CN100539586C - Method, system and equipment for supporting hierarchical mobile IP services - Google Patents
Method, system and equipment for supporting hierarchical mobile IP services Download PDFInfo
- Publication number
- CN100539586C CN100539586C CNB2004800234028A CN200480023402A CN100539586C CN 100539586 C CN100539586 C CN 100539586C CN B2004800234028 A CNB2004800234028 A CN B2004800234028A CN 200480023402 A CN200480023402 A CN 200480023402A CN 100539586 C CN100539586 C CN 100539586C
- Authority
- CN
- China
- Prior art keywords
- hmipv6
- map
- mobile node
- aaa
- eap
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Expired - Fee Related
Links
Images
Landscapes
- Mobile Radio Communication Systems (AREA)
Abstract
Description
技术领域 technical field
本发明一般涉及移动通信,并且更具体地涉及对移动IP(因特网协议)业务的支持,并且尤其是分级移动IP第6版业务。The present invention relates generally to mobile communications, and more particularly to the support of Mobile IP (Internet Protocol) services, and in particular Hierarchical Mobile IP Release 6 services.
背景技术 Background technique
移动IP(MIP)使移动节点(MN)可以以极小的服务中断更改它到因特网的连接点。MIP本身不提供任何对跨不同管理域的移动性的特定支持,这限制了在大规模商业部署中MIP的可应用性。Mobile IP (MIP) enables a Mobile Node (MN) to change its point of attachment to the Internet with minimal service interruption. MIP itself does not provide any specific support for mobility across different administrative domains, which limits the applicability of MIP in large-scale commercial deployments.
移动IP第6版(MIPv6)协议[1]使节点可以在因特网拓扑内移动,同时保持可达性和与通信节点的正进行连接。在此情况中,每个移动节点总是由它的归属地址来标识,而不管它到IPv6因特网的当前连接点。当远离它的归属网络时,移动节点还与转交地址(CoA)相关联,转交地址提供有关该移动节点的当前位置的信息。将寻址到移动节点的归属地址的IPv6分组或多或少透明地路由选择到它的转交地址。MIPv6协议使IPv6节点能够高速缓存移动节点的归属地址与它的转交地址的绑定,并然后将发往移动节点的任何分组发送到转交地址。为此,每次移动时,移动节点发送所说的绑定更新到它的归属代理(HA)以及它正在通信的通信节点。鉴权绑定更新需要一些在移动节点和每个通信节点之间的往返。此外,需要一个往返来更新归属代理,尽管这可以在更新通信节点的同时进行。每次执行到新接入路由器的切换时,这些往返延迟将中断有效连接。The Mobile IP Version 6 (MIPv6) protocol [1] enables nodes to move within the Internet topology while maintaining reachability and ongoing connectivity with communicating nodes. In this case, each mobile node is always identified by its home address, regardless of its current point of attachment to the IPv6 Internet. When away from its home network, a mobile node is also associated with a care-of address (CoA), which provides information about the mobile node's current location. IPv6 packets addressed to the mobile node's home address are routed more or less transparently to its care-of-address. The MIPv6 protocol enables an IPv6 node to cache the binding of a mobile node's home address to its care-of address, and then send any packets destined for the mobile node to the care-of address. To this end, each time it moves, the mobile node sends said binding update to its home agent (HA) and to the correspondent nodes it is communicating with. Authentication binding updates require some round trips between the mobile node and each correspondent node. Furthermore, a round trip is required to update the home agent, although this can be done at the same time as the correspondent node is updated. These round-trip delays interrupt active connectivity each time a switchover to a new access router is performed.
为此以及其他原因,提出了分级移动IPv6(HMIPv6)协议[2],以支持本地或分级形式的移动性管理。移动IPv6的分级移动性管理通过引入所说的位于受访网络的移动锚点(MAP)来降低MN、它的通信节点(CN)以及它的HA之间的信令数量。MAP的引入还可以用于提高移动IPv6在切换速度方面的性能。For this and other reasons, the Hierarchical Mobile IPv6 (HMIPv6) protocol [2] was proposed to support local or hierarchical forms of mobility management. Hierarchical mobility management for Mobile IPv6 reduces the amount of signaling between a MN, its Correspondent Node (CN) and its HA by introducing so-called Mobility Anchor Points (MAPs) located in the visited network. The introduction of MAP can also be used to improve the performance of moving IPv6 in terms of switching speed.
图1示意地示出现有技术的MAP在受访网络中的HMIPv6域的示例。整个系统视图包括具有普通归属代理(HA)15的归属网络10、具有MAP25和接入路由器(AR)27的受访网络20。进入MAP域的移动节点(MN)30将接收所说的含有关于一个或多个本地MAP的信息的路由器公告。MN 30可以将其当前的位置(链路相关转交地址或LCoA)与称为区域转交地址(RCoA)的MAP的子网上的地址绑定。作为本地HA,MAP 25将代表它正服务的MN 30接收所有分组,并将封装它们并直接转发到MN的LCoA。Fig. 1 schematically shows an example of the HMIPv6 domain of the MAP in the visited network in the prior art. The overall system view includes a
当移动节点在与通信节点(CN)40通信时从接入路由器1(AR1)27-1移动到接入路由器2(AR2)27-2时,MAP可以帮助为移动节点提供无缝移动。当到达受访网络时,移动节点30将发现MAP25的全局地址。该地址存储在接入路由器中,并经由路由器公告传送到移动节点。此过程称为MAP发现,并且需要执行该过程来通知移动节点存在MAP。MAP域通常由向连接的移动节点公告MAP信息的接入路由器来限定。MAP发现过程在移动节点从一个子网移动到下一个子网时继续。只要移动节点在MAP域内漫游,则接入路由器配置为公告相同的MAP地址。如果接收到公告的MAP的地址中改变,则移动节点必须执行移动检测,并向它的归属代理和通信节点发送必要的绑定更新。MAP can help provide seamless mobility for a mobile node as it moves from Access Router 1 (AR1) 27-1 to Access Router 2 (AR2) 27-2 while communicating with a Correspondent Node (CN) 40 . When arriving at the visited network, the
如果移动节点不是知道HMIPv6的,则将不执行MAP发现,且将移动IPv6将用于移动性管理。另一方面,如果移动节点是知道HMIPv6的,则它应该选择使用HMIPv6。如果这样,移动节点通过发送含有其归属地址和LCoA地址的绑定更新来向MAP 25登记。绑定更新中所用的归属地址是RCoA地址,并且MAP 25将此信息存储在它的绑定高速缓存中,以可以在从通信节点40或HA 15接收到分组时将它们转发到它们的最终目的地。If the mobile node is not HMIPv6 aware, MAP discovery will not be performed and Mobile IPv6 will be used for mobility management. On the other hand, if the mobile node is HMIPv6 aware, it should choose to use HMIPv6. If so, the mobile node registers with the
像MIP一样,HMIPv6本身不提供任何对跨不同管理域的移动性的特定支持,这限制了在大规模商业部署中HMIPv6的可应用性。Like MIP, HMIPv6 itself does not provide any specific support for mobility across different administrative domains, which limits the applicability of HMIPv6 in large-scale commercial deployments.
通常可以预期,MN在被授权使用HMIPv6的业务之前需要首先经过鉴权。重要的是,移动节点与MAP之间的安全关系具有强壮的性质;它应该优选地涉及互相鉴权、完整性保护和防重放攻击保护。为此,如MN和MAP之间的安全密钥的证书相关数据的分发目前需要依赖于公共密钥基础结构(PKI)和其他复杂的协议。目前的HMIPv6草案[2]还将MAP的位置限制于受访网络。Generally, it can be expected that the MN needs to be authenticated first before being authorized to use HMIPv6 services. It is important that the security relationship between the mobile node and the MAP is of a strong nature; it should preferably involve mutual authentication, integrity protection and protection against replay attacks. To this end, the distribution of certificate-related data such as security keys between MNs and MAPs currently needs to rely on Public Key Infrastructure (PKI) and other complex protocols. The current HMIPv6 draft [2] also restricts the location of the MAP to the visited network.
发明内容 Contents of the invention
本发明克服了现有技术安排的这些和其他缺点。The present invention overcomes these and other disadvantages of prior art arrangements.
本发明的一般目的是提供对移动节点的HMIPv6业务的改进支持。解决方案应该优选地包括便于部署HMIPv6的机制。A general object of the present invention is to provide improved support for HMIPv6 traffic to mobile nodes. The solution should preferably include mechanisms to facilitate the deployment of HMIPv6.
具体地,希望提供一种HMIPv6业务的鉴权和授权的流线式但健壮的解决方案,它不需要依赖于公共密钥基础结构(PKI)和其他复杂的协议。In particular, it is desirable to provide a streamlined but robust solution for authentication and authorization of HMIPv6 traffic, which does not need to rely on public key infrastructure (PKI) and other complex protocols.
本发明的另一个目的是允许缩短整个HMIPv6建立时间。Another object of the invention is to allow shortening of the overall HMIPv6 setup time.
本发明的再一个目的是提供一种用于支持HMIPv6业务的方法和系统。Another object of the present invention is to provide a method and system for supporting HMIPv6 services.
本发明的又一个目的是提供支持HMIPv6业务的流线式鉴权和/或授权的单独的网络组件。Yet another object of the present invention is to provide individual network components that support streamlined authentication and/or authorization of HMIPv6 traffic.
如所附专利权利要求限定的,由本发明来满足这些和其他目的。These and other objects are met by the present invention, as defined by the appended patent claims.
本发明的基本特征是依赖AAA基础结构来“引导”移动节点的HMIPv6业务。根据本发明的首选实施例,引导HMIPv6业务涉及基于AAA基础结构为HMIPv6业务对移动节点鉴权和授权。在重要的场合中,移动节点在受访网络中漫游,并且AAA基础结构将受访网络与移动节点的归属网络链接。但是,本发明还支持移动节点实际位于归属网络时的场合。在此情况中,归属网络的AAA基础结构组件可以用归属网络中的MAP提供对HMIPv6业务的必要支持。An essential feature of the present invention is that it relies on the AAA infrastructure to "bootstrap" the HMIPv6 traffic of the mobile node. According to a preferred embodiment of the present invention, directing HMIPv6 traffic involves authenticating and authorizing mobile nodes for HMIPv6 traffic based on the AAA infrastructure. In important scenarios, the mobile node roams in a visited network, and the AAA infrastructure links the visited network with the mobile node's home network. However, the invention also supports the case when the mobile node is actually located in the home network. In this case, the AAA infrastructure components of the home network can use the MAP in the home network to provide the necessary support for HMIPv6 services.
对AAA基础结构的依赖优选地涉及通过AAA基础结构传送为HMIPv6业务对移动节点授权所需的HMIPv6相关信息。The reliance on the AAA infrastructure preferably involves the transfer of HMIPv6 related information needed to authorize the mobile node for HMIPv6 traffic via the AAA infrastructure.
HMIPv6引导通常基于在适当的MAP与移动节点之间建立安全关联,以使相关的通信安全,例如允许鉴权的HMIPv6MAP绑定。HMIPv6 bootstrapping is usually based on establishing security associations between appropriate MAPs and mobile nodes to make associated communications secure, eg HMIPv6 MAP bindings that allow authentication.
在本发明的首选实施例中,在与HMIPv6安全关联过程相同的往返中捎带传输HMIPv6移动性过程使得可能通过在公共过程中优化鉴权、授权和移动性来缩短整个建立时间。In a preferred embodiment of the invention, piggybacking the HMIPv6 mobility procedures in the same round trip as the HMIPv6 security association procedures makes it possible to reduce the overall setup time by optimizing authentication, authorization and mobility in common procedures.
授权阶段自然包括显式授权,但是还可以包括所涉及的节点的配置。HMIPv6相关配置,如移动节点的配置和/或MAP的配置,因此通常可以视为整个授权过程的一部分。这往往意味着HMIPv6相关信息可以是HMIPv6鉴权、授权和/或配置信息。The authorization phase naturally includes explicit authorization, but may also include configuration of the nodes involved. HMIPv6 related configurations, such as the configuration of the mobile node and/or the configuration of the MAP, can therefore generally be considered as part of the overall authorization process. This often means that HMIPv6 related information may be HMIPv6 authentication, authorization and/or configuration information.
代替常规的MAP发现过程,响应从移动节点发起的MAP指定请求(移动节点发起的MAP指定)或作为网络发起的重新指定,AAA基础结构优选地用于将适当的MAP指定给移动节点。Instead of the conventional MAP discovery process, the AAA infrastructure is preferably used to assign the appropriate MAP to the mobile node in response to a MAP assignment request initiated from the mobile node (Mobile Node Initiated MAP Assignment) or as a network initiated reassignment.
还认识到,存在这样的情况,使MAP位于归属网络或其他网络中是有益的,例如对于受访网络不提供MAP支持的情况。位于归属网络中的MAP可以用于解决HA可伸缩性问题,通过减少MAP域内移动期间去往HA的绑定更新的数量来卸载HA。通过选择在地形上靠近MN位置的MAP,可以实现快速切换。It is also recognized that there are situations where it is beneficial to have the MAP located in the home network or other network, eg where the visited network does not provide MAP support. The MAP located in the home network can be used to solve the HA scalability problem by offloading the HA by reducing the number of binding updates to the HA during intra-domain mobility of the MAP. Fast switching can be achieved by selecting a MAP that is topographically close to the MN's location.
在MAP位于归属网络时的情况中,将AAA归属网络服务器(AAAh)用作适合用于MAP指定的AAA基础结构组件可以是适当的。另一方面,当MAP位于受访网络时,将AAA受访网络服务器(AAAv)用于MAP指定可以是适当的。实际上,MAP的位置可以在归属网络、受访网络或其他网络中。在预定的MAP域内不再对含关于MAP的信息的路由器公告有任何强制依赖性。In the case when the MAP is located in the home network, it may be appropriate to use the AAA Home Network Server (AAAh) as an AAA infrastructure component suitable for MAP assignment. On the other hand, when the MAP is located in the visited network, it may be appropriate to use an AAA visited network server (AAAv) for MAP assignment. Actually, the location of the MAP can be in the home network, the visited network or other networks. There is no longer any mandatory dependency on router advertisements containing information about MAPs within a predetermined MAP domain.
相对于使用PKI基础结构,对AAA基础结构的依赖提供用于引导HMIPv6业务的不同可能性。例如,提供对通过AAA基础结构承载的普通鉴权协议的扩展和/或增强AAA框架协议应用是可能的。The reliance on the AAA infrastructure offers different possibilities for directing HMIPv6 traffic compared to using a PKI infrastructure. For example, it is possible to provide extensions to common authentication protocols carried over the AAA infrastructure and/or to enhance AAA frame protocol applications.
例如,已经证明,在移动节点和AAA归属网络服务器之间在端到端过程中在鉴权协议内传送HMIPv6相关信息是非常有益的。鉴权协议可以是基于现有协议的扩展鉴权协议或新协议。For example, it has proven to be very beneficial to transfer HMIPv6 related information within the authentication protocol in the end-to-end procedure between the mobile node and the AAA home network server. The authentication protocol can be an extended authentication protocol based on an existing protocol or a new protocol.
一种可能的用作引导HMIPv6的基础的鉴权协议是可扩展鉴权协议(EAP),创建EAP扩展同时优选地保持EAP较低层完整。这通常意味着将HMIPv6相关信息作为附加数据结合在EAP协议栈中,例如作为EAP协议栈的EAP方法层中的EAP属性或在EAP层或EAP方法层上的通用容器中传送。One possible authentication protocol to use as the basis for bootstrapping HMIPv6 is the Extensible Authentication Protocol (EAP), creating EAP extensions while preferably keeping the EAP lower layers intact. This usually means incorporating HMIPv6 related information as additional data in the EAP protocol stack, e.g. as EAP attributes in the EAP method layer of the EAP protocol stack or conveyed in a generic container on the EAP layer or EAP method layer.
用作对EAP扩展的补充或备选的另一种方式是,增强EAP“较低层”,如创建新的或扩展的AAA框架协议应用,例如适合于HMIPv6的直径应用或基于RADIUS协议的应用。Another way to use as a supplement or alternative to EAP extensions is to enhance EAP "lower layers", such as creating new or extended AAA frame protocol applications, such as Diameter applications or RADIUS protocol-based applications suitable for HMIPv6.
当MAP位于归属网络中时,例如使用通过AAA基础结构承载的扩展的鉴权协议或增强的AAA框架协议应用是可能的。但是,当MAP位于受访网络中时,优选地结合增强的AAA框架协议应用来使用扩展的EAP协议,或者备选地在不支持任何EAP扩展的情况下使用增强的AAA框架协议应用。When the MAP is located in the home network, it is possible, for example, to use extended authentication protocols or enhanced AAA frame protocol applications carried over the AAA infrastructure. However, when the MAP is located in the visited network, the extended EAP protocol is preferably used in conjunction with the enhanced AAA frame protocol application, or alternatively the enhanced AAA frame protocol application is used without supporting any EAP extensions.
例如,在移动节点与受访网络中的AAA客户之间,扩展的EAP协议可以由PANA(用于承载网络接入鉴权的协议)、PPP(点到点协议)、IEEE 802.1X或甚至通过GPRS/UMTS接口来承载,以及在AAA基础结构内由直径或RADIUS应用来承载。For example, between the mobile node and the AAA client in the visited network, the extended EAP protocol can be implemented by PANA (Protocol for Bearer Network Access Authentication), PPP (Point-to-Point Protocol), IEEE 802.1X or even through GPRS/UMTS interface, and within the AAA infrastructure by Diameter or RADIUS applications.
具体地,依赖EAP扩展提供一种流线式解决方案,它易于管理且一流,向后兼容问题最少。EAP的使用使AAA客户(和AAAv)可以至少在MAP位于归属网络中时对HMIPv6过程不可知(agnostic)(即,这去除对受访网络的HMIPv6支持的依赖),并仅充当直通(pass-through)代理。这是使用EAP的主要优点之一。Specifically, relying on EAP extensions provides a streamlined solution that is manageable and classy with minimal backward compatibility issues. The use of EAP enables AAA clients (and AAAv) to be agnostic to HMIPv6 procedures at least while the MAP is in the home network (i.e. this removes the reliance on the visited network's HMIPv6 support) and act only as a pass-through through) proxy. This is one of the main advantages of using EAP.
通过还在扩展的鉴权协议栈中或在增强的AAA框架协议应用中包括MIPv6相关信息,通过AAA基础结构同时将HMIPv6和MIPv6鉴权和授权容纳于相同的往返中是可能的。当然可能的是,使用这样的启用MIPv6/HMIPv6的网络并在没有MIPv6鉴权和/或授权的情况下仅执行HMIPv6鉴权和/或授权,且反之亦然,取决于特定情况下MN的具体需求。这使单个扩展的鉴权协议和/或增强的AAA框架协议应用可以灵活地在各种用例场合使用。By including MIPv6 related information also in the extended authentication protocol stack or in the enhanced AAA framework protocol application, it is possible to accommodate both HMIPv6 and MIPv6 authentication and authorization in the same round trip through the AAA infrastructure. It is of course possible to use such a MIPv6/HMIPv6-enabled network and perform only HMIPv6 authentication and/or authorization without MIPv6 authentication and/or authorization, and vice versa, depending on the specific circumstances of the MN in a particular case. need. This enables a single extended authentication protocol and/or enhanced AAA framework protocol application to be flexibly used in various use cases.
本发明提供以下优点:The present invention provides the following advantages:
·有效地引导HMIPv6业务;·Effectively guide HMIPv6 business;
·有效地传送用于授权HMIPv6业务的HMIPv6相关信息;Effectively transmit HMIPv6-related information used to authorize HMIPv6 services;
·基于EAP扩展的HMIPv6支持的流线式解决方案,它易于管理且一流,向后兼容问题最少;A streamlined solution based on EAP extensions for HMIPv6 support, which is easy to manage and best-in-class with minimal backward compatibility issues;
·缩短整个HMIPv6建立时间;Shorten the entire HMIPv6 establishment time;
·在公共过程中优化鉴权、授权和移动性;· Optimize authentication, authorization and mobility in common procedures;
·基于AAA的MAP指定;AAA-based MAP designation;
·MAP位置不限于受访网络;The MAP location is not limited to the visited network;
·MAP可以位于归属网络中,以解决HA可伸缩性问题,通过减少MAP域内移动期间去往HA的绑定更新的数量来卸载HA;以及MAPs can be located in the home network to address HA scalability issues, offloading HA by reducing the number of binding updates to HA during intra-domain mobility of the MAP; and
·同时将HMIPv6和MIPv6鉴权和授权容纳于相同的往返中。• Accommodates both HMIPv6 and MIPv6 authentication and authorization in the same round trip.
当阅读以下对本发明实施例的描述时,将理解本发明提供的其他优点。Other advantages offered by the invention will be understood when reading the following description of the embodiments of the invention.
附图简介 Brief introduction to the drawings
通过参考以下结合附图进行的描述,可以非常好地理解本发明及其其他目的和优点,图中:The present invention, together with other objects and advantages thereof, may be best understood by reference to the following description taken in conjunction with the accompanying drawings, in which:
图1是示出现有技术的MAP在受访网络中的HMIPv6域的示例的示意图;FIG. 1 is a schematic diagram showing an example of an HMIPv6 domain of a MAP in a visited network in the prior art;
图2是示出根据本发明示范实施例的在受访网络中漫游的移动节点的HMIPv6支持的创新体系结构的示意图;2 is a schematic diagram illustrating an innovative architecture of HMIPv6 support for a mobile node roaming in a visited network according to an exemplary embodiment of the present invention;
图3是示出根据本发明另一个示范实施例的在受访网络中漫游的移动节点的HMIPv6支持的创新体系结构的示意图;3 is a schematic diagram illustrating an innovative architecture of HMIPv6 support for a mobile node roaming in a visited network according to another exemplary embodiment of the present invention;
图4是示出根据本发明示范实施例的在其自己的归属网络中操作的移动节点的HMIPv6支持的创新体系结构的示意图;4 is a schematic diagram illustrating an innovative architecture of HMIPv6 support for a mobile node operating in its own home network according to an exemplary embodiment of the present invention;
图5是根据本发明首选示范实施例的AAA归属网络服务器的示意框图;5 is a schematic block diagram of an AAA home network server according to a preferred exemplary embodiment of the present invention;
图6是根据本发明首选示范实施例的MAP节点的示意框图;Figure 6 is a schematic block diagram of a MAP node according to a preferred exemplary embodiment of the present invention;
图7示出对于MAP位于归属网络时的情况、使用直径/EAP/HMIPv6的HMIPv6AAA的示范信令流;Figure 7 shows an exemplary signaling flow for HMIPv6 AAA using Diameter/EAP/HMIPv6 for the case when the MAP is located in the home network;
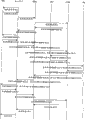
图8示出对于MAP位于受访网络时的情况、结合直径HMIPv6应用、使用直径/EAP/HMIPv6的HMIPv6AAA的示范信令流;Figure 8 shows an exemplary signaling flow for HMIPv6 AAA using Diameter/EAP/HMIPv6 in conjunction with Diameter HMIPv6 applications for the case when the MAP is located in the visited network;
图9示出对于MAP位于归属网络时的情况、使用直径HMIPv6应用的HMIPv6AAA的示范信令流;Figure 9 shows an exemplary signaling flow for HMIPv6 AAA using Diameter HMIPv6 applications for the case when the MAP is located in the home network;
图10示出对于MAP位于受访网络时的情况、使用直径HMIPv6应用的HMIPv6AAA的示范信令流;以及Figure 10 shows an exemplary signaling flow for HMIPv6 AAA using Diameter HMIPv6 applications for the case when the MAP is located in the visited network; and
图11是用于支持移动节点的HMIPv6业务的方法的说明性示例的示意流程图。Figure 11 is a schematic flow diagram of an illustrative example of a method for supporting HMIPv6 traffic for a mobile node.
具体实施方式 Detailed ways
在所有附图中,对于对应的或相似的部件将使用相同的引用符号。Throughout the drawings, the same reference signs will be used for corresponding or analogous parts.
根据本发明的基本思想是,为了HMIPv6鉴权和授权,基于AAA基础结构而不是依赖于复杂的PKI基础结构来“引导”移动节点的HMIPv6业务。HMIPv6引导对于在归属网络中操作的移动节点和在受访网络中漫游的移动节点都是有效的,在前一种情况中采用归属网络AAA基础结构,而在后一种情况中采用将受访网络与归属网络链接的整个AAA基础结构。The basic idea according to the invention is to "bootstrap" the HMIPv6 traffic of a mobile node for HMIPv6 authentication and authorization based on an AAA infrastructure instead of relying on a complex PKI infrastructure. HMIPv6 bootstrapping is valid for both a mobile node operating in a home network and a mobile node roaming in a visited network, in the former case using the home network AAA infrastructure and in the latter case using the visited The entire AAA infrastructure where the network is linked with the home network.
代替通过采用公共密钥基础结构(PKI)在MN和MAP之间建立安全关联和分发安全密钥,优选地基于AAA基础结构来执行HMIPv6业务的鉴权和授权,例如通过AAA基础结构传送为HMIPv6业务对移动节点鉴权和授权所需的HMIPv6相关信息。Instead of establishing a security association and distributing security keys between the MN and the MAP by employing a public key infrastructure (PKI), it is preferable to perform authentication and authorization of HMIPv6 services based on the AAA infrastructure, for example conveyed as HMIPv6 via the AAA infrastructure HMIPv6-related information required by services for mobile node authentication and authorization.
代替常规的MAP发现过程,响应从移动节点发起的MAP指定请求(移动节点发起的MAP指定)或作为网络发起的重新指定,还优选地将AAA基础结构用于将适当的MAP指定给移动节点,稍后将进行更详细地描述。在预定的MAP域内不再对含关于MAP的信息的路由器公告有任何强制依赖性。Instead of the conventional MAP discovery process, the AAA infrastructure is also preferably used to assign the appropriate MAP to the mobile node in response to a MAP assignment request initiated from the mobile node (Mobile Node Initiated MAP Assignment) or as a network initiated reassignment, It will be described in more detail later. There is no longer any mandatory dependency on router advertisements containing information about MAPs within a predetermined MAP domain.
AAA HMIPv6引导通常是基于通过AAA基础结构的在适当的MAP与移动节点之间的安全关联即安全关系的建立,以使相关通信安全,例如允许鉴权的HMIPv6MAP绑定。AAA HMIPv6 bootstrapping is usually based on the establishment of a security association, i.e., a security relationship, between the appropriate MAP and the mobile node through the AAA infrastructure to secure the associated communication, such as HMIPv6 MAP binding that allows authentication.
在首选实施方式中,在与HMIPv6安全关联过程相同的往返中捎带传输包括绑定更新的HMIPv6移动性过程,由此使得可能通过在公共过程中优化鉴权、授权和移动性来缩短整个建立时间。In a preferred embodiment, the HMIPv6 mobility procedure including the binding update is piggybacked in the same round trip as the HMIPv6 security association procedure, thus making it possible to reduce the overall setup time by optimizing authentication, authorization and mobility in common procedures .
术语“AAA”应该取其因特网草案、RFC和其他标准化文档中的一般含义。通常,AAA(授权、鉴权、计费)基础结构的鉴权和安全密钥同意基于对称密码学,意味着在移动节点和归属网络营运商或可信方之间存在共享的初始秘密。在一些场合和应用中,例如可以禁用或不实施AAA基础结构的计费特征。AAA基础结构在归属网络、中间网络(如果有的话)和/或受访网络中一般包括一个或多个AAA服务器,而且还可以包括一个或多个AAA客户。The term "AAA" should be taken in its ordinary meaning in Internet-Drafts, RFCs, and other standardization documents. Typically, the authentication and security key agreement of the AAA (Authorization, Authentication, Accounting) infrastructure is based on symmetric cryptography, meaning that there is a shared initial secret between the mobile node and the home network operator or trusted party. In some scenarios and applications, for example, the accounting features of the AAA infrastructure may be disabled or not implemented. The AAA infrastructure typically includes one or more AAA servers, and may also include one or more AAA clients, in the home network, intermediate network (if any) and/or visited network.
一般来说,如直径协议的AAA协议恰恰使移动用户能够在不一定由他们的归属服务提供商所有的网络中漫游和获得服务。因此为了在商业网络中部署移动IP,需要有对该协议的AAA支持。对于无任何分级移动性管理的移动IPv6(MIPv6)的特殊情况,提出了因特网草案[3],它规定一种直径的新应用,它启用在不是归属营运商管理的网络的网络中漫游的MIPv6。在我们于2003年6月18日提交的美国临时专利伸请60/479156并且还在后来的因特网草案[4]中,建议一种用于基于AAA基础结构来执行移动IPv6授权和配置的体系结构和相关协议。归属提供商的AAA服务器与移动节点之间的为MIPv6的必要交互是使用EAP(可扩展鉴权协议)来实现的,它将用于移动IPv6协商的信息与鉴权数据一起传送。In general, AAA protocols like Diameter precisely enable mobile users to roam and obtain service in networks not necessarily owned by their home service provider. Therefore, in order to deploy Mobile IP in commercial networks, AAA support for this agreement is required. For the special case of Mobile IPv6 (MIPv6) without any hierarchical mobility management, an Internet-Draft [3] is proposed, which specifies a new application of Diameter that enables roaming in networks other than those managed by the home operator . In our US provisional patent application 60/479156 filed on June 18, 2003 and also in a later Internet-Draft [4], an architecture for performing Mobile IPv6 authorization and configuration based on an AAA infrastructure is proposed and related agreements. The necessary interaction for MIPv6 between the home provider's AAA server and the mobile node is achieved using EAP (Extensible Authentication Protocol), which transfers information for Mobile IPv6 negotiation together with the authentication data.
图2是示出一种根据本发明示范实施例的HMIPv6支持的创新体系结构的示意图。移动节点130在受访网络中漫游,并通过使用将受访网络与移动节点的归属网络链接的AAA基础结构来执行HMIPv6鉴权和授权。在该示例中,AAA基础结构基本上涉及AAA归属网络服务器110、受访网络中的AAA受访网络服务器120和AAA客户122。Fig. 2 is a schematic diagram showing an innovative architecture supported by HMIPv6 according to an exemplary embodiment of the present invention. The
优选地,可以将AAA受访网络服务器(AAAv)120用作适合用于MAP指定的AAA基础结构组件,在选择MAP时考虑受访营运商的策略。MAP的选择可以例如基于可用MAP的当前负载、移动节点的位置和/或可能由移动节点给出的偏好。Preferably, an AAA Visited Network Server (AAAv) 120 may be used as an AAA infrastructure component suitable for MAP assignment, taking into account the visited operator's policy when selecting a MAP. The selection of the MAP may eg be based on the current load of available MAPs, the location of the mobile node and/or preferences possibly given by the mobile node.
AAA基础结构的主要组件是AAAh服务器110,它优选地将对MAP指定的任何请求从移动节点转发到AAAv服务器120,并还生成用于在给定的移动节点130和指定的MAP 125之间的立即的或将来的安全关联的安全密钥或类似的证书。然后通常将安全密钥经由AAAv 120从AAAh 110传送到MAP 125,并且MAP 125优选地经由AAAv 120以用于完成安全关联的信息响应AAAh 110。最后,AAAh服务器110将生成的且收集的HMIPv6授权信息通过AAA基础结构发送到移动节点130。假定采用AAA基础结构的安全隧道或其他安全措施如加密和源完整性保护来传送如安全密钥的敏感信息。The main component of the AAA infrastructure is the
对AAA基础结构的依赖提供用于引导HMIPv6业务的不同可能性。例如,提供新的鉴权协议或提供对通过AAA基础结构承载的鉴权协议的扩展和/或增强AAA框架协议应用以承载HMIPv6相关信息是可能的,如图2示意所示。The reliance on the AAA infrastructure offers different possibilities for directing HMIPv6 traffic. For example, it is possible to provide a new authentication protocol or provide an extension of the authentication protocol carried by the AAA infrastructure and/or enhance the application of the AAA framework protocol to carry HMIPv6 related information, as schematically shown in FIG. 2 .
优选地,利用扩展的鉴权协议,如适合于HMIPv6的扩展EAP(可扩展鉴权协议)协议,另外还有增强的AAA框架协议应用,如用于AAAh服务器与受访网络MAP之间的经由AAAv服务器的接口的HMIPv6直径或RADIUS应用。Preferably, an extended authentication protocol is used, such as an extended EAP (Extensible Authentication Protocol) protocol suitable for HMIPv6, and an enhanced AAA framework protocol application, such as for the via between the AAAh server and the visited network MAP The HMIPv6-diameter or RADIUS application for the interface of the AAAv server.
例如,在移动节点与受访网络中的AAA客户之间,一种新的或扩展的鉴权协议可以由PANA(用于承载网络接入鉴权的协议)、PPP(点到点协议)、IEEE 802.1X或甚至通过GPRS/UMTS接口来承载,以及在AAA基础结构内由直径或类似的AAA框架或载体协议来承载。For example, between the mobile node and the AAA client in the visited network, a new or extended authentication protocol can be composed of PANA (protocol for bearer network access authentication), PPP (point-to-point protocol), IEEE 802.1X or even carried over the GPRS/UMTS interface, and within the AAA infrastructure by Diameter or similar AAA frame or bearer protocols.
备选地,在不支持任何EAP扩展的情况下,使用增强的AAA框架协议应用,如一种新的或扩展的直径或RADIUS应用。对于移动节点和AAA客户之间的路径,可以例如由ICMP(因特网控制消息协议)来承载直径或RADIUS应用。Alternatively, an enhanced AAA profile application, such as a new or extended Diameter or RADIUS application, is used without supporting any EAP extensions. For the path between the mobile node and the AAA client, Diameter or RADIUS applications can be carried eg by ICMP (Internet Control Message Protocol).
还认识到,存在这样的情况,使MAP位于归属网络或其他网络中是有益的,例如对于受访网络不提供MAP支持的情况。图3示出MAP位于归属网络时HMIPv6支持的示范体系结构。It is also recognized that there are situations where it is beneficial to have the MAP located in the home network or other network, eg where the visited network does not provide MAP support. Figure 3 shows an exemplary architecture supported by HMIPv6 when the MAP is located in the home network.
此处将AAA归属网络服务器(AAAh)110用于MAP指定是有益的。优选地,AAA归属网络服务器(AAAh)110还生成用于在移动节点与指定的MAP 125之间的安全关联的安全密钥或类似的安全参数或证书,并将所述安全密钥发送到MAP 125。MAP 125以用于完成安全关联的信息响应AAAh 110,并且AAAh 110随后通过AAA基础结构将MIPv6授权信息发送到移动节点130。It is beneficial here to use the AAA Home Network Server (AAAh) 110 for MAP assignment. Preferably, the AAA home network server (AAAh) 110 also generates a security key or similar security parameters or certificates for the security association between the mobile node and the designated
因为MAP125位于归属网络,所以AAAv120无需查看该事务,并且具有用于HMIPv6鉴权和授权的“端到端过程”从而是可能的。这优选地通过使用扩展的鉴权协议来实现,如适合于HMIPv6的扩展EAP(可扩展鉴权协议)协议。备选地,可以利用增强的AAA框架协议应用,如HMIPv6直径或RADIUS应用。位于归属网络的MAP125还可以用于解决HA可伸缩性问题,通过减少MAP域内移动期间去往HA 115的绑定更新的数量来卸载HA。通过选择在地形上靠近MN位置的MAP,可以实现快速切换。Since the
应该理解,本发明去除了MAP 125需要位于受访网络的现有技术的限制。现在,MAP的位置可以在归属网络、受访网络或其他网络中。在技术上来说,MN与任何MAP绑定都是可能的,只要利用AAA支持可以获得MAP上的RCoA,如果营运商允许这样的话。It should be appreciated that the present invention removes the prior art limitation of requiring the
在以下示范情况期间可以发生MAP的重新指定:Reassignment of a MAP can occur during the following exemplary situations:
·MN和MAP之间的安全密钥到期-对于此情况,MN发起HMIPv6重新鉴权/授权,并且网络可以基于例如MN的当前拓扑位置指定不同的更适当的MAP。• Expiration of security keys between MN and MAP - For this case, the MN initiates HMIPv6 re-authentication/authorization and the network can assign a different more appropriate MAP based eg on the current topological location of the MN.
·在移动节点请求时(MN发起的)-对于此情况,MN发起HMIPv6重新鉴权/授权,请求重新指定MAP。• On mobile node request (MN initiated) - For this case, the MN initiates HMIPv6 re-authentication/authorization, requesting reassignment of the MAP.
·在网络请求时(网络发起的)-对于此情况,AAAh或AAAv发起MAP的重新指定,并在此需求出现时,例如当MN移动到由新MAP更好地覆盖的AR时将其“推”给MN。· At network request (network-initiated) - for this case, AAAh or AAAv initiates the reassignment of the MAP and "pushes" it when the need arises, for example when the MN moves to an AR that is better covered by the new MAP. "To MN.
再参考图2和3,下面概括段AAA客户-AAAh和AAAh-(AAAv)-MAP之间的不同协议组合的若干可能的示例:Referring again to Figures 2 and 3, several possible examples of different protocol combinations between segments AAA Client-AAAh and AAAh-(AAAv)-MAP are summarized below:
组合(iii)尤其适用于MAP位于归属网络的情况。当MAP位于受访网络时,在基于受访网络策略选择MAP时可能涉及AAAv。Combination (iii) is especially applicable when the MAP is located in the home network. When the MAP is located in the visited network, AAAv may be involved in selecting the MAP based on the visited network policy.
在图4示意示出的另一个场合中,移动节点130实际位于归属网络,并且归属网络的AAA基础结构组件如AAAh服务器110利用归属网络中的MAP125提供对HMIPv6业务的必要支持。这意味着只需要将扩展的鉴权HMIPv6协议和AAA HMIPv6应用的相关部分用于交换必要的鉴权和授权信息。In another situation schematically shown in FIG. 4 , the
图5是根据本发首选示范实施例的AAA归属网络服务器的示意框图。在此示例中,AAAh服务器110基本上包括任选的MAP指定模块111、安全关联模块112、授权信息管理器113和输入/输出(I/O)接口114。对于MAP在归属网络中的情况,AAAh服务器110包括MAP指定模块111,它可操作用于指定和/或重新指定适合的MAP给移动节点。对于MAP在受访网络中的情况,AAAh服务器110通常在其I/O接口114上接收必要的MAP指定信息。AAAh服务器通常还从移动节点接收密钥种子和绑定更新(BU)。备选地,AAAh服务器本身生成密钥种子并将其发送到移动节点。安全关联模块112优选地生成所需的安全密钥以响应该种子,并将该密钥安全地发送到MAP(直接到归属网络中的MAP或经由AAAv服务器到受访网络中的MAP)。绑定更新(BU)也被转发到MAP。AAAh服务器110从MAP接收RCoA地址并将该数据连同其他相关授权(和/或配置)信息存储在授权信息管理器113中。AAAh服务器还可以从MAP接收用于完成安全关联的诸如IPSec信息的信息。最后,将收集的授权(和/或配置)信息传送到移动节点。Fig. 5 is a schematic block diagram of an AAA home network server according to a preferred exemplary embodiment of the present invention. In this example, the
AAAh服务器还可以负责归属地址指定(除非归属地址是由MN本身配置的)和/或归属代理指定。The AAAh Server may also be responsible for Home Address Assignment (unless the Home Address is configured by the MN itself) and/or Home Agent Assignment.
图6是根据本发明首选示范实施例的MAP节点的示意框图。在此示例中,MAP125基本上包括RCoA指定模块126、安全关联模块127和输入/输出(I/O)接口128。MAP优选地与AAA归属网络服务器交互,以支持建立与移动节点的安全关联。MAP通过I/O接口128从AAA归属网络服务器接收安全密钥,以安全地存储在安全关联模块127中。MAP还准备用于完成与移动节点的安全关联所必需的信息,并将其发送回AAA归属网络服务器,又通过AAA基础结构将其转发到移动节点。为在MAP中绑定,RCoA模块126优选地指定RCoA地址给移动节点,并将该地址连同移动节点的LCoA地址存储在MAP的绑定高速缓存(未示出)中,并且还将指定的RCoA地址发送到AAA归属网络服务器,以随后转发到移动节点。Fig. 6 is a schematic block diagram of a MAP node according to a preferred exemplary embodiment of the present invention. In this example,
为了更好地理解本发明,将马上描述HMIPv6的扩展鉴权协议和适合于HMIPv6的AAA框架协议应用的更详细一些的示例。In order to better understand the present invention, some more detailed examples of the extended authentication protocol of HMIPv6 and the application of the AAA framework protocol suitable for HMIPv6 will be described shortly.
HMIPv6的扩展鉴权协议Extended Authentication Protocol of HMIPv6
在首选示范实施例中,定义了一种HMIPv6的扩展鉴权协议,本文以新的或扩展EAP鉴权协议(称为“HMIPv6鉴权方法”或“EAP/HMIPv6”)为例,它承载便于例如发现MAP、动态分配MAP、动态分配RCoA、MN和MAP之间分发安全密钥和/或可能的捎带传输HMIPv6移动性过程的HMIPv6相关信息。In the preferred exemplary embodiment, an extended authentication protocol of HMIPv6 is defined. This paper takes the new or extended EAP authentication protocol (referred to as "HMIPv6 authentication method" or "EAP/HMIPv6") as an example, which is convenient for carrying Such as discovery of MAP, dynamic allocation of MAP, dynamic allocation of RCoA, distribution of security keys between MN and MAP, and/or possible piggybacking of HMIPv6 related information for the HMIPv6 mobility process.
如果希望,HMIPv6和MIPv6鉴权和/或授权可以集成在相同的协议中,例如将EAP/HMIPv6定义为EAP/MIPv6协议的超集,除了MIPv6特定的类型-长度-值(TLV),它还定义新的HMIP特定的TLV属性。通过将EAP/MIPv6TLV属性作为EAP/HMIPv6的一部分包括,将MIPv6和HMIPv6鉴权和/或授权的同时执行容纳于单个遍历中是可能的,这允许更短的建立时间。还可能的是在没有MIPv6鉴权和/或授权的情况下仅执行HMIPv6鉴权和/或授权,且反之亦然,取决于特定情况下MN的具体需求。这使单个EAP鉴权协议EAP/HMIPv6可以灵活地在各种用例场合使用。If desired, HMIPv6 and MIPv6 authentication and/or authorization can be integrated in the same protocol, e.g. EAP/HMIPv6 is defined as a superset of the EAP/MIPv6 protocol, in addition to the MIPv6 specific type-length-value (TLV), it also Defines new HMIP-specific TLV attributes. By including the EAP/MIPv6 TLV attributes as part of EAP/HMIPv6, it is possible to accommodate simultaneous performance of MIPv6 and HMIPv6 authentication and/or authorization in a single pass, which allows for shorter setup times. It is also possible to perform only HMIPv6 authentication and/or authorization without MIPv6 authentication and/or authorization, and vice versa, depending on the specific needs of the MN in a particular case. This enables a single EAP authentication protocol, EAP/HMIPv6, to be used flexibly in various use cases.
具体地,依赖EAP扩展提供一种流线式解决方案,它易于管理且一流,向后兼容问题最少。EAP的使用使AAA客户(和AAAv)可以至少在MAP位于归属网络时对HMIPv6过程不可知(即这去除对受访网络的HMIPv6支持的依赖),并仅充当直通代理。这是使用EAP的主要优点之一。Specifically, relying on EAP extensions provides a streamlined solution that is manageable and classy with minimal backward compatibility issues. The use of EAP allows the AAA client (and AAAv) to be agnostic of the HMIPv6 process at least while the MAP is in the home network (ie this removes the dependency on the visited network's HMIPv6 support) and just act as a pass-through proxy. This is one of the main advantages of using EAP.
如前面所指出的,在移动节点与受访网络中的AAA客户之间,EAP/HMIPv6可以例如由PANA、PPP、ICMP、IEEE 802.1X或甚至通过GPRS/UMTS接口来承载。虽然,PANA在一些情况中可能是首选的,但是如PPP[6]和IEEE 802.1X[7]的满足对较低层排序保证的EAP需求的其他载体协议可以用于承载MN和AAA客户之间的EAP/MIPv6。具体对于3GPP2 CDMA2000的情况,在MN和AAA客户之间,使用对于EAP[6]协议字段值设为C227(Hex)的PPP数据链路层协议封装来承载EAP/HMIPv6是可能的。As previously indicated, between the mobile node and the AAA client in the visited network, EAP/HMIPv6 can be carried eg by PANA, PPP, ICMP, IEEE 802.1X or even over the GPRS/UMTS interface. Although, PANA may be preferred in some cases, other bearer protocols such as PPP [6] and IEEE 802.1X [7] that meet the EAP requirements for lower layer ordering guarantees can be used to carry between MNs and AAA clients EAP/MIPv6. Specifically for the case of 3GPP2 CDMA2000, between the MN and the AAA client, it is possible to use the PPP data link layer protocol encapsulation with the value of the EAP [6] protocol field set to C227 (Hex) to carry EAP/HMIPv6.
首选实施例将直径、RADIUS或类似的AAA框架或载体协议用于AAA客户与AAAh服务器之间的通信。例如,在AAA客户以外朝向AAA基础结构和在AAA基础结构内,直径EAP应用[5]可以用于将EAP/HMIPv6封装在直径内,即PAA/AAA客户和AAAh之间。直径协议还可以被AAAh用于经由MIP过滤器规则任选地将MIP分组过滤器指定给PAA/EP和HA,它们对应于过滤器增强点。为PAA安全,直径协议还可以被AAAh用于将安全密钥分发给PAA,以及任选地发送QoS参数信号。The preferred embodiment uses Diameter, RADIUS or similar AAA framework or bearer protocol for communication between the AAA client and the AAAh server. For example, the Diameter EAP application [5] can be used to encapsulate EAP/HMIPv6 within the Diameter, outside the AAA client towards the AAA infrastructure and within the AAA infrastructure, ie between the PAA/AAA client and AAAh. The Diameter protocol can also be used by AAAh to optionally assign MIP packet filters to PAA/EP and HA via MIP filter rules, which correspond to filter enhancement points. For PAA security, the Diameter protocol can also be used by the AAAh to distribute security keys to the PAA, and optionally signal QoS parameters.
应该注意,尽管直径是首选,但是有时改为使用另一种具有对本领域技术人员显而易见的修改的如RADIUS的AAA协议可以是适当的。It should be noted that while Diameter is preferred, sometimes it may be appropriate to use another AAA protocol like RADIUS with modifications obvious to those skilled in the art instead.
再者,在EAP/HMIPv6中捎带传输HMIPv6移动性过程使得可能通过在公共过程中优化鉴权、授权和移动性来缩短整个建立时间。Furthermore, piggybacking HMIPv6 mobility procedures in EAP/HMIPv6 makes it possible to shorten the overall setup time by optimizing authentication, authorization and mobility in common procedures.
示范EAP/HMIPv6协议的详细信息Demonstrate details of EAP/HMIPv6 protocol
在下文中,提供示范EAP/HMIPv6协议的详细信息,以说明整体流程的示例和概念的可行性(viability of concept)。In the following, details of the exemplary EAP/HMIPv6 protocol are provided to illustrate an example of the overall flow and the viability of concept.
EAP TLV属性EAP TLV attributes
在第一实现示例中,根据EAP/HMIPv6定义一组新的EAP TLV属性。凭借这些属性,除了主要的IPv6鉴权信息,EAP协议还可以承载HMIPv6相关信息和任选地还可以承载MIPv6相关信息。In a first implementation example, a new set of EAP TLV attributes is defined according to EAP/HMIPv6. With these properties, besides the main IPv6 authentication information, the EAP protocol can also carry HMIPv6 related information and optionally MIPv6 related information.
对于EAP/HMIPv6,不同的鉴权协议是可能的。在首选实施例中,本发明提出通过MD5询问鉴权的实施方式,但是其他协议也属于本发明的范围。For EAP/HMIPv6 different authentication protocols are possible. In the preferred embodiment, the present invention proposes the implementation of authentication via MD5 challenge, but other protocols are also within the scope of the present invention.
下表1中给出EAP/HMIPv6 TLV的示范概括矩阵:An exemplary summary matrix of EAP/HMIPv6 TLVs is given in Table 1 below:
注意:IKE KeyID包括一些八位位组,它告知HA/MAP如何从AAA检索(或生成)HA-MN预共享密钥/MAP-MN预共享密钥。NOTE: IKE KeyID includes octets that tell HA/MAP how to retrieve (or generate) HA-MN pre-shared key/MAP-MN pre-shared key from AAA.
可以为HMIPv6定义以下示范EAP-TLV属性的一个或多个:One or more of the following exemplary EAP-TLV attributes may be defined for HMIPv6:
·RCoA请求EAP-TLV属性:· RCoA requests EAP-TLV attributes:
这表示对鉴权的MN的动态分配的RCoA地址的请求。在MN请求被鉴权和被给予HMIPv6业务时,由MN向AAAH请求它。This represents a request for a dynamically assigned RCoA address for an authenticated MN. When the MN requests to be authenticated and given HMIPv6 service, it is requested by the MN from the AAAH.
·RCoA响应EAP-TLV属性:RCoA response EAP-TLV attributes:
这表示鉴权的MN的动态分配的RCoA地址。在对例如已经请求的MN成功鉴权时,从AAAh将其通知给MN。This represents the dynamically assigned RCoA address of the authenticated MN. Upon successful authentication of, for example, a MN that has requested, this is notified to the MN from the AAAh.
·RCoA EAP-TLV属性:RCoA EAP-TLV attributes:
这表示鉴权的MN的动态分配的RCoA地址。在对例如已经请求的MN成功鉴权时,从AAAh将其通知给MAP,以在MAP中指定RCoA地址。This represents the dynamically assigned RCoA address of the authenticated MN. Upon successful authentication of, for example, a MN that has requested, it is notified from the AAAh to the MAP to specify the RCoA address in the MAP.
·MAP地址请求EAP-TLV属性:MAP Address Request EAP-TLV Attributes:
这表示当成功鉴权时对MN的动态分配的MAP的地址的请求。在MN请求被鉴权和被给予HMIPv6业务时,由MN向AAAH请求它。因为HMIPv6协议具有动态MAP发现方法来分配MAP,所以该属性是任选的。This represents a request for the address of the MN's dynamically allocated MAP upon successful authentication. When the MN requests to be authenticated and given HMIPv6 service, it is requested by the MN from the AAAH. Since the HMIPv6 protocol has a dynamic MAP discovery method to allocate MAPs, this attribute is optional.
·MAP地址响应EAP-TLV属性:MAP address response EAP-TLV attribute:
这表示鉴权的MN的动态分配的MAP地址。当MN请求被鉴权和被给予HMIPv6业务时,从AAAh将其通知给MN。因为HMIPv6协议具有动态MAP发现方法来分配MAP,所以该属性是任选的。This represents the dynamically assigned MAP address of the authenticated MN. When a MN requests to be authenticated and given HMIPv6 service, it is notified to the MN from AAAh. Since the HMIPv6 protocol has a dynamic MAP discovery method to allocate MAPs, this attribute is optional.
·MAP-MN预共享密钥生成现用值EAP-TLV属性:· MAP-MN pre-shared key generation present value EAP-TLV attribute:
这表示MN随机生成的作为用于生成MAP-MN之间的预共享密钥的种子的八位位组串。通过对该现用值和MN与AAAh之间的共享密钥的组合使用适当的散列算法,MN可以内部生成MAP-MN预共享密钥。当已经存在有效的MAP-MN预共享密钥时,该属性是任选的。This indicates an octet string randomly generated by the MN as a seed for generating a pre-shared key between MAP-MNs. By using an appropriate hashing algorithm on the combination of this nonce and the shared key between the MN and AAAh, the MN can internally generate a MAP-MN pre-shared key. This attribute is optional when a valid MAP-MN pre-shared key already exists.
·MAP-MN预共享密钥EAP-TLV属性:· MAP-MN pre-shared key EAP-TLV attributes:
这表示MAP--MN之间动态生成的预共享密钥。当MN请求被鉴权和被给予HMIPv6业务时,从AAAh将其通知给MAP。通过对由MAP-MN预共享密钥生成现用值EAP-TLV属性给出的现用值和MN与AAAh之间的共享密钥的组合使用适当的散列算法,AAAh可以内部生成MAP-MN预共享密钥。当已经存在有效的MAP-MN预共享密钥时,该属性是任选的。This means MAP—a dynamically generated pre-shared key between MNs. When the MN requests to be authenticated and given HMIPv6 service, it is notified to the MAP from AAAh. AAAh can internally generate a MAP-MN by using an appropriate hashing algorithm on the combination of the nonce given by the MAP-MN pre-shared key generation nonce EAP-TLV attribute and the shared key between the MN and AAAh pre-shared key. This attribute is optional when a valid MAP-MN pre-shared key already exists.
·MAP IKE KeyID EAP-TLV属性:MAP IKE KeyID EAP-TLV attributes:
这表示[8]中定义的ID有效负荷。KeyID由AAAh生成,并当成功鉴权时被发送到MN。KeyID包括一些八位位组,它告知MAP如何从AAAh检索(或生成)MAP-MN预共享密钥。该属性是任选的,以及当MN未提交MAP-MN预共享密钥生成现用值即已经存在有效的MAP-MN预共享密钥时,例如MIPv6切换期间,一般不需要该属性。对于MAP-MN预共享密钥由AAAh传送到MAP时的情况也不需要该属性。This represents the ID payload as defined in [8]. KeyID is generated by AAAh and sent to MN upon successful authentication. KeyID consists of octets that tell the MAP how to retrieve (or generate) the MAP-MN pre-shared key from the AAAh. This attribute is optional and is generally not required when the MN has not submitted a MAP-MN pre-shared key generation nonce, ie a valid MAP-MN pre-shared key already exists, such as during MIPv6 handover. This attribute is also not required for the case when the MAP-MN pre-shared key is transmitted by AAAh to the MAP.
·MAP-MN IPSec SPI EAP-TLV属性:MAP-MN IPSec SPI EAP-TLV attributes:
这表示MAP-MN之间的IPSec的安全参数索引。对于MAP-MN预共享密钥由AAAh传送到MAP时的情况,这优选地由MAP生成,并通知给MN。该属性是任选的,以及当MN未提交MAP-MN预共享密生成现用值即已经存在有效的MAP--MN预共享密钥时,例如MIPv6切换期间,一般不需要该属性。This indicates the security parameter index of IPSec between MAP-MN. For the case when the MAP-MN pre-shared key is transferred to the MAP by AAAh, this is preferably generated by the MAP and notified to the MN. This attribute is optional, and when the MN has not submitted the MAP-MN pre-shared secret to generate the nonce, that is, there is already a valid MAP--MN pre-shared key, such as during MIPv6 handover, this attribute is generally not required.
·MAP-MN IPSec协议EAP-TLV属性:MAP-MN IPSec protocol EAP-TLV attributes:
这表示MAP-MN之间的IPSec协议(例如ESP或AH)。对于MAP-MN预共享密钥由AAAh传送到MAP时的情况,这被通知给MN。该属性是任选的,以及当MN未提交MAP-MN预共享密钥生成现用值即已经存在有效的MAP-MN预共享密钥时,例如MIPv6切换期间,一般不需要该属性。This represents an IPSec protocol (eg ESP or AH) between MAP-MN. This is notified to the MN for the case when the MAP-MN pre-shared key is transferred by AAAh to the MAP. This attribute is optional and is generally not required when the MN has not submitted a MAP-MN pre-shared key generation nonce, ie a valid MAP-MN pre-shared key already exists, such as during MIPv6 handover.
·MAP-MN IPSec密码EAP-TLV属性:MAP-MN IPSec password EAP-TLV attribute:
这表示MAP-MN之间的IPSec的密码算法。对于MAP-MN预共享密钥由AAAh传送到MAP时的情况,这被通知给MN。该属性是任选的,以及当MN未提交MAP-MN预共享密钥生成现用值即已经存在有效的MAP-MN预共享密钥时,例如MIPv6切换期间,一般不需要该属性。This indicates the encryption algorithm of IPSec between MAP-MN. This is notified to the MN for the case when the MAP-MN pre-shared key is transferred by AAAh to the MAP. This attribute is optional and is generally not required when the MN has not submitted a MAP-MN pre-shared key generation nonce, ie a valid MAP-MN pre-shared key already exists, such as during MIPv6 handover.
·MAP--MN IPSec密钥有效期EAP-TLV属性:MAP--MN IPSec key validity period EAP-TLV attribute:
这表示MAP-MN之间的IPSec的密钥有效期。对于MAP-MN预共享密钥由AAAh传送到MAP时的情况,这被通知给MN。该属性是任选的,以及当MN未提交MAP--MN预共享密钥生成现用值即已经存在有效的MAP-MN预共享密钥时,例如MIPv6切换期间,一般不需要该属性。This indicates the key validity period of IPSec between MAP-MN. This is notified to the MN for the case when the MAP-MN pre-shared key is transferred by AAAh to the MAP. This attribute is optional, and is generally not required when the MN has not submitted the MAP--MN pre-shared key generation nonce, ie there is already a valid MAP-MN pre-shared key, such as during MIPv6 handover.
·HMIP-绑定-更新EAP-TLV属性:HMIP-bind-update EAP-TLV attributes:
这表示MN生成的MAP绑定更新分组。这在鉴权和授权交换中经由AAAh从MN转发到MAP。该属性是任选的,以及当MN将MAP绑定更新分组直接发送到MAP时,一般不需要该属性。This represents the MAP Binding Update packet generated by the MN. This is forwarded from the MN to the MAP via the AAAh in an authentication and authorization exchange. This attribute is optional and generally not required when the MN sends MAP Binding Update packets directly to the MAP.
·HMIP-绑定-确认EAP-TLV属性:HMIP-Binding-Confirm EAP-TLV Attributes:
这表示MAP生成的MAP绑定确认分组。这在鉴权和授权交换中经由AAAh从MAP转发到MN。该属性是任选的,以及当MAP将MAP绑定确认更新分组直接发送到MN时,一般不需要该属性。This represents the MAP Binding Ack packet generated by the MAP. This is forwarded from the MAP to the MN via the AAAh in an authentication and authorization exchange. This attribute is optional and generally not required when the MAP sends the MAP Binding Ack Update packet directly to the MN.
对于特殊的MIPv6,可以定义以下任选的EAP-TLV属性:For MIPv6-specific, the following optional EAP-TLV attributes may be defined:
·MIPv6归属地址EAP-TLV属性:· MIPv6 home address EAP-TLV attribute:
这表示鉴权的MN的动态分配的MIPv6归属地址。在对例如已经请求的MN成功鉴权时从AAAh将其通知给HA,以在HA中指定MIPv6归属地址。This represents the dynamically assigned MIPv6 home address of the authenticated MN. The HA is notified from the AAAh upon successful authentication of, for example, the MN that has requested, to specify the MIPv6 home address in the HA.
·HA-MN预共享密钥EAP-TLV属性:HA-MN pre-shared key EAP-TLV attributes:
这表示HA-MN之间的动态生成的预共享密钥。当MN请求被鉴权和被给予MIPv6业务时,从AAAh将其通知给HA。通过对由HA-MN预共享密钥生成现用值EAP-TLV属性给出的现用值和MN与AAAh之间的共享密钥的组合使用适当的散列算法,AAAh可以内部生成HA-MN预共享密钥。当已经存在有效的HA-MN预共享密钥时,该属性是任选的。This represents a dynamically generated pre-shared key between HA-MN. When MN requests to be authenticated and given MIPv6 service, it is notified to HA from AAAh. AAAh can internally generate the HA-MN by using an appropriate hashing algorithm on the combination of the nonce given by the HA-MN pre-shared key generation nonce EAP-TLV attribute and the shared key between the MN and AAAh pre-shared key. This attribute is optional when a valid HA-MN pre-shared key already exists.
·HA-MN IPSec协议EAP-TLV属性:HA-MN IPSec protocol EAP-TLV attributes:
这表示HA--MN之间的IPSec协议(例如ESP或AH)。对于HA-MN预共享密钥由AAAh传送到HA时的情况,这被通知给MN。该属性是任选的,以及当MN未提交HA-MN预共享密钥生成现用值即已经存在有效的HA-MN预共享密钥时,例如MIPv6切换期间,一般不需要该属性。This represents an IPSec protocol (eg ESP or AH) between HA-MNs. This is notified to the MN for the case when the HA-MN pre-shared key is transferred to the HA by AAAh. This attribute is optional, and when the MN has not submitted the HA-MN pre-shared key to generate the present value, that is, there is already a valid HA-MN pre-shared key, such as during MIPv6 handover, this attribute is generally not required.
·HA-MN IPSec密码EAP-TLV属性:HA-MN IPSec password EAP-TLV attribute:
这表示HA-MN之间的IPSec的密码算法。对于HA-MN预共享密钥由AAAh传送到HA时的情况,这被通知给MN。该属性是任选的,以及当MN未提交HA-MN预共享密钥生成现用值即已经存在有效的HA-MN预共享密钥时,例如MIPv6切换期间,一般不需要该属性。This indicates the encryption algorithm of IPSec between HA-MN. This is notified to the MN for the case when the HA-MN pre-shared key is transferred to the HA by AAAh. This attribute is optional, and when the MN has not submitted the HA-MN pre-shared key to generate the present value, that is, there is already a valid HA-MN pre-shared key, such as during MIPv6 handover, this attribute is generally not required.
·MIP-绑定-更新EAP-TLV属性:MIP-Binding-Update EAP-TLV Attributes:
这表示MN生成的绑定更新分组。这在鉴权和授权交换中经由AAAh从MN转发到HA。该属性是任选的,以及当MN将绑定更新分组直接发送到HA时,一般不需要该属性。This represents the Binding Update packet generated by the MN. This is forwarded from the MN to the HA via the AAAh in an authentication and authorization exchange. This attribute is optional and generally not required when the MN sends Binding Update packets directly to the HA.
·MIP-绑定-确认EAP-TLV属性:MIP-Binding-Confirm EAP-TLV Attributes:
这表示HA生成的绑定确认分组。这在鉴权和授权交换中经由AAAh从HA转发到MN。该属性是任选的,以及当HA将绑定确认分组直接发送到MN时,一般不需要该属性。This represents the Binding Ack packet generated by the HA. This is forwarded from the HA to the MN via the AAAh in an authentication and authorization exchange. This attribute is optional and generally not required when the HA sends the Binding Ack packet directly to the MN.
可以定义以下用于HMIPv6/MIPv6鉴权的EAP-TLV属性:The following EAP-TLV attributes for HMIPv6/MIPv6 authentication can be defined:
·MD5询问EAP-TLV属性:MD5 query EAP-TLV attributes:
这表示AAAh随机生成并发送到MN以实现MD5询问的八位位组串。This represents the octet string that the AAAh randomly generates and sends to the MN to implement the MD5 challenge.
·MD5响应EAP-TLV属性:MD5 response EAP-TLV attributes:
这表示作为MD5散列函数的结果生成的连同AAAh和MN之间的预共享秘密密钥的八位位组串。This represents the octet string generated as a result of the MD5 hash function together with the pre-shared secret key between AAAh and the MN.
对于动态MN归属地址分配,可以定义以下任选的EAP-TLV属性:For dynamic MN home address assignment, the following optional EAP-TLV attributes may be defined:
·MIPv6归属地址请求EAP-TLV属性:· MIPv6 home address request EAP-TLV attribute:
这表示对鉴权的MN的动态分配的MIPv6归属地址的请求。在MN最初请求被鉴权和被给予MIPv6业务时,由MN向AAAh请求它。当MN已经具有先前指定的归属地址时,例如MIPv6切换期间,该属性是任选的。This represents a request for a dynamically assigned MIPv6 home address of the authenticated MN. It is requested from AAAh by the MN when it initially requests to be authenticated and given MIPv6 service. This attribute is optional when the MN already has a previously assigned home address, eg during MIPv6 handover.
·MIPv6归属地址响应EAP-TLV属性:MIPv6 home address response EAP-TLV attribute:
这表示鉴权的MN的动态分配的MIPv6归属地址。在对例如已经请求的MN成功鉴权时,从AAAh将其通知给MN。当MN已经具有先前指定的归属地址时,例如MIPv6切换期间,该属性是任选的。This represents the dynamically assigned MIPv6 home address of the authenticated MN. Upon successful authentication of, for example, a MN that has requested, this is notified to the MN from the AAAh. This attribute is optional when the MN already has a previously assigned home address, eg during MIPv6 handover.
对于动态HA分配,可以定义以下任选的EAP-TLV属性:For dynamic HA allocation, the following optional EAP-TLV attributes may be defined:
·MIPv6归属代理地址请求EAP-TLV属性:·MIPv6 Home Agent Address Request EAP-TLV Attributes:
这表示当成功鉴权时对MN的动态分配的HA的地址的请求。在MN最初请求被鉴权和被给予MIPv6业务时,由MN向AAAH请求它。当MIPv6协议具有动态HA发现方法以分配HA时,该属性是任选的。当MN已经具有先前指定的HA时,例如MIPv6切换期间,该属性也是任选的。This represents a request for the address of the MN's dynamically assigned HA upon successful authentication. When the MN initially requests to be authenticated and given MIPv6 service, it is requested from the AAAH by the MN. This attribute is optional when the MIPv6 protocol has a dynamic HA discovery method to assign HAs. This attribute is also optional when the MN already has a previously assigned HA, eg during MIPv6 handover.
·MIPv6归属代理地址响应EAP-TLV属性:MIPv6 Home Agent Address Response EAP-TLV Attribute:
这表示鉴权的MN的动态分配的HA地址。当MN最初请求被鉴权和被给予MIPv6业务时,从AAAh将其通知给MN。因为MIPv6协议具有动态的归属代理发现方法以分配归属代理,所以该属性是任选的。当MN已经具有先前指定的HA时,例如MIPv6切换期间,该属性也是任选的。This represents the dynamically assigned HA address of the authenticated MN. When the MN initially requests to be authenticated and given MIPv6 service, it is notified to the MN from AAAh. This attribute is optional because the MIPv6 protocol has a dynamic home agent discovery method to assign a home agent. This attribute is also optional when the MN already has a previously assigned HA, eg during MIPv6 handover.
可以定义以下任选的EAP-TLV属性以在HA和MN之间分发安全密钥:The following optional EAP-TLV attributes may be defined to distribute security keys between HA and MN:
·HA-MN预共享密钥生成现用值EAP-TLV属性:HA-MN pre-shared key generation present value EAP-TLV attribute:
这表示MN随机生成的作为用于生成HA-MN之间预共享密钥的种子的八位位组串。通过对该现用值和MN与AAAh之间的共享密钥的组合使用适当的散列算法,MN可以内部生成HA-MN预共享密钥。当已经存在有效的HA-MN预共享密钥时,例如MIPv6切换期间,该属性常是任选的。This indicates an octet string randomly generated by the MN as a seed for generating an inter-HA-MN pre-shared key. By using an appropriate hashing algorithm on the combination of the nonce and the shared key between the MN and AAAh, the MN can internally generate the HA-MN pre-shared key. This attribute is often optional when a valid HA-MN pre-shared key already exists, eg during MIPv6 handover.
·IKE KeyID EAP-TLV属性:IKE KeyID EAP-TLV attribute:
这表示[8]中定义的ID有效负荷。KeyID由AAAh生成,并当成功鉴权时被发送到MN。KeyID包括一些八位位组,它告知HA如何从AAAh检索(或生成)HA-MN预共享密钥。该属性是任选的,以及当MN未提交HA-MN预共享密钥生成现用值即已经存在有效的HA-MN预共享密钥时,例如MIPv6切换期间,一般不需要该属性。在HA-MN预共享密钥由AAAh经由[9]中定义的AAAh-HA接口传送到HA时的情况中也不需要该属性。This represents the ID payload as defined in [8]. KeyID is generated by AAAh and sent to MN upon successful authentication. KeyID consists of octets that tell the HA how to retrieve (or generate) the HA-MN pre-shared key from the AAAh. This attribute is optional, and when the MN has not submitted the HA-MN pre-shared key to generate the present value, that is, there is already a valid HA-MN pre-shared key, such as during MIPv6 handover, this attribute is generally not required. This attribute is also not required in the case when the HA-MN pre-shared key is transferred by AAAh to the HA via the AAAh-HA interface defined in [9].
·HA-MN IPSec SPI EAP-TLV属性:HA-MN IPSec SPI EAP-TLV attributes:
这表示HA和MN之间的IPSec的安全参数索引。对于HA-MN预共享密钥由AAAh经由[9]中定义的AAAh-HA接口传送到HA时的情况,这由HA生成并被通知给MN。该属性是任选的,以及当MN未提交HA-MN预共享密钥生成现用值即已经存在有效的HA-MN预共享密钥时,例如MIPv6切换期间,一般不需要它。当未使用[9]中定义的AAAh--HA接口时,也不需要它。This indicates the security parameter index of IPSec between HA and MN. For the case when the HA-MN pre-shared key is delivered by AAAh to the HA via the AAAh-HA interface defined in [9], this is generated by the HA and notified to the MN. This attribute is optional and is generally not needed when the MN has not submitted the HA-MN pre-shared key generation nonce, ie there is already a valid HA-MN pre-shared key, eg during MIPv6 handover. It is also not required when the AAAh--HA interface defined in [9] is not used.
·HA-MN IPSec密钥有效期EAP-TLV属性:HA-MN IPSec key validity period EAP-TLV attribute:
这表示HA和MN之间的IPSec的密钥有效期。对于HA-MN预共享密钥由AAAh经由[9]中定义的AAAh-HA接口传送到HA时的情况,这由HA生成并被通知给MN。该属性是任选的,以及当MN未提交HA-MN预共享密钥生成现用值即已经存在有效的HA-MN预共享密钥时,例如MIPv6切换期间,一般不需要该属性。当不使用[9]中定义的AAAh-HA接口时,也不需要它。This indicates the key validity period of IPSec between HA and MN. For the case when the HA-MN pre-shared key is delivered by AAAh to the HA via the AAAh-HA interface defined in [9], this is generated by the HA and notified to the MN. This attribute is optional, and when the MN has not submitted the HA-MN pre-shared key to generate the present value, that is, there is already a valid HA-MN pre-shared key, such as during MIPv6 handover, this attribute is generally not required. It is also not required when the AAAh-HA interface defined in [9] is not used.
最后,可以定义以下任选的EAP-TLV属性以在PAC和PAA之间分发安全密钥以实现PANA安全:Finally, the following optional EAP-TLV attributes can be defined to distribute security keys between the PAC and PAA for PANA security:
·PAC-PAA预共享密钥生成现用值EAP-TLV属性:· PAC-PAA pre-shared key generation present value EAP-TLV attribute:
这表示MN/PAC随机生成的作为用于生成PAC-PAA之间的预共享密钥的种子的八位位组串。通过对该现用值和MN与AAAh之间的共享密钥的组合使用适当的散列算法,MN/PAC可以内部生成PAC-PAA预共享密钥。需要该属性来实现PANA安全。This represents an octet string randomly generated by the MN/PAC as a seed for generating a pre-shared key between PAC-PAA. By using an appropriate hashing algorithm on the combination of this nonce and the shared key between the MN and AAAh, the MN/PAC can internally generate the PAC-PAA pre-shared key. This attribute is required for PANA security.
备选地,AAAh服务器可以配置用于不仅生成MN-MAP安全密钥,还生成完成安全关联所需的信息。Alternatively, the AAAh server can be configured to generate not only the MN-MAP security key, but also the information needed to complete the security association.
从上述示例可以看出,HMIPv6相关配置通常被视为整个授权过程的一部分。As can be seen from the above examples, HMIPv6-related configurations are generally considered part of the entire authorization process.
EAP通用容器属性(EAP GCA)EAP Generic Container Attributes (EAP GCA)
在备选的EAP实现中,EAP被用作HMIPv6相关信息的载体(任选地还有MIPv6信息),其中不创建新的所说的EAP方法,而是通过在可以与任何EAP方法一起使用的通用容器EAP属性中承载信息来实施。In an alternative EAP implementation, EAP is used as the bearer of HMIPv6 related information (and optionally MIPv6 information), where no new said EAP method is created, but is passed in the The implementation is carried out by carrying the information in the EAP attributes of the generic container.
在该基于接入网中AAA支持的示范实现中,EAP以通用容器属性来增补,通用容器属性可以用于承载任何(也许非EAP相关的)数据,例如HMIPv6特定的数据和任选地还有MIPv6特定的数据(如果还希望MIPv6引导的话)。这使MN和AAAh可以至少对于MAP在归属网络的情况以对受访域透明的方式通信,受访域包括接入网、AAA客户和AAAv。在AAA客户和AAA之间,EAP优选地在AAA协议中承载,例如直径EAP应用或甚至RADIUS[10]、[11]。In this exemplary implementation based on AAA support in the access network, EAP is supplemented with generic container attributes that can be used to carry any (perhaps non-EAP related) data, such as HMIPv6 specific data and optionally also MIPv6 specific data (if MIPv6 bootstrap is also desired). This enables the MN and AAAh to communicate in a manner transparent to the visited domain, including the access network, the AAA client and the AAAv, at least for the case of the MAP in the home network. Between the AAA client and AAA, EAP is preferably carried in an AAA protocol, eg Diameter EAP application or even RADIUS [10], [11].
该新属性应该优选地可用于所有EAP方法,而且可以被包括在任何EAP消息中,包括EAP成功/失败消息。在此解决方案中,该新通用容器属性用于在MN和AAAh之间传送HMIPv6特定的数据(任选地还有MIPv6数据)。该解决方案还可以包括用于在AAAh和HA之间交换AAA和相关数据的直径或RADIUS应用。This new attribute should preferably be available for all EAP methods, and can be included in any EAP message, including EAP success/failure messages. In this solution, this new generic container attribute is used to transfer HMIPv6 specific data (optionally also MIPv6 data) between the MN and the AAAh. The solution may also include a Diameter or RADIUS application for exchanging AAA and related data between the AAAh and the HA.
下文中,根据目前的EAP协议[12]来讨论通用容器属性(GCA)的可能实施方式。如所述,通用容器属性应该优选地可用于所有方法,而且应该可能在任何EAP消息中包括,包括EAP成功/失败消息。这意味着它应该是EAP层而非EAP方法层的一部分[12]。重要的问题是向后兼容(这是指就MN和EAP鉴权者(通常位于NAS)而言的向后兼容。MN和EAP鉴权服务器(即AAA)假定为总是兼容的)。在这些给定的示例中,GCA的使用一般假定,以向后兼容和对EAP鉴权者透明的方式在EAP中引入该新属性。引入含有这些特性的GCA需要一些特殊的考虑,将在下面讨论。In the following, possible implementations of Generic Container Attributes (GCA) are discussed according to the current EAP protocol [12]. As stated, common container attributes should preferably be available to all methods, and should be possible to include in any EAP message, including EAP success/failure messages. This means it should be part of the EAP layer and not the EAP method layer [12]. The important issue is backward compatibility (this means backward compatibility in terms of MN and EAP authenticator (usually located at NAS). MN and EAP authentication server (ie AAA) are assumed to be always compatible). In these given examples, the use of GCA generally assumes that this new attribute is introduced in EAP in a backward compatible and transparent manner to the EAP authenticator. Introducing a GCA with these features requires some special considerations, discussed below.
例如,GCA的格式可以是两字节的GCA长度指示符,后跟GCA接受方指示符和GCA有效负荷。GCA接受方指示符指示EAP模块应将接收到的GCA的有效负荷发送到什么内部实体(即该指示符对应于IP报头中的协议/下一个报头字段或UDP和TCP报头中的端口号)。GCA有效负荷则是不由EAP层解释的通用数据块。没有GCA优选地可以通过将GCA长度指示符设为零来指示。For example, the format of a GCA may be a two-byte GCA length indicator followed by a GCA recipient indicator and a GCA payload. The GCA recipient indicator instructs the EAP module to what internal entity the received GCA's payload should be sent (ie the indicator corresponds to the protocol/next header field in the IP header or the port number in the UDP and TCP headers). The GCA payload is a generic data block that is not interpreted by the EAP layer. No GCA may preferably be indicated by setting the GCA length indicator to zero.
为了实现向后兼容,GCA应该优选地以对直通EAP鉴权者透明的方式被包含在EAP分组中。直通EAP鉴权者是在MN和后端EAP鉴权服务器(AAA服务器)之间中继(几乎所有)EAP分组的EAP鉴权者(驻留在NAS中;通常是WLAN AP或接入路由器)。根据[12]中所述,EAP鉴权者的直通行为是基于EAP层报头来中继EAP分组,即EAP分组的开始位置中的代码、标识符和长度字段。这意味着,如果将GCA置于EAP层报头之后(即在代码、标识符和长度字段之后),则可能实现所期望的透明性(和由此实现向后兼容)。For backward compatibility, the GCA should preferably be included in the EAP packet in a manner transparent to the pass-through EAP authenticator. A pass-through EAP authenticator is an EAP authenticator that relays (almost all) EAP packets between the MN and the backend EAP authentication server (AAA server) (resides in the NAS; usually a WLAN AP or access router) . According to [12], the pass-through behavior of the EAP authenticator is to relay the EAP packet based on the EAP layer header, ie the code, identifier and length fields in the start position of the EAP packet. This means that if the GCA is placed after the EAP layer header (ie after the code, identifier and length fields), it is possible to achieve the desired transparency (and thus backward compatibility).
但是,EAP鉴权者一般还需要检查EAP响应分组的类型字段(在EAP层报头之后),以识别EAP身份响应分组,据此提取AAA路由选择所需的NAI。当EAP鉴权者识别EAP身份响应分组时,它从类型字段之后的类型-数据字段提取NAI。因此,将GCA置于紧随EAP层报头之后(以对EAP鉴权者透明的方式)仅在EAP请求分组中可能。因此,一般首选是将GCA安排在类型字段之后或甚至(可能空终止)类型-数据字段之后。However, the EAP authenticator generally also needs to check the type field of the EAP response packet (after the EAP layer header) to identify the EAP identity response packet, and extract the NAI required for AAA routing accordingly. When the EAP authenticator recognizes the EAP Identity Response packet, it extracts the NAI from the Type-Data field following the Type field. Therefore, placing the GCA immediately after the EAP layer header (in a manner transparent to the EAP authenticator) is only possible in EAP request packets. Therefore, it is generally preferred to arrange the GCA after the type field or even after the (possibly null-terminated) type-data field.
将GCA置于紧随类型字段之后允许在除EAP身份响应分组外的所有EAP响应分组中使用GCA。在EAP身份响应分组中使用GCA会被禁止,因为从这些分组中,EAP鉴权者需要从类型-数据字段提取NAI,而遗留EAP鉴权者预期在紧随类型字段之后查找它。考虑到EAP一般具有相当少的往返,这可能限制GCA的使用。可能,GCA可以被置于EAP身份响应分组中的空终止类型-数据字段之后,而在其他EAP分组中保持其在类型字段之后的位置。Placing GCA immediately after the Type field allows the use of GCA in all EAP Response packets except EAP Identity Response packets. The use of GCA in EAP Identity Response packets is prohibited because from these packets the EAP authenticator needs to extract the NAI from the Type-Data field, whereas legacy EAP authenticators are expected to look for it immediately after the Type field. Considering that EAP generally has relatively few round trips, this may limit the use of GCA. Possibly, the GCA could be placed after the null-terminated Type-Data field in the EAP Identity Response packet, while maintaining its position after the Type field in other EAP packets.
会经常希望可以在所有EAP分组中一致使用的GCA位置。从上述讨论看起来,可以以向后兼容的方式将GCA置于所有EAP分组中的位置是在分组的末端,或多或少作为尾部。但是,该GCA位置对于没有类型-数据参数的显式长度指示符而依赖于EAP层报头中的长度字段的那些EAP分组可能导致问题。在这些分组中,不能将GCA与类型-数据字段区分。It will often be desirable to have a GCA position that can be used consistently across all EAP packets. From the above discussion it appears that the place where the GCA can be placed in all EAP packets in a backward compatible manner is at the end of the packet, more or less as the tail. However, this GCA location may cause problems for those EAP packets that do not have an explicit length indicator for the type-data parameter but instead rely on the length field in the EAP layer header. In these packets, the GCA cannot be distinguished from the type-data field.
为了解决此问题,应该反转GCA长度指示符、GCA接受方指示符以及GCA有效负荷的次序,使得GCA长度指示符最后出现。从而,当将GCA置于EAP分组的末端时,EAP分组的最后两个八位位组(其长度由EAP层报头中的长度字段指示)始终会是GCA长度指示符。除非GCA长度指示符为零,GCA接受方指示符会出现在GCA长度指示符之前而GCA有效负荷(其大小由GCA长度指示符确定)位于GCA接受方指示符之前。通过该原理,识别EAP分组中的GCA并将GCA与类型-数据字段区分总是可能。GCA的使用仍是对直通EAP鉴权者透明的。To solve this problem, the order of the GCA length indicator, GCA recipient indicator and GCA payload should be reversed so that the GCA length indicator appears last. Thus, when a GCA is placed at the end of an EAP packet, the last two octets of the EAP packet (whose length is indicated by the length field in the EAP layer header) will always be the GCA length indicator. Unless the GCA length indicator is zero, the GCA recipient indicator will appear before the GCA length indicator and the GCA payload (whose size is determined by the GCA length indicator) will precede the GCA recipient indicator. By this principle it is always possible to identify the GCA in the EAP packet and to distinguish the GCA from the type-data field. The use of GCA is still transparent to the pass-through EAP authenticator.
与该GCA解决方案的向后兼容还要求,EAP鉴权者不尝试从EAP请求/响应分组提取信息(除了EAP层报头和NAI),并且它接受成功/失败分组中的长度字段指示大于4的值。Backwards compatibility with this GCA solution also requires that the EAP authenticator does not attempt to extract information from the EAP request/response packet (except the EAP layer header and the NAI), and that it accepts length fields in success/failure packets indicating values greater than 4 value.
处理向后兼容问题的备选方式是,使用EAP GCA测试请求/响应分组(即具有类型字段的新定义值的新EAP分组)来判断MN是否支持GCA。An alternative way to handle backward compatibility issues is to use EAP GCA test request/response packets (ie new EAP packets with newly defined values for the Type field) to determine whether the MN supports GCA.
在初始的EAP身份请求/响应分组交换前或后,支持GCA的EAP鉴权者将EAP GCA测试请求分组(即具有专用类型值的EAP请求分组)发送到MN。([13]中的EAP对等状态机器指示两种备选的发送时间都是可行的)。如果MN支持GCA,则它以EAP GCA测试响应分组响应。否则,MN将EAP GCA测试请求分组解释为使用未知EAP方法的请求,并由此MN以EAP Nak分组响应。基于来自MN的响应,EAP鉴权者可以判断MN是否支持GCA。Before or after the initial EAP Identity Request/Response packet exchange, the EAP Authenticator supporting GCA sends an EAP GCA Test Request packet (i.e., an EAP Request packet with a dedicated Type value) to the MN. (The EAP peer state machine in [13] indicates that both alternative send times are feasible). If the MN supports GCA, it responds with an EAP GCA Test Response packet. Otherwise, the MN interprets the EAP GCA Test-Request packet as a request to use an unknown EAP method, and thus the MN responds with an EAP Nak packet. Based on the response from the MN, the EAP authenticator can determine whether the MN supports GCA.
支持GCA的MN可以根据EAP GCA测试请求分组的有无来判断EAP鉴权者是否支持GCA。如果当期望时(即在EAP身份请求/响应交换前或后)接收到EAP GCA测试请求分组,则EAP鉴权者支持GCA。否则,EAP鉴权者不支持GCA。The MN that supports GCA can judge whether the EAP authenticator supports GCA according to whether there is an EAP GCA test request packet. The EAP authenticator supports GCA if an EAP GCA Test-Request packet is received when expected (i.e. before or after the EAP Identity Request/Response exchange). Otherwise, the EAP authenticator does not support GCA.
如果MN和EAP鉴权者都支持GCA,则可以将其置于所有随后的EAP分组中的EAP层报头之后(GCA分量为原始顺序)。否则,GCA可以仍被包含在EAP分组中,这些EAP分组使它可以以向后兼容方式被包含(如上所述)。If both the MN and the EAP authenticator support GCA, it can be placed after the EAP layer header in all subsequent EAP packets (GCA components in original order). Otherwise, the GCA may still be included in the EAP packets that enable it to be included in a backward compatible manner (as described above).
所述处理向后兼容问题的备选方式有一些局限。首先,浪费了一个MN-EAP鉴权者往返。再者,如果在初始的EAP身份请求/响应分组交换之后交换EAP GCA测试请求/响应分组,则GCA无法在EAP身份响应分组中使用。该实施例还可以要求EAP鉴权者(可能是NAS)使用EAP的修改版本,例如EAPv2。因此,虽然其他备选方式是可能的,但是将GCA安排在EAP分组中的首选方式通常会是在分组末端作为尾部,GCA长度指示符在最后,在GCA有效负荷和GCA接受方指示符之后。The described alternative ways of dealing with backward compatibility issues have some limitations. First, one MN-EAP authenticator round trip is wasted. Furthermore, if the EAP GCA test request/response packets are exchanged after the initial EAP Identity Request/Response packet exchange, GCA cannot be used in the EAP Identity Response packet. This embodiment may also require the EAP authenticator (possibly the NAS) to use a modified version of EAP, such as EAPv2. Therefore, although other alternatives are possible, the preferred way of arranging the GCA in the EAP packet will generally be at the end of the packet as a trailer, with the GCA length indicator at the end, after the GCA payload and the GCA recipient indicator.
如果对于在GCA中交换的数据,EAP往返的数量不够,则为了传送GCA,AAAh可以通过EAP通知请求/响应交换来增加EAP往返的数量。If the number of EAP round trips is not enough for the data exchanged in GCA, AAAh may increase the number of EAP round trips by EAP Notification Request/Response exchange in order to convey GCA.
另一种变体实际是在EAP协议栈的方法层上的EAP方法中引入GCA。如果GCA设为方法特定的,则GCA不会引入任何向后兼容问题,因为它将通常是类型-数据字段的一部分。Another variant actually introduces GCA in the EAP method on the method layer of the EAP protocol stack. If the GCA is made method-specific, the GCA won't introduce any backward compatibility issues, since it will normally be part of the type-data field.
EAP/HMIPv6的示范信令流Demonstration signaling flow of EAP/HMIPv6
图7示出针对MAP位于归属网络时的情况的示范EAP/HMIPv6(直径)信令流。Figure 7 shows an exemplary EAP/HMIPv6 (diameter) signaling flow for the case when the MAP is located in the home network.
AAA客户使用EAP(请求身份)请求MN鉴权,以及MN以EAP(响应身份)响应。The AAA client requests the MN to authenticate using the EAP (request identity), and the MN responds with the EAP (response identity).
MN响应经由AAA基础结构发送到AAAh。AAAh根据MN的身份和基于营运商策略确定EAP/HMIPv6方法适于MN的鉴权和授权(即AAAh知道MN的能力)。AAAh经由AAA基础结构向MN发送建议的EAP方法(例如EAP/HMIPv6)的指示连同询问。EAP方法或方案的指示可以通过为扩展的EAP方案(例如EAP/HMIPv6)指定新的EAP类型编号来实施。这样,移动节点将知道AAAh提出的是哪种EAP方案。备选地,向移动节点发送专门格式化的询问,移动节点识别该询问指示给定的EAP方案。The MN response is sent to AAAh via the AAA infrastructure. AAAh determines that the EAP/HMIPv6 method is suitable for the authentication and authorization of the MN according to the identity of the MN and based on the operator's policy (that is, AAAh knows the capabilities of the MN). The AAAh sends an indication of the proposed EAP method (eg EAP/HMIPv6) along with a query to the MN via the AAA infrastructure. The indication of the EAP method or scheme can be implemented by specifying a new EAP type number for the extended EAP scheme (eg EAP/HMIPv6). In this way, the mobile node will know which EAP scheme AAAh proposes. Alternatively, a specially formatted challenge is sent to the mobile node, which the mobile node recognizes indicates a given EAP scheme.
MN希望引导HMIPv6,并以询问响应以及适当的EAP属性(TLV)来答复AAAh建议和询问,适当的EAP属性(TLV)传送指定适当的MAP的请求连同用于与指定的MAP安全关联的必要信息。在此过程中,MN还可以引导MIPv6,如果先前尚未执行过的话。MN响应经由AAA基础结构发送到AAAh。虽然MAP指定请求实际可以是隐含的,但是一般推荐利用显式的MAP指定请求。对于移动节点已经知道MAP地址并且例如可以只更新与MAP的安全关联的情况,将不会有MAP指定请求,而仅有重新鉴权和/或重新授权。The MN wishes to bootstrap HMIPv6, and replies to the AAAh Proposal and Challenge with a Challenge Response with the appropriate EAP Attributes (TLV) conveying a request to specify the appropriate MAP along with the necessary information for security association with the specified MAP . During this process, the MN can also bootstrap MIPv6, if it has not been performed previously. The MN response is sent to AAAh via the AAA infrastructure. Although MAP-specific requests can actually be implicit, it is generally recommended to utilize explicit MAP-specific requests. For the case where the mobile node already knows the MAP address and can eg just update the security association with the MAP, there will be no MAP assignment request but only re-authentication and/or re-authorization.
AAAh验证MN的询问响应,并且如果成功,则这意味着MN是可信的,并且AAAh然后继续处理MN的其他请求。The AAAh verifies the MN's challenge response, and if successful, this means the MN is authentic, and the AAAh then proceeds to process other requests of the MN.
首先,AAAh在归属网络中选择MAP,并向MAP发送增强的包括例如安全密钥的EAP(注意这是不同于已经在MN和AAAh之间正进行的EAP会话的EAP会话)消息,并且MAP优选地通过提供用于完成与MN的安全关联的信息(如果是需要的或在其他方面是适当的)来对AAAh响应。例如,对于IPSec安全关联,可能需要利用EAP属性,如上表1中定义的IPSec协议、IPSec密码、IPSec密钥有效期EAP TLV属性。First, the AAAh selects a MAP in the home network and sends an enhanced EAP (note that this is an EAP session different from an already ongoing EAP session between the MN and AAAh) message to the MAP, and the MAP preferably Respond to the AAAh by providing information (if needed or otherwise appropriate) for completing the security association with the MN. For example, for IPSec security associations, it may be necessary to utilize EAP attributes such as the IPSec protocol, IPSec cipher, IPSec key validity period EAP TLV attributes defined in Table 1 above.
在该说明性示例和以下的说明性示例中,假定移动节点(MN)和AAAh具有公共共享秘密。例如这可能是移动节点中安装的身份模块与归属网络营运商之间共享的对称密钥。身份模块可以是本领域已知的任何防篡改身份模块,包括GSM(全球移动通信系统)移动电话中使用的标准SIM卡、通用SIM(USIM)、还称为WIM的WAP(无线应用协议)SIM、ISIM(IP多媒体子系统身份模块)以及更普遍的UICC(通用集成电路卡)模块。对于MN-MAP(MN-HA)安全关联,可以由MN向AAA传送种子或现用值(或从相反方向,即由AAAh始发种子并传送到MN),AAAh据此可以基于共享秘密创建MN-MAP(MN-HA)安全密钥。移动节点可以独自生成相同的安全密钥,因为它始发种子/现用值(或从AAAh接收种子)并也具有共享秘密。备选地,AAAh可以自己生成安全信息,并将其安全传送到相关节点。In this and the following illustrative examples, it is assumed that the mobile node (MN) and AAAh have a common shared secret. This could eg be a symmetric key shared between the identity module installed in the mobile node and the home network operator. The identity module can be any tamper-resistant identity module known in the art, including standard SIM cards used in GSM (Global System for Mobile Communications) mobile phones, Universal SIM (USIM), WAP (Wireless Application Protocol) SIM also known as WIM , ISIM (IP Multimedia Subsystem Identity Module) and more generally UICC (Universal Integrated Circuit Card) module. For the MN-MAP (MN-HA) security association, the MN can transmit the seed or nonce to the AAA (or from the opposite direction, that is, the AAAh initiates the seed and transmits it to the MN), and the AAAh can create the MN based on the shared secret - MAP (MN-HA) security key. The mobile node can generate the same security key on its own, since it originates the seed/nonce (or receives the seed from AAAh) and also has the shared secret. Alternatively, the AAAh can generate the security information itself and transmit it securely to the relevant nodes.
其次,如果请求MIPv6引导,则AAAh通过使用另一个增强EAP会话选择HA来继续为该MIPv6引导请求服务,并且HA通过提供创建与MN的安全关联所需的信息来响应AAAh。任选地,在鉴权和授权交换中捎带传输“MAP绑定更新”以及“HA绑定更新”是可能的。这意味着HMIPv6绑定集成在与MN-MAP安全关联相同的往返中(在来自移动节点的绑定更新中只需LCoA)。对于此情况,AAAh在与MAP的第一次操作中获得的HMIPv6RCoA自动是在与HA的第二次操作中更新的MIPv6绑定。Second, if MIPv6 bootstrap is requested, AAAh selects an HA to continue servicing this MIPv6 bootstrap request by using another enhanced EAP session, and the HA responds to AAAh by providing the information required to create a security association with the MN. Optionally, it is possible to piggyback "MAP Binding Update" and "HA Binding Update" in the authentication and authorization exchange. This means that the HMIPv6 binding is integrated in the same round trip as the MN-MAP security association (only LCoA is required in the binding update from the mobile node). For this case, the HMIPv6 RCoA obtained by the AAAh in the first operation with the MAP is automatically the updated MIPv6 binding in the second operation with the HA.
在如上所述AAAh与MAP和HA通信之后,AAAh经由扩展的EAP将授权(和/或配置)信息如MAP地址、RCoA、HA地址、MN归属地址和安全关联信息以及鉴权成功指示发送回MN。图7中交换的额外最后一个往返是为确保根据目前的EAP协议规范平滑实现EAP协议。After AAAh communicates with MAP and HA as described above, AAAh sends authorization (and/or configuration) information such as MAP address, RCoA, HA address, MN home address and security association information and authentication success indication back to MN via extended EAP . The extra last round trip exchanged in Figure 7 is to ensure a smooth implementation of the EAP protocol according to the current EAP protocol specification.
图8示出针对MAP位于受访网络时的情况的示范EAP/HMIPv6(直径)信令流。Figure 8 shows an exemplary EAP/HMIPv6 (diameter) signaling flow for the case when the MAP is located in the visited network.
AAA客户使用EAP(请求身份)请求MN鉴权,以及MN以EAP(响应身份)响应。The AAA client requests the MN to authenticate using the EAP (request identity), and the MN responds with the EAP (response identity).
MN响应经由AAA基础结构发送到AAAh。AAAh根据MN的身份和基于营运商策略确定EAP/HMIPv6方法适于MN的鉴权和授权(即AAAh知道MN的能力)。AAAh经由AAA基础结构向MN发送建议的EAP方法(即EAP/HMIPv6)的指示连同询问。The MN response is sent to AAAh via the AAA infrastructure. AAAh determines that the EAP/HMIPv6 method is suitable for the authentication and authorization of the MN according to the identity of the MN and based on the operator's policy (that is, AAAh knows the capabilities of the MN). AAAh sends an indication of the proposed EAP method (ie EAP/HMIPv6) to the MN along with a query via the AAA infrastructure.
MN希望引导HMIPv6,并以询问响应以及适当的EAP属性(例如TLV)来答复AAAh建议和询问,适当的EAP属性传送指定适当的MAP的请求连同用于与指定的MAP安全关联的必要信息。在此过程中,MN还可以引导MIPv6,如果先前尚未执行过的话。MN响应经由AAA基础结构发送到AAAh。The MN wishes to bootstrap HMIPv6, and replies to the AAAh Proposal and Challenge with a Challenge Response and appropriate EAP Attributes (eg TLV) that convey a request to specify the appropriate MAP along with the necessary information for security association with the specified MAP. During this process, the MN can also bootstrap MIPv6, if it has not been performed previously. The MN response is sent to AAAh via the AAA infrastructure.
AAAh验证MN的询问响应,并且如果成功,则这意味着MN是可信的,并且AAAh继续处理MN的其他请求。The AAAh verifies the MN's challenge response, and if successful, this means the MN is authentic, and the AAAh proceeds to process other requests of the MN.
首先,AAAh将对受访网络中MAP的请求转发到适当的AAAv,这优选地经由直径应用(为简单被称作直径HMIPv6应用)来进行。这样做的原因是,在受访网络中选择MAP时需要考虑受访营运商的策略,并且由此AAAv需要可以查看该事务(在EAP情况下这些交换是端到端的,因此这是不可能的)。AAAv在受访网络中选择MAP,并将含有例如安全密钥的直径HMIPv6应用消息转发到MAP。MAP优选地通过提供用于完成与MN的安全关联的信息(如果是需要的或在其他方面是适当的)来对AAAh响应。其次,如果这样的请求存在,则AAAh通过使用另一个增强EAP会话选择HA来继续为该MIPv6引导请求服务,并且HA通过提供创建与MN的安全关联所需的信息来响应AAAh。注意到,在鉴权和授权交换中捎带传输“MAP绑定更新”以及“HA绑定更新”是可能的。对于此情况,AAAh在与MAP的第一次操作中获得的HMIPv6RCoA自动是在与HA的第二次操作中更新的MIPv6绑定。First, the AAAh forwards the request for the MAP in the visited network to the appropriate AAAv, preferably via the Diameter application (referred to simply as the Diameter HMIPv6 application). The reason for this is that the visited operator's policy needs to be taken into account when choosing a MAP in the visited network, and thus the AAAv needs to be able to see the transaction (in the EAP case these exchanges are end-to-end, so this is not possible ). The AAAv selects a MAP in the visited network and forwards the Diameter HMIPv6 Application message containing eg a security key to the MAP. The MAP preferably responds to the AAAh by providing information (if needed or otherwise appropriate) to complete the security association with the MN. Second, if such a request exists, the AAAh selects an HA to continue servicing this MIPv6 bootstrap request by using another enhanced EAP session, and the HA responds to the AAAh by providing the information needed to create a security association with the MN. Note that it is possible to piggyback "MAP Binding Updates" as well as "HA Binding Updates" in the authentication and authorization exchanges. For this case, the HMIPv6 RCoA obtained by the AAAh in the first operation with the MAP is automatically the updated MIPv6 binding in the second operation with the HA.
在如上所述AAAh与MAP和HA通信之后,AAAh经由扩展的EAP将授权(和/或配置)信息如MAP地址、RCoA、HA地址、MN归属地址和安全关联信息以及鉴权成功指示发送回MN。图8中交换的额外最后一个往返是为确保根据目前的EAP协议规范平滑实现EAP协议。After AAAh communicates with MAP and HA as described above, AAAh sends authorization (and/or configuration) information such as MAP address, RCoA, HA address, MN home address and security association information and authentication success indication back to MN via extended EAP . The extra last round trip exchanged in Figure 8 is to ensure a smooth implementation of the EAP protocol according to the current EAP protocol specification.
虽然一些详细示范实施例主要是参考目前的EAP版本来讨论,但是应该理解,本发明非常适用于其他EAP版本,如EAPv2,以及以所述方式扩展或配置的其他鉴权协议。EAP仅仅是可能的实施方式的示例,并且本发明一般不局限于此,而是可以备选地涉及非EAP方案。Although some detailed exemplary embodiments are primarily discussed with reference to the current EAP version, it should be understood that the present invention is well suited to other EAP versions, such as EAPv2, and other authentication protocols extended or configured in the manner described. EAP is only an example of possible implementations, and the invention is generally not limited thereto, but may alternatively relate to non-EAP schemes.
HMIPv6的AAA框架协议应用Application of AAA Framework Protocol in HMIPv6
在另一个示范实施例中,创建一种新的AAA框架协议应用,本文以适合HMIPv6的直径应用(称为“直径HMIPv6应用”)为例,它承载便于例如发现MAP、动态分配MAP、动态分配RCoA、MN和MAP之间分发安全密钥和/或可能的捎带传输HMIPv6移动性过程的HMIPv6相关信息。虽然下文涉及的是直径,但是应该理解,还可以使用RADIUS或其他类似的AAA框架协议来作为新的或扩展的HMIPv6应用的基础。In another exemplary embodiment, a new AAA framework protocol application is created. This paper takes the diameter application suitable for HMIPv6 (referred to as "diameter HMIPv6 application") as an example. Distribute security keys and/or possibly piggyback HMIPv6 related information for HMIPv6 mobility procedures among RCoA, MN and MAP. Although diameter is referred to below, it should be understood that RADIUS or other similar AAA framework protocols can also be used as the basis for new or extended HMIPv6 applications.
如果希望的话,HMIPv6和MIPv6鉴权和/或授权可以集成在相同的AAA框架协议应用中。这可以通过采用[3]中所述的直径MIPv6应用以及另外还定义新的HMIP特定的命令代码、AVP和/或标志来实现。通过将直径MIPv6应用的命令代码、AVP和标志作为直径HMIPv6应用的一部分包括,将MIPv6和HMIPv6鉴权和/或授权的同时执行容纳于允许更短建立时间的单个遍历中。在没有MIPv6鉴权和/或授权的情况下仅执行HMIPv6鉴权和/或授权也是可能的,且反之亦然,具体取决于特定情况下MN的具体需求。这使单个应用(直径HMIPv6应用)可以灵活地在各种用例场合使用。HMIPv6 and MIPv6 authentication and/or authorization can be integrated in the same AAA frame protocol application if desired. This can be achieved by adopting the Diameter MIPv6 application described in [3] and additionally defining new HMIP-specific command codes, AVPs and/or flags. By including the command codes, AVPs and flags of the Diameter MIPv6 application as part of the Diameter HMIPv6 application, simultaneous execution of MIPv6 and HMIPv6 authentication and/or authorization is accommodated in a single pass allowing for shorter setup times. It is also possible to perform only HMIPv6 authentication and/or authorization without MIPv6 authentication and/or authorization, and vice versa, depending on the specific needs of the MN in a particular situation. This enables a single application (diameter HMIPv6 application) to be used flexibly in various use case scenarios.
再者,在直径HMIPv6应用中捎带传输HMIPv6移动性过程使得可能通过在公共过程中优化鉴权、授权和移动性来缩短整个建立时间。Furthermore, piggybacking HMIPv6 mobility procedures in Diameter HMIPv6 applications makes it possible to shorten the overall setup time by optimizing authentication, authorization and mobility in common procedures.
直径HMIPv6应用的详细信息Diameter HMIPv6 Application Details
在下文中,提供示范直径HMIPv6应用的详细信息,以说明整体流程的示例和概念的可行性。优选地,定义新的HMIP特定的命令代码、AVP和/或标志,它们承载便于例如发现MAP、动态分配MAP、动态分配RCoA、MN和MAP之间分发安全密钥和/或可能的捎带传输HMIPv6移动性过程的信息。直径MIPv6应用[3]的命令代码、AVP和标志可以任选地作为直径HMIPv6应用的一部分包括。In the following, details of a demonstration diameter HMIPv6 application are provided to illustrate an example of the overall flow and the feasibility of the concept. Preferably, new HMIP-specific command codes, AVPs and/or flags are defined which carry HMIPv6 to facilitate e.g. discovery of MAPs, dynamic allocation of MAPs, dynamic allocation of RCoA, distribution of security keys between MNs and MAPs and/or possible piggybacking of HMIPv6 Information on the mobility process. The command codes, AVPs and flags of the Diameter MIPv6 Application [3] may optionally be included as part of the Diameter HMIPv6 Application.
下表2中给出直径HMIPv6应用命令代码和AVP的示范概括矩阵:An exemplary summary matrix of Diameter HMIPv6 application command codes and AVPs is given in Table 2 below:
对于附加信息,因特网草案[5]定义了在网络接入服务器(NAS)与后端鉴权服务器之间承载EAP分组所需的命令代码和AVP。For additional information, Internet-Draft [5] defines the command codes and AVPs required to carry EAP packets between a Network Access Server (NAS) and a backend authentication server.
直径HMIPv6应用的示范信令流Demonstration signaling flow for Diameter HMIPv6 application
图9示出针对MAP位于归属网络时的情况的示范直径HMIPv6应用信令流。Figure 9 shows an exemplary Diameter HMIPv6 application signaling flow for the case when the MAP is located in the home network.
AAA客户经由例如因特网控制消息协议(ICMP)、PANA等的协议向要鉴权的MN发布询问。MN以询问响应以及HMIPv6可能还有MIPv6引导请求来响应。The AAA client issues a challenge to the MN to be authenticated via a protocol such as Internet Control Message Protocol (ICMP), PANA, and the like. The MN responds with a Challenge Response and possibly a MIPv6 Bootstrap Request.
AAA客户理解HMIPv6和MIPv6引导请求,并使用直径HMIPv6应用命令代码(ARR)经由AAA基础结构将MN响应转发到AAAh。在该过程中,AAA客户还包括使AAAh可以检验MN的可信性的询问。The AAA Client understands HMIPv6 and MIPv6 Bootstrap Requests and forwards MN responses to AAAh via the AAA infrastructure using the Diameter HMIPv6 Application Command Code (ARR). In this process, the AAA client also includes a query that allows the AAAh to verify the authenticity of the MN.
AAAh验证MN的询问响应,并且如果成功,则这意味着MN是可信的,并且AAAh然后继续处理MN的其他请求。The AAAh verifies the MN's challenge response, and if successful, this means the MN is authentic, and the AAAh then proceeds to process other requests of the MN.
首先,AAAh在归属网络中选择MAP,并将含有例如安全密钥的适当的直径HMIPv6应用命令代码(MAR)发送到MAP,并且MAP经由命令代码(MAA)优选地通过提供用于完成与MN的安全关联的信息(如果是需要的或在其他方面是适当的)来对AAAh响应。其次,如果请求MIPv6引导,则AAAh通过使用直径HMIPv6应用命令代码((HOR))选择HA来继续为该MIPv6引导请求服务,并且HA经由命令代码(HOA)通过提供创建与MN的安全关联所需的信息来响应AAAh。注意到,在鉴权和授权交换中捎带传输“MAP绑定更新”以及“HA绑定更新”是可能的。对于此情况,AAAh在与MAP的第一次操作中获得的HMIPv6RCoA自动是在与HA的第二次操作中更新的MIPv6绑定。First, the AAAh selects the MAP in the home network and sends the appropriate Diameter HMIPv6 Application Command Code (MAR) containing e.g. Security Association information (if required or otherwise appropriate) in response to the AAAh. Second, if MIPv6 bootstrapping is requested, the AAAh selects the HA to continue servicing the MIPv6 bootstrap request by using the Diameter HMIPv6 Application command code ((HOR)), and the HA passes the command code (HOA) by providing the HA required to create a security association with the MN. information to respond to AAAh. Note that it is possible to piggyback "MAP Binding Updates" as well as "HA Binding Updates" in the authentication and authorization exchanges. For this case, the HMIPv6 RCoA obtained by the AAAh in the first operation with the MAP is automatically the updated MIPv6 binding in the second operation with the HA.
在如上所述AAAh与MAP和HA通信之后,AAAh经由直径HMIPv6应用命令代码(ARA)和例如ICMP、PANA等将授权(和/或配置)信息如MAP地址、RCoA、HA地址、MN归属地址和安全关联信息以及鉴权成功指示发送回MN。After AAAh communicates with MAP and HA as described above, AAAh will authorize (and/or configure) information such as MAP address, RCoA, HA address, MN home address and The security association information and the successful authentication indication are sent back to the MN.
图10示出针对MAP位于受访网络时的情况的示范直径HMIPv6应用信令流。Figure 10 shows an exemplary Diameter HMIPv6 application signaling flow for the case when the MAP is located in the visited network.
AAA客户经由例如ICMP或PANA向要鉴权的MN发布询问。MN以询问响应以及HMIPv6可能还有MIPv6引导请求来响应。The AAA client issues a challenge to the MN to be authenticated via eg ICMP or PANA. The MN responds with a Challenge Response and possibly a MIPv6 Bootstrap Request.
AAA客户理解HMIPv6和MIPv6引导请求,并使用直径HMIPv6应用命令代码(ARR)经由AAA基础结构将MN响应转发到AAAh。在该过程中,AAA客户还包括使AAAh可以检验MN的可信性的询问。The AAA Client understands HMIPv6 and MIPv6 Bootstrap Requests and forwards MN responses to AAAh via the AAA infrastructure using the Diameter HMIPv6 Application Command Code (ARR). In this process, the AAA client also includes a query that allows the AAAh to verify the authenticity of the MN.
AAAh验证MN的询问响应,并且如果成功,则这意味着MN是可信的,并且AAAh然后继续处理MN的其他请求。The AAAh verifies the MN's challenge response, and if successful, this means the MN is authentic, and the AAAh then proceeds to process other requests of the MN.
首先,AAAh将对受访网络中MAP的请求转发到适当的AAAv,这优选地经由直径HMIPv6应用命令代码(MAR)来进行。AAAv在受访网络中选择MAP,并将包括例如安全密钥的命令代码(MAR)转发到MAP,并且MAP优选地使用命令代码(MAA)通过提供用于完成与MN的安全关联的信息(如果是需要的或在其他方面是适当的)来经由AAAv对AAAh响应。其次,如果被请求,则AAAh通过使用直径HMIPv6应用命令代码(HOR)选择HA来继续为该MIPv6引导请求服务,并且HA经由命令代码(HOA)通过提供创建与MN的安全关联所需的信息来响应AAAh。注意到,在鉴权和授权交换中捎带传输“MAP绑定更新”以及“HA绑定更新”是可能的。对于此情况,AAAh在与MAP的第一次操作中获得的HMIPv6RCoA自动是在与HA的第二次操作中更新的MIPv6绑定。First, the AAAh forwards the request for the MAP in the visited network to the appropriate AAAv, preferably via the Diameter HMIPv6 Application Order Code (MAR). AAAv selects a MAP in the visited network and forwards to the MAP a command code (MAR) including, for example, a security key, and the MAP preferably uses the command code (MAA) by providing information for completing a security association with the MN (if is required or otherwise appropriate) to respond to AAAh via AAAv. Second, if requested, the AAAh selects an HA to continue servicing this MIPv6 Bootstrap Request by using the Diameter HMIPv6 Application Order Code (HOR), and the HA proceeds via the order code (HOA) by providing the information required to create a Security Association with the MN Respond to AAAh. Note that it is possible to piggyback "MAP Binding Updates" as well as "HA Binding Updates" in the authentication and authorization exchanges. For this case, the HMIPv6 RCoA obtained by the AAAh in the first operation with the MAP is automatically the updated MIPv6 binding in the second operation with the HA.
在如上所述AAAh与MAP和HA通信之后,AAAh经由直径HMIPv6应用命令代码(ARA)和例如ICMP或PANA的协议将授权(和/或配置)信息如MAP地址、RCoA、HA地址、MN归属地址和安全关联信息以及鉴权成功指示发送回MN。After AAAh communicates with MAP and HA as described above, AAAh will authorize (and/or configure) information such as MAP address, RCoA, HA address, MN home address via Diameter HMIPv6 Application Command Code (ARA) and protocols such as ICMP or PANA and the security association information and the successful authentication indication are sent back to the MN.
概括上述一些方面,可以看出,对AAA基础结构的依赖提供了用于引导HMIPv6业务的若干可能性。例如,可能的是,提供对通过AAA基础结构承载的普通鉴权协议(如目前或将来的EAP版本)的扩展和/或增强AAA框架协议应用,如直径和RADIUS应用。Summarizing some of the above aspects, it can be seen that the reliance on the AAA infrastructure provides several possibilities for directing HMIPv6 traffic. For example, it is possible to provide extensions and/or enhancements to common authentication protocols carried over the AAA infrastructure (such as current or future EAP versions) and/or enhancements to AAA frame protocol applications such as DIAMETER and RADIUS applications.
图11是用于支持移动节点的HMIPv6业务的方法的基本示例的示意流程图。在该示例中,步骤S1-S4所示的信息传送和操作涉及移动节点的鉴权(S1)、MN-MAP安全关联的建立(S2)、HMIPv6配置(S3)和HMIPv6绑定(S4)。步骤S2-S3通称为授权阶段。如果希望的话,可以或多或少以并行方式执行步骤S1-S4,例如在与HMIPv6安全关联过程相同的往返中捎带传输HMIPv6绑定,以可以缩短整个建立时间。在步骤S1,通过AAA基础结构传送信息,以在归属网络端对移动节点鉴权。在步骤S2,传送HMIPv6相关信息,以立即建立或允许将来建立MN和MAP之间的安全关联。在步骤S3中,执行附加的HMIPv6配置,例如通过向移动节点传送配置参数以在其中进行适合的存储。在步骤S4,移动节点发送绑定更新,并在MAP中建立HMIPv6绑定。Fig. 11 is a schematic flowchart of a basic example of a method for supporting HMIPv6 services of a mobile node. In this example, the information transfer and operations shown in steps S1-S4 involve authentication of the mobile node (S1), establishment of MN-MAP security association (S2), HMIPv6 configuration (S3) and HMIPv6 binding (S4). Steps S2-S3 are collectively referred to as the authorization phase. If desired, steps S1-S4 can be performed in a more or less parallel manner, eg piggybacking the HMIPv6 binding in the same round trip as the HMIPv6 security association process, so that the overall setup time can be shortened. In step S1, information is transmitted through the AAA infrastructure to authenticate the mobile node at the home network side. In step S2, HMIPv6-related information is transmitted to immediately establish or allow future establishment of a security association between the MN and the MAP. In step S3, additional HMIPv6 configuration is performed, for example by transferring configuration parameters to the mobile node for suitable storage therein. In step S4, the mobile node sends a binding update and establishes HMIPv6 binding in the MAP.
在其他应用领域中,本发明可应用于诸如WLAN、CDMA2000、WCDMA等的所有接入网,其中可以使用HMIPv6以及任选地还有MIPv6,包括诸如AAA和IPv6移动性的技术、诸如CMS11、WCDMA和GSM系统的系统、诸如服务/应用子系统和终端的子系统以及诸如AAA服务器、归属代理服务器和终端节点的产品。In other fields of application, the invention is applicable to all access networks such as WLAN, CDMA2000, WCDMA, etc., where HMIPv6 and optionally also MIPv6 can be used, including technologies such as AAA and IPv6 mobility, such as CMS11, WCDMA and GSM systems, subsystems such as service/application subsystems and terminals, and products such as AAA servers, home agent servers, and terminal nodes.
作为上述MN-HA密钥分发的示例过程的备选方式,与目前的3GPP2解决方案类似的机制结合IKE框架可以用于分发MN和HA的动态预共享密钥。As an alternative to the above example procedure of MN-HA key distribution, a mechanism similar to the current 3GPP2 solution combined with the IKE framework can be used to distribute the dynamic pre-shared keys of the MN and HA.
上述实施例仅是作为示例给出,并且应该理解,本发明并不局限于此。而且保留本文公开的和要求保护的基本基础原理的其他修改、更改和改进都属于本发明的范围。The above-mentioned embodiments are given as examples only, and it should be understood that the present invention is not limited thereto. Furthermore, other modifications, changes and improvements which retain the basic underlying principles disclosed and claimed herein are within the scope of the invention.
参考文献references
[1]“IPv6中的移动性支持(Mobility Support in IPv6)”,D.Johnson,C.Perkins,J.Arkko,2003年6月30日,<draft-ietf-mobileip-ipv6-24.txt>。[1] "Mobility Support in IPv6", D.Johnson, C.Perkins, J.Arkko, June 30, 2003, <draft-ietf-mobileip-ipv6-24.txt> .
[2]“分级移动IPv6移动性管理(Hierarchical Mobile IPv6 mobilitymanagement)(HMIPv6)”,Hesham Soliman,Claude Castelluccia,Karim El-Malki,Ludovic Bellier,2003年6月,<draft-ietf-mobileip-hmipv6-08.txt>。[2] "Hierarchical Mobile IPv6 mobility management (HMIPv6)", Hesham Soliman, Claude Castelluccia, Karim El-Malki, Ludovic Bellier, June 2003, <draft-ietf-mobileip-hmipv6-08 .txt>.
[3]“直径移动Ipv6应用(Diameter Mobile IPv6 Application)”,Stefano M.Faccin,Franck Le,Basavaraj Patil,Charles E.Perkins,2003年4月,<draft-le-aaa-diameter-mobileipv6-03.txt>。[3] "Diameter Mobile IPv6 Application", Stefano M.Faccin, Franck Le, Basavaraj Patil, Charles E.Perkins, April 2003, <draft-le-aaa-diameter-mobileipv6-03. txt>.
[4]“基于EAP的MIPv6授权和配置(MIPv6 Authorization andConfiguration based on EAP)”,G.Giaretta,I.Guardini,E.Demaria,2004年2月,<draft-giaretta-mip6-authorization-eap-00.txt>。[4] "EAP-based MIPv6 authorization and configuration (MIPv6 Authorization and Configuration based on EAP)", G.Giaretta, I.Guardini, E.Demaria, February 2004, <draft-giaretta-mip6-authorization-eap-00 .txt>.
[5]“直径可扩展鉴权协议(Diameter Extensible AuthenticationProtocol)(EAP)应用”,P.Eronen,T.Hiller,G.Zorn,2004年2月16日,<draft-ietf-aaa-eap-04.txt>。[5] "Diameter Extensible Authentication Protocol (EAP) application", P.Eronen, T.Hiller, G.Zorn, February 16, 2004, <draft-ietf-aaa-eap-04 .txt>.
[6]“PPP可扩展鉴权协议(PPP Extensible AuthenticationProtocol)(EAP)”,RFC2284,L.Blunk,J.Vollbrecht,1998年3月。[6] "PPP Extensible Authentication Protocol (EAP)", RFC2284, L.Blunk, J.Vollbrecht, March 1998.
[7]IEEE标准802.1X,局域网和城域网-基于端口的网络接入控制。[7] IEEE Standard 802.1X, Local and Metropolitan Area Networks - Port-Based Network Access Control.
[8]“因特网安全关联和密钥管理协议(Internet SecurityASSociation and Key Management Protocol)(ISAKMP)”,RFC2408,D.Maughan,M.Schertler,M.Schneider,J.Turner,1998年11月。[8] "Internet Security Association and Key Management Protocol (Internet SecurityASSociation and Key Management Protocol) (ISAKMP)", RFC2408, D.Maughan, M.Schertler, M.Schneider, J.Turner, November 1998.
[9]“直径移动IPv4应用(Diameter Mobile IPv4 Application)”,P.Calhoun,T.Johansson,C.Perkins,2003,<draft-ietf-aaa-diameter-mobileip-14.txt>。[9] "Diameter Mobile IPv4 Application", P.Calhoun, T.Johansson, C.Perkins, 2003, <draft-ietf-aaa-diameter-mobileip-14.txt>.
[10]“远程鉴权拨号用户服务(Remote Authentication Dial In UserService)(RADIUS)”-RFC2865,C.Rigney,S.Willens,A.Rubens,W.Simpson,2000年6月。[10] "Remote Authentication Dial In UserService (RADIUS)" - RFC2865, C. Rigney, S. Willens, A. Rubens, W. Simpson, June 2000.
[11]“RADIUS扩展(RADIUS Extensions)”-RFC2869,C.Rigney,W.Willats,P.Calhoun,2000年6月。[11] "RADIUS Extensions" - RFC2869, C. Rigney, W. Willats, P. Calhoun, June 2000.
[12]“可扩展鉴权协议(Extensible Authentication Protocol)(EAP)”-RFC2284,L.Blunk,J.Vollbrecht,B.Aboba,J.Carlson,H.Levkowetz,2003年9月,<draft-ietf-eap-rfc2284bis-06.txt>。[12] "Extensible Authentication Protocol (EAP)" - RFC2284, L.Blunk, J.Vollbrecht, B.Aboba, J.Carlson, H.Levkowetz, September 2003, <draft-ietf -eap-rfc2284bis-06.txt>.
[13]“EAP对等和鉴权者的状态机器(State Machines for EAP Peerand Authenticator)”,J.Vollbrecht,P.Eronen,N.Petroni,Y.Ohba,2003年10月<draft-ietf-eap-statemachine-01.pdf>。[13] "State Machines for EAP Peer and Authenticator", J.Vollbrecht, P.Eronen, N.Petroni, Y.Ohba, October 2003 <draft-ietf-eap -statemachine-01.pdf>.
Claims (20)
Applications Claiming Priority (3)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| US47915603P | 2003-06-18 | 2003-06-18 | |
| US60/479,156 | 2003-06-18 | ||
| US60/551,039 | 2004-03-09 |
Publications (2)
| Publication Number | Publication Date |
|---|---|
| CN1836420A CN1836420A (en) | 2006-09-20 |
| CN100539586C true CN100539586C (en) | 2009-09-09 |
Family
ID=37003349
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| CNB2004800234028A Expired - Fee Related CN100539586C (en) | 2003-06-18 | 2004-06-15 | Method, system and equipment for supporting hierarchical mobile IP services |
Country Status (2)
| Country | Link |
|---|---|
| CN (1) | CN100539586C (en) |
| ZA (1) | ZA200510088B (en) |
Families Citing this family (2)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| EP2210429B1 (en) * | 2007-09-20 | 2014-01-15 | Telefonaktiebolaget LM Ericsson (publ) | Method and apparatus for roaming between communications networks |
| CN108351792A (en) * | 2016-01-15 | 2018-07-31 | 谷歌有限责任公司 | Use application containers to manage the delivery of code and dependency data |
Citations (2)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US20020199104A1 (en) * | 2001-06-22 | 2002-12-26 | Mitsuaki Kakemizu | Service control network |
| WO2003014935A1 (en) * | 2001-08-08 | 2003-02-20 | Nokia Corporation | Efficient security association establishment negotiation technique |
-
2004
- 2004-06-15 CN CNB2004800234028A patent/CN100539586C/en not_active Expired - Fee Related
- 2004-06-15 ZA ZA200510088A patent/ZA200510088B/en unknown
Patent Citations (2)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US20020199104A1 (en) * | 2001-06-22 | 2002-12-26 | Mitsuaki Kakemizu | Service control network |
| WO2003014935A1 (en) * | 2001-08-08 | 2003-02-20 | Nokia Corporation | Efficient security association establishment negotiation technique |
Non-Patent Citations (1)
| Title |
|---|
| Hierarchical Mobile IPv6 and Fast Handoffs. H.soliman,摘要、第10部分. 2000 * |
Also Published As
| Publication number | Publication date |
|---|---|
| ZA200510088B (en) | 2007-03-28 |
| CN1836420A (en) | 2006-09-20 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| EP1634422B1 (en) | Method, system and apparatus to support hierarchical mobile ip services | |
| US20060185013A1 (en) | Method, system and apparatus to support hierarchical mobile ip services | |
| US7983418B2 (en) | AAA support for DHCP | |
| CN1836419B (en) | Method, system and device for supporting Mobile IP Release 6 service in CDMA system | |
| KR101030645B1 (en) | How to establish a security binding, how to validate a join update, and how to run a join update | |
| KR100918440B1 (en) | Communication method and device of mobile terminal using IP address of gateway in virtual private network | |
| KR100935421B1 (en) | Use of Generic Authentication Architecture for Mobile Internet Protocol Key Distribution | |
| JP4723158B2 (en) | Authentication methods in packet data networks | |
| US7079499B1 (en) | Internet protocol mobility architecture framework | |
| RU2437238C2 (en) | Methods and device for provision of pmip keys hierarchy in wireless communication network | |
| JP5461591B2 (en) | Combination of IP and cellular mobility | |
| CN101803413B (en) | Method and apparatus for roaming between communication networks | |
| JP2013021712A (en) | Mobility management system, home agent, mobile terminal management method used for them, and its program | |
| CN101540999A (en) | Method and equipment for establishing safe data tunnel | |
| JP4909357B2 (en) | Method for transmitting data packets based on an Ethernet transmission protocol between at least one mobile communication unit and a communication system | |
| CN100539586C (en) | Method, system and equipment for supporting hierarchical mobile IP services | |
| TWI390876B (en) | Methods and apparatuses for cdma2000/gprs roaming | |
| ES2616499T3 (en) | Devices and method for authentication in heterogeneous IP networks |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| C06 | Publication | ||
| PB01 | Publication | ||
| C10 | Entry into substantive examination | ||
| SE01 | Entry into force of request for substantive examination | ||
| CI02 | Correction of invention patent application |
Correction item: Priority Correct: 2004.03.09 US 60/551,039 False: Lack of priority second Number: 38 Page: The title page Volume: 22 |
|
| COR | Change of bibliographic data |
Free format text: CORRECT: PRIORITY; FROM: MISSING THE SECOND ARTICLE OF PRIORITY TO: 2004.3.9 US 60/551,039 |
|
| REG | Reference to a national code |
Ref country code: HK Ref legal event code: DE Ref document number: 1094844 Country of ref document: HK |
|
| C14 | Grant of patent or utility model | ||
| GR01 | Patent grant | ||
| REG | Reference to a national code |
Ref country code: HK Ref legal event code: WD Ref document number: 1094844 Country of ref document: HK |
|
| CF01 | Termination of patent right due to non-payment of annual fee |
Granted publication date: 20090909 Termination date: 20170615 |
|
| CF01 | Termination of patent right due to non-payment of annual fee |