CN110839004A - Method and apparatus for access authentication - Google Patents
Method and apparatus for access authentication Download PDFInfo
- Publication number
- CN110839004A CN110839004A CN201810935614.7A CN201810935614A CN110839004A CN 110839004 A CN110839004 A CN 110839004A CN 201810935614 A CN201810935614 A CN 201810935614A CN 110839004 A CN110839004 A CN 110839004A
- Authority
- CN
- China
- Prior art keywords
- signature
- authentication
- access request
- access
- timestamp
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Pending
Links
Images
Classifications
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/08—Network architectures or network communication protocols for network security for authentication of entities
Landscapes
- Engineering & Computer Science (AREA)
- Computer Hardware Design (AREA)
- Computer Security & Cryptography (AREA)
- Computing Systems (AREA)
- General Engineering & Computer Science (AREA)
- Computer Networks & Wireless Communication (AREA)
- Signal Processing (AREA)
- Data Exchanges In Wide-Area Networks (AREA)
Abstract
本发明公开了一种访问认证的方法和装置,涉及计算机技术领域。该方法的一具体实施方式包括:接收访问请求;判断所述访问请求中的时间戳、第一签名、访问者IP是否均符合第二认证规则;若是,则通过认证;所述第二认证规则包括:所述时间戳在第一预设时间范围内,所述第一签名在第二预设时间范围内未使用过,所述访问者IP在允许访问的IP列表中。该实施方式因为采用签名的时效性验证、签名不能重复使用、允许访问IP的限制等技术手段,避免了签名重复使用的情况,优化了资源访问流程,提高了资源访问效率及减轻了业务系统的恶意请求的压力。
The invention discloses an access authentication method and device, and relates to the technical field of computers. A specific implementation of the method includes: receiving an access request; judging whether the timestamp, the first signature, and the visitor's IP in the access request all conform to the second authentication rule; if so, pass the authentication; the second authentication rule Including: the timestamp is within a first preset time range, the first signature has not been used within a second preset time range, and the visitor IP is in the list of IPs that are allowed to access. This embodiment avoids the repeated use of signatures, optimizes the resource access process, improves the efficiency of resource access, and reduces the workload of the business system due to the adoption of technical means such as signature timeliness verification, signatures that cannot be reused, and restrictions on allowing access to IP. The pressure of malicious requests.
Description
技术领域technical field
本发明涉及计算机技术领域,尤其涉及一种访问认证的方法和装置。The present invention relates to the field of computer technology, and in particular, to a method and device for access authentication.
背景技术Background technique
现有技术通过笛卡尔网关封装暴露统一资源定位符URL(Uniform ResourceLocator)供给资源访问者调用。认证规则由资源访问者指定的签名生成规则来进行认证。服务端(资源提供者)提供的http接口需要传token认证,token在计算机身份认证中是令牌(临时)的意思。In the prior art, a uniform resource locator URL (Uniform ResourceLocator) is exposed through a Cartesian gateway encapsulation for resource visitors to call. Authentication rules are authenticated by signature generation rules specified by resource visitors. The http interface provided by the server (resource provider) needs to pass token authentication, and token means token (temporary) in computer authentication.
在实现本发明过程中,发明人发现现有技术中至少存在如下问题:In the process of realizing the present invention, the inventor found that there are at least the following problems in the prior art:
1.现有的签名认证规则是客户提供的,如果验证规则和需要验证的参数泄露后很容易遭到恶意攻击。1. The existing signature authentication rules are provided by the customer. If the verification rules and the parameters that need to be verified are leaked, they will be easily attacked maliciously.
2.token存在重复使用的情况,若token重复使用,当遇到恶意攻击时,因为这个签名用过了,会拦截到恶意攻击的访问请求。2. The token is repeatedly used. If the token is reused, when a malicious attack is encountered, the access request of the malicious attack will be intercepted because the signature has been used.
发明内容SUMMARY OF THE INVENTION
有鉴于此,本发明实施例提供一种访问认证的方法和装置,能够解决签名token重复使用和参数泄露后容易遭受外网的恶意攻击的问题。In view of this, the embodiments of the present invention provide an access authentication method and apparatus, which can solve the problem of being vulnerable to malicious attacks from external networks after repeated use of the signature token and parameter leakage.
为实现上述目的,根据本发明实施例的一个方面,提供了一种访问认证的方法,包括:接收访问请求;判断所述访问请求中的时间戳、第一签名、访问者IP是否均符合第二认证规则;若是,则通过认证;所述第二认证规则包括:所述时间戳在第一预设时间范围内,所述第一签名在第二预设时间范围内未使用过,所述访问者IP在允许访问的IP列表中。In order to achieve the above purpose, according to an aspect of the embodiments of the present invention, a method for access authentication is provided, including: receiving an access request; Two authentication rules; if yes, pass the authentication; the second authentication rules include: the timestamp is within the first preset time range, the first signature has not been used within the second preset time range, the The visitor IP is in the list of allowed IPs.
可选地,判断所述访问请求中的时间戳、第一签名、访问者IP是否均符合第二认证规则之前,所述方法还包括:确定所述访问请求的版本号、必填参数符合第一认证规则;所述第一认证规则包括:所述访问请求的版本号与预设版本号一致,所述必填参数未缺失。Optionally, before judging whether the timestamp, the first signature, and the visitor's IP in the access request all conform to the second authentication rule, the method further includes: determining that the version number and required parameters of the access request conform to the second authentication rule. An authentication rule; the first authentication rule includes: the version number of the access request is consistent with the preset version number, and the required parameter is not missing.
可选地,判断所述访问请求中的时间戳、第一签名、访问者IP是否均符合第二认证规则;若是,则通过认证,包括:判断所述访问请求中的时间戳、第一签名、访问者IP是否均符合第二认证规则;若是,则根据所述访问请求中的签名参数,生成第二签名,并验证所述第二签名与所述第一签名是否一致;若所述第二签名与所述第一签名一致,则通过认证。Optionally, judging whether the timestamp, the first signature, and the visitor IP in the access request all meet the second authentication rule; if so, passing the authentication, including: judging the timestamp, the first signature in the access request , whether the visitor IP conforms to the second authentication rule; if so, generate a second signature according to the signature parameters in the access request, and verify whether the second signature is consistent with the first signature; if the first signature If the second signature is consistent with the first signature, the authentication is passed.
可选地,根据所述访问请求中的签名参数,生成第二签名,包括:获取访问请求中的签名参数,所述签名参数包括访问令牌、时间戳、通用唯一识别码、部分统一资源标识符;按照所述签名参数的键值,以字典序升序对所述签名参数进行排序并拼接,得到字符串;在所述字符串的末尾添加密钥,对添加密钥的字符串进行编码处理;采用消息摘要算法计算编码处理结果的摘要值,从而得到第二签名。Optionally, generating a second signature according to the signature parameters in the access request, including: acquiring the signature parameters in the access request, where the signature parameters include an access token, a timestamp, a universal unique identifier, and a partial uniform resource identifier according to the key value of the signature parameter, sort and splicing the signature parameter in ascending lexicographical order to obtain a string; add a key at the end of the character string, and encode the string to which the key is added. ; Use the message digest algorithm to calculate the digest value of the encoded processing result, thereby obtaining the second signature.
为实现上述目的,根据本发明实施例的再一个方面,提供了一种访问认证的装置,包括:接收模块,用于:接收访问请求;认证模块,用于:判断所述访问请求中的时间戳、第一签名、访问者IP是否均符合第二认证规则;若是,则通过认证;所述第二认证规则包括:所述时间戳在第一预设时间范围内,所述第一签名在第二预设时间范围内未使用过,所述访问者IP在允许访问的IP列表中。In order to achieve the above object, according to another aspect of the embodiments of the present invention, there is provided an access authentication device, comprising: a receiving module for: receiving an access request; an authentication module for: judging the time in the access request Whether the stamp, the first signature, and the visitor's IP all meet the second authentication rule; if so, pass the authentication; the second authentication rule includes: the timestamp is within the first preset time range, and the first signature is within the first preset time range. It has not been used within the second preset time range, and the visitor IP is in the list of IPs that are allowed to access.
可选地,所述认证模块,还用于:确定所述访问请求的版本号、必填参数符合第一认证规则;所述第一认证规则包括:所述访问请求的版本号与预设版本号一致,所述必填参数未缺失。Optionally, the authentication module is further configured to: determine that the version number and required parameters of the access request conform to a first authentication rule; the first authentication rule includes: the version number of the access request and a preset version The numbers are the same, and the required parameters are not missing.
可选地,所述认证模块,还用于:判断所述访问请求中的时间戳、第一签名、访问者IP是否均符合第二认证规则;若是,则根据所述访问请求中的签名参数,生成第二签名,并验证所述第二签名与所述第一签名是否一致;若所述第二签名与所述第一签名一致,则通过认证。Optionally, the authentication module is further configured to: judge whether the timestamp, the first signature and the visitor IP in the access request all conform to the second authentication rule; if so, according to the signature parameter in the access request , generate a second signature, and verify whether the second signature is consistent with the first signature; if the second signature is consistent with the first signature, the authentication is passed.
可选地,所述认证模块,还用于:获取访问请求中的签名参数,所述签名参数包括访问令牌、时间戳、通用唯一识别码、部分统一资源标识符;按照所述签名参数的键值,以字典序升序对所述签名参数进行排序并拼接,得到字符串;在所述字符串的末尾添加密钥,对添加密钥的字符串进行编码处理;采用消息摘要算法计算编码处理结果的摘要值,从而得到第二签名。Optionally, the authentication module is further configured to: obtain signature parameters in the access request, where the signature parameters include an access token, a timestamp, a universal unique identifier, and a partial uniform resource identifier; key value, sort and splicing the signature parameters in ascending lexicographical order to obtain a string; add a key at the end of the string, and encode the string with the added key; use message digest algorithm to calculate the encoding process The digest value of the result, resulting in the second signature.
为实现上述目的,根据本发明实施例的再一个方面,提供了一种电子设备,包括:一个或多个处理器;存储装置,用于存储一个或多个程序,当所述一个或多个程序被所述一个或多个处理器执行,使得所述一个或多个处理器实现如本发明实施例提供的访问认证的方法。To achieve the above object, according to yet another aspect of the embodiments of the present invention, an electronic device is provided, including: one or more processors; a storage device for storing one or more programs, when the one or more The program is executed by the one or more processors, so that the one or more processors implement the access authentication method provided by the embodiment of the present invention.
为实现上述目的,根据本发明实施例的再一个方面,提供了一种计算机可读介质,其上存储有计算机程序,所述程序被处理器执行时实现如本发明实施例提供的访问认证的方法。In order to achieve the above object, according to another aspect of the embodiments of the present invention, a computer-readable medium is provided, on which a computer program is stored, and when the program is executed by a processor, the access authentication as provided in the embodiments of the present invention is implemented. method.
上述发明中的一个实施例具有如下优点或有益效果:因为采用签名的时效性验证、签名不能重复使用、允许访问IP的限制等技术手段,避免了签名重复使用的情况,优化了资源访问流程,提高了资源访问效率及减轻了业务系统的恶意请求的压力。An embodiment in the above invention has the following advantages or beneficial effects: because the use of technical means such as the timeliness verification of the signature, the signature cannot be reused, and the restriction of allowing access to IP, the situation of repeated use of the signature is avoided, and the resource access process is optimized, The efficiency of resource access is improved and the pressure of malicious requests of the business system is reduced.
上述的非惯用的可选方式所具有的进一步效果将在下文中结合具体实施方式加以说明。Further effects of the above non-conventional alternatives will be described below in conjunction with specific embodiments.
附图说明Description of drawings
附图用于更好地理解本发明,不构成对本发明的不当限定。其中:The accompanying drawings are used for better understanding of the present invention and do not constitute an improper limitation of the present invention. in:
图1是根据本发明实施例的访问认证的方法的基本流程的示意图;1 is a schematic diagram of a basic flow of a method for access authentication according to an embodiment of the present invention;
图2是根据本发明实施例的访问认证的方法的优选流程的示意图;2 is a schematic diagram of a preferred flow of a method for access authentication according to an embodiment of the present invention;
图3是根据本发明实施例的访问认证的装置的基本模块的示意图;3 is a schematic diagram of a basic module of an apparatus for access authentication according to an embodiment of the present invention;
图4是本发明实施例可以应用于其中的示例性系统架构图;4 is an exemplary system architecture diagram to which an embodiment of the present invention may be applied;
图5是适于用来实现本发明实施例的终端设备或服务器的计算机系统的结构示意图。FIG. 5 is a schematic structural diagram of a computer system suitable for implementing a terminal device or a server according to an embodiment of the present invention.
具体实施方式Detailed ways
以下结合附图对本发明的示范性实施例做出说明,其中包括本发明实施例的各种细节以助于理解,应当将它们认为仅仅是示范性的。因此,本领域普通技术人员应当认识到,可以对这里描述的实施例做出各种改变和修改,而不会背离本发明的范围和精神。同样,为了清楚和简明,以下的描述中省略了对公知功能和结构的描述。Exemplary embodiments of the present invention are described below with reference to the accompanying drawings, which include various details of the embodiments of the present invention to facilitate understanding and should be considered as exemplary only. Accordingly, those of ordinary skill in the art will recognize that various changes and modifications of the embodiments described herein can be made without departing from the scope and spirit of the invention. Also, descriptions of well-known functions and constructions are omitted from the following description for clarity and conciseness.
图1是根据本发明实施例的访问认证的方法的基本流程的示意图。如图1所示,本发明实施例提供了一种访问认证的方法,包括:FIG. 1 is a schematic diagram of a basic flow of a method for access authentication according to an embodiment of the present invention. As shown in FIG. 1, an embodiment of the present invention provides an access authentication method, including:
步骤S101.接收访问请求;Step S101. Receive an access request;
步骤S102.判断所述访问请求中的时间戳、第一签名、访问者IP是否均符合第二认证规则;若是,则通过认证;Step S102. Judge whether the timestamp, the first signature and the visitor IP in the access request all meet the second authentication rule; if so, pass the authentication;
步骤S103.所述第二认证规则包括:所述时间戳在第一预设时间范围内,所述第一签名在第二预设时间范围内未使用过,所述访问者IP在预设的允许访问IP列表中。Step S103. The second authentication rule includes: the timestamp is within the first preset time range, the first signature has not been used within the second preset time range, and the visitor IP is within the preset time range. Allow access to the IP list.
本发明实施例采用签名的时效性验证、签名不能重复使用、允许访问IP的限制等技术手段,避免了签名重复使用的情况,优化了资源访问流程,提高了资源访问效率及减轻了业务系统的恶意请求的压力。The embodiment of the present invention adopts technical means such as the timeliness verification of the signature, the non-reusable signature, and the restriction of allowing access to IP, etc., so as to avoid the repeated use of the signature, optimize the resource access process, improve the resource access efficiency, and reduce the workload of the business system. The pressure of malicious requests.
本发明实施例中,判断所述访问请求中的时间戳、第一签名、访问者IP是否均符合第二认证规则之前,所述方法还包括:确定所述访问请求中的版本号、必填参数符合第一认证规则;所述第一认证规则包括:所述访问请求的版本号与预设版本号一致,所述必填参数未缺失。必填参数是指资源访问者与资源提供者约定的必须存在于访问请求中的参数。预设版本号是由资源提供者的提供的,用于验证访问请求的版本号是否符合要求。本发明实施例避免了签名重复使用的情况,优化了资源访问流程,提高了资源访问效率及减轻了业务系统的恶意请求的压力。In the embodiment of the present invention, before judging whether the timestamp, the first signature, and the visitor IP in the access request all conform to the second authentication rule, the method further includes: determining the version number, required The parameter conforms to the first authentication rule; the first authentication rule includes: the version number of the access request is consistent with the preset version number, and the required parameter is not missing. Mandatory parameters refer to the parameters agreed between the resource visitor and the resource provider that must exist in the access request. The preset version number is provided by the resource provider and is used to verify whether the version number of the access request meets the requirements. The embodiment of the present invention avoids the repeated use of the signature, optimizes the resource access process, improves the resource access efficiency, and reduces the pressure of malicious requests of the business system.
本发明实施例中,判断所述访问请求中的时间戳、第一签名、访问者IP是否均符合第二认证规则;若是,则通过认证,包括:判断所述访问请求中的时间戳、第一签名、访问者IP是否均符合第二认证规则;若是,则根据所述访问请求中的签名参数,生成第二签名,并验证所述第二签名与所述第一签名是否一致;若所述第二签名与所述第一签名一致,则通过认证。本发明实施例避免了签名重复使用的情况,优化了资源访问流程,提高了资源访问效率及减轻了业务系统的恶意请求的压力。In the embodiment of the present invention, it is judged whether the timestamp, the first signature, and the visitor's IP in the access request all meet the second authentication rule; Whether the first signature and the visitor's IP conform to the second authentication rule; if so, generate a second signature according to the signature parameters in the access request, and verify whether the second signature is consistent with the first signature; If the second signature is consistent with the first signature, the authentication is passed. The embodiment of the present invention avoids the repeated use of the signature, optimizes the resource access process, improves the resource access efficiency, and reduces the pressure of malicious requests of the business system.
本发明实施例中,根据所述访问请求中的签名参数,生成第二签名,包括:获取访问请求中的签名参数,所述签名参数包括访问令牌(api_key)、时间戳、通用唯一识别码(即UUID随机数)、部分统一资源标识符(即部分URI);所述部分URI(Uniform ResourceIdentifier)是指访问请求的URI中版本号之后的部分。按照所述签名参数的键值,以字典序升序对所述签名参数进行排序并拼接,得到字符串;在所述字符串的末尾添加密钥(secret_key),对添加密钥的字符串进行编码处理;采用消息摘要算法计算编码处理结果的摘要值,从而得到第二签名(也可以为:编码处理结果的MD5值即为第二签名)。UUID随机数是指UUID生成的随机数,UUID(Universally Unique Identifier)通用唯一识别码,是一种软件建构的标准,也指在一台机器上生成的数字,它保证对在同一时空中的所有机器都是唯一的。MD5消息摘要算法(MD5Message-Digest Algorithm),一种被广泛使用的密码散列函数,可以产生出一个128位(16字节)的散列值(hash value),用于确保信息传输完整一致。字典序是基于字母顺序排列的单词按字母顺序排列的方法。本发明实施例避免了签名重复使用的情况,优化了资源访问流程,提高了资源访问效率及减轻了业务系统的恶意请求的压力。In the embodiment of the present invention, generating the second signature according to the signature parameters in the access request includes: acquiring the signature parameters in the access request, where the signature parameters include an access token (api_key), a timestamp, and a universal unique identifier. (ie UUID random number), part of uniform resource identifier (ie part of URI); the part of URI (Uniform ResourceIdentifier) refers to the part after the version number in the URI of the access request. According to the key value of the signature parameter, sort and splicing the signature parameters in ascending lexicographic order to obtain a string; add a secret key (secret_key) at the end of the string to encode the string with the added key Processing: using the message digest algorithm to calculate the digest value of the encoding processing result, so as to obtain the second signature (it may also be: the MD5 value of the encoding processing result is the second signature). UUID random number refers to the random number generated by UUID. UUID (Universally Unique Identifier) is a standard for software construction. It also refers to the number generated on a machine. Machines are unique. MD5 Message-Digest Algorithm, a widely used cryptographic hash function, can generate a 128-bit (16-byte) hash value to ensure complete and consistent information transmission. Lexicographical order is a method of alphabetizing words based on alphabetical order. The embodiment of the present invention avoids the repeated use of the signature, optimizes the resource access process, improves the resource access efficiency, and reduces the pressure of malicious requests of the business system.
本发明实施例从以下几个维度进行认证:a.版本号的验证;b.时间戳时效性的验证;c.签名是否使用过的验证;d.签名的验证;e.远程访问IP的合法性验证。图2是根据本发明实施例的访问认证的方法的优选流程的示意图。如图所示,资源访问者将数字签名(第一签名)、api_key、本次访问生成的通用唯一识别码(UUID随机数)和时间戳发送给资源提供者;资源提供者在接收到来自资源访问者的访问请求后,验证版本号是否匹配、必填参数是否缺失、时间戳的时效、第一签名在时效期内是否使用过、访问IP是否在允许访问的范围内,资源访问者的版本号后的URI、api_key、生成的UUID随机数、请求时的时间戳和密钥(secret_key)进行MD5运算生成第二签名,将接收的第一签名与由访问请求中的参数根据签名算法生成的第二签名信息进行比对,如果结果一致,则通过认证。本发明实施例优化了资源访问流程,提高了资源访问效率及减轻了业务系统的恶意请求的压力。The embodiment of the present invention performs authentication from the following dimensions: a. Verification of the version number; b. Verification of the timeliness of the timestamp; c. Verification of whether the signature has been used; d. Verification of the signature; e. The legality of the remote access IP Sexual verification. FIG. 2 is a schematic diagram of a preferred flow of a method for access authentication according to an embodiment of the present invention. As shown in the figure, the resource visitor sends the digital signature (the first signature), the api_key, the universally unique identifier (UUID random number) generated during this visit, and the timestamp to the resource provider; After the visitor's access request, verify whether the version number matches, whether the required parameters are missing, whether the time stamp is valid, whether the first signature has been used within the validity period, whether the access IP is within the allowed access range, and the version of the resource visitor. The URI, api_key, generated UUID random number, timestamp and secret key (secret_key) after the number are subjected to MD5 operation to generate the second signature, and the received first signature and the parameters in the access request are generated according to the signature algorithm. The second signature information is compared, and if the results are consistent, the authentication is passed. The embodiment of the present invention optimizes the resource access process, improves the resource access efficiency and reduces the pressure of malicious requests of the business system.
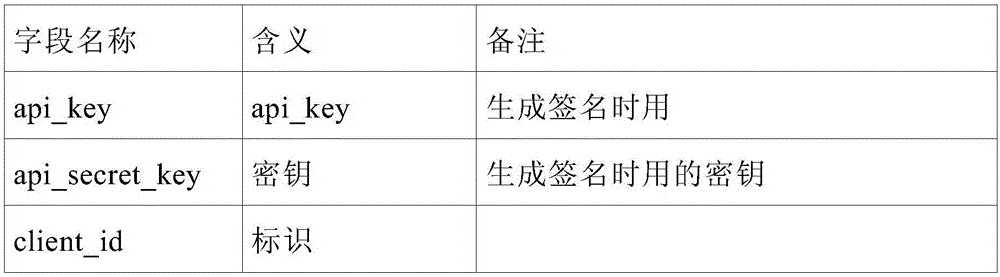
资源提供者的认证管理表如表1所示,资源提供者利用表1对资源访问者进行认证管理。The authentication management table of the resource provider is shown in Table 1, and the resource provider uses Table 1 to perform authentication management on the resource visitor.
表1Table 1
枚举类型在C#或C++、java、VB等一些计算机编程语言中是一种基本数据类型而不是构造数据类型。新合作的项目和\或公司,有认证需求时,可以在此表1中添加新记录,然后资源提供者发给资源访问者生成签名需要的api_key和secret_key,还有允许访问的IP列表。Enumeration type is a basic data type in some computer programming languages such as C# or C++, java, VB, etc., rather than a constructed data type. Newly cooperating projects and/or companies can add new records in this table 1 when they have authentication requirements, and then the resource provider sends the api_key and secret_key required to generate signatures to the resource visitor, as well as a list of IPs that are allowed to access.
资源提供者与资源访问者对接时可以将api_key、secret_key、允许访问的IP列表(allow_IP)和版本号配置到配置文件中。资源提供者与资源访问者的交互格式为JSON,并且要对访问请求中的参数进行UTF-8编码。访问请求中的请求头(HTTP Header)参数说明如表2所示:When the resource provider connects with the resource visitor, you can configure the api_key, secret_key, allowed IP list (allow_IP) and version number into the configuration file. The interaction format between the resource provider and the resource visitor is JSON, and the parameters in the access request need to be encoded in UTF-8. The description of the request header (HTTP Header) parameters in the access request is shown in Table 2:
表2Table 2
认证接口api使用签名算法生成第二签名的过程如下:The process of using the signature algorithm to generate the second signature by the authentication interface api is as follows:
1.获取访问请求的HTTP Header中的访问令牌api_key、时间戳timestamp、nonce。1. Obtain the access token api_key, timestamp, and nonce in the HTTP Header of the access request.
2.获取访问请求的URI,URI(Uniform Resource Identifier)为统一资源标识符,可以标识、定位任何资源的字符串;例如:2. Obtain the URI of the access request. URI (Uniform Resource Identifier) is a uniform resource identifier, which can identify and locate any resource string; for example:
https://IP:port/xxxx/api/v1/order/list,获取版本号“v1/”后面的部分“order/list”,即部分URI为“order/list”。https://IP:port/xxxx/api/v1/order/list, get the part of "order/list" after the version number "v1/", that is, the part of the URI is "order/list".
3.将所有签名参数(包括HTTP Header中的api_key、timestamp、nonce参数,和部分URI)键值以字典序升序排列。例如:api_key=value1&nonce=value2×tamp=value3&uri=order/list。3. Arrange the key values of all signature parameters (including the api_key, timestamp, nonce parameters in the HTTP Header, and part of the URI) in lexicographic ascending order. For example: api_key=value1&nonce=value2×tamp=value3&uri=order/list.
4.在拼接好的字符串末尾加上secret_key的值value4。例如:api_key=value1&nonce=value2×tamp=value3&uri=4. Add the value value4 of secret_key to the end of the spliced string. For example: api_key=value1&nonce=value2×tamp=value3&uri=
order/list&value4,并进行urlencode编码处理,形成基础字符串base_string,base_string的MD5值即为第二签名的值。urlencode是一个函数,可将字符串以URL编码,用于编码处理。即第二签名Signature=MD5(urlencode(api_key=value1&nonce=value2×tamp=va lue3&uri=order/list&value4))。order/list&value4, and urlencode encoding is performed to form the base string base_string, and the MD5 value of the base_string is the value of the second signature. urlencode is a function that URL-encodes a string for encoding processing. That is, the second signature Signature=MD5(urlencode(api_key=value1&nonce=value2×tamp=value3&uri=order/list&value4)).
本发明实施例提供了一种访问认证的装置300,包括:接收模块301,用于:接收访问请求;认证模块302,用于:判断所述访问请求中的时间戳、第一签名、访问者IP是否均符合第二认证规则;若是,则通过认证;所述第二认证规则包括:所述时间戳在第一预设时间范围内,所述第一签名在第二预设时间范围内未使用过,所述访问者IP在允许访问的IP列表中。本发明实施例采用验证签名的时效性、签名不能重复使用、允许访问IP的限制等技术手段,避免了签名重复使用的情况,优化了资源访问流程,提高了资源访问效率及减轻了业务系统的恶意请求的压力。An embodiment of the present invention provides an
本发明实施例中,所述认证模块302,还用于:还用于:确定所述访问请求的版本号、必填参数符合第一认证规则;所述第一认证规则包括:所述访问请求的版本号与预设版本号一致,所述必填参数未缺失。本发明实施例避免了签名重复使用的情况,优化了资源访问流程,提高了资源访问效率及减轻了业务系统的恶意请求的压力。In this embodiment of the present invention, the
本发明实施例中,所述认证模块302,还用于:判断所述访问请求中的时间戳、第一签名、访问者IP是否均符合第二认证规则;若是,则根据所述访问请求中的签名参数,生成第二签名,并验证所述第二签名与所述第一签名是否一致;若所述第二签名与所述第一签名一致,则通过认证。本发明实施例避免了签名重复使用的情况,优化了资源访问流程,提高了资源访问效率及减轻了业务系统的恶意请求的压力。In this embodiment of the present invention, the
本发明实施例中,所述认证模块302,还用于:获取访问请求中的签名参数,所述签名参数包括访问令牌、时间戳、通用唯一识别码、部分统一资源标识符;按照所述签名参数的键值,以字典序升序对所述签名参数进行排序并拼接,得到字符串;在所述字符串的末尾添加密钥,对添加密钥的字符串进行编码处理;采用消息摘要算法计算编码处理结果的摘要值,从而得到第二签名。本发明实施例避免了签名重复使用的情况,优化了资源访问流程,提高了资源访问效率及减轻了业务系统的恶意请求的压力。In this embodiment of the present invention, the
密钥(api_key/secret_key),以secret_key为参数,配合适当的签名算法,可以得到原始信息的数字签名,防止内容在传递过程中被伪造或篡改。密钥通常为成对创建和使用,包含一个api_key和一个secret_key。其中api_key会在传输中包含,而资源提供者必须保管好secret_key不在网络上传输以防止被窃取。The secret key (api_key/secret_key), with secret_key as the parameter, and the appropriate signature algorithm, can obtain the digital signature of the original information, preventing the content from being forged or tampered with during the transmission process. Secrets are usually created and used in pairs, consisting of an api_key and a secret_key. The api_key will be included in the transmission, and the resource provider must keep the secret_key from being transmitted on the network to prevent it from being stolen.
图4示出了可以应用本发明实施例的访问认证的方法或访问认证的装置的示例性系统架构400。FIG. 4 shows an
如图4所示,系统架构400可以包括终端设备401、402、403,网络404和服务器405。网络404用以在终端设备401、402、403和服务器405之间提供通信链路的介质。网络404可以包括各种连接类型,例如有线、无线通信链路或者光纤电缆等等。As shown in FIG. 4 , the
用户可以使用终端设备401、402、403通过网络404与服务器405交互,以接收或发送消息等。终端设备401、402、403上可以安装有各种通讯客户端应用,例如购物类应用、网页浏览器应用、搜索类应用、即时通信工具、邮箱客户端、社交平台软件等。The user can use the
终端设备401、402、403可以是具有显示屏并且支持网页浏览的各种电子设备,包括但不限于智能手机、平板电脑、膝上型便携计算机和台式计算机等等。The
服务器405可以是提供各种服务的服务器,例如对用户利用终端设备401、402、403所浏览的购物类网站提供支持的后台管理服务器。后台管理服务器可以对接收到的产品信息查询请求等数据进行分析等处理,并将处理结果反馈给终端设备。The
需要说明的是,本发明实施例所提供的访问认证的方法一般由服务器405执行,相应地,访问认证的装置一般设置于服务器405中。It should be noted that the access authentication method provided in the embodiment of the present invention is generally performed by the
应该理解,图4中的终端设备、网络和服务器的数目仅仅是示意性的。根据实现需要,可以具有任意数目的终端设备、网络和服务器。It should be understood that the numbers of terminal devices, networks and servers in FIG. 4 are merely illustrative. There can be any number of terminal devices, networks and servers according to implementation needs.
根据本发明的实施例,本发明实施例还提供了一种电子设备和一种计算机可读介质。According to the embodiments of the present invention, the embodiments of the present invention further provide an electronic device and a computer-readable medium.
本发明实施例的电子设备包括:一个或多个处理器;存储装置,用于存储一个或多个程序,当所述一个或多个程序被所述一个或多个处理器执行,使得所述一个或多个处理器实现如本发明实施例提供的访问认证的方法。An electronic device according to an embodiment of the present invention includes: one or more processors; and a storage device for storing one or more programs, when the one or more programs are executed by the one or more processors, the one or more programs cause the One or more processors implement the access authentication method provided by the embodiments of the present invention.
本发明实施例的计算机可读介质,其上存储有计算机程序,所述程序被处理器执行时实现如本发明实施例提供的访问认证的方法。The computer-readable medium of the embodiment of the present invention stores a computer program thereon, and when the program is executed by the processor, the access authentication method provided by the embodiment of the present invention is implemented.
下面参考图5,其示出了适于用来实现本发明实施例的终端设备的计算机系统500的结构示意图。图5示出的终端设备仅仅是一个示例,不应对本发明实施例的功能和使用范围带来任何限制。Referring to FIG. 5 below, it shows a schematic structural diagram of a
如图5所示,计算机系统500包括中央处理单元(CPU)501,其可以根据存储在只读存储器(ROM)502中的程序或者从存储部分508加载到随机访问存储器(RAM)503中的程序而执行各种适当的动作和处理。在RAM503中,还存储有系统500操作所需的各种程序和数据。CPU501、ROM502以及RAM503通过总线504彼此相连。输入/输出(I/O)接口505也连接至总线504。As shown in FIG. 5, a
以下部件连接至I/O接口505:包括键盘、鼠标等的输入部分506;包括诸如阴极射线管(CRT)、液晶显示器(LCD)等以及扬声器等的输出部分507;包括硬盘等的存储部分508;以及包括诸如LAN卡、调制解调器等的网络接口卡的通信部分509。通信部分509经由诸如因特网的网络执行通信处理。驱动器510也根据需要连接至I/O接口505。可拆卸介质511,诸如磁盘、光盘、磁光盘、半导体存储器等等,根据需要安装在驱动器510上,以便于从其上读出的计算机程序根据需要被安装入存储部分508。The following components are connected to the I/O interface 505: an
特别地,根据本发明公开的实施例,上文参考流程图描述的过程可以被实现为计算机软件程序。例如,本发明公开的实施例包括一种计算机程序产品,其包括承载在计算机可读介质上的计算机程序,该计算机程序包含用于执行流程图所示的方法的程序代码。在这样的实施例中,该计算机程序可以通过通信部分509从网络上被下载和安装,和/或从可拆卸介质511被安装。在该计算机程序被中央处理单元(CPU)501执行时,执行本发明的系统中限定的上述功能。In particular, the processes described above with reference to the flowcharts may be implemented as computer software programs in accordance with the disclosed embodiments of the present invention. For example, embodiments disclosed herein include a computer program product comprising a computer program carried on a computer-readable medium, the computer program containing program code for performing the method illustrated in the flowchart. In such an embodiment, the computer program may be downloaded and installed from the network via the
需要说明的是,本发明所示的计算机可读介质可以是计算机可读信号介质或者计算机可读存储介质或者是上述两者的任意组合。计算机可读存储介质例如可以是——但不限于——电、磁、光、电磁、红外线、或半导体的系统、装置或器件,或者任意以上的组合。计算机可读存储介质的更具体的例子可以包括但不限于:具有一个或多个导线的电连接、便携式计算机磁盘、硬盘、随机访问存储器(RAM)、只读存储器(ROM)、可擦式可编程只读存储器(EPROM或闪存)、光纤、便携式紧凑磁盘只读存储器(CD-ROM)、光存储器件、磁存储器件、或者上述的任意合适的组合。在本发明中,计算机可读存储介质可以是任何包含或存储程序的有形介质,该程序可以被指令执行系统、装置或者器件使用或者与其结合使用。而在本发明中,计算机可读的信号介质可以包括在基带中或者作为载波一部分传播的数据信号,其中承载了计算机可读的程序代码。这种传播的数据信号可以采用多种形式,包括但不限于电磁信号、光信号或上述的任意合适的组合。计算机可读的信号介质还可以是计算机可读存储介质以外的任何计算机可读介质,该计算机可读介质可以发送、传播或者传输用于由指令执行系统、装置或者器件使用或者与其结合使用的程序。计算机可读介质上包含的程序代码可以用任何适当的介质传输,包括但不限于:无线、电线、光缆、RF等等,或者上述的任意合适的组合。It should be noted that the computer-readable medium shown in the present invention may be a computer-readable signal medium or a computer-readable storage medium, or any combination of the above two. The computer-readable storage medium can be, for example, but not limited to, an electrical, magnetic, optical, electromagnetic, infrared, or semiconductor system, apparatus or device, or a combination of any of the above. More specific examples of computer readable storage media may include, but are not limited to, electrical connections with one or more wires, portable computer disks, hard disks, random access memory (RAM), read only memory (ROM), erasable Programmable read only memory (EPROM or flash memory), fiber optics, portable compact disk read only memory (CD-ROM), optical storage devices, magnetic storage devices, or any suitable combination of the foregoing. In the present invention, a computer-readable storage medium may be any tangible medium that contains or stores a program that can be used by or in conjunction with an instruction execution system, apparatus, or device. In the present invention, however, a computer-readable signal medium may include a data signal propagated in baseband or as part of a carrier wave, carrying computer-readable program code therein. Such propagated data signals may take a variety of forms, including but not limited to electromagnetic signals, optical signals, or any suitable combination of the foregoing. A computer-readable signal medium can also be any computer-readable medium other than a computer-readable storage medium that can transmit, propagate, or transport the program for use by or in connection with the instruction execution system, apparatus, or device . Program code embodied on a computer readable medium may be transmitted using any suitable medium including, but not limited to, wireless, wireline, optical fiber cable, RF, etc., or any suitable combination of the foregoing.
附图中的流程图和框图,图示了按照本发明各种实施例的系统、方法和计算机程序产品的可能实现的体系架构、功能和操作。在这点上,流程图或框图中的每个方框可以代表一个模块、程序段、或代码的一部分,上述模块、程序段、或代码的一部分包含一个或多个用于实现规定的逻辑功能的可执行指令。也应当注意,在有些作为替换的实现中,方框中所标注的功能也可以以不同于附图中所标注的顺序发生。例如,两个接连地表示的方框实际上可以基本并行地执行,它们有时也可以按相反的顺序执行,这依所涉及的功能而定。也要注意的是,框图或流程图中的每个方框、以及框图或流程图中的方框的组合,可以用执行规定的功能或操作的专用的基于硬件的系统来实现,或者可以用专用硬件与计算机指令的组合来实现。The flowchart and block diagrams in the Figures illustrate the architecture, functionality, and operation of possible implementations of systems, methods and computer program products according to various embodiments of the present invention. In this regard, each block in the flowchart or block diagrams may represent a module, segment, or portion of code that contains one or more logical functions for implementing the specified functions executable instructions. It should also be noted that, in some alternative implementations, the functions noted in the blocks may occur out of the order noted in the figures. For example, two blocks shown in succession may, in fact, be executed substantially concurrently, or the blocks may sometimes be executed in the reverse order, depending upon the functionality involved. It is also noted that each block of the block diagrams or flowchart illustrations, and combinations of blocks in the block diagrams or flowchart illustrations, can be implemented in special purpose hardware-based systems that perform the specified functions or operations, or can be implemented using A combination of dedicated hardware and computer instructions is implemented.
描述于本发明实施例中所涉及到的模块可以通过软件的方式实现,也可以通过硬件的方式来实现。所描述的模块也可以设置在处理器中,例如,可以描述为:一种处理器,包括:接收模块、认证模块、规则模块。其中,这些模块的名称在某种情况下并不构成对该模块本身的限定,例如,接收模块还可以被描述为“用于接收访问请求的模块”。The modules involved in the embodiments of the present invention may be implemented in a software manner, and may also be implemented in a hardware manner. The described module can also be set in the processor, for example, it can be described as: a processor, including: a receiving module, an authentication module, and a rule module. Wherein, the names of these modules do not constitute a limitation of the module itself under certain circumstances, for example, the receiving module may also be described as "a module for receiving access requests".
作为另一方面,本发明还提供了一种计算机可读介质,该计算机可读介质可以是上述实施例中描述的设备中所包含的;也可以是单独存在,而未装配入该设备中。上述计算机可读介质承载有一个或者多个程序,当上述一个或者多个程序被一个该设备执行时,使得该设备包括:步骤S101.接收访问请求;步骤S102.判断所述访问请求中的时间戳、第一签名、访问者IP是否均符合第二认证规则;若是,则通过认证;步骤S103.所述第二认证规则包括:所述时间戳在第一预设时间范围内,所述第一签名在第二预设时间范围内未使用过,所述访问者IP在预设的允许访问IP列表中。As another aspect, the present invention also provides a computer-readable medium, which may be included in the device described in the above embodiments; or may exist alone without being assembled into the device. The above-mentioned computer-readable medium carries one or more programs, and when the above-mentioned one or more programs are executed by a device, the device includes: step S101. receiving an access request; step S102. judging the time in the access request Whether the stamp, the first signature, and the visitor's IP all meet the second authentication rule; if so, pass the authentication; step S103. The second authentication rule includes: the timestamp is within the first preset time range, the first A signature has not been used within the second preset time range, and the visitor IP is in the preset list of allowed access IPs.
根据本发明实施例的访问认证的方法可以看出,因为采用签名的时效性验证、签名不能重复使用、允许访问IP的限制等技术手段,避免了签名重复使用的情况,优化了资源访问流程,提高了资源访问效率及减轻了业务系统的恶意请求的压力。According to the access authentication method according to the embodiment of the present invention, it can be seen that due to the use of technical means such as the timeliness of signature verification, signature cannot be reused, and the restriction of access IP, the situation of repeated use of signature is avoided, and the resource access process is optimized. The efficiency of resource access is improved and the pressure of malicious requests of the business system is reduced.
上述具体实施方式,并不构成对本发明保护范围的限制。本领域技术人员应该明白的是,取决于设计要求和其他因素,可以发生各种各样的修改、组合、子组合和替代。任何在本发明的精神和原则之内所作的修改、等同替换和改进等,均应包含在本发明保护范围之内。The above-mentioned specific embodiments do not constitute a limitation on the protection scope of the present invention. It should be understood by those skilled in the art that various modifications, combinations, sub-combinations and substitutions may occur depending on design requirements and other factors. Any modifications, equivalent replacements and improvements made within the spirit and principle of the present invention shall be included within the protection scope of the present invention.
Claims (10)
Priority Applications (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN201810935614.7A CN110839004A (en) | 2018-08-16 | 2018-08-16 | Method and apparatus for access authentication |
Applications Claiming Priority (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN201810935614.7A CN110839004A (en) | 2018-08-16 | 2018-08-16 | Method and apparatus for access authentication |
Publications (1)
| Publication Number | Publication Date |
|---|---|
| CN110839004A true CN110839004A (en) | 2020-02-25 |
Family
ID=69574071
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| CN201810935614.7A Pending CN110839004A (en) | 2018-08-16 | 2018-08-16 | Method and apparatus for access authentication |
Country Status (1)
| Country | Link |
|---|---|
| CN (1) | CN110839004A (en) |
Cited By (9)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN111510455A (en) * | 2020-04-16 | 2020-08-07 | 神州数码融信软件有限公司 | Request message authentication and data transmission method |
| CN111756749A (en) * | 2020-06-24 | 2020-10-09 | 中国建设银行股份有限公司 | Secure access method, device, equipment and storage medium |
| CN111769939A (en) * | 2020-06-29 | 2020-10-13 | 北京海泰方圆科技股份有限公司 | Access method, device, storage medium and electronic device for business system |
| CN112202706A (en) * | 2020-08-21 | 2021-01-08 | 国网浙江省电力有限公司杭州供电公司 | Safe access method and device for power system intranet |
| CN112804269A (en) * | 2021-04-14 | 2021-05-14 | 中建电子商务有限责任公司 | Method for realizing website interface anti-crawler |
| CN113612678A (en) * | 2021-07-15 | 2021-11-05 | 中标软件有限公司 | Safety protection method for downloading and using mail attachment |
| CN114520724A (en) * | 2022-02-18 | 2022-05-20 | 深圳前海环融联易信息科技服务有限公司 | Signature verification method of open API (application program interface) |
| CN114760063A (en) * | 2022-03-18 | 2022-07-15 | 百安居信息技术(上海)有限公司 | Home decoration data processing method, system, storage medium and equipment |
| CN115567296A (en) * | 2022-09-26 | 2023-01-03 | 北京树米网络科技有限公司 | A processing method for application interface protection |
Citations (6)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN102404392A (en) * | 2011-11-10 | 2012-04-04 | 山东浪潮齐鲁软件产业股份有限公司 | Web application or website integrated login method |
| CN103179134A (en) * | 2013-04-19 | 2013-06-26 | 中国建设银行股份有限公司 | Single sign on method and system based on Cookie and application server thereof |
| CN103475666A (en) * | 2013-09-23 | 2013-12-25 | 中国科学院声学研究所 | Internet of things resource digital signature authentication method |
| US9240886B1 (en) * | 2012-08-20 | 2016-01-19 | Amazon Technologies, Inc. | Authentication adaptation |
| CN108183907A (en) * | 2017-12-29 | 2018-06-19 | 浪潮通用软件有限公司 | A kind of authentication method, server and Verification System |
| CN108259437A (en) * | 2016-12-29 | 2018-07-06 | 北京神州泰岳软件股份有限公司 | A kind of http access methods, http-server and system |
-
2018
- 2018-08-16 CN CN201810935614.7A patent/CN110839004A/en active Pending
Patent Citations (6)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN102404392A (en) * | 2011-11-10 | 2012-04-04 | 山东浪潮齐鲁软件产业股份有限公司 | Web application or website integrated login method |
| US9240886B1 (en) * | 2012-08-20 | 2016-01-19 | Amazon Technologies, Inc. | Authentication adaptation |
| CN103179134A (en) * | 2013-04-19 | 2013-06-26 | 中国建设银行股份有限公司 | Single sign on method and system based on Cookie and application server thereof |
| CN103475666A (en) * | 2013-09-23 | 2013-12-25 | 中国科学院声学研究所 | Internet of things resource digital signature authentication method |
| CN108259437A (en) * | 2016-12-29 | 2018-07-06 | 北京神州泰岳软件股份有限公司 | A kind of http access methods, http-server and system |
| CN108183907A (en) * | 2017-12-29 | 2018-06-19 | 浪潮通用软件有限公司 | A kind of authentication method, server and Verification System |
Cited By (10)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN111510455A (en) * | 2020-04-16 | 2020-08-07 | 神州数码融信软件有限公司 | Request message authentication and data transmission method |
| CN111510455B (en) * | 2020-04-16 | 2022-06-10 | 神州数码融信软件有限公司 | Request message authentication and data transmission method |
| CN111756749A (en) * | 2020-06-24 | 2020-10-09 | 中国建设银行股份有限公司 | Secure access method, device, equipment and storage medium |
| CN111769939A (en) * | 2020-06-29 | 2020-10-13 | 北京海泰方圆科技股份有限公司 | Access method, device, storage medium and electronic device for business system |
| CN112202706A (en) * | 2020-08-21 | 2021-01-08 | 国网浙江省电力有限公司杭州供电公司 | Safe access method and device for power system intranet |
| CN112804269A (en) * | 2021-04-14 | 2021-05-14 | 中建电子商务有限责任公司 | Method for realizing website interface anti-crawler |
| CN113612678A (en) * | 2021-07-15 | 2021-11-05 | 中标软件有限公司 | Safety protection method for downloading and using mail attachment |
| CN114520724A (en) * | 2022-02-18 | 2022-05-20 | 深圳前海环融联易信息科技服务有限公司 | Signature verification method of open API (application program interface) |
| CN114760063A (en) * | 2022-03-18 | 2022-07-15 | 百安居信息技术(上海)有限公司 | Home decoration data processing method, system, storage medium and equipment |
| CN115567296A (en) * | 2022-09-26 | 2023-01-03 | 北京树米网络科技有限公司 | A processing method for application interface protection |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| CN112333198B (en) | Secure cross-domain login method, system and server | |
| CN110839004A (en) | Method and apparatus for access authentication | |
| CN112039826B (en) | Login method and device applied to applet end, electronic equipment and readable medium | |
| CN107888656B (en) | The calling method and calling device of the server interface | |
| EP4350556A1 (en) | Information verification method and apparatus | |
| CN113761566B (en) | A data processing method and device | |
| CN110149354A (en) | An encryption authentication method and device based on https protocol | |
| CN116112172B (en) | Android client gRPC interface security verification method and device | |
| US11977620B2 (en) | Attestation of application identity for inter-app communications | |
| CN109743161B (en) | Information encryption method, electronic device and computer readable medium | |
| CN108923925B (en) | Data storage method and device applied to block chain | |
| CN112560003A (en) | User authority management method and device | |
| CN114500054A (en) | Service access method, service access device, electronic device, and storage medium | |
| CN114553570B (en) | Method, device, electronic equipment and storage medium for generating token | |
| CN109150790B (en) | Web page crawler identification method and device | |
| CN111416788B (en) | Method and device for preventing transmission data from being tampered with | |
| CN108881122A (en) | The method and apparatus of APP Information Authentication | |
| CN112966286B (en) | Method, system, device and computer readable medium for user login | |
| CN113761549B (en) | Interface safety control and verification method and device | |
| CN112565156B (en) | Information registration method, device and system | |
| CN110098921A (en) | Verification code generation method, device, application service end and system | |
| CN114428967B (en) | Data transmission method, device, equipment and storage medium | |
| CN110602074B (en) | A method, device and system for using business identity based on master-slave association | |
| CN110858243A (en) | Page acquisition method and device for gateway | |
| CN114386073A (en) | Method, apparatus, electronic device, and storage medium for creating a security certificate |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| PB01 | Publication | ||
| PB01 | Publication | ||
| SE01 | Entry into force of request for substantive examination | ||
| SE01 | Entry into force of request for substantive examination | ||
| RJ01 | Rejection of invention patent application after publication |
Application publication date: 20200225 |
|
| RJ01 | Rejection of invention patent application after publication |