G and H are base points of an elliptic curve, and cloanPrivacy of the voucher for the historical loan amount, said coverdueFor overdue amount private vouchers, said cdA private voucher for overdue duration;
the overdue duration multiparty security certification calculation formula comprises the following steps:
wherein, the f (x)d,yd) For long timeout multiparty security certification, the xdThe expiration time of the user nodeY isdIs the timeout duration threshold of the requesting node;
the overdue amount multiparty security certification calculation formula comprises the following steps:
wherein, the f (x)v,yv) For overdue amount multiparty security certification, the xvFor the overdue amount of the user node, yvIs the overdue amount threshold of the requesting node.
14. The system of claim 13, wherein:
the sharing node comprises a multi-party security certification construction unit;
the multi-party security certification constructing unit generates a system public and private key pair through a homomorphic encryption key generating algorithm and sends the system public key to a request node;
the multi-party security certification construction unit encrypts each element in the shared node parameter set by using a system public key according to a homomorphic encryption algorithm to generate a ciphertext set; the shared node parameter set comprises a parameter true value and n-1 confusion values, wherein n is a positive integer greater than 1;
the multi-party security certification construction unit sends the ciphertext set to a request node;
the request node generates a request node parameter set, wherein the request node parameter set comprises a threshold true value corresponding to a parameter true value in a sharing node parameter set and n-1 confusion values;
the request node integrates and calculates elements in the request node parameter set and elements in the ciphertext set to obtain a set to be replaced;
the multi-party security certification construction unit receives a replaced set which is sent by the request node and obtained by randomly replacing a set to be replaced;
the multi-party security certification construction unit decrypts the replaced set to obtain a decryption result; the decryption result comprises a constructed multi-party security certificate;
the parameter true value in the sharing node parameter set comprises an overdue amount and an overdue duration, and the parameter true value in the requesting node parameter set comprises an overdue amount threshold and an overdue duration threshold; the multi-party security certificate comprises a multi-party security certificate of overdue amount and a multi-party security certificate of overdue duration.
15. The system of claim 14, wherein:
the integrated calculation formula includes:
E(zdi)=E(xdi-ydi)
E(fdi)=E(xdi-2xdiydi+ydi)
E(sdi)=E(sd(i-1)+fdi) Wherein s isd0=0
E(rdi)=E(zdi+sdiSd(i-1))
Wherein E (m) is the homomorphic encryption algorithm, and the system public key is used for encrypting a plaintext m; the E (x)di) For the ith element in the ciphertext set, ydiFor the ith element in the requesting node parameter set, the zdiIs a first intermediate variable, said fdiIs a second intermediate variable, said sdiIs a third intermediate variable, said E (r)di) Is the ith element in the set to be replaced;
the random permutation calculation formula includes:
wherein E (m) is the homomorphic encryption algorithm, xdiFor sharing the ith element in the node parameter set, the ydiFor the ith element in the parameter set of the requesting node, sdiIs a third intermediate variable, said E (r)di) For the ith element in the set to be permuted, Eθ(rdi) Is the ith element in the permuted set.
16. A system for loan auditing using the risk data sharing system of claim 11, wherein:
the request node receives loan material information submitted by the user node according to a preset format;
the request node encrypts the loan material information and the loan material information signature according to an asymmetric encryption algorithm by using a user node public key to obtain a ciphertext, stores the ciphertext into a distributed file system, and stores a hash value of the ciphertext into a block chain network; the loan material information signature is obtained by encrypting a private key of the user node;
the request node sends a user node ID to a sharing node and receives processed loan information obtained by the sharing node according to the risk data sharing method; the processed loan information comprises overdue amount multi-party safety certification, overdue duration multi-party safety certification, a historical loan amount private certificate, an overdue duration private certificate and a signature of loan materials submitted by a user node at a sharing node;
and the request node checks the user node according to the received processed loan information and judges whether to pay the user node according to a preset rule.
17. The system of claim 16, wherein:
the system also comprises an identity authentication node, wherein the identity authentication node is used for receiving identity information of the user node, the sharing node, the request node and the auditing node and distributing corresponding public and private key pairs and node IDs;
the identity authentication node registers the identity information provided by the user node and verifies the identity information of the user node; if the verification is passed, generating a user ID and a public and private key pair of the user node, and distributing the user ID and the public and private key pair to the user node;
the identity authentication node registers enterprise qualification information provided by the sharing node, the request node and the auditing node and verifies the enterprise qualification information; after the verification is passed, respective node IDs and public and private key pairs are generated for the sharing node, the request node and the auditing node and are distributed to corresponding nodes;
the identity authentication node registers a user ID, a sharing node ID, a requesting node ID and an auditing node ID in a blockchain network.
18. The system of claim 16, wherein:
the requesting node verifies the validity of the historical loan amount private voucher, the overdue amount private voucher and the overdue duration private voucher through a private voucher verification function;
the request node judges the overdue condition of the user node at the sharing node according to the overdue amount multi-party safety certificate and the overdue duration multi-party safety certificate;
the requesting node verifies the validity of the loan material signature submitted by the user node at the sharing node through a signature verification function;
and the requesting node comprehensively evaluates and determines whether to put money on the user node according to the loan information of the user node.
19. The system of claim 16, wherein:
the user node generates a loan amount private voucher by using a private key of the user node and the loan amount submitted in the loan material information;
the user node synthesizes a re-encryption key by using a self private key and an audit node public key, and encrypts the ciphertext through the re-encryption key to obtain a re-encrypted ciphertext;
and the request node issues the loan amount private certificate and the re-encrypted ciphertext to a block chain, and the validity of loan information is verified through the audit node.
20. The system of claim 19, wherein:
the audit node decrypts the re-encrypted ciphertext by using a private key of the audit node to obtain loan material information of the user node, a loan material information signature of the user node and a loan amount private voucher;
the audit node verifies the validity of the signature of the user node through a signature verification function;
if the signature verification is valid, obtaining the loan amount of the user node through the loan material information of the user node, and constructing a certificate according to the user public key and the loan amount of the user node; if the construction certificate is equal to the loan amount private certificate, judging that the loan is valid;
the construction certificate cθThe calculation formula comprises:
cθ=RA+vH
wherein, cθTo construct a certificate, RAThe method is characterized in that the method is a user node public key, v is the user node loan amount, and H is an elliptic curve base point.
Priority Applications (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN202010266336.8A CN111611609B (en) | 2020-04-07 | 2020-04-07 | Risk data sharing method and system based on secure multiparty calculation and blockchain |
Applications Claiming Priority (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN202010266336.8A CN111611609B (en) | 2020-04-07 | 2020-04-07 | Risk data sharing method and system based on secure multiparty calculation and blockchain |
Publications (2)
| Publication Number | Publication Date |
|---|---|
| CN111611609A true CN111611609A (en) | 2020-09-01 |
| CN111611609B CN111611609B (en) | 2023-05-23 |
Family
ID=72199342
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| CN202010266336.8A Active CN111611609B (en) | 2020-04-07 | 2020-04-07 | Risk data sharing method and system based on secure multiparty calculation and blockchain |
Country Status (1)
| Country | Link |
|---|---|
| CN (1) | CN111611609B (en) |
Cited By (11)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN112184219A (en) * | 2020-09-22 | 2021-01-05 | 远光软件股份有限公司 | Secure multiparty computing method, electronic device and storage medium |
| CN112613077A (en) * | 2021-01-22 | 2021-04-06 | 支付宝(杭州)信息技术有限公司 | Privacy-protecting multi-party data processing method, device and system |
| CN112884564A (en) * | 2021-01-08 | 2021-06-01 | 四川新网银行股份有限公司 | Real-time debt sharing risk management and control system and method based on multi-party security calculation |
| CN113449336A (en) * | 2021-06-11 | 2021-09-28 | 电子科技大学 | Shared data processing method based on safe multi-party privacy protection in block chain |
| CN113496436A (en) * | 2021-07-08 | 2021-10-12 | 杭州煋辰数智科技有限公司 | Wind control model parameter analysis method based on safe multi-party calculation and application thereof |
| CN113591131A (en) * | 2021-08-20 | 2021-11-02 | 南京可信区块链与算法经济研究院有限公司 | Loan total calculation method for protecting user privacy |
| CN113674077A (en) * | 2021-07-23 | 2021-11-19 | 华南理工大学 | Consumer credit risk prevention method, system, equipment and storage medium |
| CN113706145A (en) * | 2021-08-02 | 2021-11-26 | 杭州复杂美科技有限公司 | Proxy transaction method, device and storage medium for hiding transaction amount |
| CN115131121A (en) * | 2021-03-24 | 2022-09-30 | 阿里巴巴新加坡控股有限公司 | Credit assessment method, device, system and storage medium |
| CN115174049A (en) * | 2022-06-20 | 2022-10-11 | 杭州电子科技大学 | Safe multiparty ciphertext computing method based on block chain |
| CN116862668A (en) * | 2023-09-05 | 2023-10-10 | 杭州度言软件有限公司 | Intelligent collecting accelerating method for improving collecting accelerating efficiency |
Citations (12)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN105373955A (en) * | 2015-12-08 | 2016-03-02 | 布比(北京)网络技术有限公司 | Multi-signature-based digital asset treatment method and device |
| CN107180350A (en) * | 2017-03-31 | 2017-09-19 | 唐晓领 | A method, device and system for multi-party sharing of transaction metadata based on blockchain |
| CN107944887A (en) * | 2017-12-14 | 2018-04-20 | 法信公证云(厦门)科技有限公司 | A kind of personalized lending Risk Pre-control method based on block chain |
| CN108492175A (en) * | 2018-03-28 | 2018-09-04 | 深圳市元征科技股份有限公司 | A kind of financial credit risk control method and server |
| CN109472690A (en) * | 2018-10-25 | 2019-03-15 | 深圳壹账通智能科技有限公司 | The loan measures and procedures for the examination and approval, device, storage medium and electronic equipment based on block chain |
| US20190114706A1 (en) * | 2017-10-17 | 2019-04-18 | SALT Lending Holdings, Inc. | Blockchain oracle for managing loans collateralized by digital assets |
| US20190251270A1 (en) * | 2018-11-07 | 2019-08-15 | Alibaba Group Holding Limited | Regulating blockchain confidential transactions |
| WO2019159083A1 (en) * | 2018-02-13 | 2019-08-22 | Andrew Morabito | Method and system for a value based attestation of counterparty credibility |
| CN110430161A (en) * | 2019-06-27 | 2019-11-08 | 布比(北京)网络技术有限公司 | It is a kind of that data anonymous sharing method and system are supervised based on block chain |
| CN110490723A (en) * | 2018-05-15 | 2019-11-22 | 全球智能股份有限公司 | Loan administration method and system under block chain |
| US10521780B1 (en) * | 2015-12-16 | 2019-12-31 | United Services Automobile Association (Usaa) | Blockchain based transaction management |
| US20200004973A1 (en) * | 2018-06-29 | 2020-01-02 | Alibaba Group Holding Limited | Method and apparatus for obtaining input of secure multiparty computation protocol |
-
2020
- 2020-04-07 CN CN202010266336.8A patent/CN111611609B/en active Active
Patent Citations (12)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN105373955A (en) * | 2015-12-08 | 2016-03-02 | 布比(北京)网络技术有限公司 | Multi-signature-based digital asset treatment method and device |
| US10521780B1 (en) * | 2015-12-16 | 2019-12-31 | United Services Automobile Association (Usaa) | Blockchain based transaction management |
| CN107180350A (en) * | 2017-03-31 | 2017-09-19 | 唐晓领 | A method, device and system for multi-party sharing of transaction metadata based on blockchain |
| US20190114706A1 (en) * | 2017-10-17 | 2019-04-18 | SALT Lending Holdings, Inc. | Blockchain oracle for managing loans collateralized by digital assets |
| CN107944887A (en) * | 2017-12-14 | 2018-04-20 | 法信公证云(厦门)科技有限公司 | A kind of personalized lending Risk Pre-control method based on block chain |
| WO2019159083A1 (en) * | 2018-02-13 | 2019-08-22 | Andrew Morabito | Method and system for a value based attestation of counterparty credibility |
| CN108492175A (en) * | 2018-03-28 | 2018-09-04 | 深圳市元征科技股份有限公司 | A kind of financial credit risk control method and server |
| CN110490723A (en) * | 2018-05-15 | 2019-11-22 | 全球智能股份有限公司 | Loan administration method and system under block chain |
| US20200004973A1 (en) * | 2018-06-29 | 2020-01-02 | Alibaba Group Holding Limited | Method and apparatus for obtaining input of secure multiparty computation protocol |
| CN109472690A (en) * | 2018-10-25 | 2019-03-15 | 深圳壹账通智能科技有限公司 | The loan measures and procedures for the examination and approval, device, storage medium and electronic equipment based on block chain |
| US20190251270A1 (en) * | 2018-11-07 | 2019-08-15 | Alibaba Group Holding Limited | Regulating blockchain confidential transactions |
| CN110430161A (en) * | 2019-06-27 | 2019-11-08 | 布比(北京)网络技术有限公司 | It is a kind of that data anonymous sharing method and system are supervised based on block chain |
Non-Patent Citations (3)
| Title |
|---|
| PAULA FRAGA-LAMAS AND TIAGO M. FERNÁNDEZ-CARAMÉS: "A Review on Blockchain Technologies for an Advanced and Cyber-Resilient Automotive Industry" * |
| 王晓;: "区块链赋能银行供应链金融" * |
| 王洁;魏生;戴科冕;: "基于区块链的科技金融大数据开放共享体系研究" * |
Cited By (16)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN112184219A (en) * | 2020-09-22 | 2021-01-05 | 远光软件股份有限公司 | Secure multiparty computing method, electronic device and storage medium |
| CN112884564A (en) * | 2021-01-08 | 2021-06-01 | 四川新网银行股份有限公司 | Real-time debt sharing risk management and control system and method based on multi-party security calculation |
| CN112613077A (en) * | 2021-01-22 | 2021-04-06 | 支付宝(杭州)信息技术有限公司 | Privacy-protecting multi-party data processing method, device and system |
| CN112613077B (en) * | 2021-01-22 | 2021-07-23 | 支付宝(杭州)信息技术有限公司 | Privacy-protecting multi-party data processing method, device and system |
| CN115131121A (en) * | 2021-03-24 | 2022-09-30 | 阿里巴巴新加坡控股有限公司 | Credit assessment method, device, system and storage medium |
| CN113449336A (en) * | 2021-06-11 | 2021-09-28 | 电子科技大学 | Shared data processing method based on safe multi-party privacy protection in block chain |
| CN113496436A (en) * | 2021-07-08 | 2021-10-12 | 杭州煋辰数智科技有限公司 | Wind control model parameter analysis method based on safe multi-party calculation and application thereof |
| CN113674077A (en) * | 2021-07-23 | 2021-11-19 | 华南理工大学 | Consumer credit risk prevention method, system, equipment and storage medium |
| CN113706145A (en) * | 2021-08-02 | 2021-11-26 | 杭州复杂美科技有限公司 | Proxy transaction method, device and storage medium for hiding transaction amount |
| CN113706145B (en) * | 2021-08-02 | 2023-05-30 | 杭州复杂美科技有限公司 | Proxy transaction method, device and storage medium for hiding transaction amount |
| CN113591131A (en) * | 2021-08-20 | 2021-11-02 | 南京可信区块链与算法经济研究院有限公司 | Loan total calculation method for protecting user privacy |
| CN113591131B (en) * | 2021-08-20 | 2024-02-13 | 南京可信区块链与算法经济研究院有限公司 | Loan amount calculation method for protecting user privacy |
| CN115174049A (en) * | 2022-06-20 | 2022-10-11 | 杭州电子科技大学 | Safe multiparty ciphertext computing method based on block chain |
| CN115174049B (en) * | 2022-06-20 | 2025-07-08 | 杭州电子科技大学 | Safe multiparty ciphertext calculation method based on blockchain |
| CN116862668A (en) * | 2023-09-05 | 2023-10-10 | 杭州度言软件有限公司 | Intelligent collecting accelerating method for improving collecting accelerating efficiency |
| CN116862668B (en) * | 2023-09-05 | 2023-11-24 | 杭州度言软件有限公司 | Intelligent collecting accelerating method for improving collecting accelerating efficiency |
Also Published As
| Publication number | Publication date |
|---|---|
| CN111611609B (en) | 2023-05-23 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| CN111611609B (en) | Risk data sharing method and system based on secure multiparty calculation and blockchain | |
| US11900368B2 (en) | Method and system for zero-knowledge and identity based key management for decentralized applications | |
| US12015716B2 (en) | System and method for securely processing an electronic identity | |
| CN114521319B (en) | Lattice-based signature with uniform secret | |
| Li et al. | Eunomia: Anonymous and secure vehicular digital forensics based on blockchain | |
| CN113114451B (en) | Data statistical analysis method and system for enterprise cloud ERP system based on homomorphic encryption | |
| CN108765240B (en) | Block chain-based inter-institution customer verification method, transaction supervision method and device | |
| US12219069B1 (en) | Signcrypted biometric electronic signature tokens | |
| JP2023098847A (en) | Apparatus, method, computer program (selective audit process for privacy-preserving blockchain) | |
| Alharbi et al. | Survey on homomorphic encryption and address of new trend | |
| CN111160908B (en) | Blockchain-based supply chain transaction privacy protection system, method and related equipment | |
| US11621844B2 (en) | Secure data transfer system and method | |
| Bojjagani et al. | SSMBP: A secure SMS-based mobile banking protocol with formal verification | |
| Arora et al. | Hybrid algorithm designed for handling remote integrity check mechanism over dynamic cloud environment | |
| Wu et al. | Cloud-edge data encryption in the internet of vehicles using Zeckendorf representation | |
| CN108805574B (en) | Transaction method and system based on privacy protection | |
| Ahmad et al. | A secure network communication protocol based on text to barcode encryption algorithm | |
| Kumbhakar et al. | CTEA: Chaos based tiny encryption algorithm using ECDH and TinkerBell map for data security in supply chain management | |
| Danezis et al. | Towards ensuring client-side computational integrity | |
| CN114679258B (en) | Inter-bank risk customer information sharing method, storage medium and electronic device | |
| Sivasundari et al. | RETRACTED ARTICLE: Hybrid aggregated signcryption scheme using multi-constraints differential evolution algorithm for security | |
| CN113793149A (en) | Off-line transaction authentication system and method, central server and client | |
| US20250023742A1 (en) | Method, System & Computer Program Product for Multiple Signatures and Notaries for Digital Notarizations | |
| Kairi et al. | Emerging Trends in Cryptography and Security | |
| AU2021103828A4 (en) | A novel system and auditing technique for cloud based digital forensic readiness with integrity and privacy preservation of health care data |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| PB01 | Publication | ||
| PB01 | Publication | ||
| SE01 | Entry into force of request for substantive examination | ||
| SE01 | Entry into force of request for substantive examination | ||
| GR01 | Patent grant | ||
| GR01 | Patent grant |