CN111402463A - Vehicle authorization method and device based on vehicle key information - Google Patents
Vehicle authorization method and device based on vehicle key information Download PDFInfo
- Publication number
- CN111402463A CN111402463A CN202010188569.0A CN202010188569A CN111402463A CN 111402463 A CN111402463 A CN 111402463A CN 202010188569 A CN202010188569 A CN 202010188569A CN 111402463 A CN111402463 A CN 111402463A
- Authority
- CN
- China
- Prior art keywords
- vehicle
- information
- key information
- terminal
- server
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Pending
Links
Images
Classifications
-
- G—PHYSICS
- G07—CHECKING-DEVICES
- G07C—TIME OR ATTENDANCE REGISTERS; REGISTERING OR INDICATING THE WORKING OF MACHINES; GENERATING RANDOM NUMBERS; VOTING OR LOTTERY APPARATUS; ARRANGEMENTS, SYSTEMS OR APPARATUS FOR CHECKING NOT PROVIDED FOR ELSEWHERE
- G07C9/00—Individual registration on entry or exit
- G07C9/00174—Electronically operated locks; Circuits therefor; Nonmechanical keys therefor, e.g. passive or active electrical keys or other data carriers without mechanical keys
- G07C9/00571—Electronically operated locks; Circuits therefor; Nonmechanical keys therefor, e.g. passive or active electrical keys or other data carriers without mechanical keys operated by interacting with a central unit
-
- G—PHYSICS
- G07—CHECKING-DEVICES
- G07C—TIME OR ATTENDANCE REGISTERS; REGISTERING OR INDICATING THE WORKING OF MACHINES; GENERATING RANDOM NUMBERS; VOTING OR LOTTERY APPARATUS; ARRANGEMENTS, SYSTEMS OR APPARATUS FOR CHECKING NOT PROVIDED FOR ELSEWHERE
- G07C9/00—Individual registration on entry or exit
- G07C9/00174—Electronically operated locks; Circuits therefor; Nonmechanical keys therefor, e.g. passive or active electrical keys or other data carriers without mechanical keys
- G07C9/00857—Electronically operated locks; Circuits therefor; Nonmechanical keys therefor, e.g. passive or active electrical keys or other data carriers without mechanical keys where the code of the data carrier can be programmed
-
- G—PHYSICS
- G07—CHECKING-DEVICES
- G07C—TIME OR ATTENDANCE REGISTERS; REGISTERING OR INDICATING THE WORKING OF MACHINES; GENERATING RANDOM NUMBERS; VOTING OR LOTTERY APPARATUS; ARRANGEMENTS, SYSTEMS OR APPARATUS FOR CHECKING NOT PROVIDED FOR ELSEWHERE
- G07C9/00—Individual registration on entry or exit
- G07C9/00174—Electronically operated locks; Circuits therefor; Nonmechanical keys therefor, e.g. passive or active electrical keys or other data carriers without mechanical keys
- G07C9/00896—Electronically operated locks; Circuits therefor; Nonmechanical keys therefor, e.g. passive or active electrical keys or other data carriers without mechanical keys specially adapted for particular uses
-
- G—PHYSICS
- G07—CHECKING-DEVICES
- G07C—TIME OR ATTENDANCE REGISTERS; REGISTERING OR INDICATING THE WORKING OF MACHINES; GENERATING RANDOM NUMBERS; VOTING OR LOTTERY APPARATUS; ARRANGEMENTS, SYSTEMS OR APPARATUS FOR CHECKING NOT PROVIDED FOR ELSEWHERE
- G07C9/00—Individual registration on entry or exit
- G07C9/00174—Electronically operated locks; Circuits therefor; Nonmechanical keys therefor, e.g. passive or active electrical keys or other data carriers without mechanical keys
- G07C9/00857—Electronically operated locks; Circuits therefor; Nonmechanical keys therefor, e.g. passive or active electrical keys or other data carriers without mechanical keys where the code of the data carrier can be programmed
- G07C2009/0088—Electronically operated locks; Circuits therefor; Nonmechanical keys therefor, e.g. passive or active electrical keys or other data carriers without mechanical keys where the code of the data carrier can be programmed centrally
Landscapes
- Physics & Mathematics (AREA)
- General Physics & Mathematics (AREA)
- Management, Administration, Business Operations System, And Electronic Commerce (AREA)
Abstract
本申请公开了一种基于车钥匙信息的车辆授权方法和装置,涉及物联网技术领域。具体实现方案为:第一终端获取车主输入的创建数据,并将创建数据发送至服务器,以供服务器根据创建数据创建车钥匙信息;其中,创建数据包括:车辆标识和候选用车人的身份验证信息;第一终端接收服务器发送的车钥匙信息;第一终端响应于车主将车钥匙信息发送至目标用车人的操作,将车钥匙信息发送至目标用车人的第二终端,以使目标用车人的身份信息被身份验证信息验证通过后,获得车辆标识对应的车辆的使用权。本实施例以使车钥匙的交接摆脱空间的限制,同时保证车钥匙交接的便捷性和安全性。
The application discloses a vehicle authorization method and device based on vehicle key information, and relates to the technical field of the Internet of Things. The specific implementation scheme is as follows: the first terminal obtains the creation data input by the car owner, and sends the creation data to the server, so that the server can create the car key information according to the creation data; wherein the creation data includes: the vehicle identification and the identity verification of the candidate vehicle user information; the first terminal receives the car key information sent by the server; the first terminal sends the car key information to the second terminal of the target user in response to the operation of the car owner to send the car key information to the target user, so that the target After the identity information of the vehicle user is verified by the identity verification information, the right to use the vehicle corresponding to the vehicle identification is obtained. In this embodiment, the handover of the car key is free from the limitation of space, and at the same time, the convenience and safety of the handover of the car key are ensured.
Description
技术领域technical field
本申请涉及计算机技术,尤其涉及物联网技术领域。The present application relates to computer technology, in particular to the technical field of the Internet of Things.
背景技术Background technique
如今汽车已经成为人们最主要的出行工具之一,有非常好的灵活性和舒适性。由于经济、交通、车位等方面的限制,家庭中每个人都有一辆汽车是不太现实的。更常见的情况是汽车作为家庭公共的出行工具,一家人公用一辆车,甚至汽车要借给其他亲戚和朋友使用。Nowadays, cars have become one of the most important travel tools for people, with very good flexibility and comfort. Due to economic, traffic, parking space and other constraints, it is not realistic for everyone in the family to have a car. It is more common that the car is used as a public travel tool for the family, the family shares a car, and even the car is lent to other relatives and friends for use.
一般来说,家庭成员要用车或者车辆借用是需要面对面、手把手的交接车钥匙,然后才能使用汽车。生活中很多情况下并不容易跨越空间拿到车钥匙,这时就要花费时间和金钱来实现,非常不方便。Generally speaking, when family members want to use a car or borrow a vehicle, they need to hand over the car keys face to face and hand in hand before they can use the car. In many situations in life, it is not easy to get the car key across the space. At this time, it takes time and money to realize it, which is very inconvenient.
发明内容SUMMARY OF THE INVENTION
本申请实施例提供了一种基于车钥匙信息的授权、受权方法,车钥匙信息的处理方法、装置、终端、服务器和存储介质,以使车钥匙的交接摆脱空间的限制,同时保证车钥匙交接的便捷性和安全性。The embodiments of the present application provide an authorization and authorization method based on car key information, a method, device, terminal, server and storage medium for processing car key information, so that the handover of the car key can get rid of the limitation of space and ensure the handover of the car key at the same time. convenience and security.
第一方面,本申请实施例提供了一种基于车钥匙信息的车辆授权方法,包括:In a first aspect, an embodiment of the present application provides a vehicle authorization method based on vehicle key information, including:
第一终端获取车主输入的创建数据,并将所述创建数据发送至服务器,以供所述服务器根据所述创建数据创建车钥匙信息;其中,所述创建数据包括:车辆标识和候选用车人的身份验证信息;The first terminal acquires the creation data input by the car owner, and sends the created data to the server, so that the server can create car key information according to the created data; wherein, the created data includes: vehicle identification and candidate vehicle users authentication information;
所述第一终端接收所述服务器发送的所述车钥匙信息;receiving, by the first terminal, the vehicle key information sent by the server;
所述第一终端响应于所述车主将所述车钥匙信息发送至目标用车人的操作,将所述车钥匙信息发送至所述目标用车人的第二终端,以使所述目标用车人的身份信息被所述身份验证信息验证通过后,获得所述车辆标识对应的车辆的使用权。In response to the operation of the car owner to send the car key information to the target car user, the first terminal sends the car key information to the second terminal of the target car user, so that the target user can use the car key information. After the identity information of the vehicle occupant is verified by the identity verification information, the right to use the vehicle corresponding to the vehicle identification is obtained.
本申请实施例中,第一终端获取车主输入的车辆标识和候选用车人的身份验证信息,并通过服务器生成车钥匙信息,该车钥匙信息包含候选用车人的身份验证信息,保留了车主对用车人的选择权;通过第一终端响应于所述车主将所述车钥匙信息发送至目标用车人的操作,将所述车钥匙信息发送至所述目标用车人的第二终端,车主可自主将车钥匙信息发送至选定的用车人,在目标用车人的身份信息被所述身份验证信息验证通过后,获得所述车辆标识对应的车辆的使用权,可见,本实施例通过车主向用车人发送车钥匙信息,并结合身份验证的方法实现车辆使用权的授予,不需要复杂的加密和验证程序,提高了授予过程的安全性和便捷性。In the embodiment of the present application, the first terminal obtains the vehicle identification and the identity verification information of the candidate vehicle user input by the vehicle owner, and generates the vehicle key information through the server. The vehicle key information includes the identity verification information of the candidate vehicle user, and retains the vehicle owner The right to choose the vehicle user; in response to the operation of the vehicle owner sending the vehicle key information to the target vehicle user through the first terminal, the vehicle key information is sent to the second terminal of the target vehicle user , the car owner can autonomously send the car key information to the selected car user, and after the identity information of the target car user is verified by the identity verification information, the right to use the vehicle corresponding to the vehicle identification is obtained. In the embodiment, the vehicle owner sends the vehicle key information to the vehicle user, and the vehicle use right is granted in combination with the method of identity verification, which does not require complex encryption and verification procedures, and improves the security and convenience of the granting process.
可选的,第一终端响应于所述车主将所述车钥匙信息发送至目标用车人的操作,将所述车钥匙信息发送至所述目标用车人的第二终端,包括:Optionally, the first terminal sends the car key information to the second terminal of the target vehicle user in response to the operation of the vehicle owner to send the vehicle key information to the target vehicle user, including:
所述第一终端响应于车主通过社交应用程序将所述车钥匙信息分享至所述车主与目标用车人的聊天窗口中的操作,将所述车钥匙信息发送至所述目标用车人的第二终端。The first terminal, in response to the operation of the car owner sharing the car key information to the chat window between the car owner and the target car user through a social application, sends the car key information to the target car user. second terminal.
上述申请中的一种可选实施方式,车主分享车钥匙信息的平台是社交应用程序,具体可以将车钥匙信息分享至聊天窗口中,从而通过在聊天窗口中分享的操作,实现车钥匙信息的发送,操作灵活、便捷,提高用户体验。In an optional implementation manner of the above application, the platform for car owners to share car key information is a social application program, and specifically, the car key information can be shared in the chat window, so that the sharing of car key information can be achieved through the operation of sharing in the chat window. Sending, the operation is flexible and convenient, and the user experience is improved.
第二方面,本申请实施例提供了一种基于车钥匙信息的车辆受权方法,包括:In a second aspect, an embodiment of the present application provides a vehicle authorization method based on vehicle key information, including:
第二终端接收第一终端发送的车钥匙信息,所述车钥匙信息是服务器根据创建数据创建的,所述创建数据包括:车辆标识和候选用车人的身份验证信息;The second terminal receives the car key information sent by the first terminal, the car key information is created by the server according to the creation data, and the creation data includes: the vehicle identification and the identity verification information of the candidate vehicle user;
所述第二终端响应于目标用车人对所述车钥匙信息的触发操作,将所述目标用车人的身份信息发送至所述服务器,以供所述服务器根据所述候选用车人的身份验证信息对所述目标用车人的身份信息进行验证,并返回验证结果;In response to the target vehicle user's triggering operation on the car key information, the second terminal sends the target vehicle user's identity information to the server for the server to use according to the candidate vehicle user's identification information. The identity verification information verifies the identity information of the target vehicle user, and returns the verification result;
如果验证通过,所述第二终端获得所述车辆标识对应的车辆的使用权。If the verification is passed, the second terminal obtains the right to use the vehicle corresponding to the vehicle identification.
本申请实施例中,第二终端接收车钥匙信息后,响应于目标用车人对车钥匙信息的触发操作,通过服务器进行身份信息的验证,如果身份信息验证通过,则获得车辆的使用权。可见,本申请实施例中目标用车人只需要触发车钥匙信息即可进行验证并受权,操作方式简单;而且通过身份验证的方式也能保证安全性,避免车钥匙信息别其他人盗用。In the embodiment of the present application, after receiving the vehicle key information, the second terminal verifies the identity information through the server in response to the triggering operation of the vehicle key information by the target vehicle user, and obtains the right to use the vehicle if the identity information verification passes. It can be seen that in the embodiment of the present application, the target vehicle user only needs to trigger the vehicle key information to verify and authorize, and the operation method is simple; and the identity verification method can also ensure security and prevent other people from embezzling the vehicle key information.
可选的,车钥匙信息是所述服务器对所述创建数据进行加密得到密文,并将所述密文添加到身份验证页面网址中得到的;Optionally, the car key information is obtained by the server encrypting the created data to obtain ciphertext, and adding the ciphertext to the URL of the authentication page;
所述第二终端响应于目标用车人对所述车钥匙信息的触发操作,将所述目标用车人的身份信息发送至服务器,包括:The second terminal sends the identity information of the target vehicle user to the server in response to the triggering operation of the vehicle key information by the target vehicle user, including:
所述第二终端响应于目标用车人对所述车钥匙信息的触发操作,向所述服务器发送所述身份验证页面网址的请求信息,以供所述服务器向所述第二终端返回所述身份验证页面,并从所述身份验证页面网址中提取密文,对所述密文进行解密得到所述候选用车人的身份验证信息;In response to the target vehicle user's triggering operation on the car key information, the second terminal sends the request information of the URL of the identity verification page to the server, so that the server can return the information to the second terminal. identity verification page, and extract the ciphertext from the URL of the identity verification page, and decrypt the ciphertext to obtain the identity verification information of the candidate vehicle user;
所述第二终端响应于所述目标用车人在所述身份验证页面上的输入操作,从所述身份验证页面上提取所述目标用车人的身份信息并发送至所述服务器。In response to the input operation of the target vehicle user on the identity verification page, the second terminal extracts the identity information of the target vehicle user from the identity verification page and sends it to the server.
上述申请中的一种可选实施方式,车钥匙信息实质是身份验证页面网址,通过触发车钥匙信息,在第二终端展示身份验证页面,以提取目标用车人的身份信息;同时,服务器从身份验证页面网址中解密出身份验证信息,以根据身份验证信息对目标用车人的身份信息进行验证。本申请实施例提供了车钥匙信息的具体内容,以及采用车钥匙信息进行身份验证的流程,从而通过触发车钥匙信息,展示身份验证信息,巧妙、便捷地上传身份信息,同时,服务器可以直接从身份验证页面网址中获取到身份验证信息,流程简单,不需要复杂的验证程序;通过对创建数据进行加密得到密文,避免创建数据被盗用,保证了一定的安全性。In an optional implementation manner in the above application, the car key information is essentially the URL of the identity verification page, and by triggering the car key information, the identity verification page is displayed on the second terminal to extract the identity information of the target vehicle user; The identity verification information is decrypted from the URL of the identity verification page, so as to verify the identity information of the target vehicle user according to the identity verification information. The embodiment of the present application provides the specific content of the car key information and the process of using the car key information for identity verification, so that the identity verification information can be displayed by triggering the car key information, and the identity information can be uploaded smartly and conveniently. The authentication information is obtained from the URL of the authentication page. The process is simple and does not require complex authentication procedures; the ciphertext is obtained by encrypting the created data, which prevents the creation of data from being stolen and ensures a certain degree of security.
可选的,如果验证通过,所述第二终端获得所述车辆标识对应的车辆的使用权,包括:Optionally, if the verification is passed, the second terminal obtains the right to use the vehicle corresponding to the vehicle identification, including:
如果验证通过,所述第二终端接收所述服务器向所述目标用车人的终端发送的授权验证码;If the verification is passed, the second terminal receives the authorization verification code sent by the server to the terminal of the target user;
所述第二终端将目标用车人输入的验证码发送至所述服务器,以供所述服务器将所述验证码与授权验证码比对,如果一致,将所述车辆标识对应的车辆的使用权授予给所述目标用车人。The second terminal sends the verification code input by the target vehicle user to the server, so that the server can compare the verification code with the authorization verification code, and if they are consistent, identify the use of the vehicle corresponding to the vehicle identification The right is granted to the target vehicle user.
上述申请中的一种可选实施方式,考虑到车钥匙信息和用车人的身份信息如果均被其它人获取,其它人可通过所持终端窃取车辆使用权。为了避免出现这种情况,在身份验证通过后,通过授权验证码对发送身份信息的终端是否属于目标用车人进行验证。如果发送身份信息的终端属于目标用车人,则会接收到服务器发送的授权验证码,则可以指导目标用车人输入一致的验证码;如果发送信息的终端不属于目标用车人,而是其它人,则不会接收到服务器发送的授权验证码,其他人也不会输入与授权验证码一致的验证码,从而避免车辆使用权被其它人窃取。In an optional implementation manner in the above application, considering that if both the vehicle key information and the identity information of the vehicle user are obtained by other persons, other persons can steal the right to use the vehicle through the terminal they hold. In order to avoid such a situation, after the identity verification is passed, the authorization verification code is used to verify whether the terminal sending the identity information belongs to the target vehicle user. If the terminal sending the identity information belongs to the target user, it will receive the authorization verification code sent by the server and instruct the target user to input the same verification code; if the terminal sending the information does not belong to the target user, but Others will not receive the authorization verification code sent by the server, and others will not input the verification code consistent with the authorization verification code, so as to avoid the vehicle use right being stolen by others.
可选的,如果验证通过,所述第二终端获得所述车辆标识对应的车辆的使用权,包括:Optionally, if the verification is passed, the second terminal obtains the right to use the vehicle corresponding to the vehicle identification, including:
如果验证通过,所述第二终端展示解锁页面;If the verification is passed, the second terminal displays the unlock page;
所述第二终端响应于所述目标用车人在所述解锁页面上的解锁操作,向所述服务器发送解锁请求,以供所述服务器根据所述解锁请求,解锁所述车辆标识对应的车辆。The second terminal sends an unlocking request to the server in response to the unlocking operation of the target vehicle user on the unlocking page, so that the server can unlock the vehicle corresponding to the vehicle identification according to the unlocking request .
上述申请中的一种可选实施方式,目标用车人通过在解锁页面执行解锁操作,就可以通过服务器解锁车辆,不需要第二终端与车辆进行直接通信,简化了解锁流程,提高了解锁操作的便捷性。In an optional implementation manner of the above application, the target vehicle user can unlock the vehicle through the server by performing the unlocking operation on the unlocking page, and does not require the second terminal to communicate directly with the vehicle, which simplifies the unlocking process and improves the unlocking operation. convenience.
第三方面,本申请实施例提供了一种车钥匙信息的处理方法,包括:In a third aspect, an embodiment of the present application provides a method for processing vehicle key information, including:
服务器接收第一终端发送的创建数据,所述创建数据包括:车辆标识和候选用车人的身份验证信息;The server receives the creation data sent by the first terminal, and the creation data includes: the vehicle identification and the identity verification information of the candidate vehicle user;
所述服务器根据所述创建数据创建车钥匙信息;The server creates vehicle key information according to the creation data;
所述服务器将所述车钥匙信息发送至所述第一终端,以供所述第一终端将所述车钥匙信息发送至所述目标用车人的第二终端;The server sends the car key information to the first terminal, so that the first terminal sends the car key information to the second terminal of the target vehicle user;
所述服务器接收第二终端发送的目标用车人的身份信息,并根据所述候选用车人的身份验证信息对所述目标用车人的身份信息进行验证;The server receives the identity information of the target vehicle user sent by the second terminal, and verifies the identity information of the target vehicle user according to the identity verification information of the candidate vehicle user;
如果验证通过,所述服务器将所述车辆标识对应的车辆的使用权授予给所述目标用车人。If the verification is passed, the server grants the target vehicle user the right to use the vehicle corresponding to the vehicle identification.
本申请实施例中,服务器获取车主输入的车辆标识和候选用车人的身份验证信息,生成车钥匙信息,该车钥匙信息包含候选用车人的身份验证信息,保留了车主对用车人的选择权;通过服务器接收第二终端发送的目标用车人的身份信息,并根据所述候选用车人的身份验证信息对所述目标用车人的身份信息进行验证,通过身份验证的方法实现车辆使用权的授予,不需要复杂的加密和验证程序,提高了授予过程的安全性和便捷性。In the embodiment of the present application, the server obtains the vehicle identification and the identity verification information of the candidate vehicle user input by the vehicle owner, and generates the vehicle key information. The right to choose; the identity information of the target vehicle user sent by the second terminal is received by the server, and the identity information of the target vehicle user is verified according to the identity verification information of the candidate vehicle user, which is realized by the method of identity verification. The granting of vehicle use rights does not require complex encryption and verification procedures, which improves the security and convenience of the granting process.
可选的,所述服务器根据所述创建数据创建车钥匙信息,包括:Optionally, the server creates vehicle key information according to the creation data, including:
所述服务器对所述创建数据进行加密,得到密文;The server encrypts the created data to obtain ciphertext;
所述服务器将所述密文添加到身份验证页面网址中,得到所述车钥匙信息;The server adds the ciphertext to the URL of the authentication page to obtain the vehicle key information;
所述服务器接收第二终端发送的目标用车人的身份信息,根据所述候选用车人的身份验证信息对所述目标用车人的身份信息进行验证,包括:The server receives the identity information of the target vehicle user sent by the second terminal, and verifies the identity information of the target vehicle user according to the identity verification information of the candidate vehicle user, including:
所述服务器接收所述第二终端发送的所述身份验证页面网址的请求信息,向所述第二终端返回所述身份验证页面;receiving, by the server, the request information of the URL of the identity verification page sent by the second terminal, and returning the identity verification page to the second terminal;
所述服务器接收所述第二终端从所述身份验证页面上提取的目标用车人的身份信息;receiving, by the server, the identity information of the target vehicle user extracted by the second terminal from the identity verification page;
所述服务器从所述身份验证页面网址中提取密文,并对所述密文进行解密得到所述候选用车人的身份验证信息;The server extracts the ciphertext from the URL of the identity verification page, and decrypts the ciphertext to obtain the identity verification information of the candidate vehicle user;
所述服务器根据所述候选用车人的身份验证信息对所述目标用车人的身份信息进行验证。The server verifies the identity information of the target vehicle user according to the identity verification information of the candidate vehicle user.
可选的,所述创建数据还包括:车钥匙信息的失效条件;Optionally, the creation data further includes: an invalidation condition of the vehicle key information;
在所述服务器解锁所述车辆标识对应的车辆之后,所述方法还包括:After the server unlocks the vehicle corresponding to the vehicle identifier, the method further includes:
如果满足失效条件,所述服务器向所述第二终端发送失效提示信息,和/或对所述车钥匙信息进行失效处理。If the invalidation condition is satisfied, the server sends invalidation prompt information to the second terminal, and/or performs invalidation processing on the vehicle key information.
上述申请中的一种可选实施方式,通过设置车钥匙信息的时效条件,以及若满足失效条件,所述服务器向所述第二终端发送失效提示信息,和/或对所述车钥匙信息进行失效处理,从而通过失效条件,灵活地约束车辆的使用权。In an optional implementation manner of the above application, by setting the aging condition of the car key information, and if the failure condition is satisfied, the server sends the invalidation prompt information to the second terminal, and/or performs processing on the car key information. Failure handling, so as to flexibly restrict the right to use the vehicle through failure conditions.
第四方面,本申请实施例还提供了一种基于车钥匙信息的车辆授权装置,包括:In a fourth aspect, an embodiment of the present application further provides a vehicle authorization device based on vehicle key information, including:
第一发送模块,用于获取车主输入的创建数据,并将所述创建数据发送至服务器,以供所述服务器根据所述创建数据创建车钥匙信息;其中,所述创建数据包括:车辆标识和候选用车人的身份验证信息;The first sending module is configured to obtain the creation data input by the vehicle owner, and send the created data to the server, so that the server can create car key information according to the created data; wherein, the created data includes: vehicle identification and The identity verification information of the candidate vehicle user;
接收模块,用于接收所述服务器发送的所述车钥匙信息;a receiving module, configured to receive the vehicle key information sent by the server;
第二发送模块,用于响应于所述车主将所述车钥匙信息发送至目标用车人的操作,将所述车钥匙信息发送至所述目标用车人的第二终端,以使所述目标用车人的身份信息被所述身份验证信息验证通过后,获得所述车辆标识对应的车辆的使用权。The second sending module is configured to send the car key information to the second terminal of the target vehicle user in response to the operation of the vehicle owner to send the vehicle key information to the target vehicle user, so that the After the identity information of the target vehicle user is verified by the identity verification information, the right to use the vehicle corresponding to the vehicle identification is obtained.
第五方面,本申请实施例还提供了一种基于车钥匙信息的车辆受权装置,包括:In a fifth aspect, an embodiment of the present application further provides a vehicle authorization device based on vehicle key information, including:
接收模块,用于接收第一终端发送的车钥匙信息,所述车钥匙信息是服务器根据创建数据创建的,所述创建数据包括:车辆标识和候选用车人的身份验证信息;a receiving module, configured to receive the car key information sent by the first terminal, the car key information is created by the server according to the creation data, and the creation data includes: the vehicle identification and the identity verification information of the candidate vehicle user;
发送模块,用于响应于目标用车人对所述车钥匙信息的触发操作,将所述目标用车人的身份信息发送至所述服务器,以供所述服务器根据所述候选用车人的身份验证信息对所述目标用车人的身份信息进行验证,并返回验证结果;The sending module is configured to send the identity information of the target vehicle user to the server in response to the triggering operation of the vehicle key information by the target vehicle user, so that the server can send the information of the target vehicle user to the server according to the information of the candidate vehicle user. The identity verification information verifies the identity information of the target vehicle user, and returns the verification result;
受权模块,用于如果验证通过,获得所述车辆标识对应的车辆的使用权。The authorization module is configured to obtain the right to use the vehicle corresponding to the vehicle identification if the verification is passed.
第六方面,本申请实施例还提供了一种车钥匙信息的处理装置,包括:In a sixth aspect, an embodiment of the present application further provides a device for processing vehicle key information, including:
第一接收模块,用于接收第一终端发送的创建数据,所述创建数据包括:车辆标识和候选用车人的身份验证信息;a first receiving module, configured to receive creation data sent by the first terminal, where the creation data includes: vehicle identification and identity verification information of candidate vehicle users;
创建模块,用于根据所述创建数据创建车钥匙信息;A creation module for creating car key information according to the creation data;
发送模块,用于将所述车钥匙信息发送至所述第一终端,以供所述第一终端将所述车钥匙信息发送至所述目标用车人的第二终端;a sending module, configured to send the car key information to the first terminal, so that the first terminal can send the car key information to the second terminal of the target vehicle user;
第二接收模块,用于接收第二终端发送的目标用车人的身份信息,并根据所述候选用车人的身份验证信息对所述目标用车人的身份信息进行验证;a second receiving module, configured to receive the identity information of the target vehicle user sent by the second terminal, and verify the identity information of the target vehicle user according to the identity verification information of the candidate vehicle user;
授权模块,用于如果验证通过,将所述车辆标识对应的车辆的使用权授予给所述目标用车人。The authorization module is used for granting the right to use the vehicle corresponding to the vehicle identification to the target vehicle user if the verification is passed.
第七方面,本申请实施例还提供了一种终端,包括:In a seventh aspect, an embodiment of the present application further provides a terminal, including:
至少一个处理器;以及at least one processor; and
与所述至少一个处理器通信连接的存储器;其中,a memory communicatively coupled to the at least one processor; wherein,
所述存储器存储有可被所述至少一个处理器执行的指令,所述指令被所述至少一个处理器执行,以使所述至少一个处理器能够执行如第一方面实施例所提供的一种基于车钥匙信息的车辆授权方法,或者如第二方面实施例所提供的一种基于车钥匙信息的车辆受权方法。The memory stores instructions executable by the at least one processor, the instructions being executed by the at least one processor to enable the at least one processor to perform a method as provided by an embodiment of the first aspect A vehicle authorization method based on vehicle key information, or a vehicle authorization method based on vehicle key information as provided in the embodiment of the second aspect.
第八方面,本申请实施例还提供了一种服务器,包括:In an eighth aspect, an embodiment of the present application further provides a server, including:
至少一个处理器;以及at least one processor; and
与所述至少一个处理器通信连接的存储器;其中,a memory communicatively coupled to the at least one processor; wherein,
所述存储器存储有可被所述至少一个处理器执行的指令,所述指令被所述至少一个处理器执行,以使所述至少一个处理器能够执行如第三方面实施例所提供的一种车钥匙信息的处理方法。The memory stores instructions executable by the at least one processor, the instructions being executed by the at least one processor to enable the at least one processor to execute the one provided by the third aspect embodiment The processing method of car key information.
第九方面,本申请实施例还提供了一种存储有计算机指令的非瞬时计算机可读存储介质,所述计算机指令用于使所述计算机执行如第一方面实施例所提供的一种基于车钥匙信息的车辆授权方法,或者如第二方面实施例所提供的一种基于车钥匙信息的车辆受权方法,或者如第三方面实施例所提供的一种车钥匙信息的处理方法。In a ninth aspect, embodiments of the present application further provide a non-transitory computer-readable storage medium storing computer instructions, where the computer instructions are used to cause the computer to execute the vehicle-based vehicle-based storage medium provided by the embodiments of the first aspect A vehicle authorization method for key information, or a vehicle authorization method based on vehicle key information as provided in the second aspect embodiment, or a vehicle key information processing method as provided in the third aspect embodiment.
上述可选方式所具有的其他效果将在下文中结合具体实施例加以说明。Other effects of the above-mentioned optional manners will be described below with reference to specific embodiments.
附图说明Description of drawings
附图用于更好地理解本方案,不构成对本申请的限定。其中:The accompanying drawings are used for better understanding of the present solution, and do not constitute a limitation to the present application. in:
图1a是本申请实施例提供的车辆授权场景的示意图;1a is a schematic diagram of a vehicle authorization scenario provided by an embodiment of the present application;
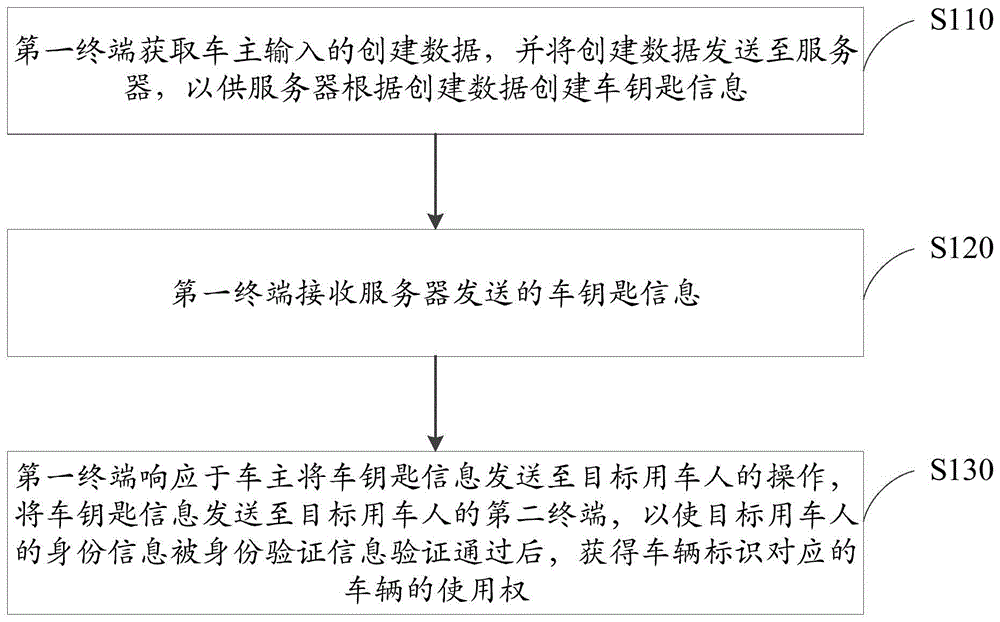
图1b是本申请实施例一中的一种基于车钥匙信息的车辆授权方法的流程图;Fig. 1b is a flowchart of a vehicle authorization method based on vehicle key information in Embodiment 1 of the present application;
图1c是本申请实施例一中的创建车钥匙页面的示意图;1c is a schematic diagram of creating a car key page in Embodiment 1 of the present application;
图1d是本申请实施例一中的创建数据输入页面的示意图;1d is a schematic diagram of creating a data input page in Embodiment 1 of the present application;
图1e是本申请实施例一中的创建成功页面的示意图;Fig. 1e is the schematic diagram of creating a successful page in the first embodiment of the present application;
图2a是本申请实施例二中的一种基于车钥匙信息的车辆授权方法的流程图;2a is a flowchart of a vehicle authorization method based on vehicle key information in Embodiment 2 of the present application;
图2b是本申请实施例二提供的社交应用程序的聊天窗口的示意图;2b is a schematic diagram of a chat window of a social application program provided in Embodiment 2 of the present application;
图3a是本申请实施例三中的一种基于车钥匙信息的车辆受权方法的流程图Fig. 3a is a flowchart of a vehicle authorization method based on vehicle key information in the third embodiment of the present application
图3b是本申请实施例三中的身份验证页面的示意图;3b is a schematic diagram of an identity verification page in Embodiment 3 of the present application;
图3c是本申请实施例三中的解锁页面的示意图;3c is a schematic diagram of an unlock page in Embodiment 3 of the present application;
图4是本本申请实施例四中的一种基于车钥匙信息的车辆受权方法的流程图4 is a flowchart of a vehicle authorization method based on vehicle key information in Embodiment 4 of the present application
图5是本申请实施例五中的一种车钥匙信息的处理方法的流程图;5 is a flowchart of a method for processing vehicle key information in Embodiment 5 of the present application;
图6是本申请实施例六中的一种基于车钥匙信息的车辆授权装置的结构图;6 is a structural diagram of a vehicle authorization device based on vehicle key information in Embodiment 6 of the present application;
图7是本申请实施例七中的一种基于车钥匙信息的车辆受权装置的结构图;7 is a structural diagram of a vehicle authorization device based on vehicle key information in Embodiment 7 of the present application;
图8是本申请实施例八中的一种车钥匙信息的处理装置的结构图;8 is a structural diagram of an apparatus for processing vehicle key information according to Embodiment 8 of the present application;
图9是用来实现本申请实施例的基于车钥匙信息的车辆授权方法或基于车钥匙信息的车辆受权方法的终端的框图。FIG. 9 is a block diagram of a terminal used to implement a vehicle authorization method based on vehicle key information or a vehicle authorization method based on vehicle key information according to an embodiment of the present application.
具体实施方式Detailed ways
以下结合附图对本申请的示范性实施例做出说明,其中包括本申请实施例的各种细节以助于理解,应当将它们认为仅仅是示范性的。因此,本领域普通技术人员应当认识到,可以对这里描述的实施例做出各种改变和修改,而不会背离本申请的范围和精神。同样,为了清楚和简明,以下的描述中省略了对公知功能和结构的描述。Exemplary embodiments of the present application are described below with reference to the accompanying drawings, which include various details of the embodiments of the present application to facilitate understanding, and should be considered as exemplary only. Accordingly, those of ordinary skill in the art will recognize that various changes and modifications of the embodiments described herein can be made without departing from the scope and spirit of the present application. Also, descriptions of well-known functions and constructions are omitted from the following description for clarity and conciseness.
图1a是本申请实施例提供的车辆授权场景的示意图。本申请实施例适用于车主、用车人通过各自的终端进行车辆使用权的授予的场景,为了便于描述和区分,将车主的终端称为第一终端,将用车人的终端称为第二终端。其中,第一终端和第二终端可以是智能手机、掌上电脑、手环等可通信的智能终端。车辆是可以支持远程控制的联网汽车。下面分别以第一终端、第二终端和服务器为执行主体,结合图1a详细描述本申请实施例提供的各个方法。FIG. 1a is a schematic diagram of a vehicle authorization scenario provided by an embodiment of the present application. The embodiments of the present application are applicable to the scenario where the vehicle owner and the vehicle user grant the right to use the vehicle through their respective terminals. For the convenience of description and distinction, the vehicle owner's terminal is called the first terminal, and the vehicle user's terminal is called the second terminal. terminal. Wherein, the first terminal and the second terminal may be intelligent terminals that can communicate with each other, such as a smart phone, a palmtop computer, and a wristband. A vehicle is a connected car that can support remote control. Hereinafter, the first terminal, the second terminal, and the server are respectively used as execution bodies, and each method provided by the embodiment of the present application is described in detail with reference to FIG. 1a.
实施例一Example 1
图1b是本申请实施例一中的一种基于车钥匙信息的车辆授权方法的流程图,本申请实施例适用于车主通过第一终端将车辆的使用权限授予给用车人的情况,该方法通过基于车钥匙信息的车辆授权的装置执行,该装置采用软件和/或硬件实现,并具体配置于具备一定数据运算能力的终端中。Fig. 1b is a flowchart of a vehicle authorization method based on car key information in the first embodiment of the present application. The embodiment of the present application is applicable to the situation where the vehicle owner grants the vehicle use authority to the vehicle user through the first terminal. Executed by a device for vehicle authorization based on vehicle key information, the device is implemented by software and/or hardware, and is specifically configured in a terminal with a certain data computing capability.
结合图1a和图1b,本实施例提供的方法包括:With reference to Fig. 1a and Fig. 1b, the method provided by this embodiment includes:
S110、第一终端获取车主输入的创建数据,并将创建数据发送至服务器,以供服务器根据创建数据创建车钥匙信息。S110. The first terminal acquires the creation data input by the vehicle owner, and sends the creation data to the server, so that the server creates the vehicle key information according to the creation data.
创建数据包括:车辆标识和候选用车人的身份验证信息。其中,车辆标识是待授权的车辆的唯一标识,如车架号、车牌号等。候选用车人是车主自主选择的用车人,例如是车主的家人、朋友等,数量为至少一个。身份验证信息是与候选用车人一一对应的唯一身份信息,如手机号、昵称或身份证号等。身份验证信息用于对用车人上传的身份信息进行一致性验证。Creation data includes: vehicle identification and identity verification information of candidate vehicle users. The vehicle identification is the unique identification of the vehicle to be authorized, such as the frame number, license plate number, and the like. The candidate vehicle user is the vehicle user selected by the vehicle owner, such as family members and friends of the vehicle owner, and the number is at least one. The identity verification information is the unique identity information corresponding to the candidate vehicle users one-to-one, such as mobile phone number, nickname or ID number, etc. The identity verification information is used to perform consistency verification on the identity information uploaded by the vehicle user.
可选的,创建数据还可以包括失效条件,如使用结束时间、使用地理范围、使用里程等。Optionally, the creation data may also include failure conditions, such as use end time, use geographic range, use mileage, and the like.
在一应用场景中,车主需要预先在服务器中进行注册,才能授权。具体的,第一终端安装有支持车辆授权功能的应用程序或H5页面,车主打开应用程序或H5页面后,应用程序或H5页面会显示用户注册的页面,该页面包括车主的身份信息输入框和车辆标识输入框。车主在对应的输入框中输入身份信息和车辆标识后,第一终端将身份信息和车辆标识发送至服务器。服务器对车主的身份信息和车辆标识进行绑定,完成注册。可以理解的是,注册操作只执行一次即可。In an application scenario, the car owner needs to register in the server in advance before authorization. Specifically, the first terminal is installed with an application or H5 page that supports the vehicle authorization function. After the owner opens the application or H5 page, the application or H5 page will display a user registration page, which includes the vehicle owner's identity information input box and Vehicle identification input box. After the vehicle owner inputs the identity information and the vehicle identifier in the corresponding input box, the first terminal sends the identity information and the vehicle identifier to the server. The server binds the owner's identity information and the vehicle identification to complete the registration. Understandably, the registration operation is only performed once.
在车主有车辆授权需求时,打开应用程序或H5页面会显示创建车钥匙页面,包括“开始创建车钥匙信息”控件和车钥匙图标,如图1c所示。应用程序或H5页面响应于车主对“开始创建车钥匙信息”控件的触发操作,展示创建数据输入页面,包括创建数据输入框和“提交”控件,如图1d所示。图1d中,创建数据包括候选用车人的手机号和使用结束时间。应用程序或H5页面响应于车主对“提交”控件的触发操作,将候选用车人的手机号、使用结束时间以及车主的身份信息发送至服务器。When the car owner has a vehicle authorization requirement, opening the application or the H5 page will display the create car key page, including the "start creating car key information" control and the car key icon, as shown in Figure 1c. The application or H5 page displays the creation data input page in response to the car owner's triggering operation on the "start to create car key information" control, including the creation of the data input box and the "submit" control, as shown in Figure 1d. In Figure 1d, the creation data includes the mobile phone number of the candidate car user and the end time of the use. The application or H5 page sends the mobile phone number of the candidate car user, the end time of use, and the identity information of the car owner to the server in response to the car owner's triggering operation on the "submit" control.
服务器根据预先注册的车主的身份信息和车辆标识,以及接收到的前述信息,得到最终的创建数据:车主的身份信息对应的车辆标识和候选用车人的身份验证信息。然后,服务器根据创建数据创建车钥匙信息,并将车钥匙信息发送至第一终端。The server obtains the final creation data according to the pre-registered vehicle owner's identity information and vehicle identification, as well as the received aforementioned information: the vehicle identification corresponding to the vehicle owner's identity information and the identity verification information of the candidate vehicle user. Then, the server creates vehicle key information according to the creation data, and sends the vehicle key information to the first terminal.
S120、第一终端接收服务器发送的车钥匙信息。S120. The first terminal receives the vehicle key information sent by the server.
第一终端接收到车钥匙信息后,应用程序或H5页面显示创建成功页面,包括创建成功图标和“发送”控件。如图1e所示。至此,车钥匙信息创建完成。After the first terminal receives the car key information, the application or H5 page displays the creation success page, including the creation success icon and the "send" control. As shown in Figure 1e. At this point, the creation of the car key information is complete.
S130、第一终端响应于车主将车钥匙信息发送至目标用车人的操作,将车钥匙信息发送至目标用车人的第二终端,以使目标用车人的身份信息被身份验证信息验证通过后,获得车辆标识对应的车辆的使用权。S130. In response to the operation of the vehicle owner sending the car key information to the target vehicle user, the first terminal sends the vehicle key information to the second terminal of the target vehicle user, so that the identity information of the target vehicle user is verified by the identity verification information After passing, the right to use the vehicle corresponding to the vehicle identification is obtained.
车主将车钥匙信息发送至目标用车人的操作包括用户对“发送”控件的触发操作和对用车人的选择操作。为了方便描述和区分,车主将车钥匙信息发送至的用车人称为目标用车人,其应是候选用车人中的一个。The operation of the car owner to send the car key information to the target car user includes the user's triggering operation of the "send" control and the selection operation of the car user. For the convenience of description and distinction, the vehicle user to which the vehicle owner sends the car key information is called the target vehicle user, which should be one of the candidate vehicle users.
值得说明的是,第一终端响应于车主将车钥匙信息发送至目标用车人的操作,将车钥匙信息采用点对点的方式发送至第二终端,也可以通过服务器转发给第二终端。如果通过服务器转发,服务器不会对车钥匙信息进行任何验证方面的处理。It is worth noting that the first terminal sends the car key information to the second terminal in a point-to-point manner in response to the operation of the car owner to send the car key information to the target vehicle user, and can also be forwarded to the second terminal through the server. If it is forwarded through the server, the server will not perform any verification processing on the car key information.
第二终端也安装有支持车辆授权功能的应用程序或H5页面。在第二终端接收到第一终端发送的车钥匙信息后,应用程序或H5页面会显示车钥匙信息对应的图标。目标用车人触发该图表,也就是触发车钥匙信息。第二终端响应于目标用车人对车钥匙信息的触发操作,将目标用车人的身份信息发送至服务器。目标用车人的身份信息可以是手机号、昵称或身份证号等。The second terminal is also installed with an application or H5 page that supports the vehicle authorization function. After the second terminal receives the car key information sent by the first terminal, the application or H5 page will display an icon corresponding to the car key information. The target user triggers the chart, that is, triggers the car key information. The second terminal sends the identity information of the target vehicle user to the server in response to the target vehicle user's triggering operation on the vehicle key information. The identity information of the target vehicle user can be a mobile phone number, a nickname or an ID number, etc.
服务器根据候选用车人的身份验证信息对目标用车人的身份信息进行验证。并返回验证结果。具体的,如果目标用车人的身份信息与候选用车人的身份验证信息之一一致,则验证通过;如果目标用车人的身份信息与任一候选用车人的身份验证信息均不一致,则验证不通过。The server verifies the identity information of the target vehicle user according to the identity verification information of the candidate vehicle user. and return the verification result. Specifically, if the identity information of the target vehicle user is consistent with one of the identity verification information of the candidate vehicle user, the verification is passed; if the identity information of the target vehicle user is inconsistent with the identity verification information of any candidate vehicle user , the verification fails.
如果验证不通过,向第二终端发送验证不通过的消息。如果验证通过,第二终端获得车辆标识对应的车辆的使用权;具体的,如果验证通过,服务器远程解锁车辆标识对应的车辆,如解锁车辆的车门。If the verification fails, a verification failure message is sent to the second terminal. If the verification is passed, the second terminal obtains the right to use the vehicle corresponding to the vehicle identification; specifically, if the verification is passed, the server remotely unlocks the vehicle corresponding to the vehicle identification, such as unlocking the door of the vehicle.
本申请实施例中,第一终端获取车主输入的车辆标识和候选用车人的身份验证信息,并通过服务器生成车钥匙信息,该车钥匙信息包含候选用车人的身份验证信息,保留了车主对用车人的选择权;通过第一终端响应于车主将车钥匙信息发送至目标用车人的操作,将车钥匙信息发送至目标用车人的第二终端,车主可自主将车钥匙信息发送至选定的用车人,在目标用车人的身份信息被身份验证信息验证通过后,获得车辆标识对应的车辆的使用权,可见,本实施例通过车主向用车人发送车钥匙信息,并结合身份验证的方法实现车辆使用权的授予,不需要复杂的加密和验证程序,提高了授予过程的安全性和便捷性。In the embodiment of the present application, the first terminal obtains the vehicle identification and the identity verification information of the candidate vehicle user input by the vehicle owner, and generates the vehicle key information through the server. The vehicle key information includes the identity verification information of the candidate vehicle user, and retains the vehicle owner The right to choose the car user; the first terminal sends the car key information to the target car user's second terminal in response to the car owner's operation of sending the car key information to the target car user, and the car owner can autonomously send the car key information. It is sent to the selected vehicle user. After the identity information of the target vehicle user is verified by the identity verification information, the right to use the vehicle corresponding to the vehicle identification is obtained. It can be seen that in this embodiment, the vehicle owner sends the vehicle key information to the vehicle user. , and combined with the method of authentication to realize the granting of vehicle use rights, which does not require complex encryption and verification procedures, and improves the security and convenience of the granting process.
实施例二Embodiment 2
图2a是本申请实施例二中的一种基于车钥匙信息的车辆授权方法的流程图,本申请实施例在上述各实施例的技术方案的基础上进行优化。FIG. 2 a is a flowchart of a vehicle authorization method based on vehicle key information in Embodiment 2 of the present application. The embodiments of the present application are optimized on the basis of the technical solutions of the foregoing embodiments.
可选的,将操作“第一终端响应于车主将车钥匙信息发送至目标用车人的操作,将车钥匙信息发送至目标用车人的第二终端”细化为“第一终端响应于车主通过社交应用程序将车钥匙信息分享至车主与目标用车人的聊天窗口中的操作,将车钥匙信息发送至目标用车人的第二终端”,以提高授权的便捷性。Optionally, the operation "the first terminal sends the car key information to the target vehicle user's second terminal in response to the operation of the owner to send the car key information to the target vehicle user" is refined into "the first terminal responds to the The operation of the car owner sharing the car key information to the chat window between the car owner and the target car user through the social application, and sending the car key information to the second terminal of the target car user” to improve the convenience of authorization.
如图2a所示的一种基于车钥匙信息的车辆授权方法,包括:As shown in Figure 2a, a vehicle authorization method based on vehicle key information includes:
S210、第一终端获取车主输入的创建数据,并将创建数据发送至服务器,以供服务器根据创建数据创建车钥匙信息。S210: The first terminal acquires the creation data input by the vehicle owner, and sends the creation data to the server, so that the server creates the vehicle key information according to the creation data.
S220、第一终端接收服务器发送的车钥匙信息。S220. The first terminal receives the vehicle key information sent by the server.
S230、第一终端响应于车主通过社交应用程序将车钥匙信息分享至车主与目标用车人的聊天窗口中的操作,将车钥匙信息发送至目标用车人的第二终端,以使目标用车人的身份信息被身份验证信息验证通过后,获得车辆标识对应的车辆的使用权。S230. In response to the operation of the car owner sharing the car key information to the chat window between the car owner and the target car user through the social application program, the first terminal sends the car key information to the second terminal of the target car user, so that the target user After the identity information of the vehicle occupant is verified by the identity verification information, the right to use the vehicle corresponding to the vehicle identification is obtained.
第一终端和第二终端均安装有社交应用程序,并可以通过社交应用程序提供的聊天窗口向对方发送消息,例如文字、图片、短视频、网址等。Both the first terminal and the second terminal are installed with a social networking application, and can send messages to each other through a chat window provided by the social networking application, such as text, pictures, short videos, website addresses, and the like.
图2b是本申请实施例二提供的社交应用程序的聊天窗口的示意图。在一应用场景中,响应于车主对图1e中“发送”控件的触发操作,跳转到社交应用程序的分享页面,如图2b的上部分所示,分享页面包括“发送给朋友”选项。社交应用程序响应于车主对“发送给朋友”选项的触发操作,将车钥匙信息分享至车主与目标用车人的聊天窗口中,如图2b的下部分所示。同时,目标用车人通过与车主的聊天窗口接收到车钥匙信息。FIG. 2b is a schematic diagram of a chat window of a social application program provided in Embodiment 2 of the present application. In an application scenario, in response to the vehicle owner triggering the "send" control in Fig. 1e, jump to the sharing page of the social application, as shown in the upper part of Fig. 2b, the sharing page includes the "send to friend" option. In response to the car owner's triggering of the "send to a friend" option, the social application shares the car key information to the chat window between the car owner and the target car user, as shown in the lower part of Figure 2b. At the same time, the target car user receives the car key information through the chat window with the car owner.
本实施例中,车主分享车钥匙信息的平台是社交应用程序,具体可以将车钥匙信息分享至聊天窗口中,从而通过在聊天窗口中分享的操作,实现车钥匙信息的发送,操作灵活、便捷,提高用户体验。In this embodiment, the platform for the car owner to share the car key information is a social application program. Specifically, the car key information can be shared in the chat window, so that the transmission of the car key information can be realized through the operation of sharing in the chat window, and the operation is flexible and convenient. , to improve the user experience.
实施例三Embodiment 3
图3a是本申请实施例三中的一种基于车钥匙信息的车辆受权方法的流程图,本申请实施例适用于目标用车人通过第二终端获取车辆的使用权限的情况,该方法通过基于车钥匙信息的车辆受权的装置执行,该装置采用软件和/或硬件实现,并具体配置于具备一定数据运算能力的终端中。Fig. 3a is a flowchart of a vehicle authorization method based on vehicle key information in the third embodiment of the present application. The embodiment of the present application is applicable to the situation where the target vehicle user obtains the use authority of the vehicle through the second terminal. The vehicle key information is executed by a vehicle authorized device, the device is implemented by software and/or hardware, and is specifically configured in a terminal with a certain data computing capability.
如图3a所示的一种基于车钥匙信息的车辆受权方法,包括:As shown in Figure 3a, a vehicle authorization method based on vehicle key information includes:
S310、第二终端接收第一终端发送的车钥匙信息。S310. The second terminal receives the car key information sent by the first terminal.
车钥匙信息是服务器根据创建数据创建的,创建数据包括:车辆标识和候选用车人的身份验证信息。The vehicle key information is created by the server according to the creation data, and the creation data includes the vehicle identification and the identity verification information of the candidate vehicle user.
可选的,服务器接收到第一终端发送的创建数据后,对创建数据进行加密,得到密文;然后,将密文添加到身份验证页面网址中得到车钥匙信息。Optionally, after receiving the creation data sent by the first terminal, the server encrypts the creation data to obtain ciphertext; then, the ciphertext is added to the URL of the authentication page to obtain the car key information.
身份验证页面网址的格式如:https://smartkey.host.com/{$token$}。其中,https://smartkey.host.com是身份验证页面网址,{$token$}是采用加密算法对创建数据进行加密,得到的密文。该密文具有不可伪造和不可枚举性,每一个车钥匙信息都是唯一且不重复的。The format of the authentication page URL is: https://smartkey.host.com/{$token$}. Among them, https://smartkey.host.com is the URL of the authentication page, and {$token$} is the ciphertext obtained by encrypting the created data with an encryption algorithm. The ciphertext is unforgeable and non-enumerable, and each car key information is unique and non-repetitive.
该车钥匙信息从服务器发送到第一终端后,再由第一终端发送至第二终端,则第二终端接收到车钥匙信息。After the car key information is sent from the server to the first terminal, and then sent by the first terminal to the second terminal, the second terminal receives the car key information.
S320、第二终端响应于目标用车人对车钥匙信息的触发操作,将目标用车人的身份信息发送至服务器,以供服务器根据候选用车人的身份验证信息对目标用车人的身份信息进行验证,并返回验证结果。S320: In response to the target vehicle user's triggering operation on the car key information, the second terminal sends the target vehicle user's identity information to the server, so that the server can verify the target vehicle user's identity according to the candidate vehicle user's identity verification information The information is verified and the verification result is returned.
第二终端响应于目标用车人对车钥匙信息的触发操作,向服务器发送身份验证页面网址的请求信息。服务器一方面向第二终端返回身份验证页面,另一方面从身份验证页面网址中提取密文,对密文进行解密得到候选用车人的身份验证信息。可以理解的是,密文作为身份验证页面网址的参数存在,且位于网址的最后,不影响服务器返回身份验证页面。其中,服务器采用与前述加密方法对应的解密方法对密文进行解密,得到创建数据。In response to the target vehicle user's triggering operation on the car key information, the second terminal sends the request information of the URL of the identity verification page to the server. On the one hand, the server returns the identity verification page to the second terminal, and on the other hand, extracts the ciphertext from the URL of the identity verification page, and decrypts the ciphertext to obtain the identity verification information of the candidate vehicle user. It is understandable that the ciphertext exists as a parameter of the authentication page URL and is located at the end of the URL, which does not affect the server returning to the authentication page. The server decrypts the ciphertext by using a decryption method corresponding to the aforementioned encryption method to obtain the created data.
第二终端展示身份验证页面,包括身份信息的输入框和“提交”控件,如图3b所示。目标用车人可以在输入框中输入自己的身份信息。第二终端响应于目标用车人在身份验证页面上的输入操作,从身份验证页面上提取目标用车人的身份信息并发送至服务器。The second terminal displays an authentication page, including an input box for identity information and a "submit" control, as shown in Figure 3b. The target user can enter their own identity information in the input box. In response to the input operation of the target vehicle user on the identity verification page, the second terminal extracts the identity information of the target vehicle user from the identity verification page and sends it to the server.
服务器接收到目标用车人的身份信息后,根据候选用车人的身份验证信息对目标用车人的身份信息进行验证,并向第二终端返回验证结果。After receiving the identity information of the target vehicle user, the server verifies the identity information of the target vehicle user according to the identity verification information of the candidate vehicle user, and returns the verification result to the second terminal.
S330、如果验证通过,第二终端获得车辆标识对应的车辆的使用权。S330. If the verification is passed, the second terminal obtains the right to use the vehicle corresponding to the vehicle identification.
可选的,如果验证通过,第二终端展示解锁页面,包括车辆的图标、车辆的锁定状态说明和解锁面板,如图3c所示。目标用车人可在解锁面板上进行解锁操作,如向右滑动。第二终端响应于目标用车人在解锁页面上的解锁操作,向服务器发送解锁请求。服务器根据解锁请求,解锁车辆标识对应的车辆,如解锁车辆的车门。本实施例中,目标用车人通过在解锁页面执行解锁操作,就可以通过服务器解锁车辆,不需要第二终端与车辆进行直接通信,简化了解锁流程,提高了解锁操作的便捷性。Optionally, if the verification is passed, the second terminal displays the unlocking page, including the icon of the vehicle, the description of the locked state of the vehicle, and the unlocking panel, as shown in FIG. 3c . The target user can perform an unlocking operation on the unlocking panel, such as swiping right. The second terminal sends an unlocking request to the server in response to the target vehicle user's unlocking operation on the unlocking page. According to the unlocking request, the server unlocks the vehicle corresponding to the vehicle identification, such as unlocking the door of the vehicle. In this embodiment, the target vehicle user can unlock the vehicle through the server by performing the unlocking operation on the unlocking page, and does not require the second terminal to communicate directly with the vehicle, which simplifies the unlocking process and improves the convenience of the unlocking operation.
本申请实施例中,第二终端接收车钥匙信息后,响应于目标用车人对车钥匙信息的触发操作,通过服务器进行身份信息的验证,如果身份信息验证通过,则获得车辆的使用权。可见,本申请实施例中目标用车人只需要触发车钥匙信息即可进行验证并受权,操作方式简单;而且通过身份验证的方式也能保证安全性,避免车钥匙信息别其他人盗用。In the embodiment of the present application, after receiving the vehicle key information, the second terminal verifies the identity information through the server in response to the triggering operation of the vehicle key information by the target vehicle user, and obtains the right to use the vehicle if the identity information verification passes. It can be seen that in the embodiment of the present application, the target vehicle user only needs to trigger the vehicle key information to verify and authorize, and the operation method is simple; and the identity verification method can also ensure security and prevent other people from embezzling the vehicle key information.
进一步的,车钥匙信息实质是身份验证页面网址,通过触发车钥匙信息,在第二终端展示身份验证页面,以提取目标用车人的身份信息;同时,服务器从身份验证页面网址中解密出身份验证信息,以根据身份验证信息对目标用车人的身份信息进行验证。本申请实施例提供了车钥匙信息的具体内容,以及采用车钥匙信息进行身份验证的流程,从而通过触发车钥匙信息,展示身份验证信息,巧妙、便捷地上传身份信息,同时,服务器可以直接从身份验证页面网址中获取到身份验证信息,流程简单,不需要复杂的验证程序;通过对创建数据进行加密得到密文,避免创建数据被盗用,保证了一定的安全性。Further, the car key information is essentially the URL of the identity verification page. By triggering the car key information, the identity verification page is displayed on the second terminal to extract the identity information of the target vehicle user; at the same time, the server decrypts the identity from the URL of the identity verification page. Verification information, so as to verify the identity information of the target vehicle user according to the identity verification information. The embodiment of the present application provides the specific content of the car key information and the process of using the car key information for identity verification, so that the identity verification information can be displayed by triggering the car key information, and the identity information can be uploaded smartly and conveniently. The authentication information is obtained from the URL of the authentication page. The process is simple and does not require complex authentication procedures; the ciphertext is obtained by encrypting the created data, which prevents the creation of data from being stolen and ensures a certain degree of security.
实施例四Embodiment 4
图4是本本申请实施例四中的一种基于车钥匙信息的车辆受权方法的流程图,本申请实施例在上述各实施例的技术方案的基础上进行优化。FIG. 4 is a flowchart of a vehicle authorization method based on vehicle key information in Embodiment 4 of the present application. The embodiments of the present application are optimized on the basis of the technical solutions of the foregoing embodiments.
可选的,将操作“如果验证通过,第二终端获得车辆标识对应的车辆的使用权”细化为“如果验证通过,第二终端接收服务器向目标用车人的终端发送的授权验证码;第二终端将目标用车人输入的验证码发送至服务器,以供服务器将验证码与授权验证码比对,如果一致,将车辆标识对应的车辆的使用权授予给目标用车人”,以提高授权过程的安全性。Optionally, the operation "if the verification is passed, the second terminal obtains the right to use the vehicle corresponding to the vehicle identification" is refined into "if the verification is passed, the second terminal receives the authorization verification code sent by the server to the terminal of the target vehicle user; The second terminal sends the verification code input by the target vehicle user to the server, so that the server can compare the verification code with the authorization verification code, and if they are consistent, grant the right to use the vehicle corresponding to the vehicle identification to the target vehicle user.” Improve the security of the authorization process.
如图4所示的基于车钥匙信息的车辆受权方法,包括:As shown in Figure 4, the vehicle authorization method based on vehicle key information includes:
S410、第二终端接收第一终端发送的车钥匙信息。S410. The second terminal receives the vehicle key information sent by the first terminal.
车钥匙信息是服务器根据创建数据创建的,创建数据包括:车辆标识和候选用车人的身份验证信息。The vehicle key information is created by the server according to the creation data, and the creation data includes the vehicle identification and the identity verification information of the candidate vehicle user.
S420、第二终端响应于目标用车人对车钥匙信息的触发操作,将目标用车人的身份信息发送至服务器,以供服务器根据候选用车人的身份验证信息对目标用车人的身份信息进行验证,并返回验证结果。S420: In response to the target vehicle user's triggering operation on the car key information, the second terminal sends the target vehicle user's identity information to the server, so that the server can verify the target vehicle user's identity according to the candidate vehicle user's identity verification information The information is verified and the verification result is returned.
S430、如果验证通过,第二终端接收服务器向目标用车人的终端发送的授权验证码。S430. If the verification is passed, the second terminal receives the authorization verification code sent by the server to the terminal of the target vehicle user.
S440、第二终端将目标用车人输入的验证码发送至服务器,以供服务器将验证码与授权验证码比对,如果一致,将车辆标识对应的车辆的使用权授予给目标用车人。S440: The second terminal sends the verification code input by the target vehicle user to the server, so that the server can compare the verification code with the authorization verification code, and if they are consistent, grant the target vehicle user the right to use the vehicle corresponding to the vehicle identification.
考虑到车钥匙信息和用车人的身份信息如果均被其它人获取,其它人可通过所持终端窃取车辆使用权。为了避免出现这种情况,在身份验证通过后,通过授权验证码对发送身份信息的终端是否属于目标用车人进行验证。Considering that if both the car key information and the identity information of the user are obtained by others, others can steal the right to use the vehicle through the terminal they hold. In order to avoid such a situation, after the identity verification is passed, the authorization verification code is used to verify whether the terminal sending the identity information belongs to the target vehicle user.
具体的,如图3b所示,身份验证页面还包括验证码输入框。如果验证通过,服务器会向目标用车人的终端发送授权验证码。例如,目标用车人的身份信息是手机号,则服务器会向该手机号所属的终端发送授权验证码。Specifically, as shown in Figure 3b, the identity verification page further includes a verification code input box. If the verification is passed, the server will send the authorization verification code to the terminal of the target user. For example, if the identity information of the target user is a mobile phone number, the server will send an authorization verification code to the terminal to which the mobile phone number belongs.
如果发送身份信息的终端属于目标用车人,则会接收到服务器发送的授权验证码,则可以指导目标用车人输入一致的验证码;如果发送信息的终端不属于目标用车人,而是其它人,则发送信息的终端不会接收到服务器发送的授权验证码,其他人也不会输入与授权验证码一致的验证码,从而避免车辆使用权被其它人窃取。If the terminal sending the identity information belongs to the target user, it will receive the authorization verification code sent by the server and instruct the target user to input the same verification code; if the terminal sending the information does not belong to the target user, but For other people, the terminal sending the information will not receive the authorization verification code sent by the server, and other people will not input the verification code consistent with the authorization verification code, so as to prevent the vehicle use right from being stolen by others.
服务器接收到验证码后,将验证码与授权验证码比对。如果二者一致,将车辆标识对应的车辆的使用权授予给目标用车人;如果二者不一致,向第二终端发送验证不通过的消息。After the server receives the verification code, it compares the verification code with the authorization verification code. If the two are consistent, the right to use the vehicle corresponding to the vehicle identification is granted to the target vehicle user; if the two are inconsistent, a verification failure message is sent to the second terminal.
实施例五Embodiment 5
图5是本申请实施例五中的一种车钥匙信息的处理方法的流程图,本申请实施例适用于服务器根据车主的要求将车辆的使用权限授予给用车人的情况,该方法通过车钥匙信息的处理的装置执行,该装置采用软件和/或硬件实现,并具体配置于具备一定数据运算能力的服务器中。5 is a flowchart of a method for processing car key information in Embodiment 5 of the present application. The embodiment of the present application is applicable to the situation where the server grants the vehicle use authority to the vehicle user according to the requirements of the vehicle owner. The device for processing key information is implemented, and the device is implemented by software and/or hardware, and is specifically configured in a server with a certain data computing capability.
如图5所示的车钥匙信息的处理方法,包括:The processing method of the car key information as shown in Figure 5 includes:
S510、服务器接收第一终端发送的创建数据,创建数据包括:车辆标识和候选用车人的身份验证信息。S510. The server receives the creation data sent by the first terminal, where the creation data includes the vehicle identification and the identity verification information of the candidate vehicle user.
可选的,创建数据还包括:车钥匙信息的失效条件,如使用结束时间、使用地理范围、使用里程等。Optionally, the creation data further includes: invalidation conditions of the vehicle key information, such as the end time of use, the geographic range of use, and the mileage of use.
S520、服务器根据创建数据创建车钥匙信息。S520. The server creates vehicle key information according to the creation data.
S530、服务器将车钥匙信息发送至第一终端,以供第一终端将车钥匙信息发送至目标用车人的第二终端。S530: The server sends the car key information to the first terminal, so that the first terminal sends the car key information to the second terminal of the target vehicle user.
S540、服务器接收第二终端发送的目标用车人的身份信息,并根据候选用车人的身份验证信息对目标用车人的身份信息进行验证。S540. The server receives the identity information of the target vehicle user sent by the second terminal, and verifies the identity information of the target vehicle user according to the identity verification information of the candidate vehicle user.
S550、如果验证通过,服务器将车辆标识对应的车辆的使用权授予给目标用车人。S550. If the verification is passed, the server grants the right to use the vehicle corresponding to the vehicle identification to the target vehicle user.
可选的,在S550之后,还包括:如果满足失效条件,服务器向第二终端发送失效提示信息,和/或对车钥匙信息进行失效处理。Optionally, after S550, the method further includes: if the failure condition is satisfied, the server sends failure prompt information to the second terminal, and/or performs invalidation processing on the vehicle key information.
相应的,如果当前时间到达使用结束信息、车辆当前位置超过使用地理范围、车辆行驶路线长度超过使用里程,服务器判定车钥匙信息满足失效条件。其中,车辆当前位置和行驶路线长度可从车辆的定位系统中获取。服务器可对内部存储的车钥匙信息打上失效标签,当下次接收到第二终端发送的身份验证页面网址(即车钥匙信息)的请求信息时,如果检测到内部存储的同一车钥匙信息具有失效标签,则返回失效提示信息,并锁定该车辆。Correspondingly, if the current time reaches the end of use information, the current position of the vehicle exceeds the geographic range of use, and the length of the vehicle's travel route exceeds the mileage used, the server determines that the vehicle key information meets the invalidation condition. Wherein, the current position of the vehicle and the length of the travel route can be obtained from the positioning system of the vehicle. The server can label the internally stored car key information with an invalid label. When it receives the request information from the URL of the identity verification page (that is, the car key information) sent by the second terminal next time, if it detects that the same car key information stored internally has an invalid label , it returns the failure prompt message and locks the vehicle.
本实施例中,通过设置车钥匙信息的时效条件,以及若满足失效条件,服务器向第二终端发送失效提示信息,和/或对车钥匙信息进行失效处理,从而通过失效条件,灵活地约束车辆的使用权。In this embodiment, by setting the aging condition of the car key information, and if the failure condition is satisfied, the server sends the invalidation prompt information to the second terminal, and/or performs the invalidation processing on the car key information, so that the vehicle can be flexibly restricted by the invalidation condition. the right to use.
实施例六Embodiment 6
图6是本申请实施例六中的一种基于车钥匙信息的车辆授权装置的结构图,本申请实施例适用于车主通过第一终端将车辆的使用权限授予给用车人的情况,该装置采用软件和/或硬件实现,并具体配置于具备一定数据运算能力的终端中。FIG. 6 is a structural diagram of a vehicle authorization device based on vehicle key information in Embodiment 6 of the present application. The embodiment of the present application is applicable to the case where the vehicle owner grants the vehicle use authority to the vehicle user through the first terminal. It is implemented in software and/or hardware, and is specifically configured in a terminal with certain data computing capabilities.
如图6所示的一种基于车钥匙信息的车辆授权装置600,包括:第一发送模块601、接收模块602和第二发送模块603。As shown in FIG. 6 , a
第一发送模块601,用于获取车主输入的创建数据,并将创建数据发送至服务器,以供服务器根据创建数据创建车钥匙信息;其中,创建数据包括:车辆标识和候选用车人的身份验证信息;The
接收模块602,用于接收服务器发送的车钥匙信息;A receiving
第二发送模块603,用于响应于车主将车钥匙信息发送至目标用车人的操作,将车钥匙信息发送至目标用车人的第二终端,以使目标用车人的身份信息被身份验证信息验证通过后,获得车辆标识对应的车辆的使用权。The
本申请实施例中,第一终端获取车主输入的车辆标识和候选用车人的身份验证信息,并通过服务器生成车钥匙信息,该车钥匙信息包含候选用车人的身份验证信息,保留了车主对用车人的选择权;通过第一终端响应于车主将车钥匙信息发送至目标用车人的操作,将车钥匙信息发送至目标用车人的第二终端,车主可自主将车钥匙信息发送至选定的用车人,在目标用车人的身份信息被身份验证信息验证通过后,获得车辆标识对应的车辆的使用权,可见,本实施例通过车主向用车人发送车钥匙信息,并结合身份验证的方法实现车辆使用权的授予,不需要复杂的加密和验证程序,提高了授予过程的安全性和便捷性。In the embodiment of the present application, the first terminal obtains the vehicle identification and the identity verification information of the candidate vehicle user input by the vehicle owner, and generates the vehicle key information through the server. The vehicle key information includes the identity verification information of the candidate vehicle user, and retains the vehicle owner The right to choose the car user; the first terminal sends the car key information to the target car user's second terminal in response to the car owner's operation of sending the car key information to the target car user, and the car owner can autonomously send the car key information. It is sent to the selected vehicle user. After the identity information of the target vehicle user is verified by the identity verification information, the right to use the vehicle corresponding to the vehicle identification is obtained. It can be seen that in this embodiment, the vehicle owner sends the vehicle key information to the vehicle user. , and combined with the method of authentication to realize the granting of vehicle use rights, which does not require complex encryption and verification procedures, and improves the security and convenience of the granting process.
进一步的,第二发送模块603具体用于:响应于车主通过社交应用程序将车钥匙信息分享至车主与目标用车人的聊天窗口中的操作,将车钥匙信息发送至目标用车人的第二终端。Further, the
上述基于车钥匙信息的车辆授权装置可执行本申请任意实施例所提供的基于车钥匙信息的车辆授权方法,具备执行基于车钥匙信息的车辆授权方法相应的功能模块和有益效果。The above vehicle authorization device based on vehicle key information can execute the vehicle authorization method based on vehicle key information provided by any embodiment of the present application, and has functional modules and beneficial effects corresponding to executing the vehicle authorization method based on vehicle key information.
实施例七Embodiment 7
图7是本申请实施例七中的一种基于车钥匙信息的车辆受权装置的结构图,本申请实施例适用于目标用车人通过第二终端获取车辆的使用权限的情况,该装置采用软件和/或硬件实现,并具体配置于具备一定数据运算能力的终端中。FIG. 7 is a structural diagram of a vehicle authorization device based on vehicle key information in the seventh embodiment of the present application. The embodiment of the present application is applicable to the situation where the target vehicle user obtains the vehicle use authority through the second terminal, and the device adopts software And/or hardware implementation, and is specifically configured in a terminal with certain data computing capabilities.
如图7所示的一种基于车钥匙信息的车辆受权装置700,包括:接收模块701、发送模块702和受权模块703。As shown in FIG. 7 , a
接收模块701,用于接收第一终端发送的车钥匙信息,车钥匙信息是服务器根据创建数据创建的,创建数据包括:车辆标识和候选用车人的身份验证信息;The receiving
发送模块702,用于响应于目标用车人对车钥匙信息的触发操作,将目标用车人的身份信息发送至服务器,以供服务器根据候选用车人的身份验证信息对目标用车人的身份信息进行验证,并返回验证结果;The sending
受权模块703,用于如果验证通过,获得车辆标识对应的车辆的使用权。The
本申请实施例中,第二终端接收车钥匙信息后,响应于目标用车人对车钥匙信息的触发操作,通过服务器进行身份信息的验证,如果身份信息验证通过,则获得车辆的使用权。可见,本申请实施例中目标用车人只需要触发车钥匙信息即可进行验证并受权,操作方式简单;而且通过身份验证的方式也能保证安全性,避免车钥匙信息别其他人盗用。In the embodiment of the present application, after receiving the vehicle key information, the second terminal verifies the identity information through the server in response to the triggering operation of the vehicle key information by the target vehicle user, and obtains the right to use the vehicle if the identity information verification passes. It can be seen that in the embodiment of the present application, the target vehicle user only needs to trigger the vehicle key information to verify and authorize, and the operation method is simple; and the identity verification method can also ensure security and prevent other people from embezzling the vehicle key information.
进一步的,车钥匙信息是服务器对创建数据进行加密得到密文,并将密文添加到身份验证页面网址中得到的;发送模块702具体用于:响应于目标用车人对车钥匙信息的触发操作,向服务器发送身份验证页面网址的请求信息,以供服务器向第二终端返回身份验证页面,并从身份验证页面网址中提取密文,对密文进行解密得到候选用车人的身份验证信息;响应于目标用车人在身份验证页面上的输入操作,从身份验证页面上提取目标用车人的身份信息并发送至服务器,以供服务器根据候选用车人的身份验证信息对目标用车人的身份信息进行验证。Further, the car key information is obtained by the server encrypting the created data to obtain ciphertext, and adding the ciphertext to the URL of the authentication page; the sending
进一步的,受权模块703具体用于:如果验证通过,接收服务器向目标用车人的终端发送的授权验证码;将目标用车人输入的验证码发送至服务器,以供服务器将验证码与授权验证码比对,如果一致,将车辆标识对应的车辆的使用权授予给目标用车人。Further, the
进一步的,受权模块703具体用于:如果验证通过,展示解锁页面;响应于目标用车人在解锁页面上的解锁操作,向服务器发送解锁请求,以供服务器根据解锁请求,解锁车辆标识对应的车辆。Further, the
上述基于车钥匙信息的车辆受权装置可执行本申请任意实施例所提供的基于车钥匙信息的车辆受权方法,具备执行基于车钥匙信息的车辆受权方法相应的功能模块和有益效果。The above vehicle authorization device based on vehicle key information can execute the vehicle authorization method based on vehicle key information provided in any embodiment of the present application, and has functional modules and beneficial effects corresponding to executing the vehicle authorization method based on vehicle key information.
实施例八Embodiment 8
图8是本申请实施例八中的一种车钥匙信息的处理装置的结构图,本申请实施例适用于服务器根据车主的要求将车辆的使用权限授予给用车人的情况,该装置采用软件和/或硬件实现,并具体配置于具备一定数据运算能力的服务器中。8 is a structural diagram of an apparatus for processing vehicle key information in the eighth embodiment of the present application. The embodiment of the present application is applicable to the situation where the server grants the vehicle use authority to the vehicle user according to the requirements of the vehicle owner, and the apparatus adopts software And/or hardware implementation, and is specifically configured in a server with certain data computing capabilities.
如图8所示的一种车钥匙信息的处理装置800,包括:第一接收模块801、创建模块802、发送模块803、第二接收模块804和授权模块805。As shown in FIG. 8 , an
第一接收模块801,用于接收第一终端发送的创建数据,创建数据包括:车辆标识和候选用车人的身份验证信息;The
创建模块802,用于根据创建数据创建车钥匙信息;A
发送模块803,用于将车钥匙信息发送至第一终端,以供第一终端将车钥匙信息发送至目标用车人的第二终端;a sending
第二接收模块804,用于接收第二终端发送的目标用车人的身份信息,并根据候选用车人的身份验证信息对目标用车人的身份信息进行验证;The
授权模块805,用于如果验证通过,将车辆标识对应的车辆的使用权授予给目标用车人。The
本申请实施例中,服务器获取车主输入的车辆标识和候选用车人的身份验证信息,生成车钥匙信息,该车钥匙信息包含候选用车人的身份验证信息,保留了车主对用车人的选择权;通过服务器接收第二终端发送的目标用车人的身份信息,并根据候选用车人的身份验证信息对目标用车人的身份信息进行验证,通过身份验证的方法实现车辆使用权的授予,不需要复杂的加密和验证程序,提高了授予过程的安全性和便捷性。In the embodiment of the present application, the server obtains the vehicle identification and the identity verification information of the candidate vehicle user input by the vehicle owner, and generates the vehicle key information. The right to choose; receive the identity information of the target vehicle user sent by the second terminal through the server, and verify the identity information of the target vehicle user according to the identity verification information of the candidate vehicle user, and realize the right to use the vehicle through the method of identity verification. Granting does not require complicated encryption and verification procedures, which improves the security and convenience of the granting process.
进一步的,创建模块802具体用于:对创建数据进行加密,得到密文;将密文添加到身份验证页面网址中,得到车钥匙信息;相应的,第二接收模块804具体用于:接收第二终端发送的身份验证页面网址的请求信息,向第二终端返回身份验证页面;接收第二终端从身份验证页面上提取的目标用车人的身份信息;从身份验证页面网址中提取密文,并对密文进行解密得到候选用车人的身份验证信息;根据候选用车人的身份验证信息对目标用车人的身份信息进行验证。Further, the
进一步的,创建数据还包括:车钥匙信息的失效条件;该装置还包括失效模块,用于如果满足失效条件,服务器向第二终端发送失效提示信息,和/或对车钥匙信息进行失效处理。Further, the creation data further includes: failure conditions of the car key information; the device further includes a failure module, for if the failure conditions are met, the server sends failure prompt information to the second terminal, and/or performs failure processing on the car key information.
上述车钥匙信息的处理装置可执行本申请任意实施例所提供的车钥匙信息的处理方法,具备执行车钥匙信息的处理方法相应的功能模块和有益效果。The above apparatus for processing vehicle key information can execute the method for processing vehicle key information provided by any embodiment of the present application, and has functional modules and beneficial effects corresponding to the method for processing vehicle key information.
实施例九Embodiment 9
根据本申请的实施例,本申请还提供了一种终端、服务器和一种可读存储介质。According to the embodiments of the present application, the present application further provides a terminal, a server, and a readable storage medium.
如图9所示,是实现本申请实施例的基于车钥匙信息的车辆授权方法或基于车钥匙信息的车辆受权方法(以下简称基于车钥匙信息的车辆授权或受权方法)的终端的框图。终端旨在表示各种形式的数字计算机,诸如,膝上型计算机、台式计算机、工作台、个人数字助理、服务器、刀片式服务器、大型计算机、和其它适合的计算机。终端还可以表示各种形式的移动装置,诸如,个人数字处理、蜂窝电话、智能电话、可穿戴设备和其它类似的计算装置。本文所示的部件、它们的连接和关系、以及它们的功能仅仅作为示例,并且不意在限制本文中描述的和/或者要求的本申请的实现。As shown in FIG. 9 , it is a block diagram of a terminal that implements the vehicle authorization method based on vehicle key information or the vehicle authorization method based on vehicle key information (hereinafter referred to as vehicle authorization or authorization method based on vehicle key information) according to an embodiment of the present application. Terminals are intended to represent various forms of digital computers, such as laptop computers, desktop computers, workstations, personal digital assistants, servers, blade servers, mainframe computers, and other suitable computers. A terminal may also represent various forms of mobile devices, such as personal digital processors, cellular phones, smart phones, wearable devices, and other similar computing devices. The components shown herein, their connections and relationships, and their functions are by way of example only, and are not intended to limit implementations of the application described and/or claimed herein.
如图9所示,该终端包括:一个或多个处理器901、存储器902,以及用于连接各部件的接口,包括高速接口和低速接口。各个部件利用不同的总线互相连接,并且可以被安装在公共主板上或者根据需要以其它方式安装。处理器可以对在终端内执行的指令进行处理,包括存储在存储器中或者存储器上以在外部输入/输出装置(诸如,耦合至接口的显示设备)上显示GUI的图形信息的指令。在其它实施方式中,若需要,可以将多个处理器和/或多条总线与多个存储器和多个存储器一起使用。同样,可以连接多个终端,各个终端提供部分必要的操作(例如,作为服务器阵列、一组刀片式服务器、或者多处理器系统)。图9中以一个处理器901为例。As shown in FIG. 9, the terminal includes: one or
存储器902即为本申请所提供的非瞬时计算机可读存储介质。其中,存储器存储有可由至少一个处理器执行的指令,以使至少一个处理器执行本申请所提供的基于车钥匙信息的车辆授权或受权方法。本申请的非瞬时计算机可读存储介质存储计算机指令,该计算机指令用于使计算机执行本申请所提供的基于车钥匙信息的车辆授权或受权方法。The
存储器902作为一种非瞬时计算机可读存储介质,可用于存储非瞬时软件程序、非瞬时计算机可执行程序以及模块,如本申请实施例中的基于车钥匙信息的车辆授权或受权方法对应的程序指令/模块(例如,附图6所示的包括第一发送模块601、接收模块602和第二发送模块603;如附图7所示的包括接收模块701、发送模块702和受权模块703)。处理器901通过运行存储在存储器902中的非瞬时软件程序、指令以及模块,从而执行服务器的各种功能应用以及数据处理,即实现上述方法实施例中的基于车钥匙信息的车辆授权或受权方法。As a non-transitory computer-readable storage medium, the
存储器902可以包括存储程序区和存储数据区,其中,存储程序区可存储操作系统、至少一个功能所需要的应用程序;存储数据区可存储实现基于车钥匙信息的车辆授权或受权方法的终端的使用所创建的数据等。此外,存储器902可以包括高速随机存取存储器,还可以包括非瞬时存储器,例如至少一个磁盘存储器件、闪存器件、或其他非瞬时固态存储器件。在一些实施例中,存储器902可选包括相对于处理器901远程设置的存储器,这些远程存储器可以通过网络连接至执行基于车钥匙信息的车辆授权或受权方法的终端。上述网络的实例包括但不限于互联网、企业内部网、局域网、移动通信网及其组合。The
执行基于车钥匙信息的车辆授权或受权方法的终端还可以包括:输入装置903和输出装置904。处理器901、存储器902、输入装置903和输出装置904可以通过总线或者其他方式连接,图9中以通过总线连接为例。The terminal for executing the vehicle authorization or authorization method based on the vehicle key information may further include: an
输入装置903可接收输入的数字或字符信息,以及产生与执行基于车钥匙信息的车辆授权或受权方法的终端的用户设置以及功能控制有关的键信号输入,例如触摸屏、小键盘、鼠标、轨迹板、触摸板、指示杆、一个或者多个鼠标按钮、轨迹球、操纵杆等输入装置。输出装置904可以包括显示设备、辅助照明装置(例如,LED)和触觉反馈装置(例如,振动电机)等。该显示设备可以包括但不限于,液晶显示器(LCD)、发光二极管(LED)显示器和等离子体显示器。在一些实施方式中,显示设备可以是触摸屏。The
本实施例还提供一种服务器,其结构如图9所示,对图9中各部分的描述详见上述实施例,此处不再赘述。不同之处在于,存储器902作为一种非瞬时计算机可读存储介质,可用于存储非瞬时软件程序、非瞬时计算机可执行程序以及模块,如本申请实施例中的车钥匙信息的处理方法对应的程序指令/模块(例如,附图8所示的包括第一接收模块801、创建模块802、发送模块803、第二接收模块804和授权模块805)。This embodiment further provides a server, the structure of which is shown in FIG. 9 . For the description of each part in FIG. 9 , refer to the foregoing embodiment, and details are not repeated here. The difference is that the
此处描述的系统和技术的各种实施方式可以在数字电子电路系统、集成电路系统、专用ASIC(专用集成电路)、计算机硬件、固件、软件、和/或它们的组合中实现。这些各种实施方式可以包括:实施在一个或者多个计算机程序中,该一个或者多个计算机程序可在包括至少一个可编程处理器的可编程系统上执行和/或解释,该可编程处理器可以是专用或者通用可编程处理器,可以从存储系统、至少一个输入装置、和至少一个输出装置接收数据和指令,并且将数据和指令传输至该存储系统、该至少一个输入装置、和该至少一个输出装置。Various implementations of the systems and techniques described herein can be implemented in digital electronic circuitry, integrated circuit systems, application specific ASICs (application specific integrated circuits), computer hardware, firmware, software, and/or combinations thereof. These various embodiments may include being implemented in one or more computer programs executable and/or interpretable on a programmable system including at least one programmable processor that The processor, which may be a special purpose or general-purpose programmable processor, may receive data and instructions from a storage system, at least one input device, and at least one output device, and transmit data and instructions to the storage system, the at least one input device, and the at least one output device an output device.
这些计算程序(也称作程序、软件、软件应用、或者代码)包括可编程处理器的机器指令,并且可以利用高级过程和/或面向对象的编程语言、和/或汇编/机器语言来实施这些计算程序。如本文使用的,术语“机器可读介质”和“计算机可读介质”指的是用于将机器指令和/或数据提供给可编程处理器的任何计算机程序产品、设备、和/或装置(例如,磁盘、光盘、存储器、可编程逻辑装置(PLD)),包括,接收作为机器可读信号的机器指令的机器可读介质。术语“机器可读信号”指的是用于将机器指令和/或数据提供给可编程处理器的任何信号。These computational programs (also referred to as programs, software, software applications, or codes) include machine instructions for programmable processors, and may be implemented using high-level procedural and/or object-oriented programming languages, and/or assembly/machine languages calculation program. As used herein, the terms "machine-readable medium" and "computer-readable medium" refer to any computer program product, apparatus, and/or apparatus for providing machine instructions and/or data to a programmable processor ( For example, magnetic disks, optical disks, memories, programmable logic devices (PLDs), including machine-readable media that receive machine instructions as machine-readable signals. The term "machine-readable signal" refers to any signal used to provide machine instructions and/or data to a programmable processor.
为了提供与用户的交互,可以在计算机上实施此处描述的系统和技术,该计算机具有:用于向用户显示信息的显示装置(例如,CRT(阴极射线管)或者LCD(液晶显示器)监视器);以及键盘和指向装置(例如,鼠标或者轨迹球),用户可以通过该键盘和该指向装置来将输入提供给计算机。其它种类的装置还可以用于提供与用户的交互;例如,提供给用户的反馈可以是任何形式的传感反馈(例如,视觉反馈、听觉反馈、或者触觉反馈);并且可以用任何形式(包括声输入、语音输入或者、触觉输入)来接收来自用户的输入。To provide interaction with a user, the systems and techniques described herein may be implemented on a computer having a display device (eg, a CRT (cathode ray tube) or LCD (liquid crystal display) monitor) for displaying information to the user ); and a keyboard and pointing device (eg, a mouse or trackball) through which a user can provide input to the computer. Other kinds of devices can also be used to provide interaction with the user; for example, the feedback provided to the user can be any form of sensory feedback (eg, visual feedback, auditory feedback, or tactile feedback); and can be in any form (including acoustic input, voice input, or tactile input) to receive input from the user.
可以将此处描述的系统和技术实施在包括后台部件的计算系统(例如,作为数据服务器)、或者包括中间件部件的计算系统(例如,应用服务器)、或者包括前端部件的计算系统(例如,具有图形用户页面或者网络浏览器的用户计算机,用户可以通过该图形用户页面或者该网络浏览器来与此处描述的系统和技术的实施方式交互)、或者包括这种后台部件、中间件部件、或者前端部件的任何组合的计算系统中。可以通过任何形式或者介质的数字数据通信(例如,通信网络)来将系统的部件相互连接。通信网络的示例包括:局域网(LAN)、广域网(WAN)、互联网和区块链网络。The systems and techniques described herein may be implemented on a computing system that includes back-end components (eg, as a data server), or a computing system that includes middleware components (eg, an application server), or a computing system that includes front-end components (eg, a user's computer having a graphical user page or web browser through which a user may interact with implementations of the systems and techniques described herein), or including such backend components, middleware components, Or any combination of front-end components in a computing system. The components of the system may be interconnected by any form or medium of digital data communication (eg, a communication network). Examples of communication networks include: Local Area Networks (LANs), Wide Area Networks (WANs), the Internet, and blockchain networks.
计算机系统可以包括客户端和服务器。客户端和服务器一般远离彼此并且通常通过通信网络进行交互。通过在相应的计算机上运行并且彼此具有客户端-服务器关系的计算机程序来产生客户端和服务器的关系。A computer system can include clients and servers. Clients and servers are generally remote from each other and usually interact through a communication network. The relationship of client and server arises by computer programs running on the respective computers and having a client-server relationship to each other.
应该理解,可以使用上面所示的各种形式的流程,重新排序、增加或删除步骤。例如,本发申请中记载的各步骤可以并行地执行也可以顺序地执行也可以不同的次序执行,只要能够实现本申请公开的技术方案所期望的结果,本文在此不进行限制。It should be understood that steps may be reordered, added or deleted using the various forms of flow shown above. For example, the steps described in the present application can be performed in parallel, sequentially or in different orders, and as long as the desired results of the technical solutions disclosed in the present application can be achieved, no limitation is imposed herein.
上述具体实施方式,并不构成对本申请保护范围的限制。本领域技术人员应该明白的是,根据设计要求和其他因素,可以进行各种修改、组合、子组合和替代。任何在本申请的精神和原则之内所作的修改、等同替换和改进等,均应包含在本申请保护范围之内。The above-mentioned specific embodiments do not constitute a limitation on the protection scope of the present application. It should be understood by those skilled in the art that various modifications, combinations, sub-combinations and substitutions may occur depending on design requirements and other factors. Any modifications, equivalent replacements and improvements made within the spirit and principles of this application shall be included within the protection scope of this application.
Claims (15)
Priority Applications (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN202010188569.0A CN111402463A (en) | 2020-03-17 | 2020-03-17 | Vehicle authorization method and device based on vehicle key information |
Applications Claiming Priority (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN202010188569.0A CN111402463A (en) | 2020-03-17 | 2020-03-17 | Vehicle authorization method and device based on vehicle key information |
Publications (1)
| Publication Number | Publication Date |
|---|---|
| CN111402463A true CN111402463A (en) | 2020-07-10 |
Family
ID=71432525
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| CN202010188569.0A Pending CN111402463A (en) | 2020-03-17 | 2020-03-17 | Vehicle authorization method and device based on vehicle key information |
Country Status (1)
| Country | Link |
|---|---|
| CN (1) | CN111402463A (en) |
Cited By (10)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN112333178A (en) * | 2020-10-29 | 2021-02-05 | 深圳市元征科技股份有限公司 | Vehicle sharing method and device, terminal device and storage medium |
| CN113442871A (en) * | 2021-06-30 | 2021-09-28 | 重庆长安新能源汽车科技有限公司 | NFC-based keyless entry method and system |
| CN113516527A (en) * | 2020-12-24 | 2021-10-19 | 九号智能(常州)科技有限公司 | Vehicle management method for electric scooter, owner terminal, user terminal and equipment |
| CN113709695A (en) * | 2021-08-04 | 2021-11-26 | 一汽解放汽车有限公司 | Vehicle use authorization method and system |
| CN113989960A (en) * | 2021-10-21 | 2022-01-28 | 上海瓶钵信息科技有限公司 | Method and system for sharing digital key of equipment |
| CN114419770A (en) * | 2022-03-28 | 2022-04-29 | 斯润天朗(北京)科技有限公司 | Fleet digital key management method and device and computer |
| CN114627578A (en) * | 2022-03-05 | 2022-06-14 | 小耳朵(广东)电子科技股份有限公司 | Remote control unlocking method, device and system |
| CN115019419A (en) * | 2022-04-26 | 2022-09-06 | 上海银基信息安全技术股份有限公司 | Vehicle unlocking method, device, equipment and storage medium |
| CN116912982A (en) * | 2023-07-31 | 2023-10-20 | 重庆赛力斯新能源汽车设计院有限公司 | Vehicle Bluetooth key management method and device and terminal equipment |
| CN120135113A (en) * | 2025-03-31 | 2025-06-13 | 广汽本田汽车有限公司 | Vehicle anti-theft control method, device, equipment and medium |
Citations (9)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN106375312A (en) * | 2016-08-31 | 2017-02-01 | 长城汽车股份有限公司 | Virtual key authorization method and system, mobile terminal and server |
| US20170267214A1 (en) * | 2011-04-22 | 2017-09-21 | Angel A. Penilla | Vehicles and cloud systems for assigning temporary e-keys to access use of a vehicle |
| CN107650863A (en) * | 2017-09-19 | 2018-02-02 | 大陆汽车投资(上海)有限公司 | Vehicle sharing method and system |
| CN107685714A (en) * | 2017-08-30 | 2018-02-13 | 上海博泰悦臻电子设备制造有限公司 | Intelligent vehicle key system and its control method |
| CN108038770A (en) * | 2018-01-02 | 2018-05-15 | 戴姆勒股份公司 | The method of shared automobile |
| CN109389459A (en) * | 2018-09-05 | 2019-02-26 | 浙江吉利汽车研究院有限公司 | A kind of vehicle lending system and method |
| CN109874125A (en) * | 2019-01-29 | 2019-06-11 | 上海博泰悦臻网络技术服务有限公司 | The car owner's authorization method and system of bluetooth key, storage medium and vehicle Cloud Server |
| CN110126782A (en) * | 2019-05-23 | 2019-08-16 | 东风小康汽车有限公司重庆分公司 | A kind of Vehicular intelligent key application method and device |
| CN110316149A (en) * | 2019-05-31 | 2019-10-11 | 大众问问(北京)信息科技有限公司 | A kind of method, apparatus, equipment and system authorizing unlocking vehicle |
-
2020
- 2020-03-17 CN CN202010188569.0A patent/CN111402463A/en active Pending
Patent Citations (9)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US20170267214A1 (en) * | 2011-04-22 | 2017-09-21 | Angel A. Penilla | Vehicles and cloud systems for assigning temporary e-keys to access use of a vehicle |
| CN106375312A (en) * | 2016-08-31 | 2017-02-01 | 长城汽车股份有限公司 | Virtual key authorization method and system, mobile terminal and server |
| CN107685714A (en) * | 2017-08-30 | 2018-02-13 | 上海博泰悦臻电子设备制造有限公司 | Intelligent vehicle key system and its control method |
| CN107650863A (en) * | 2017-09-19 | 2018-02-02 | 大陆汽车投资(上海)有限公司 | Vehicle sharing method and system |
| CN108038770A (en) * | 2018-01-02 | 2018-05-15 | 戴姆勒股份公司 | The method of shared automobile |
| CN109389459A (en) * | 2018-09-05 | 2019-02-26 | 浙江吉利汽车研究院有限公司 | A kind of vehicle lending system and method |
| CN109874125A (en) * | 2019-01-29 | 2019-06-11 | 上海博泰悦臻网络技术服务有限公司 | The car owner's authorization method and system of bluetooth key, storage medium and vehicle Cloud Server |
| CN110126782A (en) * | 2019-05-23 | 2019-08-16 | 东风小康汽车有限公司重庆分公司 | A kind of Vehicular intelligent key application method and device |
| CN110316149A (en) * | 2019-05-31 | 2019-10-11 | 大众问问(北京)信息科技有限公司 | A kind of method, apparatus, equipment and system authorizing unlocking vehicle |
Cited By (13)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN112333178A (en) * | 2020-10-29 | 2021-02-05 | 深圳市元征科技股份有限公司 | Vehicle sharing method and device, terminal device and storage medium |
| CN113516527A (en) * | 2020-12-24 | 2021-10-19 | 九号智能(常州)科技有限公司 | Vehicle management method for electric scooter, owner terminal, user terminal and equipment |
| CN113442871A (en) * | 2021-06-30 | 2021-09-28 | 重庆长安新能源汽车科技有限公司 | NFC-based keyless entry method and system |
| CN113709695B (en) * | 2021-08-04 | 2024-04-09 | 一汽解放汽车有限公司 | Vehicle use authorization method and system |
| CN113709695A (en) * | 2021-08-04 | 2021-11-26 | 一汽解放汽车有限公司 | Vehicle use authorization method and system |
| CN113989960A (en) * | 2021-10-21 | 2022-01-28 | 上海瓶钵信息科技有限公司 | Method and system for sharing digital key of equipment |
| CN114627578A (en) * | 2022-03-05 | 2022-06-14 | 小耳朵(广东)电子科技股份有限公司 | Remote control unlocking method, device and system |
| CN114419770A (en) * | 2022-03-28 | 2022-04-29 | 斯润天朗(北京)科技有限公司 | Fleet digital key management method and device and computer |
| CN115019419A (en) * | 2022-04-26 | 2022-09-06 | 上海银基信息安全技术股份有限公司 | Vehicle unlocking method, device, equipment and storage medium |
| CN115019419B (en) * | 2022-04-26 | 2024-12-31 | 上海银基科技股份有限公司 | Vehicle unlocking method, device, equipment and storage medium |
| CN116912982A (en) * | 2023-07-31 | 2023-10-20 | 重庆赛力斯新能源汽车设计院有限公司 | Vehicle Bluetooth key management method and device and terminal equipment |
| CN120135113A (en) * | 2025-03-31 | 2025-06-13 | 广汽本田汽车有限公司 | Vehicle anti-theft control method, device, equipment and medium |
| CN120135113B (en) * | 2025-03-31 | 2025-11-18 | 广汽本田汽车有限公司 | Vehicle anti-theft control methods, devices, equipment and media |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| CN111402463A (en) | Vehicle authorization method and device based on vehicle key information | |
| US10217304B2 (en) | Intelligent vehicular electronic key system | |
| CN111277577B (en) | Digital identity verification method, apparatus, device and storage medium | |
| CN111064757B (en) | Application access method and device, electronic equipment and storage medium | |
| US11206521B2 (en) | Selective pairing of wireless devices using shared keys | |
| CN108351927B (en) | Password-free authentication for access management | |
| US8955076B1 (en) | Controlling access to a protected resource using multiple user devices | |
| US10581826B2 (en) | Run-time trust management system for access impersonation | |
| US10225283B2 (en) | Protection against end user account locking denial of service (DOS) | |
| US11196563B2 (en) | System and method for providing services via a network | |
| JP7550125B2 (en) | Digital key system for vehicle, digital key management method for vehicle, mobile terminal | |
| TWI788354B (en) | Method and apparatus for managing vehicle control permissions | |
| CN113674455B (en) | Remote control method, device, system, equipment and storage medium for intelligent door lock | |
| CN105659557A (en) | Web-based interface integration for single sign-on | |
| US12043210B2 (en) | System for managing access to a vehicle by a service provider that is to provide a service associated with the vehicle | |
| JP6638945B2 (en) | Electronic key management system auxiliary device, electronic key management system, method, and program | |
| WO2023054296A1 (en) | Vehicle-use digital key system, vehicle-use digital key management method, vehicle-use device, and mobile terminal | |
| JP7605077B2 (en) | Digital key system for vehicle and method for managing digital key for vehicle | |
| CN113554793A (en) | Temporary access method, device, storage medium and system for intelligent access control system | |
| CN113468565B (en) | Intelligent door lock control method and system | |
| CN114155630B (en) | Security verification method, electronic device and medium | |
| CN115623478B (en) | Information transmission methods, devices, electronic equipment and readable storage media | |
| US20260019282A1 (en) | Digital-key sharing method, digital-key authentication method, and computing device | |
| JP6962676B2 (en) | Authentication-related information transmission control program, authentication-related information transmission control device, and authentication-related information transmission control method | |
| CN120808472A (en) | Vehicle control method, device and related system |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| PB01 | Publication | ||
| PB01 | Publication | ||
| SE01 | Entry into force of request for substantive examination | ||
| SE01 | Entry into force of request for substantive examination | ||
| TA01 | Transfer of patent application right |
Effective date of registration: 20211022 Address after: 100176 101, floor 1, building 1, yard 7, Ruihe West 2nd Road, Beijing Economic and Technological Development Zone, Daxing District, Beijing Applicant after: Apollo Intelligent Connectivity (Beijing) Technology Co., Ltd. Address before: 2 / F, baidu building, 10 Shangdi 10th Street, Haidian District, Beijing 100085 Applicant before: BEIJING BAIDU NETCOM SCIENCE AND TECHNOLOGY Co.,Ltd. |
|
| TA01 | Transfer of patent application right |