CN110136045B - A Method of Concealment and Restoration Based on Mutual Scrambling of Two Images - Google Patents
A Method of Concealment and Restoration Based on Mutual Scrambling of Two Images Download PDFInfo
- Publication number
- CN110136045B CN110136045B CN201910311263.7A CN201910311263A CN110136045B CN 110136045 B CN110136045 B CN 110136045B CN 201910311263 A CN201910311263 A CN 201910311263A CN 110136045 B CN110136045 B CN 110136045B
- Authority
- CN
- China
- Prior art keywords
- image
- images
- pixel
- sub
- pairs
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Expired - Fee Related
Links
Images
Classifications
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F21/60—Protecting data
- G06F21/602—Providing cryptographic facilities or services
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06T—IMAGE DATA PROCESSING OR GENERATION, IN GENERAL
- G06T1/00—General purpose image data processing
- G06T1/0021—Image watermarking
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06T—IMAGE DATA PROCESSING OR GENERATION, IN GENERAL
- G06T2201/00—General purpose image data processing
- G06T2201/005—Image watermarking
- G06T2201/0203—Image watermarking whereby the image with embedded watermark is reverted to the original condition before embedding, e.g. lossless, distortion-free or invertible watermarking
Landscapes
- Engineering & Computer Science (AREA)
- Theoretical Computer Science (AREA)
- General Physics & Mathematics (AREA)
- Physics & Mathematics (AREA)
- General Health & Medical Sciences (AREA)
- Computer Hardware Design (AREA)
- Computer Security & Cryptography (AREA)
- Software Systems (AREA)
- General Engineering & Computer Science (AREA)
- Health & Medical Sciences (AREA)
- Bioethics (AREA)
- Facsimile Transmission Control (AREA)
- Editing Of Facsimile Originals (AREA)
- Two-Way Televisions, Distribution Of Moving Picture Or The Like (AREA)
Abstract
Description
技术领域technical field
本发明属于保密通信与图像信息处理技术领域,具体涉及一种图像信息隐藏与恢复方法。The invention belongs to the technical field of secure communication and image information processing, and in particular relates to an image information hiding and restoring method.
背景技术Background technique
随着互联网数字多媒体技术的发展,信息的安全性问题由于涉及个人隐私、商业利益以及国家机密等领域而显得越来越重要。因此,对传输的信息进行可靠的加密处理,已成为当前信息安全领域最重要的研究方向。With the development of Internet digital multimedia technology, information security issues are becoming more and more important because they involve personal privacy, commercial interests, and state secrets. Therefore, reliable encryption of transmitted information has become the most important research direction in the field of information security.
由于数字图像的数据量大以及由视觉引起的易迷惑性等特性,以图像为载体的信息加密技术成为信息安全传输的研究热点之一。对图像隐藏的其中一个技术是对其置乱,即发送方借助数学或其它技术,对待隐藏的数字图像作变换使之变成一幅肉眼无法识辨的图像后再用于传输;在图像传输过程中,即使被非法身份者截获但无仍法从图像中获得原图像的信息,从而达到图像加密的目的。接收方可通过预定的方法进行解密,从而恢复原出图像。置乱加密过程可在图像的位置空间和颜色空间,即空间域上进行,也可在其频率域上进行,甚至可在空间域和频率域同时进行。故该加密方法灵活多样,合法使用者可自由控制算法的选择、参数的选择以及使用随机数技术,大大增加非法截获者的破译难度。Due to the large amount of data of digital images and the easy confusion caused by vision, information encryption technology using images as carriers has become one of the research hotspots in information security transmission. One of the techniques for hiding images is to scramble them, that is, the sender uses mathematics or other techniques to transform the hidden digital image so that it becomes an image that cannot be recognized by the naked eye before being used for transmission; In the process, even if it is intercepted by an illegal identity person, the information of the original image cannot be obtained from the image, so as to achieve the purpose of image encryption. The receiving party can decrypt through a predetermined method, so as to restore the original image. The scrambling encryption process can be carried out in the position space and color space of the image, that is, in the space domain, and can also be carried out in its frequency domain, and can even be carried out in both the space domain and the frequency domain. Therefore, the encryption method is flexible and diverse, and legal users can freely control the selection of algorithms, parameter selection and use of random number technology, which greatly increases the difficulty of deciphering for illegal interceptors.
现有的图像置乱的算法大的方面可分为基于图像位置空间、基于图像色彩空间和基于图像频域空间的置乱。具体地,基于图像位置空间的经典置乱方法如基于Arnold变换、Hilbert 曲线、幻方变换、队列变换等图像置乱方法。基于色彩空间的图像置乱方法如基于混沌序列、 Gray码的图像置乱等方法。以上这些方法都是基于单个图像的,对基于多个图像的置乱研究相对较少,本发明提出了基于两个图像的置乱方法,具有破译难度大、图像信息传输效率高等优点。The existing image scrambling algorithms can be divided into scrambling based on image position space, image color space and image frequency domain space. Specifically, classical scrambling methods based on image position space, such as image scrambling methods based on Arnold transformation, Hilbert curve, magic square transformation, queue transformation, etc. Image scrambling methods based on color space, such as image scrambling based on chaotic sequence and Gray code, etc. The above methods are all based on a single image, and there are relatively few studies on scrambling based on multiple images. The present invention proposes a scrambling method based on two images, which has the advantages of high difficulty in deciphering and high image information transmission efficiency.
发明内容Contents of the invention
本发明的发明目的在于:针对上述存在的问题,提供一种基于广义中国余数定理的两图像互置乱隐藏及恢复的方案。The object of the present invention is to provide a scheme for mutual scrambling, hiding and restoration of two images based on the generalized Chinese remainder theorem for the above-mentioned problems.
本发明首先将两张图片的像素通过若干两两互质的模,然后将这些像素按原来的位置构成子图像,其中相同模的两张图片称为同模对图像。在图像置乱加密阶段,将得到两组图像的部分同模对的像素互换。然后分别进行传输。在接收端,通过广义的中国余数定理,首先恢复出两个无序的像素对。然后根据接收到的图像的,分别确定出两个图像对应的像素。In the present invention, the pixels of the two pictures are firstly passed through several pairs of mutually prime modes, and then these pixels are formed into sub-images according to the original positions, wherein the two pictures of the same mode are called the same mode pair images. In the phase of image scrambling and encryption, the pixels of the partial identical model pairs of the two sets of images are exchanged. Then transfer them separately. At the receiving end, through the generalized Chinese remainder theorem, two disordered pixel pairs are recovered first. Then, according to the received images, the pixels corresponding to the two images are respectively determined.
本发明的基于两图像互置乱隐藏方法,是通过一种基于广义中国余数定理方法的技术方案来实现的,其具体包含以下步骤:The hiding method based on mutual scrambling of two images of the present invention is realized through a technical solution based on the generalized Chinese remainder theorem method, which specifically includes the following steps:
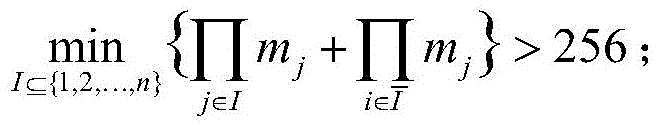
步骤1:选取适当的两两互质的模m1,m2,...,mn,使得图像中的任一像素对可在该组模下能唯一地被恢复出,基于广义中国余数定理,本发明中,所选取的模应满足如下关系式:其中,n表示所选取的模的数量。Step 1: Select an appropriate pairwise coprime modulus m 1 ,m 2 ,...,m n , so that any pixel pair in the image can be uniquely recovered under this modulus, based on the generalized Chinese remainder Theorem, in the present invention, the selected module should satisfy following relational expression: Among them, n represents the number of modules selected.
步骤2:对待互置处理的两幅图像分别用图像A、B表示,且图像A、B的图像尺寸相同;Step 2: The two images to be processed with each other are represented by images A and B respectively, and the image sizes of images A and B are the same;
对图像A的所有像素关于m1,m2,...,mn分别取模运算,得到每个像素取模后的像素值ai,j: ai,j≡pi mod mj,i=1,2,...,S,j=1,2,...,n,其中,pi表示图像A的第i个像素点的像素值,S表示互置图像的像素点数;Perform modulo operations on all pixels of image A with respect to m 1 , m 2 ,...,m n respectively, and obtain the pixel value a i,j after modulus of each pixel: a i,j ≡p i mod m j , i=1,2,...,S,j=1,2,...,n, wherein, p i represents the pixel value of the i-th pixel of the image A, and S represents the number of pixels of the mutual image;
从而得到关于不同模mj的取模运算后的图像(即图像A的子图):A1,A2,...,An;Thus obtain the image after the modulus operation of different modulus m j (ie, the sub-image of image A): A 1 , A 2 ,...,A n ;
步骤3:对图像B的所有像素关于m1,m2,...,mn分别取模运算,得到每个像素取模后的像素值值bi,j:bi,j≡qimodmj,i=1,2,...,S,j=1,2,...,n;其中,qi表示图像B的第i个像素点的像素值;Step 3: Perform modulo operations on all pixels of image B with respect to m 1 , m 2 ,...,m n respectively, and obtain the pixel value b i,j after modulo of each pixel: b i,j ≡q i modm j ,i=1,2,...,S,j=1,2,...,n; where, q i represents the pixel value of the i-th pixel of image B;
从而得到关于不同模mj的取模运算后的图像(即图像B的子图):B1,B2,...,Bn;Thereby obtain the image after the modulus operation of different modulus m j (ie the subgraph of image B): B 1 , B 2 ,..., B n ;
步骤4:从n对图像对(A1,B1),…,(An,Bn)中,随机选取t对图像对作为部分像素互换的对象,即将待进行部分像素(随机选取子图中的部分像素点作为待互换像素点)互换的图像对中的同一像素点位置的像素进行互换,从而得到互换后的图像对 Step 4: Randomly select t pairs of image pairs from n pairs of image pairs (A 1 ,B 1 ),…,(A n ,B n ) As the object of partial pixel exchange, the pixels at the same pixel position in the image pair to be exchanged (randomly select some pixels in the sub-image as the pixels to be exchanged) are exchanged, so as to obtain the exchange Image pair after swapping
步骤5:经过步骤4的互换处理后,得到互换处理后的加密图像:Step 5: After the exchange processing in step 4, the encrypted image after the exchange processing is obtained:
属于A的n个子图像序列: A sequence of n subimages belonging to A:
属于B的n个子图像序列: A sequence of n subimages belonging to B:
为了进一步保证两图像能从置乱后的子图像中完整地恢复出来,本发明中,可设置t小于取上整后的值。In order to further ensure that the two images can be completely recovered from the scrambled sub-images, in the present invention, t can be set to be less than Take the rounded value.
本发明的上述通过互换处理方式的图像加密方法,所带来的技术效果为:The technical effect brought by the above-mentioned image encryption method by exchanging processing methods of the present invention is:
(1)通过充分利用给定的两个图像及它们子图像的信息来达到信息隐藏的目的,由于整个系统不需要额外的其它图像,故大大降低了系统的设计难度。(1) The purpose of information hiding is achieved by making full use of the information of the given two images and their sub-images. Since the entire system does not require additional images, the difficulty of system design is greatly reduced.
(2)基于广义中国余数定理的两幅图像置乱方法,由于非法用户无法确定哪些图像对以及图像对中的哪些像素点互换了,故无法用传统的中国剩余定理方法或搜索的法等去准确恢复出两幅图像,大大增加了非法用户的破译难度。(2) The method of scrambling two images based on the generalized Chinese remainder theorem, because illegal users cannot determine which image pairs and which pixels in the image pairs have been exchanged, it is impossible to use the traditional Chinese remainder theorem method or search method Accurately recovering two images greatly increases the difficulty of deciphering for illegal users.
(3)基于广义中国余数定理的两图像置乱方法在图像信息隐藏的整个过程中,没有额外附加多余的信息,故增加了图像信息的传输效率。(3) The two-image scrambling method based on the generalized Chinese remainder theorem does not add redundant information during the whole process of image information hiding, so the transmission efficiency of image information is increased.
对应本发明的基于两图像互置乱隐藏方法,本发明还公开了一种基于广义中国余数定理的两图像恢复方法,其包括如下步骤:Corresponding to the concealment method based on mutual scrambling of two images of the present invention, the present invention also discloses a restoration method of two images based on the generalized Chinese remainder theorem, which includes the following steps:
步骤1:对接收到的基于两图像互置乱隐藏方法处理后的两组子图像序列(每组子图序列对应一幅待恢复图像),按序对两组子图像序列的子图进行组合,得到多对图相对,记为其中,分别表示两组子图像序列中序列相同的两副子图,且j=1,2,...,n,n表示图像对数量;Step 1: For the received two sets of sub-image sequences processed based on the two-image mutual scrambling hiding method (each set of sub-image sequences corresponds to an image to be restored), the sub-images of the two sets of sub-image sequences are combined in sequence , to get multiple pairs of graphs relative to each other, denoted as in, represent two subimages with the same sequence in the two subimage sequences respectively, and j=1,2,...,n, n represents the number of image pairs;
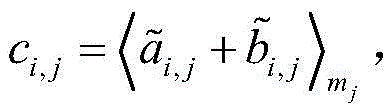
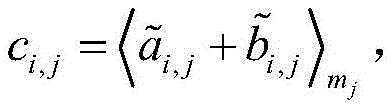
以图像对为单位,根据公式计算每对图像对中的相同像素点的像素值之和关于mj取模后的余数ci,j:其中,表示子图像在第i个像素点的像素值,表示子图像在第i个像素点的像素值,j=1,2,...,n,m1,m2,...,mn表示两图像互置乱隐藏方法处理中的n个两两互质的模,符号表示x关于mj取模后的余数。Taking the image pair as the unit, calculate the remainder c i,j of the sum of the pixel values of the same pixel in each image pair with respect to m j modulo according to the formula: in, Represents a sub-image The pixel value of the i-th pixel point, Represents a sub-image The pixel value at the i-th pixel point, j=1, 2,..., n, m 1 , m 2 ,..., m n represent the n pairwise mutual quality model, symbol Indicates the remainder after taking the modulus of x with respect to m j .
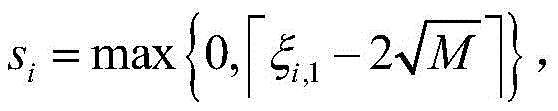
步骤2:记M=m1m2...mn,Mi=M/mi且满足并计算以下两个参数:Step 2: record M=m 1 m 2 ... m n , M i =M/m i and Satisfy and calculate the following two parameters:
其中, 为上取整函数。in, is the upper integer function.
步骤3:求解方程(x-si)2-(ξi,1-2si)(x-si)+ξi,2=0的两个根:{xi,1,xi,2}。Step 3: Solve the two roots of the equation (xs i ) 2 −(ξ i,1 −2s i )(xs i )+ξ i,2 =0: { xi,1 , xi,2 }.
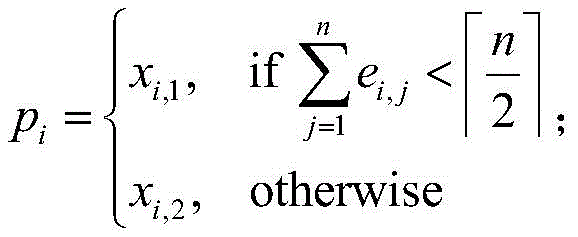
步骤4:确定待恢复图像对各自的像素:Step 4: Determine the respective pixels of the image to be restored:
根据公式计算参数ej;确定子图像对应的待恢复图像A的每个像素pi: According to the formula Compute parameter e j ; determine subimage Corresponding to each pixel p i of image A to be restored:
确定子图像对应的待恢复图像B的每个像素qi:qi={xi,1,xi,2}\{pi}。Determine the sub-image Corresponding to each pixel q i of the image B to be restored: q i ={ xi,1 , xi,2 }\{p i }.
步骤5:基于步骤4所确定的每幅恢复图像各自的像素,得到恢复图像A和B,即恢复出两组子图像序列各自对应的原图A和B。Step 5: Based on the respective pixels of each restored image determined in step 4, the restored images A and B are obtained, that is, the original images A and B respectively corresponding to the two sub-image sequences are restored.
综上所述,由于采用了上述技术方案,本发明的有益效果是:In summary, owing to adopting above-mentioned technical scheme, the beneficial effect of the present invention is:
与现有的图像恢复方法相比,本发明提出基于广义中国余数定理的两幅图像置乱恢复方法和系统具有如下的优点。Compared with the existing image restoration method, the two image scrambling restoration method and system proposed by the present invention based on the generalized Chinese remainder theorem have the following advantages.
1、本发明充分利用给定的两个图像及它们子图像的信息来达到信息隐藏的目的,由于整个系统不需要额外的其它图像,故大大降低了系统的设计难度。1. The present invention makes full use of the information of the given two images and their sub-images to achieve the purpose of information hiding. Since the entire system does not require additional images, the design difficulty of the system is greatly reduced.
2、本发明提供的基于广义中国余数定理的两幅图像置乱方法,由于非法用户无法确定哪些图像对以及图像对中的哪些像素点互换了,故无法用传统的中国剩余定理方法或搜索的法等去准确恢复出两幅图像,大大增加了非法用户的破译难度。2. The method for scrambling two images based on the generalized Chinese remainder theorem provided by the present invention cannot use the traditional Chinese remainder theorem method or search method because illegal users cannot determine which image pairs and which pixels in the image pairs have been exchanged. To accurately restore the two images by other methods, it greatly increases the difficulty of deciphering for illegal users.
3、本发明提供的基于广义中国余数定理的两图像置乱方法在图像信息隐藏的整个过程中,没有额外附加多余的信息,故增加了图像信息的传输效率。3. The two-image scrambling method based on the generalized Chinese remainder theorem provided by the present invention does not add redundant information during the entire process of image information hiding, so the transmission efficiency of image information is increased.
4、本发明提供的基于广义中国余数定理的两图像置乱的恢复方法高效,所需的运算量小。4. The restoration method of the scrambling of two images based on the generalized Chinese remainder theorem provided by the present invention is highly efficient and requires a small amount of computation.
附图说明Description of drawings
图1为具体实施方式中,两图像互置乱隐藏的处理流程示意图;Fig. 1 is a schematic diagram of the processing flow of mutual scrambling and hiding of two images in a specific embodiment;
图2为具体实施方式中,对两图像互置乱隐藏处理后的两组子图像序列的回复处理流程示意图;Fig. 2 is a schematic diagram of the reply processing flow of two groups of sub-image sequences after mutual scrambling and concealment processing of two images in a specific embodiment;
图3为具体实施方式中,对图像A(命名为Lena)进行取模运算后的图像:图中A1~A5 所示的子图像;Fig. 3 is the image after performing modulo operation on the image A (named Lena) in the specific embodiment: the sub-images shown in A1-A5 in the figure;
图4为具体实施方式中,对图像(命名为Zelda)进行取模运算后的图像:图中B1~B5 所示的子图像;Fig. 4 is in the specific embodiment, the image (named as Zelda) after carrying out modulus operation to the image: the sub-image shown in B1~B5 among the figure;
图5为具体实施方式中,对子图像对A4与B4,A5和B5中的部分对应位置的像素置换后的子图像;Fig. 5 is in the specific embodiment, the sub-image after sub-image is replaced by the pixel of part corresponding position in sub-image pair A4 and B4, A5 and B5;
图6为具体实施方式中,采用中国余数定理方法恢复后的两幅图像;Fig. 6 is in the specific embodiment, adopts two images after the Chinese remainder theorem method restores;
图7为具体实施方式中,采用本发明的用广义中国余数定理方法恢复后的两幅图像。Fig. 7 shows two images restored by using the generalized Chinese remainder theorem method of the present invention in the specific implementation manner.
具体实施方式detailed description
为使本发明的目的、技术方案和优点更加清楚,下面结合实施方式和附图,对本发明作进一步地详细描述。In order to make the purpose, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the implementation methods and accompanying drawings.
参见图1、图3和图4,为了实现对待传输图像A和图像B两幅图像的互置乱隐藏,即实现对图像对(A,B)的互加密处理,其具体实现过程如下:Referring to Fig. 1, Fig. 3 and Fig. 4, in order to realize the mutual scrambling and hiding of the two images of the image A and the image B to be transmitted, that is to realize the mutual encryption processing of the image pair (A, B), the specific implementation process is as follows:
首先,设置一组两两互质的模(也称素数)m1,m2,...,mn,且其中j=1,2,...,n;本具体实施方式中,设置了一组包括5个模的模组,其依次分别为:4,5, 7,11,13;该组模将共享于图像接收端,用于图像的恢复处理;Firstly, set a set of pairwise coprime modules (also called prime numbers) m 1 ,m 2 ,...,m n , and Wherein j=1,2,...,n; In this embodiment, a group of modules comprising 5 modules is set, which are respectively: 4,5,7,11,13; Shared at the image receiving end for image recovery processing;
再分别将图像A和B关于两两互质的素数m1,m2,...,m5分别取模后得到两组子图像,分别记为A1~A5,以及B1~B5,如图3、4所示;其中图像A和B的尺寸相同,本具体实施方式中,均为512×512。Then take the modulus of images A and B with respect to the pairwise prime numbers m 1 , m 2 ,...,m 5 respectively, and then obtain two groups of sub-images, which are respectively marked as A1~A5 and B1~B5, as shown in the figure 3 and 4; where images A and B have the same size, in this embodiment, they are both 512×512.
然后从这两组子图像中取出t对子图:和 和和为了保证两图像能从置乱后的子图像中完整地恢复出来,要求t小于取上整后的值。将这t对图像对应位置的像素部分互换,得到t对新的子图分别记为和 和和进而得到关于模m1,m2,...,mn的两组子图分别为:和 Then take t pairs of subgraphs from these two sets of subimages: with with with In order to ensure that the two images can be completely recovered from the scrambled sub-image, it is required that t be less than Take the rounded value. Swap the pixels of the corresponding positions of the t pairs of images to obtain t pairs of new subimages, respectively denoted as with with with Then two groups of subgraphs about modulus m 1 , m 2 ,...,m n are obtained: with
本具体实施方式中,设置t的取值为2,互换的子图像对设置为:A4与B4,A5和B5,从而得到如图5所示的互置乱隐藏后的两组子图;并对两组子图像序列发送至接收端。In this specific embodiment, the value of setting t is 2, and the sub-image pair of interchange is set to: A4 and B4, A5 and B5, thereby obtain two groups of sub-images after mutual scrambling and hiding as shown in Figure 5; And send the two groups of sub-image sequences to the receiving end.
参见图2,对于收到的两组子图像序列:和本发明利用广义的中国余数定理恢复出两图像的像素对后再根据图像的特征找出对应的像素。See Figure 2, for the two received sub-image sequences: with The invention recovers the pixel pairs of the two images by using the generalized Chinese remainder theorem, and then finds the corresponding pixels according to the features of the images.
其具体过程如下:The specific process is as follows:
首先对按序构成的子图像对,计算同一像素点位置的像素值之和关于对应的模的取模后的余数,通过序列索引匹配对应的模,例如对于第一对子图像对,则匹配的模为m1,第二对对应m2,依次类推。First, for the sub-image pairs formed in order, calculate the remainder of the sum of the pixel values at the same pixel position with respect to the modulus of the corresponding modulus, and match the corresponding modulus through the sequence index, for example, for the first pair of sub-image pairs, then match The modulus of is m 1 , the second pair corresponds to m 2 , and so on.
再经过对应的运算处理从两组子图中准确恢复出所有无序的像素对{pi,qi},即根据求解方程(x-si)2-(ξi,1-2si)(x-si)+ξi,2=0得到的两个根{xi,1,xi,2}。然后根据图像的特征,将得到的像素对中的无序像素对准确地分类,即分别找出属于A和B的像素,待所有的像素都准确地分类后,原来两图像可以无损地恢复出,恢复结果如图7所示。After the corresponding operation processing, all unordered pixel pairs {p i ,q i } are accurately restored from the two sub-images, that is, according to the solution equation (xs i ) 2 -(ξ i,1 -2s i )(xs i )+ξ i,2 =0 to get two roots { xi,1 , xi,2 }. Then according to the characteristics of the image, the unordered pixel pairs in the obtained pixel pairs are accurately classified, that is, the pixels belonging to A and B are respectively found out. After all the pixels are accurately classified, the original two images can be restored without loss. , and the recovery results are shown in Figure 7.
与现有的采用中国余数定理方法恢复后的两幅图像相比(图6所示),本发明能高效、准确的恢复出所加密的图像,且运算量小。且由于非法用户无法确定哪些图像对以及图像对中的哪些像素点互换了,故无法用传统的中国剩余定理方法或搜索的法等去准确恢复出两幅图像,大大增加了非法用户的破译难度。Compared with the existing two images restored by the Chinese remainder theorem method (as shown in FIG. 6 ), the invention can efficiently and accurately restore the encrypted image with a small amount of computation. And because the illegal user cannot determine which image pairs and which pixels in the image pair have been exchanged, it is impossible to use the traditional Chinese remainder theorem method or search method to accurately recover the two images, which greatly increases the illegal user's deciphering. difficulty.
以上所述,仅为本发明的具体实施方式,本说明书中所公开的任一特征,除非特别叙述,均可被其他等效或具有类似目的的替代特征加以替换;所公开的所有特征、或所有方法或过程中的步骤,除了互相排斥的特征和/或步骤以外,均可以任何方式组合。The above is only a specific embodiment of the present invention. Any feature disclosed in this specification, unless specifically stated, can be replaced by other equivalent or alternative features with similar purposes; all the disclosed features, or All method or process steps may be combined in any way, except for mutually exclusive features and/or steps.
Claims (2)
Priority Applications (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN201910311263.7A CN110136045B (en) | 2019-04-18 | 2019-04-18 | A Method of Concealment and Restoration Based on Mutual Scrambling of Two Images |
Applications Claiming Priority (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN201910311263.7A CN110136045B (en) | 2019-04-18 | 2019-04-18 | A Method of Concealment and Restoration Based on Mutual Scrambling of Two Images |
Publications (2)
| Publication Number | Publication Date |
|---|---|
| CN110136045A CN110136045A (en) | 2019-08-16 |
| CN110136045B true CN110136045B (en) | 2022-12-20 |
Family
ID=67570295
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| CN201910311263.7A Expired - Fee Related CN110136045B (en) | 2019-04-18 | 2019-04-18 | A Method of Concealment and Restoration Based on Mutual Scrambling of Two Images |
Country Status (1)
| Country | Link |
|---|---|
| CN (1) | CN110136045B (en) |
Families Citing this family (3)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN110136046B (en) * | 2019-05-20 | 2024-07-05 | 北京宏硕数通科技有限公司 | Two-image scrambling hiding and reconstructing method with threshold |
| CN110473214B (en) * | 2019-08-19 | 2022-11-18 | 李小平 | Image scrambling and recovering method based on Ramanujan matrix |
| CN113222829B (en) * | 2021-02-25 | 2023-04-25 | 安徽师范大学 | Bernstein-based digital image splitting method and image restoration method |
Citations (9)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| WO2001052178A1 (en) * | 2000-01-13 | 2001-07-19 | Digimarc Corporation | Authenticating metadata and embedding metadata in watermarks of media signals |
| CN1471019A (en) * | 2003-06-26 | 2004-01-28 | 上海交通大学 | Digital Watermark Embedding and Extraction Method Based on Residue Image |
| JP2004064720A (en) * | 2002-06-03 | 2004-02-26 | Fujitsu Ltd | Binarization method, binarization device, image forming apparatus, binarization program, and computer-readable recording medium recording the program |
| WO2012120674A1 (en) * | 2011-03-10 | 2012-09-13 | Nttエレクトロニクス株式会社 | Memory access device |
| CN103761702A (en) * | 2014-01-09 | 2014-04-30 | 太原科技大学 | Image hiding and authentication method based on secret sharing |
| CN103903215A (en) * | 2014-01-27 | 2014-07-02 | 西安理工大学 | Multi-image encryption method based on chaos and FrFT domain phase retrieval process |
| CN106228504A (en) * | 2016-07-17 | 2016-12-14 | 西安电子科技大学 | Based on plaintext and the digital image encryption method of key structure encryption parameter |
| CN106910156A (en) * | 2017-02-27 | 2017-06-30 | 东北大学 | A kind of New chaotic image encryption method with plaintext association key stream generting machanism |
| CN107274458A (en) * | 2017-06-15 | 2017-10-20 | 东北林业大学 | Quantum multicolor image encryption algorithm based on chaos system |
Family Cites Families (1)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN101667285A (en) * | 2009-09-25 | 2010-03-10 | 上海大学 | Reversible data hiding method based on pixel grouping strategy |
-
2019
- 2019-04-18 CN CN201910311263.7A patent/CN110136045B/en not_active Expired - Fee Related
Patent Citations (9)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| WO2001052178A1 (en) * | 2000-01-13 | 2001-07-19 | Digimarc Corporation | Authenticating metadata and embedding metadata in watermarks of media signals |
| JP2004064720A (en) * | 2002-06-03 | 2004-02-26 | Fujitsu Ltd | Binarization method, binarization device, image forming apparatus, binarization program, and computer-readable recording medium recording the program |
| CN1471019A (en) * | 2003-06-26 | 2004-01-28 | 上海交通大学 | Digital Watermark Embedding and Extraction Method Based on Residue Image |
| WO2012120674A1 (en) * | 2011-03-10 | 2012-09-13 | Nttエレクトロニクス株式会社 | Memory access device |
| CN103761702A (en) * | 2014-01-09 | 2014-04-30 | 太原科技大学 | Image hiding and authentication method based on secret sharing |
| CN103903215A (en) * | 2014-01-27 | 2014-07-02 | 西安理工大学 | Multi-image encryption method based on chaos and FrFT domain phase retrieval process |
| CN106228504A (en) * | 2016-07-17 | 2016-12-14 | 西安电子科技大学 | Based on plaintext and the digital image encryption method of key structure encryption parameter |
| CN106910156A (en) * | 2017-02-27 | 2017-06-30 | 东北大学 | A kind of New chaotic image encryption method with plaintext association key stream generting machanism |
| CN107274458A (en) * | 2017-06-15 | 2017-10-20 | 东北林业大学 | Quantum multicolor image encryption algorithm based on chaos system |
Non-Patent Citations (8)
| Title |
|---|
| Sathishkumar G.A..Image Encryption using random pixel permutation by chaotic mapping.《2012 IEEE Symposium on Computer&Informatic》.2012, * |
| Shyong Jian Shyu.Threshold Secret Image Sharing by Chinese Remainder Thorem.《2008 IEEE Asia-Pacific Services Conference》.2008, * |
| Wei Wang.The Largest Dynamic Range of a Generalized Chinese Remainder Theorem for Two Integers.《IEEE Signal Processing Letters》.2015,第22卷(第2期), * |
| Xiaoping Li.A Secret Image Restoring Scheme Using Threshold Pairs of Unordered Image Shares.《IEEE Access》.2019,第7卷 * |
| Yan Ke.A Reversible Data Hiding Scheme in Encrypted Domain for Secret Image Sharing Based on Chinese Remainder.《IEEE Transactions on Circuits and Systems for Video Technology》.2022,第32卷(第4期), * |
| 一种基于抖动和混沌技术的数字图像篡改检测及修复算法;王兴元;《物理学报》;20141231;第63卷(第21期);第210701-1-8页 * |
| 一种多门限秘密图像共享机制的研究;张欢;《中国优秀硕士学位论文全文数据库 (信息科技辑)》;20160315;第1-46页 * |
| 基于物理随机位生成器与混沌像素交叉互换的图像加密算法;郭静博;《包装工程》;20180731;第39卷(第13期);第222-232页 * |
Also Published As
| Publication number | Publication date |
|---|---|
| CN110136045A (en) | 2019-08-16 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| Zhan et al. | Cross-utilizing hyperchaotic and DNA sequences for image encryption | |
| Yang et al. | Property analysis of XOR-based visual cryptography | |
| CN107220923B (en) | Digital picture feedback encryption method based on image network | |
| CN104200424B (en) | Difference conversion based (K, N) meaningful image sharing and recovering method | |
| CN110136045B (en) | A Method of Concealment and Restoration Based on Mutual Scrambling of Two Images | |
| CN103023633B (en) | Digital image hiding method based on chaotic random phase and coherence stack principle | |
| CN103646264A (en) | Multiple information encrypted two-dimensional code anti-counterfeiting method | |
| Guo et al. | A multi-threshold secret image sharing scheme based on MSP | |
| CN103455971A (en) | Image encryption method combining three-dimensional Arnold transformation with chaotic sequence | |
| CN105450899B (en) | Multiple image encryption method based on PWLCM chaos | |
| Yang et al. | Reduce shadow size in aspect ratio invariant visual secret sharing schemes using a square block-wise operation | |
| CN104063833B (en) | A kind of image encryption, read method and device | |
| CN113014742B (en) | Image tampering detection positioning and self-recovery method based on fragile watermark | |
| CN112330521B (en) | A method for image encryption | |
| CN116827509A (en) | Image encryption method based on five-dimensional conserved hyperchaotic system and bit plane segmentation diffusion | |
| CN105812614B (en) | More image encryptions and decryption method based on optical field imaging with digital refocusing technology | |
| CN103971320B (en) | A kind of image scrambling and restoration methods based on Henon mappings | |
| CN103971321B (en) | Method and system for steganalysis of JPEG compatibility | |
| CN104702814B (en) | (K, N) Image of Meaningful based on triple backups point is deposited and restoration methods | |
| CN110335218B (en) | Confidential image recovery method based on redundant remainder system | |
| CN111400731A (en) | DNACNott-based quantum image encryption method | |
| Sarkar et al. | Blockchain-based authenticable (k, n) multi-secret image sharing scheme | |
| CN109948353A (en) | Asymmetric multi-image encryption method, device and storage medium | |
| CN110136046B (en) | Two-image scrambling hiding and reconstructing method with threshold | |
| CN109558701B (en) | A method for secret sharing of medical CT images |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| PB01 | Publication | ||
| PB01 | Publication | ||
| SE01 | Entry into force of request for substantive examination | ||
| SE01 | Entry into force of request for substantive examination | ||
| GR01 | Patent grant | ||
| GR01 | Patent grant | ||
| CF01 | Termination of patent right due to non-payment of annual fee |
Granted publication date: 20221220 |
|
| CF01 | Termination of patent right due to non-payment of annual fee |