CN110868388A - System and method for operating a networked device - Google Patents
System and method for operating a networked device Download PDFInfo
- Publication number
- CN110868388A CN110868388A CN201910791760.1A CN201910791760A CN110868388A CN 110868388 A CN110868388 A CN 110868388A CN 201910791760 A CN201910791760 A CN 201910791760A CN 110868388 A CN110868388 A CN 110868388A
- Authority
- CN
- China
- Prior art keywords
- tree structure
- compressed
- subpart
- sub
- node
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Granted
Links
- 238000000034 method Methods 0.000 title claims abstract description 61
- 230000006835 compression Effects 0.000 claims abstract description 29
- 238000007906 compression Methods 0.000 claims abstract description 29
- 238000012360 testing method Methods 0.000 claims abstract description 12
- 230000015654 memory Effects 0.000 claims description 114
- 238000001914 filtration Methods 0.000 claims description 16
- 238000005516 engineering process Methods 0.000 description 35
- 238000010586 diagram Methods 0.000 description 10
- 230000006855 networking Effects 0.000 description 9
- 239000007787 solid Substances 0.000 description 5
- 238000004891 communication Methods 0.000 description 4
- 230000000116 mitigating effect Effects 0.000 description 4
- 238000012545 processing Methods 0.000 description 4
- 238000013459 approach Methods 0.000 description 3
- 238000004590 computer program Methods 0.000 description 2
- 238000001514 detection method Methods 0.000 description 2
- 238000012986 modification Methods 0.000 description 2
- 230000004048 modification Effects 0.000 description 2
- 241001237160 Kallima inachus Species 0.000 description 1
- 238000003491 array Methods 0.000 description 1
- 230000003190 augmentative effect Effects 0.000 description 1
- 230000009286 beneficial effect Effects 0.000 description 1
- 238000007796 conventional method Methods 0.000 description 1
- 230000000694 effects Effects 0.000 description 1
- 239000000835 fiber Substances 0.000 description 1
- 230000014509 gene expression Effects 0.000 description 1
- 238000012806 monitoring device Methods 0.000 description 1
- 230000003287 optical effect Effects 0.000 description 1
- 238000005457 optimization Methods 0.000 description 1
- 230000009467 reduction Effects 0.000 description 1
Images
Classifications
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/02—Network architectures or network communication protocols for network security for separating internal from external traffic, e.g. firewalls
- H04L63/0227—Filtering policies
- H04L63/0263—Rule management
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/04—Network architectures or network communication protocols for network security for providing a confidential data exchange among entities communicating through data packet networks
- H04L63/0428—Network architectures or network communication protocols for network security for providing a confidential data exchange among entities communicating through data packet networks wherein the data content is protected, e.g. by encrypting or encapsulating the payload
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L12/00—Data switching networks
- H04L12/28—Data switching networks characterised by path configuration, e.g. LAN [Local Area Networks] or WAN [Wide Area Networks]
- H04L12/44—Star or tree networks
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L43/00—Arrangements for monitoring or testing data switching networks
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L45/00—Routing or path finding of packets in data switching networks
- H04L45/02—Topology update or discovery
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L45/00—Routing or path finding of packets in data switching networks
- H04L45/56—Routing software
- H04L45/566—Routing instructions carried by the data packet, e.g. active networks
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L45/00—Routing or path finding of packets in data switching networks
- H04L45/74—Address processing for routing
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/02—Network architectures or network communication protocols for network security for separating internal from external traffic, e.g. firewalls
- H04L63/0227—Filtering policies
- H04L63/0236—Filtering by address, protocol, port number or service, e.g. IP-address or URL
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/02—Network architectures or network communication protocols for network security for separating internal from external traffic, e.g. firewalls
- H04L63/0227—Filtering policies
- H04L63/0245—Filtering by information in the payload
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/14—Network architectures or network communication protocols for network security for detecting or protecting against malicious traffic
- H04L63/1408—Network architectures or network communication protocols for network security for detecting or protecting against malicious traffic by monitoring network traffic
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/14—Network architectures or network communication protocols for network security for detecting or protecting against malicious traffic
- H04L63/1408—Network architectures or network communication protocols for network security for detecting or protecting against malicious traffic by monitoring network traffic
- H04L63/1416—Event detection, e.g. attack signature detection
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/14—Network architectures or network communication protocols for network security for detecting or protecting against malicious traffic
- H04L63/1441—Countermeasures against malicious traffic
- H04L63/1458—Denial of Service
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/32—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials
- H04L9/3247—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials involving digital signatures
- H04L9/3255—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials involving digital signatures using group based signatures, e.g. ring or threshold signatures
Landscapes
- Engineering & Computer Science (AREA)
- Computer Networks & Wireless Communication (AREA)
- Signal Processing (AREA)
- Computer Security & Cryptography (AREA)
- Computer Hardware Design (AREA)
- Computing Systems (AREA)
- General Engineering & Computer Science (AREA)
- Business, Economics & Management (AREA)
- General Business, Economics & Management (AREA)
- Data Exchanges In Wide-Area Networks (AREA)
Abstract
描述了用于压缩将网络分组签名与网络分组元数据相关联的树结构的方法和系统,该树结构包括包含网络分组元数据的多个叶节点和单比特测试节点的多个非叶节点,该方法包括确定是否要压缩树结构的子部分。如果做出要压缩树结构的子部分的确定,则生成经压缩的节点数据结构,经压缩的节点数据结构包括树结构的子部分的路径,该路径包括由与树结构的子部分的连续非叶节点中的每一个相关联的单比特的级联形成的比特序列,该序列的比特数等于或大于压缩阈值。
Described are methods and systems for compressing a tree structure that associates network packet signatures with network packet metadata, the tree structure including a plurality of leaf nodes containing network packet metadata and a plurality of non-leaf nodes of single-bit test nodes, The method includes determining whether to compress sub-portions of the tree structure. If a determination is made that a sub-portion of the tree structure is to be compressed, a compressed node data structure is generated, the compressed node data structure including a path to the sub-portion of the tree structure, the path including a path consisting of consecutive non-subsections with the sub-portion of the tree structure A bit sequence formed by concatenation of single bits associated with each leaf node, the number of bits in the sequence is equal to or greater than the compression threshold.
Description
交叉引用cross reference
本申请要求于2018年8月27日提交的欧洲专利申请第1 831 5022.6号的优先权。This application claims priority from European Patent Application No. 1 831 5022.6 filed on August 27, 2018.
技术领域technical field
本文描述的实施方式大体上涉及用于操作联网设备的系统和方法,并且更具体地,涉及用于生成和/或操作将网络数据签名与网络分组元数据相关联的数据结构的系统和方法。Embodiments described herein relate generally to systems and methods for operating networked devices, and more particularly, to systems and methods for generating and/or manipulating data structures that associate network data signatures with network packet metadata.
背景技术Background technique
连接至因特网的基础设施例如数据中心可能遭受旨在渗透或损害其操作的攻击。例如,包括大量僵尸程序的僵尸网络可以用于引起对数据中心的分布式拒绝服务(DDoS)攻击。DDoS攻击可能使数据中心充斥着过多的请求。在这样的攻击下,数据中心处理和通信能力可能会变得过载,以至于暂时无法向合法用户和客户端提供服务。在至少一个事件中,攻击可以对数据中心施加每秒一(1)太比特的负荷。Internet-connected infrastructure, such as data centers, may be subject to attacks aimed at infiltrating or compromising their operations. For example, a botnet comprising a large number of bots can be used to cause a distributed denial of service (DDoS) attack on a data center. DDoS attacks can flood a data center with too many requests. Under such an attack, data center processing and communication capabilities can become so overloaded that legitimate users and clients cannot be served temporarily. In at least one event, the attack can impose a load of one (1) terabit per second on the data center.
因此,需要采取缓解措施,以降低潜在攻击的负面影响。这样的缓解措施可以包括过滤非法网络分组同时准许合法网络分组访问数据中心的网络。鉴于大量网络分组从因特网路由到数据中心,即使在数据中心的规模相对较小的情况下,从合法网络分组中过滤非法网络分组可能需要重要的处理资源,并且可能影响要呈现给合法用户和数据中心的客户端的服务质量(例如,提供托管在数据中心处的给定服务时的时延)。Therefore, mitigation measures are required to reduce the negative impact of potential attacks. Such mitigations may include filtering illegal network packets while granting legitimate network packets access to the data center's network. Given the large number of network packets routed from the Internet to the data center, even at relatively small data centers, filtering illegal network packets from legitimate network packets can require significant processing resources and can affect the ability of data to be presented to legitimate users and data Quality of service for clients at the center (eg, latency in providing a given service hosted at the data center).
虽然已经研究了旨在降低缓解措施的负面影响的方法,但仍然需要改进。While methods to reduce the negative impact of mitigation measures have been investigated, improvements are still needed.
背景技术部分中讨论的主题不应仅仅因为是在背景技术部分中提及而被认为是现有技术。类似地,在背景技术部分中提到的问题或与背景技术部分的主题关联的问题不应被认为先前在现有技术中已被认识到。背景技术部分中的主题仅表示不同的方法。The subject matter discussed in the Background section should not be admitted to be prior art merely because it is mentioned in the Background section. Similarly, problems mentioned in the Background section or problems associated with the subject matter of the Background section should not be considered to have been previously recognized in the prior art. The topics in the Background section are merely indicative of different approaches.
发明内容SUMMARY OF THE INVENTION
以下概述仅出于说明性目的,并不旨在限制或约束详细描述。以下概述仅以简化形式呈现各种所描述的方面作为下面提供的更详细描述的序言。The following summary is for illustrative purposes only and is not intended to limit or restrict the detailed description. The following summary merely presents the various described aspects in a simplified form as a prelude to the more detailed description provided below.
在某些实例中,过滤和/或分类网络分组可能需要访问将网络分组签名与网络分组元数据相关联的数据结构。In some instances, filtering and/or classifying network packets may require access to data structures that associate network packet signatures with network packet metadata.
在一些实例中,网络分组签名可以是与发送主机或目的地主机相关联的网络地址。作为示例但不限于此,网络分组签名可以是与网络分组相关联的因特网协议(IP)地址,例如因特网协议版本4(IPv4)地址或因特网协议版本6(IPv6)地址。在另一示例中,网络分组签名可以是IP地址的一部分(例如,IP地址的网络部分或主机部分)。在其他示例中,可以基于IP地址生成网络分组签名。在一些实施方式中,网络分组签名可以包括来自以下列表的一个或更多个元素:该列表包括源IP地址、目的地IP地址、IP协议(例如TCP或UDP)、源TCP或UDP端口、目的地TCP或UDP端口。在一些其他实施方式中,网络分组签名可以包括与一些元数据(例如,简档标识符和/或计数器标识符)相关联的源IP地址和/或目的地IP地址。关于网络分组签名可以包含什么的变型对于本技术领域的技术人员来说将变得明显,并且不应该被解释为是限制性的。In some instances, the network packet signature may be a network address associated with the sending host or the destination host. By way of example and not limitation, the network packet signature may be an Internet Protocol (IP) address associated with the network packet, such as an Internet Protocol version 4 (IPv4) address or an Internet Protocol version 6 (IPv6) address. In another example, the network packet signature may be part of the IP address (eg, the network portion or the host portion of the IP address). In other examples, network packet signatures can be generated based on IP addresses. In some implementations, the network packet signature may include one or more elements from a list including source IP address, destination IP address, IP protocol (eg, TCP or UDP), source TCP or UDP port, destination local TCP or UDP port. In some other implementations, the network packet signature may include a source IP address and/or a destination IP address associated with some metadata (eg, a profile identifier and/or a counter identifier). Variations on what a network packet signature may contain will become apparent to those skilled in the art and should not be construed as limiting.
在一些实例中,网络分组元数据可以是与一个或更多个网络分组签名相关联或要与一个或更多个网络分组签名相关联的信息。作为示例,网络分组元数据可以建立数据分组分类和/或过滤规则。这样的数据分组分类可以使得能够确定与网络分组签名相关联的网络分组是否合法。分类和/或过滤规则可以确定应该如何处理数据分组和/或应该执行什么服务。例如,过滤规则可以用于测试从外部计算设备进入数据中心的网络的网络分组,以确保可以拦截进入数据中心的网络的企图。替选过滤规则也可以用于基于优先级传输流量(traffic)。即使在来自第二主机的网络分组可能被丢弃的情况下,也可以传输来自第一主机的网络分组,因为来自第一主机的网络分组具有更高的优先级。在一些实施方式中,网络分组元数据还可以被称为网络分组简档标签。在一些实施方式中,网络分组元数据还可以被称为网络分组标签(或标签)。关于网络分组元数据可以包含什么的变型对于本技术领域的技术人员来说将变得明显,并且不应该被解释为是限制性的。In some instances, network packet metadata may be information associated with or to be associated with one or more network packet signatures. As an example, network packet metadata may establish data packet classification and/or filtering rules. Such data packet classification may enable a determination of whether a network packet associated with a network packet signature is legitimate. Classification and/or filtering rules may determine how data packets should be handled and/or what services should be performed. For example, filtering rules can be used to test network packets entering the data center's network from external computing devices to ensure that attempts to enter the data center's network can be blocked. Alternative filtering rules can also be used to transmit traffic based on priority. The network packets from the first host can be transmitted even though the network packets from the second host may be dropped because the network packets from the first host have higher priority. In some embodiments, network packet metadata may also be referred to as a network packet profile tag. In some implementations, network packet metadata may also be referred to as a network packet label (or label). Variations on what the network packet metadata may contain will become apparent to those skilled in the art and should not be construed as limiting.
在某些实例中,将网络分组签名与网络分组元数据相关联的数据结构可以被实现为树结构。树结构可以包括非叶节点和叶节点。非叶节点和叶节点可以包括网络分组元数据(例如,标签)。从树结构的根延伸到树结构的叶(同时穿过一个或更多个非叶节点)的路径可以定义前缀。可以通过将网络分组签名与来自树结构的一个或更多个前缀进行比较来执行对网络分组的过滤和/或分类。然后,可以将与对应于网络分组签名的最长前缀相关联的网络分组元数据确定为要与网络分组数据签名相关联。In some instances, the data structure associating network packet signatures with network packet metadata may be implemented as a tree structure. The tree structure can include non-leaf nodes and leaf nodes. Non-leaf nodes and leaf nodes may include network packet metadata (eg, labels). A path extending from the root of the tree structure to the leaves of the tree structure (while traversing one or more non-leaf nodes) may define a prefix. Filtering and/or sorting of network packets may be performed by comparing the network packet signatures to one or more prefixes from the tree structure. Then, the network packet metadata associated with the longest prefix corresponding to the network packet signature may be determined to be associated with the network packet data signature.
在某些方法下,树结构是二叉树,其中逐个测试网络分组签名的每个比特(例如,IP地址的每个比特)。在这样的朴素方法下,可能需要最多32个步骤来过滤和/或分类IPv4地址(即,32位的地址),并且可能需要最多128个步骤来过滤和/或分类IPv6地址(即,128位的地址)。每个步骤均需要存储器访问,从而实现最大过滤和/或分类借记(debit)。结果是,需要压缩树结构以减少所需的存储器访问次数。Under certain approaches, the tree structure is a binary tree, where each bit of the network packet signature (eg, each bit of an IP address) is tested one by one. Under such a naive approach, up to 32 steps may be required to filter and/or classify IPv4 addresses (ie, 32-bit addresses), and up to 128 steps may be required to filter and/or classify IPv6 addresses (ie, 128-bit addresses) the address of). Each step requires memory access, enabling maximum filtering and/or sorting debits. As a result, the tree structure needs to be compressed to reduce the number of memory accesses required.
在一个方面,本技术的各种实现方式提供了一种分析网络分组以用于通过过滤非法网络分组同时准许合法网络分组访问网络来防止对网络的攻击的方法,过滤基于网络地址与数据分组分类之间的关联,该关联被实现为树结构,数据分组分类使得能够确定网络分组是否合法,该方法由计算设备执行,该方法包括:In one aspect, various implementations of the present technology provide a method of analyzing network packets for preventing attacks on a network by filtering illegal network packets while granting legitimate network packets access to the network, filtering based on network address and data packet classification The association is implemented as a tree structure, the data packet classification enables to determine whether the network packet is legitimate, the method is performed by the computing device, and the method includes:
压缩将网络地址与数据分组分类相关联的树结构,树结构包括包含数据分组分类的多个叶节点和单比特测试节点的多个非叶节点,压缩的步骤包括:Compressing a tree structure that associates network addresses with data packet classification, the tree structure includes a plurality of leaf nodes of the data packet classification and a plurality of non-leaf nodes of a single-bit test node, and the step of compressing includes:
基于具有单个子节点的连续非叶节点的数量和压缩阈值,确定是否要压缩树结构的包括具有单个子节点的连续非叶节点的子部分;determining, based on the number of consecutive non-leaf nodes with a single child node and a compression threshold, whether to compress a sub-portion of the tree structure that includes consecutive non-leaf nodes with a single child node;
如果做出要压缩树结构的子部分的确定,则:If a determination is made to compress subsections of the tree structure, then:
生成树结构的经压缩子部分,树结构的经压缩子部分包括由与树结构的子部分的连续非叶节点中的每一个相关联的单比特的级联形成的比特序列,该序列的比特数等于或大于压缩阈值;以及Spanning a compressed subsection of a tree structure comprising a sequence of bits formed by a concatenation of single bits associated with each of the consecutive non-leaf nodes of the subsection of the tree structure, the bits of the sequence is equal to or greater than the compression threshold; and
将树结构的经压缩子部分存储在非暂态计算机可读存储器中。The compressed sub-portions of the tree structure are stored in non-transitory computer readable memory.
在一个方面,本技术的各种实现方式提供了一种压缩将网络分组签名与网络分组元数据相关联的树结构的方法,该树结构包括包含网络分组元数据的多个叶节点和单比特测试节点的多个非叶节点,该方法包括:In one aspect, various implementations of the present technology provide a method of compressing a tree structure associating a network packet signature with network packet metadata, the tree structure including a plurality of leaf nodes and a single bit containing network packet metadata Test multiple non-leaf nodes of a node, the method includes:
对于树结构的子部分,确立具有单个子节点的连续非叶节点的数量;For subsections of the tree structure, establish the number of consecutive non-leaf nodes with a single child node;
基于具有单个子节点的连续非叶节点的数量和压缩阈值,确定是否要压缩树结构的子部分;based on the number of consecutive non-leaf nodes with a single child node and a compression threshold, determine whether to compress subsections of the tree structure;
如果做出要压缩树结构的子部分的确定,则:If a determination is made to compress subsections of the tree structure, then:
生成经压缩的节点数据结构,经压缩的节点数据结构包括树结构的子部分的路径,该路径包括由与树结构的子部分的连续非叶节点中的每一个相关联的单比特的级联形成的比特序列,该序列的比特数等于或大于压缩阈值;以及generating a compressed node data structure that includes a path of subsections of the tree structure including a concatenation of single bits associated with each of the consecutive non-leaf nodes of the subsection of the tree structure a sequence of bits formed, the number of bits in the sequence being equal to or greater than the compression threshold; and
将经压缩的节点数据结构存储在非暂态计算机可读存储器中。The compressed node data structures are stored in non-transitory computer readable memory.
在一些实施方式中,经压缩的节点数据结构的序列的比特数通过(1)具有子叶节点的连续非叶节点之一的存在、(2)具有多于一个子节点的连续非叶节点之一的存在或者(3)该序列的预定义最大大小来确定。In some embodiments, the number of bits of the sequence of the compressed node data structure is determined by the presence of (1) one of the consecutive non-leaf nodes having a cotyledon node, (2) one of the consecutive non-leaf nodes having more than one child node is determined by the presence of or (3) the predefined maximum size of the sequence.
在一些实施方式中,如果做出不压缩树结构的子部分的确定,则:In some embodiments, if a determination is made not to compress a subsection of the tree structure, then:
生成非压缩的节点数据结构,非压缩的节点数据结构包括树结构的子部分的路径,该路径包括由与树结构的子部分的至少一个非叶节点相关联的一个或更多个单比特的级联形成的比特序列,所述至少一个非叶节点具有多于一个子节点,该序列的比特数小于压缩阈值;以及Generating an uncompressed node data structure that includes a path to a subsection of the tree structure, the path including a path consisting of one or more single-bit nodes associated with at least one non-leaf node of the subsection of the tree structure a bit sequence formed by concatenation, the at least one non-leaf node has more than one child node, and the number of bits of the sequence is less than the compression threshold; and
将非压缩的节点数据结构存储在非暂态计算机可读存储器中。The uncompressed node data structures are stored in non-transitory computer readable memory.
在一些实施方式中,压缩阈值是5比特。在一些实施方式中,序列的预定义最大大小是30比特。In some embodiments, the compression threshold is 5 bits. In some embodiments, the predefined maximum size of the sequence is 30 bits.
在一些实施方式中,非暂态计算机可读存储器包括第一非暂态计算机可读存储器和第二非暂态计算机可读存储器。在一些实施方式中,(1)经压缩的节点数据结构是第一经压缩的节点数据结构,并且(2)非压缩的节点数据结构是第一非压缩的节点数据结构,其中,第一节点数据结构包括第一经压缩的节点数据结构和第一非压缩的节点数据结构之一,并且第二节点数据结构包括第二经压缩的节点数据结构和第二非压缩的数据结构之一。In some implementations, the non-transitory computer-readable memory includes a first non-transitory computer-readable memory and a second non-transitory computer-readable memory. In some embodiments, (1) the compressed node data structure is a first compressed node data structure, and (2) the uncompressed node data structure is a first uncompressed node data structure, wherein the first node The data structure includes one of a first compressed node data structure and a first uncompressed node data structure, and the second node data structure includes one of a second compressed node data structure and a second uncompressed data structure.
在一些实施方式中,第一节点数据结构存储在第一非暂态计算机可读存储器中,并指向第二非暂态计算机可读存储器的存储有第二节点数据结构的存储器地址。In some embodiments, the first node data structure is stored in the first non-transitory computer readable memory and points to a memory address of the second non-transitory computer readable memory where the second node data structure is stored.
在一些实施方式中,可以通过第一单次存储器访问从第一非暂态计算机可读存储器访问第一节点数据结构,并且可以通过第二单次存储器访问从第二非暂态计算机可读存储器访问第二节点数据结构。In some embodiments, the first node data structure can be accessed from the first non-transitory computer readable memory through a first single memory access, and the first node data structure can be accessed from the second non-transitory computer readable memory through a second single memory access Access the second node data structure.
在一些实施方式中,第一非暂态计算机可读存储器是第一QDR SRAM存储器的第一存储体,并且第二非暂态计算机可读存储器是第二QDR SRAM存储器的第二存储体。In some embodiments, the first non-transitory computer readable memory is a first bank of a first QDR SRAM memory and the second non-transitory computer readable memory is a second bank of a second QDR SRAM memory.
在一些实施方式中,经压缩的节点数据结构是第一经压缩的节点数据结构,并且非压缩的节点数据结构是第一非压缩的节点数据结构,并且其中,非暂态计算机可读存储器包括第一部分、第二部分和第三部分,第一部分存储第一经压缩的节点数据结构和第一非压缩的节点数据结构之一,第一经压缩的节点数据结构和第一非压缩的节点数据结构之一指向存储在第二部分中的第二经压缩的节点数据结构和第二非压缩的节点数据结构之一,并且其中:In some implementations, the compressed node data structure is a first compressed node data structure, and the uncompressed node data structure is a first uncompressed node data structure, and wherein the non-transitory computer-readable memory includes The first part, the second part and the third part, the first part stores one of the first compressed node data structure and the first uncompressed node data structure, the first compressed node data structure and the first uncompressed node data one of the structures points to one of the second compressed node data structure and the second uncompressed node data structure stored in the second portion, and wherein:
在更新树结构时,将第三经压缩的节点数据结构和第三非压缩的节点数据结构之一存储在第三部分中,并且修改第一经压缩的节点数据结构和第一非压缩的节点数据结构之一,使得第一经压缩的节点数据结构和第一非压缩的节点数据结构之一指向第三经压缩的节点数据结构和第三非压缩的节点数据结构之一。When updating the tree structure, one of the third compressed node data structure and the third uncompressed node data structure is stored in the third portion, and the first compressed node data structure and the first uncompressed node are modified One of the data structures such that one of the first compressed node data structure and the first uncompressed node data structure points to one of the third compressed node data structure and the third uncompressed node data structure.
在一些实施方式中,该方法还包括至少一个操作:(1)基于通过网络分组元数据建立的优先级来传输网络分组,(2)基于网络分组元数据识别要对网络分组执行的服务,(3)基于网络分组元数据测试网络分组以确立网络分组是网络攻击的一部分和/或(4)基于网络分组元数据创建对网络分组的流量的度量。In some embodiments, the method further comprises at least one operation of: (1) transmitting the network packet based on a priority established by the network packet metadata, (2) identifying a service to be performed on the network packet based on the network packet metadata, ( 3) Test the network packet based on the network packet metadata to establish that the network packet is part of a network attack and/or (4) create a measure of the traffic of the network packet based on the network packet metadata.
在另一方面,本技术的各种实现方式提供了一种被配置成执行以上段落中描述的方法的计算机实现的系统。In another aspect, various implementations of the present technology provide a computer-implemented system configured to perform the method described in the preceding paragraphs.
在另一方面,本技术的各种实现方式提供了一种包括计算机可执行指令的非暂态计算机可读介质,所述计算机可执行指令使系统执行以上段落中描述的方法。In another aspect, various implementations of the present technology provide a non-transitory computer-readable medium comprising computer-executable instructions that cause a system to perform the method described in the preceding paragraphs.
在本说明书的上下文中,除非另有明确规定,否则联网设备可以指代但不限于“路由器”、“交换机”、“网关”、“系统”、“基于计算机的系统”和/或其适合当前相关任务的任何组合。In the context of this specification, unless expressly stated otherwise, networked devices may refer to, but are not limited to, "routers," "switches," "gateways," "systems," "computer-based systems," and/or their appropriate Any combination of related tasks.
在本说明书的上下文中,除非另有明确规定,否则表述“计算机可读介质”和“存储器”旨在包括任何性质和种类的介质,其非限制性示例包括RAM、ROM、盘(CD-ROM、DVD、软盘、硬盘驱动器等)、USB密钥、闪存卡、固态驱动器和磁带驱动器。仍然在本说明书的上下文中,“一种”计算机可读介质和“该”计算机可读介质不应被解释为是同一计算机可读介质。与此相对,在任何合适的时候,“一种”计算机可读介质和“该”计算机可读介质也可以被解释为第一计算机可读介质和第二计算机可读介质。In the context of this specification, unless expressly stated otherwise, the expressions "computer-readable medium" and "memory" are intended to include media of any nature and kind, non-limiting examples of which include RAM, ROM, disk (CD-ROM) , DVDs, floppy disks, hard drives, etc.), USB keys, flash memory cards, solid state drives, and tape drives. Still in the context of this specification, "a" computer-readable medium and "the" computer-readable medium should not be construed as being the same computer-readable medium. In contrast, "a" computer-readable medium and "the" computer-readable medium can also be construed as a first computer-readable medium and a second computer-readable medium, whenever appropriate.
在本说明书的上下文中,除非另有明确规定,否则词语“第一”、“第二”、“第三”等被用作形容词,仅为了使得能够将其修饰的名词彼此区分的目的,而不是为了描述这些名词之间的任何特定关系的目的。In the context of this specification, unless expressly stated otherwise, the words "first", "second", "third", etc. are used as adjectives only for the purpose of enabling the nouns they modify to be distinguished from each other, and Not for the purpose of describing any particular relationship between these nouns.
本技术的实现方式各自具有上述目的和/或方面中的至少一者,但不一定具有所有这些目的和/或方面。应当理解,由于试图获得上述目的而产生的本技术的一些方面可能不满足该目的和/或可能满足本文未具体叙述的其他目的。Implementations of the present technology each have at least one, but not necessarily all, of the objects and/or aspects described above. It should be appreciated that some aspects of the technology resulting from an attempt to achieve the above-mentioned objective may not satisfy this objective and/or may satisfy other objectives not specifically recited herein.
根据以下描述、附图和所附权利要求书,本技术的实现方式的附加和/或替选特征、方面和优势将变得明显。Additional and/or alternative features, aspects and advantages of implementations of the present technology will become apparent from the following description, drawings, and appended claims.
附图说明Description of drawings
参考以下描述、权利要求书和附图,将更好地理解本公开内容的这些和其他特征、方面和优点。本公开内容通过示例的方式示出,并且不受附图的限制,在附图中相似的附图标记表示相似的元件。These and other features, aspects and advantages of the present disclosure will be better understood with reference to the following description, claims and drawings. The present disclosure is shown by way of example and not by way of limitation in the accompanying drawings, in which like reference numerals refer to like elements.
图1A和图1B示出了可以用于实现本文描述的任何方法的示例联网设备;1A and 1B illustrate example networked devices that can be used to implement any of the methods described herein;
图2示出了根据本技术的实施方式的联网设备及其联网环境的图;Figure 2 shows a diagram of a networked device and its networked environment in accordance with an embodiment of the present technology;
图3示出了根据本技术的实施方式的替选联网设备及其联网环境的图;3 shows a diagram of an alternative networked device and its networked environment in accordance with an embodiment of the present technology;
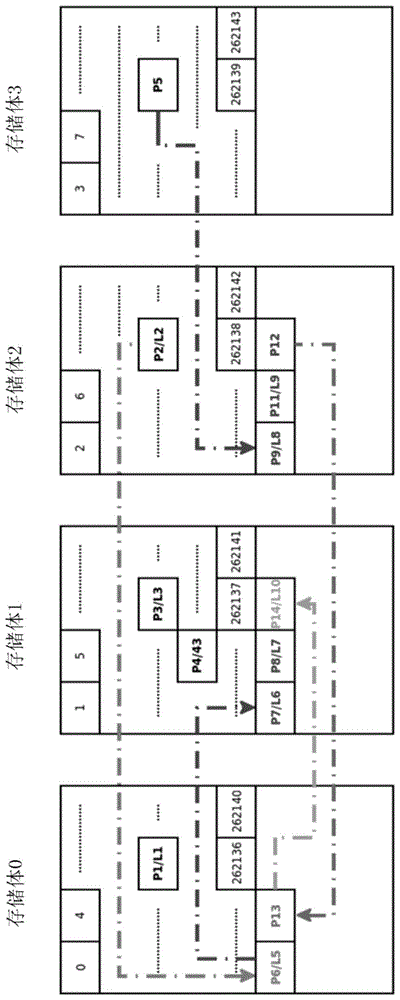
图4至图7示出了根据本技术的实施方式的树结构的图;4 to 7 illustrate diagrams of tree structures according to embodiments of the present technology;
图8示出了根据本技术的实施方式的节点数据结构的图;8 shows a diagram of a node data structure according to an embodiment of the present technology;
图9示出了根据本技术的实施方式的存储在存储器的多个存储体中的数据结构的图;以及FIG. 9 shows a diagram of a data structure stored in multiple banks of a memory in accordance with an embodiment of the present technology; and
图10示出了根据本技术的实施方式的压缩树结构的方法的第一流程图。FIG. 10 shows a first flowchart of a method of compressing a tree structure according to an embodiment of the present technology.
具体实施方式Detailed ways
在以下对各个说明性实施方式的描述中,参考附图,附图构成其一部分,并且在附图中通过图示的方式示出了可以实践本公开内容的各方面的各种实施方式。应当理解,在不脱离本公开内容的范围的情况下,可以利用其他实施方式并且可以进行结构或功能上的改变。In the following description of various illustrative embodiments, reference is made to the accompanying drawings, which form a part hereof, and in which are shown by way of illustration various embodiments in which aspects of the present disclosure may be practiced. It is to be understood that other embodiments may be utilized and structural or functional changes may be made without departing from the scope of the present disclosure.
设备的网络例如容纳在数据中心中的网络可以包括各种不同的联网硬件,例如路由器、交换机、多层交换机、线缆和/或其他联网硬件。联网设备可以服务各种计算设备,例如服务器。联网设备可以在过滤和/或分类网络分组的情况下操作所依赖的数据结构。A network of devices, such as a network housed in a data center, may include a variety of different networking hardware, such as routers, switches, multilayer switches, cables, and/or other networking hardware. Networked devices can serve various computing devices, such as servers. Networked devices may operate upon data structures that filter and/or classify network packets.
图1A示出了根据本技术的实施方式的计算环境100的图。在一些实施方式中,计算环境100可以由传统的个人计算机、服务器、路由器、交换机、控制器和/或电子设备(例如,服务器、控制器单元、控制设备、监视设备等)中的任一个和/或其适合于当前相关任务的任何组合来实现。在一些实施方式中,计算环境100包括各种硬件部件,各种硬件部件包括由处理器110共同表示的一个或更多个单核或多核处理器、固态驱动器120、随机存取存储器(RAM)存储器130、专用存储器170和输入/输出接口150。计算环境100可以是专门设计用于在数据中心环境中操作的计算机。计算环境100可以是通用计算机系统。FIG. 1A shows a diagram of a
在一些实施方式中,计算环境100还可以是上面列出的系统之一的子系统。在一些其他实施方式中,计算环境100可以是“现成的”通用计算机系统。在一些实施方式中,计算环境100还可以分布在多个系统中。计算环境100还可以专门用于实现本技术。如本技术领域的技术人员可以理解的,可以在不脱离本技术的范围的情况下设想关于如何实现计算环境100的多种变型。In some implementations,
计算环境100的各个部件之间的通信可以通过与各个硬件部件电耦接的一个或更多个内部和/或外部总线160(例如,PCI总线、通用串行总线、IEEE 1394“火线(Firewire)”总线、SCSI总线、串行ATA总线、ARINC总线等)实现。Communication between the various components of
输入/输出接口150可以提供诸如有线或无线访问的联网能力。作为示例,输入/输出接口150可以包括联网接口,例如但不限于一个或更多个网络端口、一个或更多个网络套接字、一个或更多个网络接口控制器等。可以如何实现联网接口的多个示例对于本技术领域的技术人员而言将变得明显。例如但不限于此,联网接口可以实现特定物理层和数据链路层标准,例如以太网、光纤通道、Wi-Fi或令牌环。特定物理层和数据链路层可以为完整网络协议栈提供基础,从而使得能够在同一局域网(LAN)上的计算机小组之间进行通信并通过可路由协议例如因特网协议(IP)进行大规模网络通信。Input/
根据本技术的实现方式,固态驱动器120存储适于被加载到随机存取存储器130中并且由处理器110执行的程序指令。例如,程序指令可以是库或应用的一部分。尽管被示为固态驱动器120,但是可以使用任何类型的存储器例如硬盘、光盘和/或可移除存储介质来代替固态驱动器120。According to implementations of the present technology,
在本技术的一些实施方式中,处理器110可以是通用处理器例如中央处理单元(CPU),或者专用于特定目的的处理器例如数字信号处理器(DSP)。在一些实施方式中,处理器110还可以依赖于专用于某些给定任务例如执行以下段落中阐述的方法1000的加速器112。在一些实施方式中,处理器110或加速器112可以被实现为一个或更多个现场可编程门阵列(FPGA)。此外,术语“处理器”的明确使用不应被解释为排外地提及能够执行软件的硬件,并且可以隐含地包括但不限于专用集成电路(ASIC)、用于存储软件的只读存储器(ROM)、随机存取存储器(RAM)和非易失性存储装置。还可以包括传统的和/或定制的其他硬件。In some embodiments of the present technology, the
在本技术的一些实施方式中,RAM 130可以包括高性能存储器,例如但不限于四倍数据速率(QDR)SRAM存储器。在一些实施方式中,RAM 130可以包括多个QDR SRAM存储器。另外,在一些实施方式中,还可以依赖于专用存储器170。这样的专用存储器170可以是不同的存储器单元或集成到另一部件。在一些实施方式中,专用存储器170是FPGA处理单元的一部分(例如,FPGA的寄存器)。在一些实施方式中,专用存储器170被实现为RAM 130的专用部分。还可以在不脱离本技术的范围的情况下设想其他变型。In some embodiments of the present technology,
图1B示出了根据本技术的实施方式的替选计算环境190的图。在一些实施方式中,计算环境190与计算环境100可以由相似的部件来实现(相似的部件由相同的附图标记指代)。计算环境190包括专用FPGA卡180,专用FPGA卡180可以通过输入/输出接口150或者直接通过内部和/或外部总线160连接至计算环境的其他部件。在一些实施方式中,FPGA卡180包括FPGA芯片组182(其可以包括也被称为“专用存储器”的寄存器)和专用RAM存储器,例如统称为QDR SRAM存储器184的四个不同的QDR SRAM存储器。在一些实施方式中,FPGA卡也可以包括实现至网络的连接的一个或更多个输入/输出接口。FIG. 1B shows a diagram of an
在本文中可以将软件模块或仅仅暗示是软件的模块表示为流程图元素或指示处理步骤的执行和/或文本描述的其他元素的任何组合。这样的模块可以由明确地或隐含地示出的硬件来执行。此外,应该理解,模块可以包括例如但不限于提供所需能力的计算机程序逻辑、计算机程序指令、软件、堆栈、固件、硬件电路或其组合。Software modules, or modules merely implied to be software, may be represented herein as any combination of flowchart elements or other elements that indicate the execution of process steps and/or textual descriptions. Such modules may be executed by hardware shown explicitly or implicitly. Furthermore, it should be understood that a module may include, for example, but not limited to, computer program logic, computer program instructions, software, stacks, firmware, hardware circuits, or combinations thereof, to provide the desired capabilities.
图2示出了根据本技术的实施方式的联网设备及其联网环境的图。网络10和20可以连接至因特网。网络10和/或20可以定义与数据中心相关联、由数据中心控制和操作的网络。每个网络10和20可以分别包括主机12、14和16以及22和24。每个网络10和20还可以分别包括交换机18和26,并且可以分别包括一个或更多个服务器,例如服务器17、19和28。每个网络10和20还可以分别包括至因特网30的一个或更多个网关13和25。未明确示出的是网络10和20的路由器和其他部分,路由器和其他部分还可以控制通过网络10和20的流量并且将被认为总体上分别由交换机18和26以及网络10和20固有地描绘。交换机18和26、网关13和25以及路由器通常可以被称为如下设备的网络,该设备可以被实施为类似于计算环境100的计算设备。交换机18和26、网关13和25以及路由器可以实现根据本技术的实施方式的将网络分组签名与网络分组元数据相关联的树结构。2 shows a diagram of a networked device and its networked environment in accordance with an embodiment of the present technology.
图3示出了根据本技术的实施方式的替选联网设备及其联网环境的图。所描绘的环境是操作连接至因特网30的数据中心300的基础设施。数据中心300包括第一组路由器301和第二组路由器302。第一组路由器301可以被称为管理由数据中心300操作的多个不同网络的骨干路由器。第二组路由器302可以被称为各自均管理由数据中心300操作的多个服务器303的网络连接的数据中心路由器。数据中心300还包括还被称为真空系统VAC的防DDoS系统304。在一些实施方式中,防DDoS系统304可以连接至第一组路由器301和/或第二组路由器304,以过滤从因特网30接收的网络分组。在一些实施方式中,防DDoS系统304实现缓解措施,缓解措施包括过滤非法网络分组同时准许合法网络分组访问数据中心的网络(例如,访问服务器303)。在一些实施方式中,防DDoS系统304可以包括可以专用于某些给定任务的多个子系统例如子系统305至308。3 shows a diagram of an alternative networking device and its networking environment in accordance with an embodiment of the present technology. The depicted environment is the infrastructure that operates the
作为示例但不限于此,也被称为预防火墙的第一子系统305可以操作如下控制逻辑:该控制逻辑旨在对网络分组进行分段、控制网络分组的大小,和/或对基于关联协议(例如,TCP、UDP、ICMP、GRE协议)的某些网络分组进行授权同时阻止其他网络分组(例如,除TCP、UDP、ICMP、GRE协议之外的协议)。作为另一示例但不限于此,也被称为防火墙网络的第二子系统306可以操作如下控制逻辑:该控制逻辑旨在授权/阻止IP地址、授权/阻止协议(例如,IP、TCP、UDP、ICMP、GRE协议)、授权/阻止一个或更多个网络端口(例如,TCP或UDP端口)、授权/阻止SYN/TCP、授权/阻止除SYN/TCP之外的网络分组。作为另一示例但不限于此,也被称为盾牌(Shield)的第三子系统307可以操作旨在分析网络分组(例如,以检查报头、校验和等)的控制逻辑。作为另一示例但不限于此,也被称为盔甲(Armor)的第四子系统308可以操作如下控制逻辑:该控制逻辑旨在分析网络分组和/或进行对无效TCP标记、无效序列号、僵尸网络分组、TCP SYN认证、DNS认证、DNS限制等的检测。By way of example and not limitation, the
在一些实施方式中,第四子系统308生成和/或实现根据本技术的实施方式的将网络分组签名与网络分组元数据相关联的树结构。如可以理解的,树结构可以同等地在不同的联网设备上生成和/或实现,或者甚至以分布式方式在多个联网设备上进行操作(例如,通过子系统305至308中的一个或更多个实现)。在一些实施方式中,根据本技术的实施方式的生成和/或实现将网络分组签名与网络分组元数据相关联的树结构的联网设备可以包括包含FPGA卡的一个或更多个虚拟路由器(vRouter)。适于联网设备的配置的示例可以是但不限于如下:In some embodiments, the
也可以使用其他配置,并且对于本技术领域的技术人员来说其他配置将易于变得明显。Other configurations may also be used and will be readily apparent to those skilled in the art.
现在转到图4至图7,示出了根据本技术的实施方式的树结构400的图。树结构包括子部分402、502、504、602、604和700。树结构的级数和/或子部分的数量是示例性的,并且不应被解释为对本技术的限制。树结构包括非叶节点(例如,P2/L2、P5、P6/L5)和叶节点(例如,P1/L1、P3/L3、P4/L4)。在一些实施方式中,例如图4至图9中所描绘的实施方式,非叶节点可以与网络分组元数据(例如,标签)相关联。作为示例,非叶节点P6/L5与标签“5”相关联。Turning now to FIGS. 4-7 , diagrams of a
每个非叶节点是使得能够指导对整个树结构的浏览的单比特测试节点。非叶节点可以与一个子节点或两个子节点相关联。在非叶节点与两个子节点相关联的实例中,比特值可以确定在树结构的下一级处应该考虑两个子节点中的哪一个。作为示例,如果测试的比特值是1,则非叶节点P10可以指向P12/L8,并且如果测试的比特值是0,则非叶节点P10可以指向P11/L9。在一些实施方式中,即使非叶节点仅有一个子节点,也要测试比特值。在一些实施方式中,比特值的存在确定遍历整个树结构的查找是否应该继续。Each non-leaf node is a single-bit test node that enables direct browsing of the entire tree structure. A non-leaf node can be associated with one child node or two child nodes. In the instance where a non-leaf node is associated with two child nodes, the bit value may determine which of the two child nodes should be considered at the next level in the tree structure. As an example, if the tested bit value is 1, non-leaf node P10 may point to P12/L8, and if the tested bit value is 0, non-leaf node P10 may point to P11/L9. In some implementations, the bit value is tested even if the non-leaf node has only one child node. In some implementations, the presence of a bit value determines whether a lookup traversing the entire tree structure should continue.
每个叶节点与网络分组元数据(例如,标签)相关联,例如,叶节点P3/L3、P1/L1、P11/19。在从根(例如,根P0/L0)浏览整个树结构时,到达叶节点致使浏览结束并且确定网络分组签名可以与叶节点的元数据相关联。在叶节点与标签相关联的一些实施方式中,所选标签是最后匹配节点之一,从而避免必须为每个可能的终止生成一个叶。Each leaf node is associated with network packet metadata (eg, a label), eg, leaf nodes P3/L3, P1/L1, P11/19. When browsing the entire tree structure from a root (eg, root P0/L0), reaching a leaf node causes the browsing to end and determines that a network packet signature can be associated with the leaf node's metadata. In some embodiments where leaf nodes are associated with labels, the selected label is one of the last matching nodes, thereby avoiding having to generate a leaf for every possible termination.
作为示例,遍历树结构400的从根P0/L0至叶节点P3/L3的路径包括具有单个子非叶节点412的非叶节点410,子非叶节点412又作为两个子非叶节点414和416。非叶节点414具有两个子节点,即非叶节点418和叶节点P3/L3。遍历树结构400的从根P0/L0至叶节点P3/L3的路径可以由以下比特序列“0011”定义。作为另一示例,遍历树结构400的从根P0/L0至叶节点P2/L2的路径可以由以下比特序列“00100”来定义。As an example, a path traversing
如图4至图7所示,非叶节点P5通向子部分502,子部分502本身通向非叶节点P12/L8和叶节点P11/L9。非叶节点P2/L2通向子部分504,子部分504本身通向非叶节点P6/L5。非叶节点P12/L8通向子部分602,子部分602本身通向非叶节点P13/L8。非叶节点P13/L8通向子部分604,子部分604本身通向叶节点P14/L10。非叶节点P6/L5通向子部分700,子部分700本身通向叶节点P7/L6和叶节点P9/L7。As shown in Figures 4-7, non-leaf node P5 leads to
在多个方面中,本技术提供了压缩树结构例如树结构400的方法。压缩树结构的方法针对树结构的给定子部分确立具有单个子节点的连续非叶节点的数量。在一些实施方式中,具有单个子节点的非叶节点可以被称为不具有分叉的非叶节点,换句话说,它仅具有一个分支。作为示例,如子部分402、502、504、602、604和700所示,子部分可以由树结构的级数定义。子部分可以是单个分支或定义子树结构的分支的组合。在实施方式中,级数可以由比特数来定义。在一些实施方式中,级数可以被定义为非叶节点和/或叶节点的数量。作为示例,子部分可以被定义为树结构的30级(即,30比特)。在不脱离本技术的范围的情况下可以设想变型,作为示例,级数可以多于或少于30并且可以取决于某些约束(例如,存储器结构)。In various aspects, the present technology provides a method of compressing a tree structure, such as
在一些实施方式中,压缩树结构的方法确定是否要压缩树结构的子部分。在一些实施方式中,该确定基于具有单个子节点的连续非叶节点的数量。在一些实施方式中,压缩阈值可以是6比特,使得将包括多于5个具有单个子节点的连续非叶节点的子部分确定为要被压缩。在不脱离本技术的范围的情况下可以设想变型,作为示例,压缩阈值可以大于或小于5并且可以取决于某些约束(例如,存储器结构)。作为示例,子部分402包括多个非叶节点和多个叶节点,然而,子部分402不包括至少5个仅具有一个子节点的连续非叶节点(例如,非叶节点412和414各自均具有两个子节点)。结果是,该子部分被确定为不被压缩。作为另一示例,子部分504包括10个仅具有一个子节点的连续非叶节点(即,0011111100),则可以做出可以压缩子部分504的确定。In some embodiments, the method of compressing the tree structure determines whether to compress sub-portions of the tree structure. In some embodiments, the determination is based on the number of consecutive non-leaf nodes that have a single child node. In some embodiments, the compression threshold may be 6 bits, such that subsections comprising more than 5 consecutive non-leaf nodes with a single subnode are determined to be compressed. Variations are envisaged without departing from the scope of the present technology, as an example, the compression threshold may be greater or less than 5 and may depend on certain constraints (eg, memory structure). As an example,
遵循类似的逻辑,可以做出如下确定:将不压缩子部分502,将压缩子部分602(尽管未示出,但子部分602包括32个仅具有一个子节点的连续非叶节点),将不压缩子部分604(仅有3个仅具有一个子节点的非叶节点)和子部分700(一个非叶节点具有两个子节点)。在一些实施方式中,可以定义仅具有一个子节点的连续非叶节点的序列的最大大小。在上述示例中,序列的最大大小是30(例如,30比特)。结果是,即使组合在一起的子部分602和604将产生35个仅具有一个子节点的连续非叶节点,但是子部分602在30处被切断,从而使子部分604不被压缩(因为子部分604只包括5个非叶节点)。如本技术领域的技术人员可以理解,在不脱离本技术的范围的情况下,可以设想压缩阈值和/或序列的最大大小的多种变型。Following similar logic, a determination can be made that
如果该方法确定要压缩所确定的树结构的给定子部分,则生成经压缩的节点数据结构。如果该方法确定不压缩所确定的树结构的给定子部分,则生成非压缩的节点数据结构。If the method determines that a given subsection of the determined tree structure is to be compressed, a compressed node data structure is generated. If the method determines not to compress a given subsection of the determined tree structure, an uncompressed node data structure is generated.
在图8中示出了节点数据结构800的示例,节点数据结构800示出了包括公共数据结构部分802、804和806的经压缩的节点数据结构810的示例和非压缩的数据结构820的示例。节点数据结构800的总大小为72比特。在一些实施方式中,72比特是存储有节点数据结构800的存储器单元的宽度。节点数据结构800包括第一块802“压缩”,第一块802“压缩”包括指示是否压缩节点数据结构800的1个比特。节点数据结构800还包括第二块804“标签”,第二块804“标签”包括在节点数据结构800表示叶节点的情况下可以指示要与网络分组签名相关联的标签值(也被称为网络分组元数据)的16比特。节点数据结构800还包括第三块806“指向下一节点的指针”,第三块806“指向下一节点的指针”包括指示与节点数据结构800相关联(例如,父节点-子节点关联)的另一节点数据结构的存储器地址的20比特。An example of a
对于节点数据结构包含经压缩的节点数据结构810的实例,节点数据结构还包括第四块812“分支长度”,第四块812“分支长度”包括指示仅具有一个子节点的连续非叶节点的数量的5比特。在一些实施方式中,连续非叶节点的最大数量是30。节点数据结构还包括第五块814“分支路径”,第五块814“分支路径”包括指示从当前节点到达下一节点要遵循的路径的30比特。在一些实施方式中,路径包括由与树结构的经压缩子部分的连续非叶节点中的每一个相关联的单比特的级联形成的比特序列(例如,“10111100001000001”)。在一些实施方式中,压缩阈值是5,意味着序列的比特数等于或大于6。如果比特数等于或小于5,则生成非压缩的节点数据结构。在一些其他实施方式中,压缩阈值是3,意味着序列的比特数等于或大于4。如果比特数等于或小于3,则生成非压缩的节点数据结构。因此,可以在不脱离本技术的范围的情况下设想压缩阈值的多个值。For the instance in which the node data structure contains the compressed
在一些实施方式中,经压缩的节点数据结构的序列的比特数通过具有子叶节点的非叶节点的存在来确定(例如,树结构在子叶节点处结束)。在一些实施方式中,经压缩的节点数据结构的序列的比特数通过具有多于一个子节点(例如,两个子节点)的非叶节点的存在来确定,从而识别需要创建附加节点数据结构(其可以是经压缩的或非压缩的)的树结构中的分叉。在一些实施方式中,经压缩的节点数据结构的序列的比特数是序列的预定义最大大小(例如,30,以满足节点数据结构的格式约束)。In some implementations, the number of bits of the sequence of the compressed node data structure is determined by the presence of non-leaf nodes with cotyledon nodes (eg, the tree structure ends at the cotyledon nodes). In some embodiments, the number of bits of the sequence of compressed node data structures is determined by the presence of non-leaf nodes that have more than one child node (eg, two child nodes), thereby identifying the need to create additional node data structures (which can be compressed or uncompressed) forks in a tree structure. In some embodiments, the number of bits of the sequence of the compressed node data structure is a predefined maximum size of the sequence (eg, 30, to meet the format constraints of the node data structure).
对于节点数据结构包含非压缩的节点数据结构820的实例,节点数据结构还包括第六块822“填充比特”,第六块822“填充比特”包括在该配置中可能是无用比特的3比特(即,它们“填充”数据结构以使其具有恒定的大小例如72比特)。节点数据结构还包括第七块824“停止值”,第七块824“停止值”包括可以指示节点是非叶节点(例如,不是树的末端)还是叶节点(例如,树的末端)的32比特。在一些实施方式中,第七块824指示树结构的子部分的路径。该路径包括由与树结构的子部分的至少一个非叶节点相关联的一个或更多个单比特的级联形成的比特序列,所述至少一个非叶节点具有多于一个子节点,序列的比特数小于压缩阈值(例如,“1011”)。在一些实施方式中,压缩阈值是5,意味着序列的比特数不大于5。如果比特数大于5,则生成经压缩的节点数据结构。For the instance where the node data structure contains the uncompressed
在一些实施方式中,非压缩的节点可以检查5比特的签名,这意味着可能存在2^5个5比特的可能路径(00000,00001,00010,00011,00100,......)。对于每个可能的路径,可能存在一个“停止”比特:当且仅当路径00000对应于子节点时,比特0为零,否则为1。当且仅当路径00001对应于子节点时,比特1为零,否则为1。这产生32个比特值。每个比特对应于可能的路径和可能的子节点。在一些实施方式中,非压缩节点可以具有多达32个子节点。指针(806)可以指向第一个子节点,下一个子节点可以连续存储在存储器中(因此第一个子节点在806中的地址处,第二个子节点在地址+1处,第三个子节点在地址+2处......)。非压缩节点可以具有0到32个子节点。相比之下,在一些实施方式中,经压缩节点可以确切地具有一个子节点。非压缩节点可以支持多达32个5比特路径,并且经压缩节点可以仅支持一个30比特路径。In some embodiments, a non-compressed node can check a 5-bit signature, which means that there may be 2^5 possible paths of 5 bits (00000, 00001, 00010, 00011, 00100, ...). For each possible path, there may be a "stop" bit:
返回压缩树结构的方法,如果该方法确定要压缩树结构的给定子部分,则生成经压缩的节点数据结构(例如,经压缩的节点数据结构810)。如果该方法确定不压缩所确定的树结构的给定子部分,则生成非压缩的节点数据结构(例如,非压缩的节点数据结构820)。根据本技术,树结构400的子部分504可以由经压缩的节点数据结构P2/L2表示,经压缩的节点数据结构P2/L2包括由10比特序列“0011111100”定义的路径。Returning to a method of compressing a tree structure, if the method determines that a given subsection of the tree structure is to be compressed, a compressed node data structure (eg, compressed node data structure 810) is generated. If the method determines not to compress a given sub-portion of the determined tree structure, an uncompressed node data structure (eg, uncompressed node data structure 820) is generated. In accordance with the present technique,
现在转向图9,示出了包括四个存储器存储体(“存储体0”、“存储体1”、“存储体2”和“存储体3”)的非暂态计算机可读存储器的示例。在一些实施方式中,所有四个存储器是同一非暂态计算机可读存储器的一部分。在一些其他实施方式中,四个存储器中的每一个定义了不同的非暂态计算机可读存储器。在一些实施方式中,四个存储器存储体可以被称为第一非暂态计算机可读存储器、第二非暂态计算机可读存储器、第三非暂态计算机可读存储器和第四非暂态计算机可读存储器。在一些实施方式中,第一非暂态计算机可读存储器、第二非暂态计算机可读存储器、第三非暂态计算机可读存储器和第四非暂态计算机可读存储器中的每一个被实现为不同的QDR SRAM存储器。在这样的实施方式中,存储体0将与第一QDR SRAM存储器相关联,存储体1将与第二QDR SRAM存储器相关联,存储体2将与第三QDR SRAM存储器相关联,并且存储体3将与第四QDR SRAM存储器相关联。Turning now to FIG. 9, an example of a non-transitory computer readable memory including four memory banks ("
根据本技术的实施方式并结合图4至图7参照图8,对树结构400进行建模的多个节点数据结构跨存储体0、存储体1、存储体2和存储体3存储。多个节点数据结构包括经压缩的节点数据结构和非压缩的数据结构。存储多个节点数据结构的方法包括:将第一节点数据结构存储在存储体中的第一存储体中,将第二节点数据结构(第一节点数据结构指向其)存储到存储体中的第二存储体中,从而避免在浏览树结构的表示时,连续两次访问同一存储体。作为示例,经压缩的节点数据结构P2/L2存储在存储体2中并指向(例如,基于存储在经压缩的节点数据结构中的“指向地址”)存储在存储体0中的非压缩的节点数据结构P6/L5,非压缩的节点数据结构P6/L5本身指向都存储在存储体1中的非压缩的节点数据结构P7/L6和P8/L7(即,P7/L6和P8/L7存储在同一存储体中,因为它们表示与非叶节点P6/L5相关联的两个叶节点)。作为另一示例,存储在存储体3中的非压缩的节点数据结构P5指向存储在存储体2中的与存储在存储体2中的经压缩的数据结构P12相关联的非压缩的节点数据结构P9/L8和P11/L9,经压缩的数据结构P12指向存储在存储体0中的非压缩的节点数据结构P13,非压缩的节点数据结构P13又指向存储在存储体1中的非压缩的节点数据结构P14/L10。结果是,从一个节点至另一个节点,可以通过访问四个存储体中的不同存储体来实现对树结构的浏览。节点数据结构跨存储体的分布可以使得:对于要引入的每个新节点数据结构,所选存储体是已存储节点数据结构的数量最少的存储体。对于树结构的给定分支,在循环回到已使用的存储体之前需要使用所有存储体。结果是,在某些实施方式中,本技术可以使得能够优化对存储体的访问次数和存储体的使用。作为示例,将与IPv6地址相关联的网络分组签名与网络分组标签相关联并且包括根据本技术生成的经压缩的节点数据结构和非压缩的节点数据结构的树结构可能不需要不超过八个步骤来返回相关联的网络分组标签。结果是,相对于传统方法,本技术可以使得能够减少要使用的存储器量(这在使用诸如QDR SRAM的高性能存储器的情况下更加普遍的有益),同时改进了借记。8 in conjunction with FIGS. 4-7, a plurality of node data structures modeling
在一些实施方式中,每一个存储体被划分成三个部分。第一部分存储树的第一步骤的节点,第二部分存储树的后续步骤的节点,并且第三部分保持未使用。当需要更新树结构时,在存储体的第三部分中引入新的节点数据结构,然后更新存储在第一部分中的节点数据结构中包含的存储器地址,使得其现在指向存储在第三部分中的新创建的节点数据结构。如果需要另外的更新,则在存储体中的一个存储体的第二部分中引入新的节点数据结构,然后更新存储在第一部分中的节点数据结构中包含的存储器地址,使得其现在指向存储在第二部分中的新创建的节点数据结构。因此,该方法可以通过在第二部分和第三部分中进行交替创建来创建新节点数据结构。该方法可以使得能够更新树结构,同时提供对树结构的持续访问。In some embodiments, each bank is divided into three sections. The first part stores the nodes of the first step of the tree, the second part stores the nodes of the subsequent steps of the tree, and the third part remains unused. When the tree structure needs to be updated, a new node data structure is introduced in the third part of the memory bank, then the memory address contained in the node data structure stored in the first part is updated so that it now points to the node data structure stored in the third part The newly created node data structure. If an additional update is required, introduce a new node data structure in the second part of one of the banks, then update the memory address contained in the node data structure stored in the first part so that it now points to the The newly created node data structure in the second part. Therefore, the method can create a new node data structure by alternately creating in the second and third parts. The method may enable the tree structure to be updated while providing continuous access to the tree structure.
在一些实施方式中,如果非叶节点指向要被移除的无用叶节点,则可以通过用与标签相关联的值替换指向叶节点的指针将标签(例如,网络分组元数据)直接存储在与非叶节点相关联的节点数据结构中。该方法可以使得能够访问标签的值,而不需要访问非叶节点将指向的另一节点数据结构的额外步骤。In some implementations, if a non-leaf node points to a dead leaf node to be removed, the label (eg, network packet metadata) may be stored directly in the same directory with the value associated with the label by replacing the pointer to the leaf node with the value associated with the label. In the node data structure associated with non-leaf nodes. This method may enable access to the value of the label without the additional step of accessing another node data structure to which a non-leaf node would point.
现在转向图10,公开了根据本技术的一个或更多个说明性方面的用于压缩将网络分组签名与网络分组元数据相关联的树结构的方法1000的流程图。在一个或更多个实施方式中,方法1000或者其一个或更多个步骤可以由一个或更多个计算设备或实体执行。例如,方法1000的各部分可以由联网设备100或190的部件执行。方法1000或者其一个或更多个步骤可以以存储在计算机可读介质例如非暂态计算机可读介质中的计算机可执行指令来实施。可以省略或按顺序改变流程图中的一些步骤或步骤中的一部分。Turning now to FIG. 10, a flowchart of a
在一个或更多个实施方式中,将网络分组签名与网络分组元数据相关联的树结构包括包含网络分组元数据的多个叶节点和单比特测试节点的多个非叶节点。In one or more embodiments, the tree structure associating network packet signatures with network packet metadata includes a plurality of leaf nodes containing the network packet metadata and a plurality of non-leaf nodes including single-bit test nodes.
在步骤1002处,对于树结构的子部分,该方法确立具有单个子节点的连续非叶节点的数量。然后在步骤1004处,方法1000基于具有单个子节点的连续非叶节点的数量和压缩阈值确定是否要压缩树结构的子部分。如果做出要压缩树结构的子部分的确定,则方法1000进行到步骤1006。如果做出不压缩树结构的子部分的确定,则方法1000进行到步骤1008。At
在步骤1006处,生成经压缩的节点数据结构。经压缩的节点数据结构包括树结构的子部分的路径,该路径包括由与树结构的子部分的连续非叶节点中的每一个相关联的单比特的级联形成的比特序列,该序列的比特数等于或大于压缩阈值。在一些实施方式中,经压缩的节点数据结构的序列的比特数通过(1)具有子叶节点的连续非叶节点之一的存在、(2)具有多于一个子节点的连续非叶节点之一的存在或者(3)该序列的预定义最大大小来确定。在一些实施方式中,压缩阈值是5比特。在一些实施方式中,序列的预定义最大大小是30比特。At
在步骤1008处,生成非压缩的节点数据结构。非压缩的节点数据结构包括树结构的子部分的路径,该路径包括由与树结构的子部分的至少一个非叶节点相关联的一个或更多个单比特的级联形成的比特序列,所述至少一个非叶节点具有多于一个子节点,该序列的比特数小于压缩阈值。在一些实施方式中,路径包括树结构的子部分的多个路径。At
在步骤1010处,方法1000可以将经压缩的节点数据结构或非压缩的节点数据结构存储在非暂态计算机可读存储器中。At
在一些实施方式中,非暂态计算机可读存储器包括第一非暂态计算机可读存储器和第二非暂态计算机可读存储器。在一些实施方式中,第一非暂态计算机可读存储器是第一QDR SRAM存储器的第一存储体,并且第二非暂态计算机可读存储器是第二QDR SRAM存储器的第二存储体。In some implementations, the non-transitory computer-readable memory includes a first non-transitory computer-readable memory and a second non-transitory computer-readable memory. In some embodiments, the first non-transitory computer readable memory is a first bank of a first QDR SRAM memory and the second non-transitory computer readable memory is a second bank of a second QDR SRAM memory.
在一些实施方式中,经压缩的节点数据结构是第一经压缩的节点数据结构,并且(2)非压缩的节点数据结构是第一非压缩的节点数据结构,其中,第一节点数据结构包括第一经压缩的节点数据结构和第一非压缩的节点数据结构之一,并且第二节点数据结构包括第二经压缩的节点数据结构和第二非压缩的数据结构之一。在一些实施方式中,第一节点数据结构存储在第一非暂态计算机可读存储器中,并指向第二非暂态计算机可读存储器的存储有第二节点数据结构的存储器地址。在一些实施方式中,可以通过第一单次存储器访问从第一非暂态计算机可读存储器访问第一节点数据结构,并且可以通过第二单次存储器访问从第二非暂态计算机可读存储器访问第二节点数据结构。In some embodiments, the compressed node data structure is a first compressed node data structure, and (2) the uncompressed node data structure is a first uncompressed node data structure, wherein the first node data structure includes One of the first compressed node data structure and the first uncompressed node data structure, and the second node data structure includes one of the second compressed node data structure and the second uncompressed data structure. In some embodiments, the first node data structure is stored in the first non-transitory computer readable memory and points to a memory address of the second non-transitory computer readable memory where the second node data structure is stored. In some embodiments, the first node data structure can be accessed from the first non-transitory computer readable memory through a first single memory access, and the first node data structure can be accessed from the second non-transitory computer readable memory through a second single memory access Access the second node data structure.
在一些实施方式中,经压缩的节点数据结构是第一经压缩的节点数据结构,并且非压缩的节点数据结构是第一非压缩的节点数据结构,并且其中,非暂态计算机可读存储器包括第一部分、第二部分和第三部分,第一部分存储第一经压缩的节点数据结构和第一非压缩的节点数据结构之一,第一经压缩的节点数据结构和第一非压缩的节点数据结构之一指向存储在第二部分中的第二经压缩的节点数据结构和第二非压缩的节点数据结构之一,并且其中,在更新树结构时,将第三经压缩的节点数据结构和第三非压缩的节点数据结构之一存储在第三部分中,并修改第一经压缩的节点数据结构和第一非压缩的节点数据结构之一,使得第一经压缩的节点数据结构和第一非压缩的节点数据结构之一指向第三经压缩的节点数据结构和第三非压缩的节点数据结构之一。In some implementations, the compressed node data structure is a first compressed node data structure, and the uncompressed node data structure is a first uncompressed node data structure, and wherein the non-transitory computer-readable memory includes The first part, the second part and the third part, the first part stores one of the first compressed node data structure and the first uncompressed node data structure, the first compressed node data structure and the first uncompressed node data One of the structures points to one of the second compressed node data structure and the second uncompressed node data structure stored in the second portion, and wherein, when updating the tree structure, the third compressed node data structure and One of the third uncompressed node data structures is stored in the third portion, and one of the first compressed node data structure and the first uncompressed node data structure is modified such that the first compressed node data structure and the first One of an uncompressed node data structure points to one of a third compressed node data structure and a third uncompressed node data structure.
在一些实施方式中,方法1000还包括至少一个操作:(1)基于通过网络分组元数据建立的优先级来传输网络分组,(2)基于网络分组元数据识别要对网络分组执行的服务,(3)基于网络分组元数据测试网络分组以确立网络分组是网络攻击的一部分和/或(4)基于网络分组元数据创建对网络分组的流量的度量。In some embodiments,
尽管上面描述了示例实施方式,但是取决于特定效果或应用,可以以任何期望的方式组合、划分、省略、重新布置、修改或扩充各个特征和步骤。本领域技术人员将容易想到各种改变、修改和改进。尽管未在本文中明确说明,但是通过本公开内容而明显的这样的改变、修改和改进旨在成为本说明书的一部分,并且旨在落入本公开内容的精神和范围内。因此,前面的描述仅作为示例,而不是限制。仅如以下权利要求书及其等同物中所限定的限制该专利。Although example embodiments are described above, the various features and steps may be combined, divided, omitted, rearranged, modified, or augmented in any desired manner, depending on the particular effect or application. Various changes, modifications, and improvements will readily occur to those skilled in the art. Although not expressly stated herein, such changes, modifications, and improvements apparent from the present disclosure are intended to be part of this specification, and are intended to be within the spirit and scope of the present disclosure. Accordingly, the foregoing description is by way of example only, and not limitation. This patent is limited only as defined in the following claims and their equivalents.
Claims (20)
Applications Claiming Priority (2)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| EP18315022.6A EP3618389B1 (en) | 2018-08-27 | 2018-08-27 | Systems and methods for operating a networking device |
| EP18315022.6 | 2018-08-27 |
Publications (2)
| Publication Number | Publication Date |
|---|---|
| CN110868388A true CN110868388A (en) | 2020-03-06 |
| CN110868388B CN110868388B (en) | 2023-03-24 |
Family
ID=64664693
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| CN201910791760.1A Active CN110868388B (en) | 2018-08-27 | 2019-08-26 | System and method for operating networked devices |
Country Status (5)
| Country | Link |
|---|---|
| US (2) | US11283764B2 (en) |
| EP (1) | EP3618389B1 (en) |
| CN (1) | CN110868388B (en) |
| DK (1) | DK3618389T3 (en) |
| PL (1) | PL3618389T3 (en) |
Cited By (1)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN115878025A (en) * | 2021-09-28 | 2023-03-31 | 慧与发展有限责任合伙企业 | Tree structure node compression priority |
Citations (5)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| WO2006123036A1 (en) * | 2005-05-19 | 2006-11-23 | France Telecom | Method for the tree structure representation of a group of digital data streams, the associated tree structure and method and system for the detection of a flood attack |
| US7536476B1 (en) * | 2002-12-20 | 2009-05-19 | Cisco Technology, Inc. | Method for performing tree based ACL lookups |
| US20150127783A1 (en) * | 2013-11-04 | 2015-05-07 | Amazon Technologies, Inc. | Centralized networking configuration in distributed systems |
| US20170339187A1 (en) * | 2016-05-19 | 2017-11-23 | Nec Europe Ltd. | Intrusion detection and prevention system and method for generating detection rules and taking countermeasures |
| CN107534601A (en) * | 2015-05-15 | 2018-01-02 | 三菱电机株式会社 | Packet filtering device and grouping filter method |
Family Cites Families (30)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US6385649B1 (en) * | 1998-11-06 | 2002-05-07 | Microsoft Corporation | Routers and methods for optimal routing table compression |
| US6618755B1 (en) | 1999-12-07 | 2003-09-09 | Watchguard Technologies, Inc. | Automatically identifying subnetworks in a network |
| US7331060B1 (en) | 2001-09-10 | 2008-02-12 | Xangati, Inc. | Dynamic DoS flooding protection |
| US7277426B2 (en) | 2002-05-24 | 2007-10-02 | Mosaid Technologies, Inc. | Method and apparatus for reordering entries in a multi probe lookup |
| US7324447B1 (en) | 2002-09-30 | 2008-01-29 | Packeteer, Inc. | Methods, apparatuses and systems facilitating concurrent classification and control of tunneled and non-tunneled network traffic |
| US7571242B2 (en) | 2003-10-24 | 2009-08-04 | Alcatel Lucent | Method for accelerated packet processing |
| US7411957B2 (en) | 2004-03-26 | 2008-08-12 | Cisco Technology, Inc. | Hardware filtering support for denial-of-service attacks |
| US7397766B2 (en) | 2004-03-31 | 2008-07-08 | Lucent Technologies Inc. | High-speed traffic measurement and analysis methodologies and protocols |
| US7366728B2 (en) | 2004-04-27 | 2008-04-29 | International Business Machines Corporation | System for compressing a search tree structure used in rule classification |
| US8203972B2 (en) * | 2004-06-30 | 2012-06-19 | Sap Ag | Method and system for compressing a tree |
| US7933985B2 (en) | 2004-08-13 | 2011-04-26 | Sipera Systems, Inc. | System and method for detecting and preventing denial of service attacks in a communications system |
| US8161549B2 (en) | 2005-11-17 | 2012-04-17 | Patrik Lahti | Method for defending against denial-of-service attack on the IPV6 neighbor cache |
| US8046496B1 (en) | 2007-12-12 | 2011-10-25 | Narus, Inc. | System and method for network data compression |
| SE532426C2 (en) | 2008-05-26 | 2010-01-19 | Oricane Ab | Method for data packet classification in a data communication network |
| US20110138463A1 (en) | 2009-12-07 | 2011-06-09 | Electronics And Telecommunications Research Institute | Method and system for ddos traffic detection and traffic mitigation using flow statistics |
| US20130155918A1 (en) | 2011-12-20 | 2013-06-20 | Nokia Siemens Networks Oy | Techniques To Enhance Header Compression Efficiency And Enhance Mobile Node Security |
| US9171030B1 (en) | 2012-01-09 | 2015-10-27 | Marvell Israel (M.I.S.L.) Ltd. | Exact match lookup in network switch devices |
| US8792494B2 (en) | 2012-09-14 | 2014-07-29 | International Business Machines Corporation | Facilitating insertion of device MAC addresses into a forwarding database |
| US9245626B2 (en) | 2012-10-26 | 2016-01-26 | Cisco Technology, Inc. | System and method for packet classification and internet protocol lookup in a network environment |
| GB201302402D0 (en) | 2013-02-11 | 2013-03-27 | Telecom Ltd Q | Communication apparatus |
| US9967187B2 (en) | 2013-04-11 | 2018-05-08 | Marvell Israel (M.I.S.L) Ltd. | Exact match lookup with variable key sizes |
| US9356818B2 (en) * | 2013-10-30 | 2016-05-31 | Telefonaktiebolaget Lm Ericsson (Publ) | Method and computing device for packet classification |
| JP6463898B2 (en) | 2014-03-13 | 2019-02-06 | 株式会社東芝 | Communication apparatus, information processing apparatus, communication method, and communication program |
| US9769290B2 (en) | 2014-05-23 | 2017-09-19 | Intel Corporation | Packet flow classification |
| US10587516B1 (en) | 2014-07-15 | 2020-03-10 | Marvell Israel (M.I.S.L) Ltd. | Hash lookup table entry management in a network device |
| US10277511B2 (en) | 2015-12-16 | 2019-04-30 | Nxp Usa, Inc. | Hash-based packet classification with multiple algorithms at a network processor |
| US10616271B2 (en) | 2017-01-03 | 2020-04-07 | Microsemi Frequency And Time Corporation | System and method for mitigating distributed denial of service attacks |
| US10511445B1 (en) * | 2017-01-05 | 2019-12-17 | Amazon Technologies, Inc. | Signature compression for hash-based signature schemes |
| US11310158B2 (en) | 2017-12-08 | 2022-04-19 | Corsa Technology Inc. | Packet classification using fingerprint hash table |
| US10884939B2 (en) | 2018-06-11 | 2021-01-05 | Amazon Technologies, Inc. | Cache pre-fetching using cyclic buffer |
-
2018
- 2018-08-27 DK DK18315022.6T patent/DK3618389T3/en active
- 2018-08-27 PL PL18315022T patent/PL3618389T3/en unknown
- 2018-08-27 EP EP18315022.6A patent/EP3618389B1/en active Active
-
2019
- 2019-08-21 US US16/546,806 patent/US11283764B2/en active Active
- 2019-08-26 CN CN201910791760.1A patent/CN110868388B/en active Active
-
2022
- 2022-02-16 US US17/672,850 patent/US11627110B2/en active Active
Patent Citations (5)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US7536476B1 (en) * | 2002-12-20 | 2009-05-19 | Cisco Technology, Inc. | Method for performing tree based ACL lookups |
| WO2006123036A1 (en) * | 2005-05-19 | 2006-11-23 | France Telecom | Method for the tree structure representation of a group of digital data streams, the associated tree structure and method and system for the detection of a flood attack |
| US20150127783A1 (en) * | 2013-11-04 | 2015-05-07 | Amazon Technologies, Inc. | Centralized networking configuration in distributed systems |
| CN107534601A (en) * | 2015-05-15 | 2018-01-02 | 三菱电机株式会社 | Packet filtering device and grouping filter method |
| US20170339187A1 (en) * | 2016-05-19 | 2017-11-23 | Nec Europe Ltd. | Intrusion detection and prevention system and method for generating detection rules and taking countermeasures |
Cited By (2)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN115878025A (en) * | 2021-09-28 | 2023-03-31 | 慧与发展有限责任合伙企业 | Tree structure node compression priority |
| CN115878025B (en) * | 2021-09-28 | 2024-07-16 | 慧与发展有限责任合伙企业 | Tree structure node compression priority |
Also Published As
| Publication number | Publication date |
|---|---|
| CN110868388B (en) | 2023-03-24 |
| EP3618389B1 (en) | 2020-10-07 |
| US20220294764A1 (en) | 2022-09-15 |
| US11627110B2 (en) | 2023-04-11 |
| US11283764B2 (en) | 2022-03-22 |
| DK3618389T3 (en) | 2020-11-09 |
| EP3618389A1 (en) | 2020-03-04 |
| PL3618389T3 (en) | 2021-04-06 |
| US20200067881A1 (en) | 2020-02-27 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| US10735379B2 (en) | Hybrid hardware-software distributed threat analysis | |
| US9736115B2 (en) | Firewall packet filtering | |
| US9344366B2 (en) | System and method for rule matching in a processor | |
| CN101577721A (en) | Method for splitting Broome filter by indexes and inserting, deleting and inquiring methods thereof | |
| JP2009510815A (en) | Method and system for reassembling packets before search | |
| US8365045B2 (en) | Flow based data packet processing | |
| CN110868387B (en) | System and method for operating a networked device | |
| CN108282454B (en) | Apparatus, system, and method for accelerating security checks using inline pattern matching | |
| US10681007B2 (en) | String search and matching for gate functionality | |
| CN112445771A (en) | Data processing method, device and equipment of network flow and storage medium | |
| WO2024099078A1 (en) | Method for detecting attack traffic, and related device | |
| KR102014741B1 (en) | Matching method of high speed snort rule and yara rule based on fpga | |
| CN110868388B (en) | System and method for operating networked devices | |
| CN115865843A (en) | Rule storage method, message processing method, device, electronic equipment and medium | |
| US11805050B2 (en) | Systems and methods to filter out noisy application signatures to improve precision of first packet application classification | |
| TWI763360B (en) | Method of filtering packets in network switch and related filter | |
| CN120850290B (en) | Multi-feature code matching method, device, electronic equipment, medium and program product | |
| US20250030784A1 (en) | Method and system for high-volume compression of ipv4 unicast addresses | |
| CN119342033B (en) | Layer 2 protocol transparent transmission method, device, equipment and storage medium based on access control list | |
| US20250267124A1 (en) | System and method for utilization of firewall policies for network security | |
| EP3304852B1 (en) | String search and matching for gate functionality | |
| CN116781303A (en) | A DDoS attack protection method and related devices | |
| CN116738329A (en) | A malicious sample classification method, device, electronic device and storage medium | |
| CN117857098A (en) | SYN Flood attack defense system based on radix tree | |
| CN116032592A (en) | Server network security detection method, device and storage medium |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| PB01 | Publication | ||
| PB01 | Publication | ||
| SE01 | Entry into force of request for substantive examination | ||
| SE01 | Entry into force of request for substantive examination | ||
| GR01 | Patent grant | ||
| GR01 | Patent grant |