CN108092776B - A system based on an authentication server and an authentication token - Google Patents
A system based on an authentication server and an authentication token Download PDFInfo
- Publication number
- CN108092776B CN108092776B CN201711261470.3A CN201711261470A CN108092776B CN 108092776 B CN108092776 B CN 108092776B CN 201711261470 A CN201711261470 A CN 201711261470A CN 108092776 B CN108092776 B CN 108092776B
- Authority
- CN
- China
- Prior art keywords
- module
- token
- key
- identity authentication
- signature
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Active
Links
Images
Classifications
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/32—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials
- H04L9/3271—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials using challenge-response
- H04L9/3278—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials using challenge-response using physically unclonable functions [PUF]
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/08—Network architectures or network communication protocols for network security for authentication of entities
- H04L63/0807—Network architectures or network communication protocols for network security for authentication of entities using tickets, e.g. Kerberos
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/32—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials
- H04L9/321—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials involving a third party or a trusted authority
- H04L9/3213—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials involving a third party or a trusted authority using tickets or tokens, e.g. Kerberos
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/32—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials
- H04L9/3247—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials involving digital signatures
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/08—Network architectures or network communication protocols for network security for authentication of entities
- H04L63/0853—Network architectures or network communication protocols for network security for authentication of entities using an additional device, e.g. smartcard, SIM or a different communication terminal
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/32—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials
- H04L9/3234—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials involving additional secure or trusted devices, e.g. TPM, smartcard, USB or software token
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/32—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials
- H04L9/3236—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials using cryptographic hash functions
Landscapes
- Engineering & Computer Science (AREA)
- Computer Security & Cryptography (AREA)
- Computer Networks & Wireless Communication (AREA)
- Signal Processing (AREA)
- Computer Hardware Design (AREA)
- Computing Systems (AREA)
- General Engineering & Computer Science (AREA)
- Management, Administration, Business Operations System, And Electronic Commerce (AREA)
Abstract
本发明公开了一种身份认证服务器和身份认证令牌,其特征是,身份认证服务器,包括相互连接的标准FIDO服务器和用于存储密钥的存储空间,即数据库;身份认证令牌,基于物理不可克隆与FIDO U2F协议,包括U2F模块、与U2F模块分别相连的PUF模块、TRNG模块、USB模块、交互模块,以及与交互模块连接的触摸模块;身份令牌与客户端浏览器进行交互,客户端浏览器又与身份认证服务器中的FIDO服务器进行交互。本发明采用物理不可克隆函数与FIDO相结合,以物理不可克隆函数保证令牌的唯一性,不可复制性,以FIDO保证用户身份的准确性以及所进行操作的不可篡改性、不可抵赖性。
The invention discloses an identity authentication server and an identity authentication token, which are characterized in that the identity authentication server includes a standard FIDO server connected to each other and a storage space for storing keys, namely a database; the identity authentication token is based on physical Unclonable and FIDO U2F protocol, including U2F module, PUF module connected to U2F module, TRNG module, USB module, interactive module, and touch module connected to interactive module; identity token interacts with client browser, customer The terminal browser interacts with the FIDO server in the authentication server. The invention adopts the combination of physical unclonable function and FIDO, guarantees the uniqueness and non-replicability of the token with the physical unclonable function, and guarantees the accuracy of the user's identity and the non-tampering and non-repudiation of the operation with FIDO.
Description
技术领域technical field
本发明属于身份认证安全技术领域,具体涉及一种基于身份认证服务器和身份认证令牌的系统。The invention belongs to the technical field of identity authentication security, in particular to a system based on an identity authentication server and an identity authentication token.
背景技术Background technique
随着全球能源互联网的不断发展,企业内部和企业之间的各类业务越来越多的依靠信息系统和网络平台展开。这种新形势对于人资管理、财务管理、生产管理、企业管理等电力企业的资源管理模式提出了越来越高的要求。电力企业信息系统中的核心业务,如人资业务中的人才引进涉及的人力资源的聘用、关键人才的企业间联动,财务管理中关键业务在企业内、企业间的财务往来业务,生产管理中的相关服务类和物资类的重点往来业务,企业内部、企业间的重点任务、重点专项资金的分配与下达,都是企业的重点关注点,客观上需要通过一定的手段确保相关内容的不可篡改性和不可抵赖性。With the continuous development of the global energy Internet, various businesses within and between enterprises are increasingly relying on information systems and network platforms. This new situation has put forward higher and higher requirements for the resource management modes of electric power enterprises such as human resources management, financial management, production management, and enterprise management. The core business in the information system of electric power enterprises, such as the recruitment of human resources involved in the introduction of talents in the human resources business, the inter-enterprise linkage of key talents, and the key business in financial management are the financial transactions within and between enterprises, and production management. The key business transactions of related services and materials, the key tasks within and between enterprises, and the allocation and release of key special funds are the key concerns of the enterprise. Objectively, it is necessary to ensure that the relevant content cannot be tampered with sex and non-repudiation.
保证企业员工有效控制处理企业的核心业务,并且处理过程不被篡改、不可抵赖,企业内、企业间优质资源在合法范围内通过便捷的信息化手段被监控,且在监控同时不受监控技术权限的影响,作为管理企业资源重点环节的技术手段成为能源互联网下的关键诉求。Ensure that the employees of the enterprise can effectively control the core business of the enterprise, and the processing process is not tampered with and non-repudiation, and the high-quality resources within the enterprise and between enterprises are monitored within the legal scope through convenient informatization means, and they are not subject to monitoring technical authority at the same time. As a technical means of managing the key links of enterprise resources, it has become a key demand under the Energy Internet.
FIDO(线上快速身份认证)是FIDO联盟提出的一套开放、可扩展、可协同的标准协议,旨在提供一个高安全性、跨平台兼容性、极佳用户体验与用户隐私保护的在线身份认证技术架构,来改变现有在线认证方式,减少认证用户时对密码的依赖。FIDO有两套规范:U2F(第二因子协议)和UAF。U2F是在现有的用户名+密码认证的基础之上,增加一个更安全的认证因子用于登录认证。用户可以像以前一样通过用户名和密码登录服务,服务会提示用户出示一个第二因子设备来进行认证。U2F可以使用简单的密码(比如4个数字的PIN)而不牺牲安全性。FIDO (Fast Online Identity Authentication) is a set of open, extensible and collaborative standard protocols proposed by the FIDO Alliance, aiming to provide an online identity with high security, cross-platform compatibility, excellent user experience and user privacy protection Authentication technology architecture to change the existing online authentication method and reduce the dependence on passwords when authenticating users. FIDO has two sets of specifications: U2F (Second Factor Protocol) and UAF. U2F is based on the existing user name + password authentication, adding a more secure authentication factor for login authentication. Users can log into the service with a username and password as before, and the service will prompt the user to present a second-factor device to authenticate. U2F can use simple passwords (such as a 4-digit PIN) without sacrificing security.
现有的FIDO U2F身份令牌有可能被破解,存在被恶意攻击者复制、克隆的可能,导致身份认证系统安全性的巨大风险。为了确保身份令牌的不可复制性,需引入新的技术。PUF(物理不可克隆技术)是一种依赖芯片特征的硬件函数实现电路,具有唯一性和随机性,通过提取芯片制造过程中必然引入的工艺参数偏差,实现激励信号与产生的不可预测的响应信号唯一对应的函数功能。在FIDO U2F身份令牌中集成PUF并应用其功能是一个值得探索的方向。The existing FIDO U2F identity token may be cracked, and may be copied or cloned by malicious attackers, resulting in a huge risk to the security of the identity authentication system. In order to ensure the non-replicability of identity tokens, new technologies need to be introduced. PUF (Physical Unclonable Technology) is a hardware function implementation circuit that relies on chip characteristics, with uniqueness and randomness. By extracting the process parameter deviation that must be introduced in the chip manufacturing process, the excitation signal and the generated unpredictable response signal are realized. The only corresponding function function. Integrating PUF in the FIDO U2F identity token and applying its functionality is a direction worth exploring.
另一方面,随机数的使用在身份认证系统中具有重要作用。不完善的随机数会导致攻击者能够对身份认证协议执行重放、交错等攻击,致使系统安全性出现巨大风险。为解决这一问题,应该在身份认证令牌中使用真随机数发生器。On the other hand, the use of random numbers plays an important role in identity authentication systems. Imperfect random numbers will allow attackers to perform replay, interleaving and other attacks on the authentication protocol, resulting in huge risks to system security. To solve this problem, a true random number generator should be used in the authentication token.
发明内容SUMMARY OF THE INVENTION
为解决现有技术的不足,本发明的目的在于提供一种基于身份认证服务器和身份认证令牌的系统,解决了身份认证过程中的令牌被复制、身份被冒用的问题,以确保持有者相关操作的不可篡改性以及不可抵赖性。In order to solve the deficiencies of the prior art, the purpose of the present invention is to provide a system based on an identity authentication server and an identity authentication token, which solves the problems of the token being copied and the identity being used fraudulently in the identity authentication process, so as to ensure the The immutability and non-repudiation of relevant operations.
为了实现上述目标,本发明采用如下的技术方案:一种基于身份认证服务器和身份认证令牌的系统,其特征是,身份认证服务器,包括相互连接的标准FIDO服务器和用于存储密钥的存储空间,即数据库;In order to achieve the above goals, the present invention adopts the following technical scheme: a system based on an identity authentication server and an identity authentication token, characterized in that the identity authentication server includes a standard FIDO server connected to each other and a storage key for storing keys. space, the database;
身份认证令牌,基于物理不可克隆与FIDO U2F协议,包括U2F模块、与U2F模块分别相连的PUF模块、TRNG模块、USB模块、交互模块,以及与交互模块连接的触摸模块;Identity authentication token, based on physical unclonable and FIDO U2F protocol, including U2F module, PUF module, TRNG module, USB module, interactive module connected to the U2F module, and touch module connected to the interactive module;
U2F模块用于实现加密算法、人机交互、和外界通信;The U2F module is used to implement encryption algorithms, human-computer interaction, and communication with the outside world;
PUF模块为物理不可克隆函数模块,用来产生根密钥,与U2F模块以挑战应答方式通信;The PUF module is a physical unclonable function module, which is used to generate the root key and communicate with the U2F module in a challenge-response manner;
TRNG模块为真随机数发生器;The TRNG module is a true random number generator;
USB模块的用于与PC端以人机接口设备的形式进行通信,用于将接收PC端发送过来的数据传给U2F模块,以及将U2F模块处理后的数据传给PC端;The USB module is used to communicate with the PC in the form of a human-machine interface device, to transmit the data sent by the received PC to the U2F module, and to transmit the data processed by the U2F module to the PC;
触摸模块为触摸感应模块,包括一个触摸感应模组和一个LED灯,触摸感应模组和LED灯分别与交互模块连接,注册或认证时,LED灯闪烁提示用户触摸,用户手按触摸模组,进行确认,防止非主动操作以及用户误操作;The touch module is a touch-sensing module, including a touch-sensing module and an LED light. The touch-sensing module and the LED light are respectively connected to the interaction module. During registration or authentication, the LED light flashes to prompt the user to touch, and the user presses the touch module. Confirmation to prevent involuntary operation and user misoperation;
交互模块为人机交互信息处理模块,其与触摸感应模组相连,驱动触摸感应模组以及接受用户对触摸模块的操作信息传输给U2F模块,与LED灯相连,用于驱动LED灯;The interaction module is a human-computer interaction information processing module, which is connected with the touch sensing module, drives the touch sensing module and receives the operation information of the user on the touch module and transmits it to the U2F module, and is connected with the LED light for driving the LED light;
身份令牌与客户端浏览器进行交互,客户端浏览器又与身份认证服务器中的FIDO服务器进行交互。The identity token interacts with the client browser, which in turn interacts with the FIDO server in the authentication server.
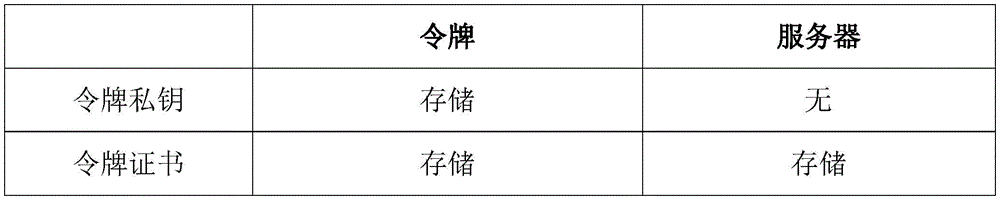
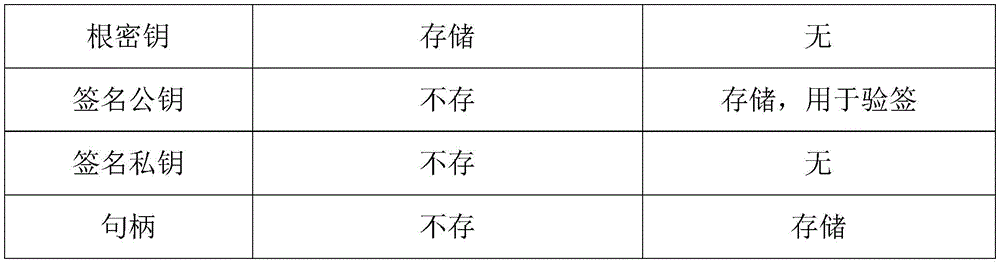
前述的一种基于身份认证服务器和身份认证令牌的系统,其特征是,所述身份认证令牌的验证过程通过数字签名实现,其中涉及到如下密钥:The aforementioned system based on an identity authentication server and an identity authentication token is characterized in that the verification process of the identity authentication token is realized by a digital signature, which involves the following keys:
①身份认证令牌的令牌私钥和令牌证书,用于验证身份令牌是否合法;令牌私钥和证书预装入身份令牌U2F模块数据库中,在注册时由令牌将证书发送给FIDO服务器;①The token private key and token certificate of the identity authentication token are used to verify whether the identity token is legal; the token private key and certificate are preloaded into the identity token U2F module database, and the token will send the certificate during registration to the FIDO server;
②身份认证令牌的根密钥,用于生成加密的密钥句柄;每次使用根密钥前,U2F模块和PUF模块要执行挑战-应答协议,协议正确执行后,U2F模块才接收PUF模块发来的根密钥值;②The root key of the identity authentication token is used to generate the encrypted key handle; before each use of the root key, the U2F module and the PUF module must execute the challenge-response protocol. After the protocol is executed correctly, the U2F module will receive the PUF module. The sent root key value;
③签名所使用的公私密钥对,这些密钥在身份认证令牌中生成,生成过程中使用物理不可克隆函数、真随机数发生器模块。③The public-private key pair used in the signature, these keys are generated in the identity authentication token, and the physical unclonable function and the true random number generator module are used in the generation process.
前述的一种基于身份认证服务器和身份认证令牌的系统,其特征是,所述身份认证服务器基于FIDO协议搭建,并在标准FIDO服务器之上额外存储了令牌证书、签名公钥、句柄,能够在收到认证或注册请求后生成挑战数据并对令牌返回的应答数据进行验证返回验证结果;所述令牌私钥、令牌证书、根密钥存储在身份认证令牌中。The aforementioned system based on an identity authentication server and an identity authentication token is characterized in that the identity authentication server is built based on the FIDO protocol, and additionally stores a token certificate, a signature public key, and a handle on the standard FIDO server, After receiving the authentication or registration request, challenge data can be generated and the response data returned by the token can be verified to return the verification result; the token private key, token certificate and root key are stored in the identity authentication token.
前述的一种基于身份认证服务器和身份认证令牌的系统,其特征是,所述身份认证令牌是硬件设备,不直接连接到网络上,通过客户端浏览器与FIDO服务器交互。The aforementioned system based on an identity authentication server and an identity authentication token is characterized in that the identity authentication token is a hardware device, which is not directly connected to the network, and interacts with the FIDO server through a client browser.
前述的一种基于身份认证服务器和身份认证令牌的系统,其特征是,所述身份认证令牌支持两种操作:注册、认证;用户第一次使用时调用注册方法,之后使用调用认证方法;其中注册操作在身份认证令牌中建立签名公钥和私钥密钥对,并在FIDO服务器注册用户的身份及公钥和句柄,用于后续的认证操作;认证操作中令牌需要向FIDO服务器证明自己持有合法的私钥。The aforementioned system based on an identity authentication server and an identity authentication token is characterized in that the identity authentication token supports two operations: registration and authentication; the user invokes the registration method when using it for the first time, and then invokes the authentication method by using it for the first time. ;The registration operation establishes the signature public key and private key key pair in the identity authentication token, and registers the user's identity, public key and handle in the FIDO server for subsequent authentication operations; in the authentication operation, the token needs to be sent to FIDO The server proves that it holds the legitimate private key.
前述的一种基于身份认证服务器和身份认证令牌的系统,其特征是,所述注册方法包括步骤:The aforementioned system based on an identity authentication server and an identity authentication token is characterized in that the registration method comprises the steps of:
(1)当用户在客户端浏览器请求注册时,在客户端浏览器输入注册用户名,发送给FIDO服务器,FIDO服务器生成一个随机数A,并将该随机数A连同用户名发送给客户端浏览器,使用随机数可以有效地防止重放攻击;(1) When the user requests registration in the client browser, input the registered user name in the client browser, send it to the FIDO server, the FIDO server generates a random number A, and sends the random number A together with the user name to the client Browsers, using random numbers can effectively prevent replay attacks;
(2)客户端浏览器检验和FIDO服务器的TLS连接,确定是合法的FIDO服务器后,客户端生成注册挑战参数列表{TLS连接数据TLSData、客户端浏览器随机生成的一个会话随机参数SessionRandomValue、随机数A、用户名},客户端进一步对FIDO服务器URL进行哈希运算,得到URL哈希值;(2) The client browser checks the TLS connection with the FIDO server, and after determining that it is a legitimate FIDO server, the client generates a registration challenge parameter list {TLS connection data TLSData, a random session parameter SessionRandomValue randomly generated by the client browser, random Number A, username}, the client further performs hash operation on the FIDO server URL to obtain the URL hash value;
(3)客户端浏览器将注册挑战参数列表和URL哈希值通过与计算机USB接口相连接的身份认证令牌的USB接口,经USB模块发送给U2F模块;(3) The client browser sends the registration challenge parameter list and the URL hash value to the U2F module through the USB module through the USB interface of the identity authentication token connected with the USB interface of the computer;
(4)身份认证令牌的U2F模块调用数字签名密钥生成算法,生成一对签名公私密钥对;签名公钥和签名私钥是以客户端登录会话信息和随机数A作为参数,通过密钥生成算法计算出来的,其中登录会话信息包括FIDO服务器URL、用户名、TLSData、SessionRandomValue;(4) The U2F module of the identity authentication token calls the digital signature key generation algorithm to generate a pair of signature public and private keys; the signature public key and signature private key take the client login session information and random number A as parameters, and pass the encryption Calculated by the key generation algorithm, where the login session information includes the FIDO server URL, username, TLSData, and SessionRandomValue;
(5)U2F模块通过挑战应答协议调用PUF模块生成自己的根密钥,并以根密钥为加密密钥,签名私钥和FIDO服务器URL哈希值作为明文,调用对称加密算法,加密后生成密钥句柄;根密钥长度为128比特;(5) The U2F module calls the PUF module through the challenge-response protocol to generate its own root key, and uses the root key as the encryption key, the signature private key and the FIDO server URL hash value as the plaintext, calls the symmetric encryption algorithm, and generates after encryption key handle; root key length is 128 bits;
(6)身份认证令牌的U2F模块调用数字签名算法,以自己的签名私钥为密钥,对列表{密钥句柄、签名公钥、注册挑战参数列表}进行签名,产生签名值;(6) The U2F module of the identity authentication token calls the digital signature algorithm, uses its own signature private key as the key, and signs the list {key handle, signature public key, registration challenge parameter list} to generate a signature value;
(7)U2F模块经USB模块,通过USB接口将密钥句柄、签名公钥、注册挑战参数列表、签名值、令牌证书发送给客户端浏览器,客户端浏览器再将其发送给FIDO服务器;(7) The U2F module sends the key handle, signature public key, registration challenge parameter list, signature value, and token certificate to the client browser through the USB module through the USB interface, and the client browser sends it to the FIDO server. ;
(8)FIDO服务器从收到的消息中提取出令牌证书,首先验证令牌证书的合法性;如果合法,则提取令牌证书中令牌公钥,并调用验签算法,使用该令牌公钥,验证签名的合法性;如果合法则FIDO服务器存储“用户名、签名公钥、密钥句柄”,并通知客户端浏览器注册成功;否则通知客户端注册失败。(8) The FIDO server extracts the token certificate from the received message, and first verifies the validity of the token certificate; if it is legal, it extracts the token public key in the token certificate, invokes the signature verification algorithm, and uses the token The public key is used to verify the validity of the signature; if it is legal, the FIDO server stores the "username, signature public key, and key handle" and informs the client browser that the registration is successful; otherwise, it informs the client that the registration failed.
前述的一种基于身份认证服务器和身份认证令牌的系统,其特征是,所述步骤(4)、(5)、(6)中的密钥生成算法、对称加密算法、哈希算法和数字签名有两种模式,一为国密算法,包括SM2、SM3、SM4算法;二为标准FIDO算法包括RSA、ECDSA、SHA256、AES,算法内置于U2F模块中。The aforementioned system based on an identity authentication server and an identity authentication token is characterized in that the key generation algorithm, the symmetric encryption algorithm, the hash algorithm and the digital key in the steps (4), (5) and (6) are There are two modes of signature, one is national secret algorithm, including SM2, SM3, SM4 algorithm; the other is standard FIDO algorithm including RSA, ECDSA, SHA256, AES, and the algorithm is built into the U2F module.
前述的一种基于身份认证服务器和身份认证令牌的系统,其特征是,所述认证方法包括步骤:The aforementioned system based on an identity authentication server and an identity authentication token is characterized in that the authentication method comprises the steps:
(1)当FIDO服务器收到用户认证请求后,查找数据库,找到该用户的注册密钥句柄,同时服务器生成一个随机数B,并将该随机数B连同注册密钥句柄一起发送给客户端;(1) When the FIDO server receives the user authentication request, it searches the database to find the user's registration key handle, and the server generates a random number B, and sends the random number B together with the registration key handle to the client;
(2)客户端浏览器检验和服务器的TLS连接,确定是合法的服务器后,获取TLS连接数据TLSData,并对列表{FIDO服务器URL,随机数B,TLSData}执行哈希运算,得到哈希运算的结果,作为认证挑战值;客户端进一步对FIDO服务器URL进行哈希运算,得到URL的哈希值;(2) The client browser checks the TLS connection of the server and determines that it is a legitimate server, obtains the TLS connection data TLSData, and performs a hash operation on the list {FIDO server URL, random number B, TLSData} to obtain the hash operation The result is used as the authentication challenge value; the client further performs hash operation on the FIDO server URL to obtain the hash value of the URL;
(3)客户端浏览器将认证挑战值、URL哈希值、注册密钥句柄通过USB接口,经USB模块,发送给身份认证令牌的U2F模块;(3) The client browser sends the authentication challenge value, URL hash value, and registration key handle to the U2F module of the identity authentication token through the USB interface and the USB module;
(4)身份认证令牌上触摸模块的LED灯亮起后,用户通过触摸亮灯旁的触摸感应模组进行物理确认,交互模块在收到触摸确认后会将确认信息传输到U2F模块;(4) After the LED light of the touch module on the identity authentication token lights up, the user performs physical confirmation by touching the touch sensing module next to the lighted light, and the interaction module will transmit the confirmation information to the U2F module after receiving the touch confirmation;
(5)U2F模块的认证签名计数器加1,这样做可以记录执行身份认证操作的次数;(5) The authentication signature counter of the U2F module is incremented by 1, which can record the number of times the identity authentication operation is performed;
(6)U2F模块以挑战应答协议调用PUF模块生成自己的根密钥,使用根密钥调用对称加密算法,对密钥句柄进行解密,得到URL哈希值和签名私钥;(6) The U2F module calls the PUF module with the challenge response protocol to generate its own root key, uses the root key to call the symmetric encryption algorithm, decrypts the key handle, and obtains the URL hash value and the signature private key;
(7)身份认证令牌的U2F模块验证解密句柄得到的URL哈希值和步骤(3)客户端发来的URL哈希值是否一致,如果不一致则中断执行,认证失败,如果一致则执行下一步;(7) The U2F module of the identity authentication token verifies whether the URL hash value obtained by the decryption handle is consistent with the URL hash value sent by the client in step (3), if it is inconsistent, the execution is interrupted, and the authentication fails, if it is consistent, execute the following step;
(8)U2F模块调用TRNG真随机数发生器产生本地随机数C;(8) The U2F module calls the TRNG true random number generator to generate a local random number C;
(9)U2F模块使用步骤(6)解密句柄得到的签名私钥,调用数字签名算法对{认证挑战值,认证签名计数器值,本地随机值C}进行数字签名得到认证签名值;(9) U2F module uses the signature private key obtained in step (6) to decrypt the handle, and invokes the digital signature algorithm to digitally sign {authentication challenge value, authentication signature counter value, local random value C} to obtain the authentication signature value;
(10)身份认证令牌的U2F模块将认证挑战值、认证签名值、认证签名计数器值、本地随机值C发送给客户端浏览器,由客户端浏览器转发给FIDO服务器;FIDO服务器查找用户的签名公钥;并使用该签名公钥调用验签算法,验证签名的合法性;如果合法则用户身份认证成功;否则通知客户端认证失败。(10) The U2F module of the identity authentication token sends the authentication challenge value, authentication signature value, authentication signature counter value, and local random value C to the client browser, and the client browser forwards it to the FIDO server; the FIDO server searches for the user's The signature public key; and use the signature public key to call the signature verification algorithm to verify the validity of the signature; if it is valid, the user identity authentication is successful; otherwise, the client is notified that the authentication fails.
前述的一种基于身份认证服务器和身份认证令牌的系统,其特征是,所述步骤(6)、(2)、(9)对称加密算法、哈希算法和数字签名有两种模式,一为国密算法,包括SM2、SM3、SM4算法;二为标准FIDO算法,包括RSA、ECDSA、SHA256、AES,算法内置于U2F模块中。The aforementioned system based on an identity authentication server and an identity authentication token is characterized in that the steps (6), (2), (9) symmetric encryption algorithm, hash algorithm and digital signature have two modes, one is The second is the standard FIDO algorithm, including RSA, ECDSA, SHA256, AES, and the algorithm is built into the U2F module.
本发明所达到的有益效果:Beneficial effects achieved by the present invention:
采用物理不可克隆函数与FIDO相结合,以物理不可克隆函数保证令牌的唯一性,不可复制性,以FIDO保证用户身份的准确性以及所进行操作的不可篡改性、不可抵赖性;The physical unclonable function is combined with FIDO to ensure the uniqueness and non-replicability of the token with the physical unclonable function, and the FIDO to ensure the accuracy of the user's identity and the non-tampering and non-repudiation of the operation;
通过第二因子验证解决传统账号密码验证存在的密码泄露等隐患;Solve hidden dangers such as password leakage existing in traditional account password verification through second factor verification;
通过U2F协议保证令牌的可扩展性和普适性,实现多系统统一身份认证;Ensure the scalability and universality of tokens through the U2F protocol, and realize multi-system unified identity authentication;
通过物理不可克隆函数保证令牌的不可克隆性;Guaranteed unclonability of tokens through a physical unclonable function;
通过真随机数发射器保证用户认证过程挑战应答机制的随机性、不可重现性。The randomness and non-reproducibility of the challenge-response mechanism in the user authentication process are guaranteed by a true random number transmitter.
附图说明Description of drawings
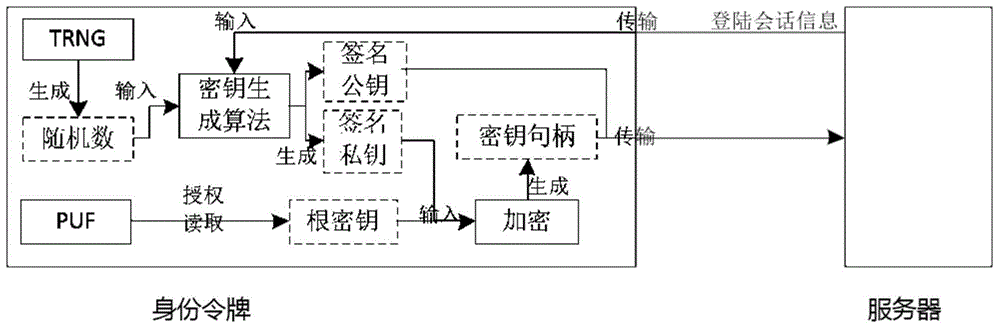
图1是本发明身份认证服务器的结构示意图;Fig. 1 is the structural representation of the identity authentication server of the present invention;
图2是本发明身份认证令牌的结构示意图;Fig. 2 is the structural representation of the identity authentication token of the present invention;
图3是签名秘钥生成流程图。Figure 3 is a flow chart of signature key generation.
具体实施方式Detailed ways
下面结合附图对本发明作进一步描述。以下实施例仅用于更加清楚地说明本发明的技术方案,而不能以此来限制本发明的保护范围。The present invention will be further described below in conjunction with the accompanying drawings. The following examples are only used to illustrate the technical solutions of the present invention more clearly, and cannot be used to limit the protection scope of the present invention.
如图1所示,一种身份认证服务器,包括相互连接的标准FIDO服务器和用于存储密钥的存储空间,即数据库。As shown in Figure 1, an identity authentication server includes a standard FIDO server connected to each other and a storage space for storing keys, that is, a database.
如图2所示,一种身份认证令牌,基于物理不可克隆与FIDO U2F协议,包括U2F模块、与U2F模块分别相连的PUF模块、TRNG模块、USB模块、交互模块,以及与交互模块连接的触摸模块、LED灯;As shown in Figure 2, an identity authentication token, based on the physical unclonable and FIDO U2F protocol, includes a U2F module, a PUF module connected to the U2F module, a TRNG module, a USB module, an interaction module, and a module connected to the interaction module. Touch module, LED light;
U2F模块功能主要是实现加密算法、人机交互、和外界通信等。U2F模块内有存储空间、加解密算法、认证计数器。U2F模块以国民认证Z8D256U-2为例,但不局限于此;The functions of the U2F module are mainly to implement encryption algorithms, human-computer interaction, and communication with the outside world. The U2F module has storage space, encryption and decryption algorithms, and authentication counters. The U2F module takes the national certification Z8D256U-2 as an example, but is not limited to this;
PUF模块为物理不可克隆函数模块,其内部集成了物理不可克隆函数,能够在收到激励后利用其内部物理构造的随机差异输出一个不可预测的响应,来保证身份令牌的不可克隆性。用来产生根密钥,与U2F模块以挑战应答方式通信。PUF模块内含一块PUF芯片,以Intrinsic ID公司Quiddikey-filex-e芯片为例,但不局限于此;The PUF module is a physical unclonable function module, which integrates a physical unclonable function, and can use the random difference of its internal physical structure to output an unpredictable response after receiving an incentive to ensure the unclonability of the identity token. It is used to generate the root key and communicate with the U2F module in a challenge-response manner. The PUF module contains a PUF chip, take the Quiddikey-filex-e chip of Intrinsic ID company as an example, but not limited to this;
TRNG模块为真随机数发生器,其利用物理方法实现随机数发生,无法猜测其产生的随机数结果,产生过程永不具有周期性,以保证每次操作的独立性。TRNG模块内含一块TRNG芯片,以ID Quantique公司的Quantis AIS 31芯片为例,但不局限于此;The TRNG module is a true random number generator, which uses physical methods to generate random numbers. It is impossible to guess the results of the random numbers it generates. The generation process is never periodic to ensure the independence of each operation. The TRNG module contains a TRNG chip, taking the Quantis AIS 31 chip of ID Quantique as an example, but not limited to this;
USB模块的功能是与PC端以USB-HID(Human Interface Device,人机接口设备)设备的形式进行通信,用于将接收PC端发送过来的数据传给U2F模块,以及将U2F模块处理后的数据传给PC端;The function of the USB module is to communicate with the PC in the form of a USB-HID (Human Interface Device) device, which is used to transmit the data sent by the PC to the U2F module, and to process the processed data from the U2F module. The data is transmitted to the PC side;
触摸模块为触摸感应模块,包括一个触摸感应模组和一个LED灯,触摸感应模组和LED灯分别与交互模块连接,注册或认证时,LED灯闪烁提示用户触摸,用户手按触摸模组,进行确认,防止非主动操作以及用户误操作;The touch module is a touch-sensing module, including a touch-sensing module and an LED light. The touch-sensing module and the LED light are respectively connected to the interaction module. During registration or authentication, the LED light flashes to prompt the user to touch, and the user presses the touch module. Confirmation to prevent involuntary operation and user misoperation;
交互模块为人机交互信息处理模块,其与触摸感应模组相连,驱动触摸感应模组以及接受用户对触摸模块的操作信息传输给U2F模块,与LED灯相连,用于驱动LED灯。The interaction module is a human-computer interaction information processing module, which is connected to the touch sensing module, drives the touch sensing module, and receives the user's operation information on the touch module and transmits it to the U2F module, and is connected to the LED light for driving the LED light.
身份令牌与客户端浏览器进行交互,客户端浏览器又与身份认证服务器中的FIDO服务器进行交互。The identity token interacts with the client browser, which in turn interacts with the FIDO server in the authentication server.
本令牌的身份验证过程通过数字签名实现,其中涉及到如下密钥:The authentication process of this token is achieved by digital signature, which involves the following keys:
①身份认证令牌的令牌私钥和证书,用于验证身份令牌是否合法;令牌私钥和证书预装入身份令牌U2F模块数据库中,在注册时由令牌将证书发送给FIDO服务器;①The token private key and certificate of the identity authentication token are used to verify whether the identity token is legal; the token private key and certificate are preloaded into the identity token U2F module database, and the token will send the certificate to FIDO during registration server;
②身份认证令牌的根密钥,用于生成加密的密钥句柄。根密钥的读取需要PUF模块的参与。PUF未集成在U2F模块的主芯片上,而是以独立芯片的方式存在,为了确保根密钥的正确性,每次使用根密钥前,U2F主芯片和PUF芯片要执行挑战-应答协议,协议正确执行后,主芯片才接收PUF芯片发来的根密钥值;②The root key of the authentication token is used to generate the encrypted key handle. The reading of the root key requires the participation of the PUF module. The PUF is not integrated on the main chip of the U2F module, but exists as an independent chip. In order to ensure the correctness of the root key, the U2F main chip and the PUF chip must execute the challenge-response protocol before each use of the root key. After the protocol is executed correctly, the main chip receives the root key value sent by the PUF chip;
③签名所使用的公私密钥对。这些密钥在身份认证令牌中生成,生成过程中使用物理不可克隆函数、真随机数发生器等模块,有效地保障密钥的高安全性。③ The public and private key pair used for signature. These keys are generated in the identity authentication token, and modules such as physical unclonable functions and true random number generators are used in the generation process to effectively ensure the high security of the keys.
密钥生成流程如图3所示。The key generation process is shown in Figure 3.
表1为密钥在身份认证令牌的U2F模块和FIDO服务器中的存储情况。Table 1 shows the storage of keys in the U2F module of the authentication token and the FIDO server.
表1密钥存储情况表Table 1 Key storage situation table
本身份认证服务器基于FIDO协议搭建,并在标准FIDO服务器之上额外存储了令牌证书、签名公钥、句柄。其能够在收到认证或注册请求后生成挑战数据并对令牌返回的应答数据进行验证返回验证结果。This identity authentication server is built based on the FIDO protocol, and additionally stores the token certificate, signature public key, and handle on top of the standard FIDO server. It can generate challenge data after receiving the authentication or registration request and verify the response data returned by the token and return the verification result.
本身份令牌是专用的硬件设备,并不直接连接到网络上,而是通过客户端浏览器与FIDO服务器交互。This identity token is a dedicated hardware device, which is not directly connected to the network, but interacts with the FIDO server through the client browser.
令牌支持两种操作:注册、认证。用户第一次使用时将调用注册方法,之后使用将调用认证方法。其中注册操作将在身份认证令牌中建立签名公钥和私钥密钥对,并在FIDO服务器注册用户的身份及公钥和句柄,用于后续的认证操作;认证操作中令牌需要向FIDO服务器证明自己持有合法的私钥。The token supports two operations: registration, authentication. The registration method will be called on the first use by the user, and the authentication method will be called on subsequent uses. The registration operation will establish a signature public key and private key key pair in the identity authentication token, and register the user's identity, public key and handle in the FIDO server for subsequent authentication operations; in the authentication operation, the token needs to be sent to FIDO The server proves that it holds the legitimate private key.
一种根据上述的身份认证服务器和身份认证令牌的注册方法,包括步骤:A registration method according to the above-mentioned identity authentication server and identity authentication token, comprising the steps of:
(1)当用户在客户端浏览器请求注册时,在客户端浏览器输入注册用户名,发送给FIDO服务器,FIDO服务器生成一个随机数A,并将该随机数A连同用户名发送给客户端浏览器,使用随机数可以有效地防止重放攻击;(1) When the user requests registration in the client browser, input the registered user name in the client browser, send it to the FIDO server, the FIDO server generates a random number A, and sends the random number A together with the user name to the client Browsers, using random numbers can effectively prevent replay attacks;
(2)客户端浏览器检验和FIDO服务器的TLS(安全传输层协议)连接,确定是合法的FIDO服务器后,客户端生成注册挑战参数列表{TLS连接数据(以下称TLSData)、客户端浏览器随机生成的一个会话随机参数(以下称SessionRandomValue)、随机数A、用户名},客户端进一步对FIDO服务器URL进行哈希运算,得到URL哈希值;(2) The client browser checks the TLS (Transport Layer Security) connection with the FIDO server, and after determining that it is a legitimate FIDO server, the client generates a registration challenge parameter list {TLS connection data (hereinafter referred to as TLSData), client browser A randomly generated session random parameter (hereinafter referred to as SessionRandomValue), random number A, user name}, the client further hashes the FIDO server URL to obtain the URL hash value;
(3)客户端浏览器将注册挑战参数列表和URL哈希值通过与计算机USB接口相连接的身份认证令牌的USB接口,经USB模块发送给U2F模块;(3) The client browser sends the registration challenge parameter list and the URL hash value to the U2F module through the USB module through the USB interface of the identity authentication token connected with the USB interface of the computer;
(4)身份认证令牌的U2F模块调用数字签名密钥生成算法,生成一对签名公私密钥对;签名公钥和签名私钥是以客户端登录会话信息和随机数A作为参数,通过密钥生成算法计算出来的,其中登录会话信息包括FIDO服务器URL、用户名、TLSData、SessionRandomValue。(4) The U2F module of the identity authentication token calls the digital signature key generation algorithm to generate a pair of signature public and private keys; the signature public key and signature private key take the client login session information and random number A as parameters, and pass the encryption It is calculated by the key generation algorithm, and the login session information includes the FIDO server URL, user name, TLSData, and SessionRandomValue.
(5)U2F模块通过挑战应答协议调用PUF模块生成自己的根密钥,并以根密钥为加密密钥,签名私钥和FIDO服务器URL哈希值作为明文,调用对称加密算法,加密后生成密钥句柄;根密钥长度为128比特;(5) The U2F module calls the PUF module through the challenge-response protocol to generate its own root key, and uses the root key as the encryption key, the signature private key and the FIDO server URL hash value as the plaintext, calls the symmetric encryption algorithm, and generates after encryption key handle; root key length is 128 bits;
(6)身份认证令牌的U2F模块调用数字签名算法,以自己的签名私钥为密钥,对列表{密钥句柄、签名公钥、注册挑战参数列表}进行签名,产生签名值;(6) The U2F module of the identity authentication token calls the digital signature algorithm, uses its own signature private key as the key, and signs the list {key handle, signature public key, registration challenge parameter list} to generate a signature value;
(7)U2F模块经USB模块,通过USB接口将密钥句柄、签名公钥、注册挑战参数列表、签名值、令牌证书发送给客户端浏览器,客户端浏览器再将其发送给FIDO服务器;(7) The U2F module sends the key handle, signature public key, registration challenge parameter list, signature value, and token certificate to the client browser through the USB module through the USB interface, and the client browser sends it to the FIDO server. ;
(8)FIDO服务器从收到的消息中提取出令牌证书,首先验证令牌证书的合法性;如果合法,则提取令牌证书中令牌公钥,并调用验签算法,使用该令牌公钥,验证签名的合法性;如果合法则FIDO服务器存储“用户名、签名公钥、密钥句柄”,并通知客户端浏览器注册成功;否则通知客户端注册失败。(8) The FIDO server extracts the token certificate from the received message, and first verifies the validity of the token certificate; if it is legal, it extracts the token public key in the token certificate, invokes the signature verification algorithm, and uses the token The public key is used to verify the validity of the signature; if it is legal, the FIDO server stores the "username, signature public key, and key handle" and informs the client browser that the registration is successful; otherwise, it informs the client that the registration failed.
自此注册流程结束。The registration process ends here.
步骤(4)、(5)、(6)密钥生成算法、对称加密算法、哈希算法和数字签名有两种模式,一为国密算法(SM2、SM3、SM4算法);二为标准FIDO算法(RSA、ECDSA、SHA256、AES),算法内置于U2F模块中。Steps (4), (5), (6) There are two modes of key generation algorithm, symmetric encryption algorithm, hash algorithm and digital signature, one is national secret algorithm (SM2, SM3, SM4 algorithm); the other is standard FIDO Algorithms (RSA, ECDSA, SHA256, AES), the algorithms are built into the U2F module.
一种根据上述的身份认证服务器和身份认证令牌的认证方法,包括步骤:An authentication method according to the above-mentioned identity authentication server and identity authentication token, comprising the steps of:
(1)当FIDO服务器收到用户认证请求后,查找数据库,找到该用户的注册密钥句柄,同时服务器生成一个随机数B,并将该随机数B连同注册密钥句柄一起发送给客户端;(1) When the FIDO server receives the user authentication request, it searches the database to find the user's registration key handle, and the server generates a random number B, and sends the random number B together with the registration key handle to the client;
(2)客户端浏览器检验和服务器的TLS连接,确定是合法的服务器后,获取TLS连接数据(以下称TLSData),并对列表{FIDO服务器URL,随机数B,TLSData}执行哈希运算,得到哈希运算的结果,作为认证挑战值;客户端进一步对FIDO服务器URL进行哈希运算,得到URL的哈希值;(2) The client browser checks the TLS connection of the server and determines that it is a legitimate server, obtains the TLS connection data (hereinafter referred to as TLSData), and performs a hash operation on the list {FIDO server URL, random number B, TLSData}, Obtain the result of the hash operation as the authentication challenge value; the client further performs the hash operation on the FIDO server URL to obtain the hash value of the URL;
(3)客户端浏览器将认证挑战值、URL哈希值、注册密钥句柄通过USB接口,经USB模块,发送给身份认证令牌的U2F模块;(3) The client browser sends the authentication challenge value, URL hash value, and registration key handle to the U2F module of the identity authentication token through the USB interface and the USB module;
(4)身份认证令牌上触摸模块的LED灯亮起后,用户通过触摸亮灯旁的触摸感应模组进行物理确认,交互模块在收到触摸确认后会将确认信息传输到U2F模块;(4) After the LED light of the touch module on the identity authentication token lights up, the user performs physical confirmation by touching the touch sensing module next to the lighted light, and the interaction module will transmit the confirmation information to the U2F module after receiving the touch confirmation;
(5)U2F模块的认证签名计数器加1,这样做可以记录执行身份认证操作的次数;(5) The authentication signature counter of the U2F module is incremented by 1, which can record the number of times the identity authentication operation is performed;
(6)U2F模块以挑战应答协议调用PUF模块生成自己的根密钥,使用根密钥调用对称加密算法,对密钥句柄进行解密,得到URL哈希值和签名私钥;(6) The U2F module calls the PUF module with the challenge response protocol to generate its own root key, uses the root key to call the symmetric encryption algorithm, decrypts the key handle, and obtains the URL hash value and the signature private key;
(7)身份认证令牌的U2F模块验证解密句柄得到的URL哈希值和步骤(3)客户端发来的URL哈希值是否一致,如果不一致则中断执行,认证失败,如果一致则执行下一步;(7) The U2F module of the identity authentication token verifies whether the URL hash value obtained by the decryption handle is consistent with the URL hash value sent by the client in step (3), if it is inconsistent, the execution is interrupted, and the authentication fails, if it is consistent, execute the following step;
(8)U2F模块调用TRNG真随机数发生器产生本地随机数C;(8) The U2F module calls the TRNG true random number generator to generate a local random number C;
(9)U2F模块使用步骤(6)解密句柄得到的签名私钥,调用数字签名算法对{认证挑战值,认证签名计数器值,本地随机值C}进行数字签名得到认证签名值;(9) U2F module uses the signature private key obtained in step (6) to decrypt the handle, and invokes the digital signature algorithm to digitally sign {authentication challenge value, authentication signature counter value, local random value C} to obtain the authentication signature value;
(10)身份认证令牌的U2F模块将认证挑战值、认证签名值、认证签名计数器值、本地随机值C发送给客户端浏览器,由客户端浏览器转发给FIDO服务器;FIDO服务器查找用户的签名公钥;并使用该签名公钥调用验签算法,验证签名的合法性。如果合法则用户身份认证成功;否则通知客户端认证失败。(10) The U2F module of the identity authentication token sends the authentication challenge value, authentication signature value, authentication signature counter value, and local random value C to the client browser, and the client browser forwards it to the FIDO server; the FIDO server searches for the user's The signature public key; and use the signature public key to call the signature verification algorithm to verify the validity of the signature. If it is legal, the user authentication is successful; otherwise, it informs the client that the authentication fails.
步骤(6)、(2)、(9)对称加密算法、哈希算法和数字签名有两种模式,一为国密算法(SM2、SM3、SM4算法);二为标准FIDO算法(RSA、ECDSA、SHA256、AES)。算法内置于U2F模块中。Steps (6), (2), (9) There are two modes of symmetric encryption algorithm, hash algorithm and digital signature, one is national secret algorithm (SM2, SM3, SM4 algorithm); the other is standard FIDO algorithm (RSA, ECDSA , SHA256, AES). The algorithm is built into the U2F module.
本发明采用物理不可克隆函数与FIDO相结合,以物理不可克隆函数保证令牌的唯一性,不可复制性,以FIDO保证用户身份的准确性以及所进行操作的不可篡改性、不可抵赖性;通过第二因子验证解决传统账号密码验证存在的密码泄露等隐患;通过U2F协议保证令牌的可扩展性和普适性,实现多系统统一身份认证;通过物理不可克隆函数保证令牌的不可克隆性;通过真随机数发射器保证用户认证过程挑战应答机制的随机性、不可重现性。The present invention adopts the combination of physical unclonable function and FIDO, uses the physical unclonable function to ensure the uniqueness and non-replicability of the token, and uses FIDO to ensure the accuracy of the user's identity and the non-tampering and non-repudiation of the operation; The second factor verification solves the hidden dangers of password leakage in traditional account password verification; guarantees the scalability and universality of tokens through the U2F protocol, and realizes multi-system unified identity authentication; through the physical unclonable function to ensure the unclonability of the token ; Ensure the randomness and non-reproducibility of the challenge-response mechanism in the user authentication process through a true random number transmitter.
以上所述仅是本发明的优选实施方式,应当指出,对于本技术领域的普通技术人员来说,在不脱离本发明技术原理的前提下,还可以做出若干改进和变形,这些改进和变形也应视为本发明的保护范围。The above are only the preferred embodiments of the present invention. It should be pointed out that for those skilled in the art, without departing from the technical principles of the present invention, several improvements and modifications can be made. These improvements and modifications It should also be regarded as the protection scope of the present invention.
Claims (6)
Priority Applications (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN201711261470.3A CN108092776B (en) | 2017-12-04 | 2017-12-04 | A system based on an authentication server and an authentication token |
Applications Claiming Priority (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN201711261470.3A CN108092776B (en) | 2017-12-04 | 2017-12-04 | A system based on an authentication server and an authentication token |
Publications (2)
| Publication Number | Publication Date |
|---|---|
| CN108092776A CN108092776A (en) | 2018-05-29 |
| CN108092776B true CN108092776B (en) | 2020-11-10 |
Family
ID=62172507
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| CN201711261470.3A Active CN108092776B (en) | 2017-12-04 | 2017-12-04 | A system based on an authentication server and an authentication token |
Country Status (1)
| Country | Link |
|---|---|
| CN (1) | CN108092776B (en) |
Cited By (1)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US12113895B2 (en) | 2020-12-11 | 2024-10-08 | PUFsecurity Corporation | Key management system providing secure management of cryptographic keys, and methods of operating the same |
Families Citing this family (39)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN108322468A (en) * | 2018-02-02 | 2018-07-24 | 广州南洋理工职业学院 | Identity authorization system |
| CN118041531A (en) * | 2018-06-29 | 2024-05-14 | 纳格拉影像有限公司 | Cryptographic key configuration using physically unclonable functions |
| CN109040067B (en) * | 2018-08-02 | 2020-12-11 | 广东工业大学 | A user authentication device and authentication method based on physical unclonable technology PUF |
| CN109194484A (en) * | 2018-08-14 | 2019-01-11 | 中国科学院信息工程研究所 | A kind of cross-domain transmission method of token based on shared key |
| CN110932858B (en) * | 2018-09-19 | 2023-05-02 | 阿里巴巴集团控股有限公司 | Authentication method and system |
| CN109302286B (en) * | 2018-10-26 | 2021-03-16 | 江苏恒宝智能系统技术有限公司 | Fido equipment key index generation method |
| US20210377263A1 (en) * | 2018-10-29 | 2021-12-02 | Login Id Inc. | Distributed computing systems for strong user authentication and related methods |
| CN109088902B (en) * | 2018-11-05 | 2019-10-25 | 江苏恒宝智能系统技术有限公司 | Register method and device, authentication method and device |
| US11245700B2 (en) | 2018-12-06 | 2022-02-08 | Fujitsu Limited | Information processing apparatus, information processing method, and recording medium recording information processing program |
| JP7269486B2 (en) * | 2018-12-06 | 2023-05-09 | 富士通株式会社 | Information processing device, information processing method and information processing program |
| CN109756872B (en) * | 2018-12-06 | 2021-08-31 | 国网山东省电力公司电力科学研究院 | End-to-end data processing method for power grid NB-IoT based on physical unclonable function |
| CN109784024A (en) * | 2018-12-14 | 2019-05-21 | 航天信息股份有限公司 | One kind authenticating FIDO method and system based on the polyfactorial quick online identity of more authenticators |
| CN109829276B (en) * | 2018-12-17 | 2023-05-09 | 航天信息股份有限公司 | Electronic invoice unified management method and system based on FIDO protocol identity authentication |
| CN110049002B (en) * | 2019-03-01 | 2021-07-27 | 中国电子科技集团公司第三十研究所 | A PUF-based IPSec Authentication Method |
| WO2020183035A1 (en) * | 2019-03-11 | 2020-09-17 | Signe,S.A. | Unclonable authentication method for device-based digital identity verification with physically unclonable function chips |
| CN110138736B (en) * | 2019-04-11 | 2022-05-13 | 泉州信息工程学院 | Identity authentication method, device and device for multiple dynamic random encryption of Internet of Things |
| US11102004B2 (en) * | 2019-04-29 | 2021-08-24 | Google Llc | Systems and methods for distributed verification of online identity |
| CN110191112B (en) * | 2019-05-22 | 2022-03-11 | 阿波罗智联(北京)科技有限公司 | Identity verification method and device, vehicle-mounted equipment and server |
| CN110211268B (en) * | 2019-06-04 | 2021-07-20 | 北京一砂信息技术有限公司 | System and method for unlocking intelligent lock by time-efficient random password and storage medium |
| US11374917B2 (en) * | 2020-01-24 | 2022-06-28 | Visa International Service Association | Prevention of token authentication replay attacks system and method |
| CN111447183B (en) * | 2020-03-06 | 2021-12-21 | 支付宝(杭州)信息技术有限公司 | Clone detection method and device |
| CN111585771B (en) * | 2020-05-20 | 2021-07-06 | 浙江大学 | A centralized authentication system for IoT devices based on U2F physical tokens |
| CN111740846B (en) * | 2020-08-04 | 2020-11-24 | 飞天诚信科技股份有限公司 | Method and system for realizing smart card information reading of mobile terminal |
| CN112003705B (en) * | 2020-08-12 | 2021-06-08 | 北京天融信网络安全技术有限公司 | Identity authentication method and device based on zero-knowledge proof |
| CN112422643B (en) * | 2020-11-02 | 2022-04-01 | 中关村科学城城市大脑股份有限公司 | Third-party interface protection request forwarding method and device |
| CN112491843B (en) * | 2020-11-17 | 2022-06-21 | 苏州浪潮智能科技有限公司 | Database multiple authentication method, system, terminal and storage medium |
| CN112434334B (en) * | 2020-11-25 | 2025-01-14 | 深圳前海微众银行股份有限公司 | Data processing method, device, equipment and storage medium |
| CN112311558B (en) | 2020-12-28 | 2021-04-06 | 飞天诚信科技股份有限公司 | Working method of key device and key device |
| CN112333214B (en) * | 2021-01-06 | 2021-03-30 | 北京邮电大学 | A security user authentication method and system for IoT device management |
| US11630723B2 (en) * | 2021-01-12 | 2023-04-18 | Qualcomm Incorporated | Protected data streaming between memories |
| CN113221136B (en) * | 2021-04-25 | 2024-04-12 | 亿海蓝(北京)数据技术股份公司 | AIS data transmission method, AIS data transmission device, electronic equipment and storage medium |
| CN113193964B (en) * | 2021-05-08 | 2023-02-07 | 国民认证科技(北京)有限公司 | Method and system for recognizing identity by combining gesture password with FIDO (fixed Internet data Access) |
| CN113806798B (en) * | 2021-08-13 | 2023-07-14 | 苏州浪潮智能科技有限公司 | A method, system, device and medium for client authentication |
| CN114430324B (en) * | 2022-01-02 | 2023-07-28 | 西安电子科技大学 | On-line rapid identity verification method based on hash chain |
| CN115694843B (en) * | 2022-12-29 | 2023-04-07 | 浙江宇视科技有限公司 | Avoid counterfeit camera access management methods, systems, devices and media |
| CN116567633B (en) * | 2023-07-10 | 2023-10-10 | 华侨大学 | Identity authentication method, system and equipment based on ECDSA signature algorithm |
| CN116976891B (en) * | 2023-07-21 | 2025-01-07 | 杭州易景数通科技有限公司 | Financial data security management system, device and method thereof |
| CN117040767B (en) * | 2023-10-10 | 2024-01-23 | 哈尔滨工业大学(深圳)(哈尔滨工业大学深圳科技创新研究院) | Fine-grained multi-terminal identity authentication method based on PUF (physical unclonable function) and related equipment |
| CN119996094A (en) * | 2025-04-17 | 2025-05-13 | 成都创信华通信息技术有限公司 | A client identity authentication and evaluation method, device and program product |
Family Cites Families (3)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US8762723B2 (en) * | 2011-07-07 | 2014-06-24 | Verayo, Inc. | Cryptographic security using fuzzy credentials for device and server communications |
| KR20140126787A (en) * | 2013-04-22 | 2014-11-03 | (주) 아이씨티케이 | Puf-based hardware device for providing one time password, and method for 2-factor authenticating using thereof |
| KR101744388B1 (en) * | 2014-04-09 | 2017-06-09 | (주) 아이씨티케이 | Apparatus and method for authenticating |
-
2017
- 2017-12-04 CN CN201711261470.3A patent/CN108092776B/en active Active
Cited By (1)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US12113895B2 (en) | 2020-12-11 | 2024-10-08 | PUFsecurity Corporation | Key management system providing secure management of cryptographic keys, and methods of operating the same |
Also Published As
| Publication number | Publication date |
|---|---|
| CN108092776A (en) | 2018-05-29 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| CN108092776B (en) | A system based on an authentication server and an authentication token | |
| US11855983B1 (en) | Biometric electronic signature authenticated key exchange token | |
| US11665006B2 (en) | User authentication with self-signed certificate and identity verification | |
| US12500760B2 (en) | Method, apparatus and device for constructing token for cloud platform resource access control | |
| CN109040067B (en) | A user authentication device and authentication method based on physical unclonable technology PUF | |
| CN108810029B (en) | A microservice architecture inter-service authentication system and optimization method | |
| US9887989B2 (en) | Protecting passwords and biometrics against back-end security breaches | |
| WO2022206349A1 (en) | Information verification method, related apparatus, device, and storage medium | |
| CN103124269B (en) | Based on the Bidirectional identity authentication method of dynamic password and biological characteristic under cloud environment | |
| CN100459488C (en) | Portable one-time dynamic password generator and security authentication system using the same | |
| EP3319292A1 (en) | Method for checking security based on biological features, client and server | |
| US11405387B1 (en) | Biometric electronic signature authenticated key exchange token | |
| CN104038486B (en) | System and method for realizing user login identification based on identification type codes | |
| CN104394172B (en) | Single-sign-on apparatus and method | |
| CN107809317A (en) | A kind of identity identifying method and system based on token digital signature | |
| CN104935568A (en) | Interface authentication signature method facing cloud platform | |
| CN111770088A (en) | Data authentication method, apparatus, electronic device and computer-readable storage medium | |
| JP2013509840A (en) | User authentication method and system | |
| WO2015188424A1 (en) | Key storage device and method for using same | |
| CN103051628A (en) | Method and system for obtaining authentication token based on servers | |
| CN104660583B (en) | A kind of cryptographic services method based on Web cryptographic services | |
| CN110659467A (en) | Remote user identity authentication method, device, system, terminal and server | |
| CN107277059A (en) | A kind of one-time password identity identifying method and system based on Quick Response Code | |
| CN111241492A (en) | Product multi-tenant secure credit granting method, system and electronic equipment | |
| CN118611919A (en) | A system and method for secure sharing of identity resolution data based on optimized Shiro framework |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| PB01 | Publication | ||
| PB01 | Publication | ||
| SE01 | Entry into force of request for substantive examination | ||
| SE01 | Entry into force of request for substantive examination | ||
| GR01 | Patent grant | ||
| GR01 | Patent grant |