CN109753769B - Software authorization method and system based on block chain - Google Patents
Software authorization method and system based on block chain Download PDFInfo
- Publication number
- CN109753769B CN109753769B CN201811405865.0A CN201811405865A CN109753769B CN 109753769 B CN109753769 B CN 109753769B CN 201811405865 A CN201811405865 A CN 201811405865A CN 109753769 B CN109753769 B CN 109753769B
- Authority
- CN
- China
- Prior art keywords
- software
- information
- blockchain
- module
- authorization
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Active
Links
Images
Landscapes
- Storage Device Security (AREA)
- Management, Administration, Business Operations System, And Electronic Commerce (AREA)
Abstract
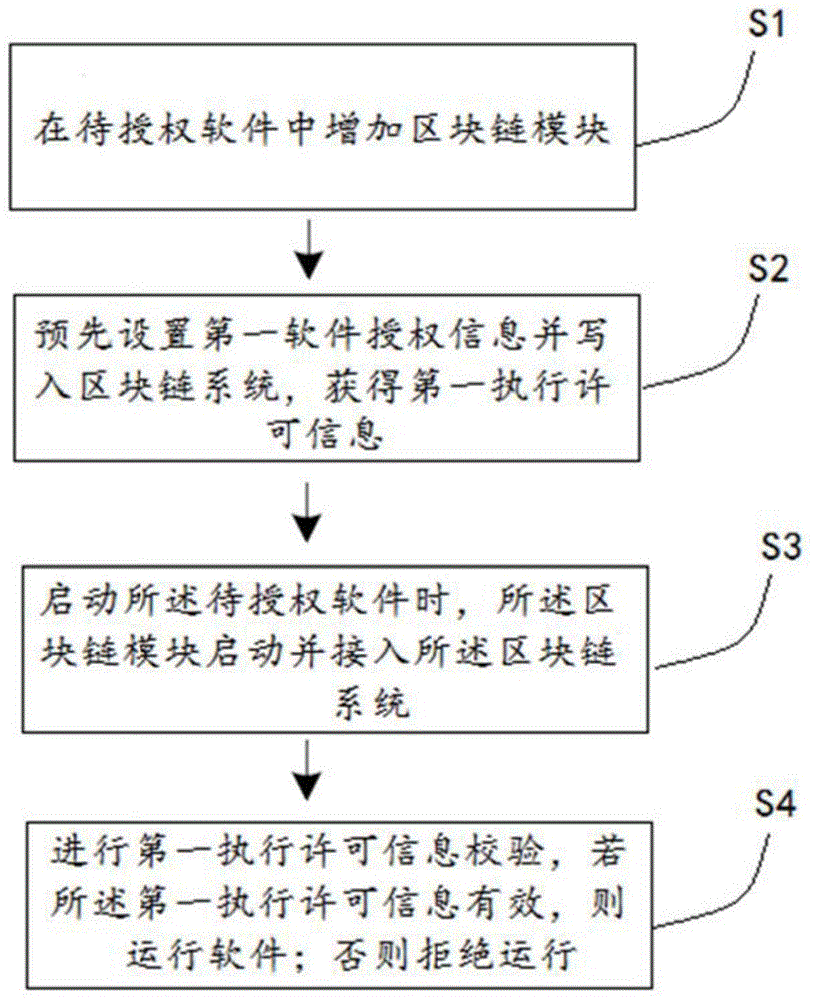
本发明公开了一种基于区块链的软件授权方法及系统,该方法包括:在待授权软件中增加区块链模块;预先设置第一软件授权信息并写入区块链系统获得第一执行许可信息;启动待授权软件时,区块链模块启动并接入区块链系统;进行第一执行许可信息校验,若第一执行许可信息有效,则运行软件,否则拒绝启动;区块链系统用以管理软件授权信息。本发明中软件通过区块链进行授权,利用区块链的特性,使得该软件授权方法通用性强,授权后的软件安全性高,任何通过私自拷贝、重置授权信息等非法行为进行软件盗版的,都将导致软件无法通过在区块链的授权验证而无法运行,由于区块链的特性,使得妄图以通过破解区块链的方式对软件进行破解,几乎是不可能的。
The invention discloses a block chain-based software authorization method and system. The method includes: adding a block chain module to the software to be authorized; presetting first software authorization information and writing it into the block chain system to obtain the first execution License information; when starting the software to be authorized, the blockchain module starts and accesses the blockchain system; the first execution permission information is verified, if the first execution permission information is valid, the software is run, otherwise it refuses to start; blockchain The system is used to manage software authorization information. In the present invention, the software is authorized through the block chain, and the characteristics of the block chain are used, so that the software authorization method has strong versatility, and the authorized software has high security. It will cause the software to fail to pass the authorization verification in the blockchain and cannot run. Due to the characteristics of the blockchain, it is almost impossible to attempt to crack the software by cracking the blockchain.
Description
Claims (7)
Priority Applications (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN201811405865.0A CN109753769B (en) | 2018-11-23 | 2018-11-23 | Software authorization method and system based on block chain |
Applications Claiming Priority (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN201811405865.0A CN109753769B (en) | 2018-11-23 | 2018-11-23 | Software authorization method and system based on block chain |
Publications (2)
| Publication Number | Publication Date |
|---|---|
| CN109753769A CN109753769A (en) | 2019-05-14 |
| CN109753769B true CN109753769B (en) | 2021-03-02 |
Family
ID=66402554
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| CN201811405865.0A Active CN109753769B (en) | 2018-11-23 | 2018-11-23 | Software authorization method and system based on block chain |
Country Status (1)
| Country | Link |
|---|---|
| CN (1) | CN109753769B (en) |
Families Citing this family (2)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN112241518A (en) * | 2020-10-22 | 2021-01-19 | 广州市金其利信息科技有限公司 | Software authority management method and system based on block chain |
| CN113868691B (en) * | 2021-12-02 | 2022-05-24 | 北京溪塔科技有限公司 | Authorized operation method and device of block chain based on cloud-native technology |
Citations (12)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN103258151B (en) * | 2012-10-30 | 2016-01-20 | 中国科学院沈阳自动化研究所 | A kind of software License control method of real-time authorization |
| US20170132621A1 (en) * | 2015-11-06 | 2017-05-11 | SWFL, Inc., d/b/a "Filament" | Systems and methods for autonomous device transacting |
| CN106875254A (en) * | 2017-01-20 | 2017-06-20 | 暨南大学 | A kind of Android malicious application control methods based on block chain technology |
| US20170359374A1 (en) * | 2016-06-11 | 2017-12-14 | Lntel Corporation | Blockchain System with Nucleobase Sequencing as Proof of Work |
| US20180167198A1 (en) * | 2016-12-09 | 2018-06-14 | Cisco Technology, Inc. | Trust enabled decentralized asset tracking for supply chain and automated inventory management |
| US20180183687A1 (en) * | 2016-12-28 | 2018-06-28 | Acronis International Gmbh | System and Method for Managing Services and Licenses Using a Blockchain Network |
| CN108243182A (en) * | 2017-10-26 | 2018-07-03 | 招商银行股份有限公司 | Management authorization method, sub- management end, root management end and the storage medium of block chain |
| US20180211059A1 (en) * | 2017-01-23 | 2018-07-26 | Health2047, Inc. | Trust based access to records via encrypted protocol communications with authentication system |
| CN108389059A (en) * | 2018-02-26 | 2018-08-10 | 成都大学 | Digital copyrighted work protection, transaction and distributing method based on ownership and system |
| CN108573071A (en) * | 2018-05-09 | 2018-09-25 | 广东工业大学 | A file operation method and related device |
| US20180293363A1 (en) * | 2017-04-07 | 2018-10-11 | Cisco Technology, Inc. | Blockchain based software licensing enforcement |
| CN108665946A (en) * | 2018-05-08 | 2018-10-16 | 阿里巴巴集团控股有限公司 | A kind of access method and device of business datum |
Family Cites Families (3)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN103186725B (en) * | 2011-12-31 | 2016-10-05 | 北大方正集团有限公司 | software authorization method and device |
| CN108566374A (en) * | 2018-03-09 | 2018-09-21 | 深圳市元征科技股份有限公司 | A kind of application method for down loading and its system, block chain node device, terminal |
| CN108768618B (en) * | 2018-06-07 | 2021-05-11 | 广东工业大学 | A blockchain-based IP soft core authorization method, device and medium |
-
2018
- 2018-11-23 CN CN201811405865.0A patent/CN109753769B/en active Active
Patent Citations (12)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN103258151B (en) * | 2012-10-30 | 2016-01-20 | 中国科学院沈阳自动化研究所 | A kind of software License control method of real-time authorization |
| US20170132621A1 (en) * | 2015-11-06 | 2017-05-11 | SWFL, Inc., d/b/a "Filament" | Systems and methods for autonomous device transacting |
| US20170359374A1 (en) * | 2016-06-11 | 2017-12-14 | Lntel Corporation | Blockchain System with Nucleobase Sequencing as Proof of Work |
| US20180167198A1 (en) * | 2016-12-09 | 2018-06-14 | Cisco Technology, Inc. | Trust enabled decentralized asset tracking for supply chain and automated inventory management |
| US20180183687A1 (en) * | 2016-12-28 | 2018-06-28 | Acronis International Gmbh | System and Method for Managing Services and Licenses Using a Blockchain Network |
| CN106875254A (en) * | 2017-01-20 | 2017-06-20 | 暨南大学 | A kind of Android malicious application control methods based on block chain technology |
| US20180211059A1 (en) * | 2017-01-23 | 2018-07-26 | Health2047, Inc. | Trust based access to records via encrypted protocol communications with authentication system |
| US20180293363A1 (en) * | 2017-04-07 | 2018-10-11 | Cisco Technology, Inc. | Blockchain based software licensing enforcement |
| CN108243182A (en) * | 2017-10-26 | 2018-07-03 | 招商银行股份有限公司 | Management authorization method, sub- management end, root management end and the storage medium of block chain |
| CN108389059A (en) * | 2018-02-26 | 2018-08-10 | 成都大学 | Digital copyrighted work protection, transaction and distributing method based on ownership and system |
| CN108665946A (en) * | 2018-05-08 | 2018-10-16 | 阿里巴巴集团控股有限公司 | A kind of access method and device of business datum |
| CN108573071A (en) * | 2018-05-09 | 2018-09-25 | 广东工业大学 | A file operation method and related device |
Non-Patent Citations (2)
| Title |
|---|
| 区块链技术在版权保护中的应用实践;邹健;《https://www.infoq.cn/article/blockchain-in-copyright-protection》;20180418;正文全文 * |
| 区块链软件开发者需要注意的几种软件许可;Mark Radcliffe等;《https://www.infoq.cn/article/the-big-legal-issue-blockchain-developers-rarely-discuss》;20180922;正文全文 * |
Also Published As
| Publication number | Publication date |
|---|---|
| CN109753769A (en) | 2019-05-14 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| US20250356343A1 (en) | Non Fungible Token (NFT) Based Licensing and Digital Rights Management (DRM) for Software and Other Digital Assets | |
| US11218478B1 (en) | Security platform | |
| CN112861191B (en) | Application program monitoring method and device | |
| US8074287B2 (en) | Renewable and individualizable elements of a protected environment | |
| KR101537027B1 (en) | How to install security software and devices | |
| US20080295174A1 (en) | Method and System for Preventing Unauthorized Access and Distribution of Digital Data | |
| US9460272B2 (en) | Method and apparatus for group licensing of device features | |
| JP2003500722A (en) | Information protection method and device | |
| KR20200000448A (en) | Systems and methods for software activation and license tracking | |
| CN109446259B (en) | Data processing method and device, processor and storage medium | |
| KR20120051662A (en) | A method for controlling unauthorized software application usage | |
| CN113297595A (en) | Method and device for processing right-offering, storage medium and electronic equipment | |
| CN109753769B (en) | Software authorization method and system based on block chain | |
| CN108881132B (en) | Application authorization method, client, server and computer readable medium | |
| US7890756B2 (en) | Verification system and method for accessing resources in a computing environment | |
| CN112699344B (en) | Software authorization method based on block chain | |
| CN111143832A (en) | Mobile terminal SDK (software development kit) suitable for multiple scenes and hybrid authorization method thereof | |
| CN118041628A (en) | Access checking method and system of domain controller | |
| CN101167296B (en) | Updatable and Personalizable Elements of a Protected Computing Environment | |
| KR102317863B1 (en) | Methodology to protect copyright for images using blockchain technology | |
| KR101012054B1 (en) | Copyright management method of copyrighted works and its system | |
| CN117675317B (en) | Single sign-on method, system, electronic equipment and storage medium | |
| US20250131427A1 (en) | Bot prevention techniques | |
| KR101440234B1 (en) | The method and system for managing program integrity, and computer-radable recording medium storing program integrity management program recored theron | |
| HK40044561B (en) | An application program monitoring method and device |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| PB01 | Publication | ||
| PB01 | Publication | ||
| SE01 | Entry into force of request for substantive examination | ||
| SE01 | Entry into force of request for substantive examination | ||
| GR01 | Patent grant | ||
| GR01 | Patent grant | ||
| TR01 | Transfer of patent right | ||
| TR01 | Transfer of patent right |
Effective date of registration: 20240306 Address after: Room 1179, W Zone, 11th Floor, Building 1, No. 158 Shuanglian Road, Qingpu District, Shanghai, 201702 Patentee after: Shanghai Zhongan Information Technology Service Co.,Ltd. Country or region after: China Address before: 518000 Room 201, building A, No. 1, Qian Wan Road, Qianhai Shenzhen Hong Kong cooperation zone, Shenzhen, Guangdong (Shenzhen Qianhai business secretary Co., Ltd.) Patentee before: ZHONGAN INFORMATION TECHNOLOGY SERVICE Co.,Ltd. Country or region before: China |
|
| TR01 | Transfer of patent right | ||
| TR01 | Transfer of patent right |
Effective date of registration: 20240415 Address after: Room 1179, W Zone, 11th Floor, Building 1, No. 158 Shuanglian Road, Qingpu District, Shanghai, 201702 Patentee after: Shanghai Zhongan Information Technology Service Co.,Ltd. Country or region after: China Address before: 518000 Room 201, building A, No. 1, Qian Wan Road, Qianhai Shenzhen Hong Kong cooperation zone, Shenzhen, Guangdong (Shenzhen Qianhai business secretary Co., Ltd.) Patentee before: ZHONGAN INFORMATION TECHNOLOGY SERVICE Co.,Ltd. Country or region before: China |
|
| CP03 | Change of name, title or address | ||
| CP03 | Change of name, title or address |
Address after: 3F-24, Group A, Qianhai Shenzhen Hong Kong Innovation Center, No. 4008 Menghai Avenue, Nanshan Street, Qianhai Shenzhen Hong Kong Cooperation Zone, Shenzhen, Guangdong Province 518054 Patentee after: Zhong'an Xinke (Shenzhen) Co.,Ltd. Country or region after: China Address before: Room 1179, W Zone, 11th Floor, Building 1, No. 158 Shuanglian Road, Qingpu District, Shanghai, 201702 Patentee before: Shanghai Zhongan Information Technology Service Co.,Ltd. Country or region before: China |